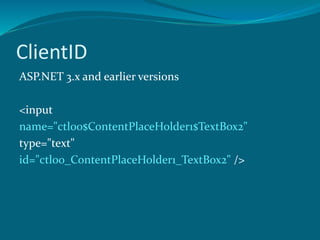
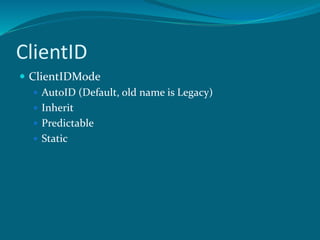
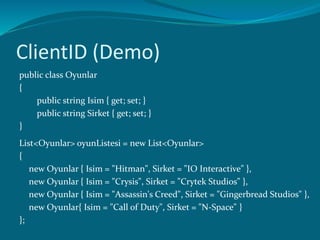
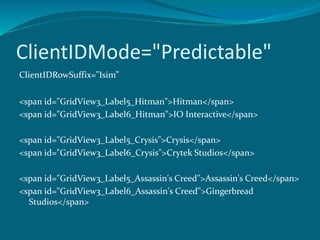
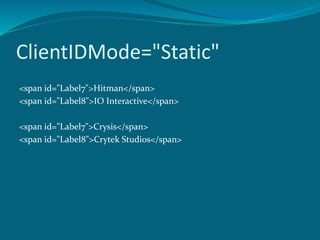
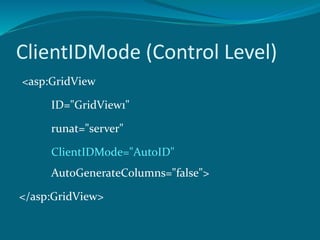
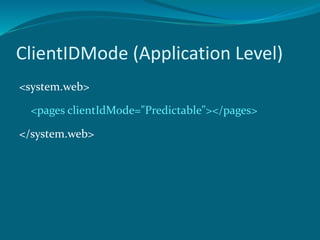
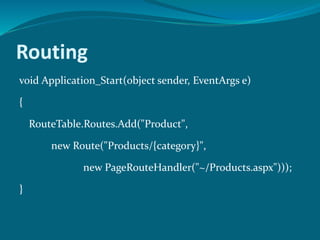
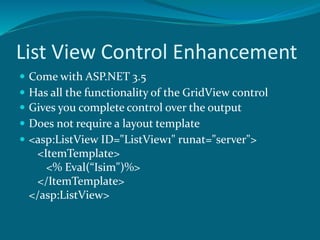
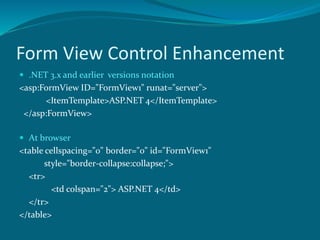
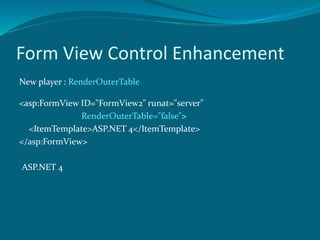
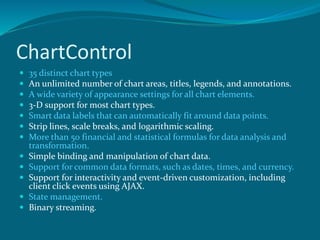
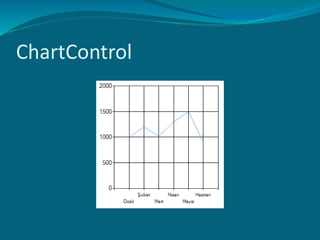
This document summarizes several new features in ASP.NET 4 including improvements to ViewState, ClientID, routing, list views, form views, chart controls, caching, and request validation. Key enhancements include more control over ViewState and ClientID generation, support for routing URLs, additional layout options for lists and forms, over 35 chart types, extensible output caching providers, and the ability to customize request validation.