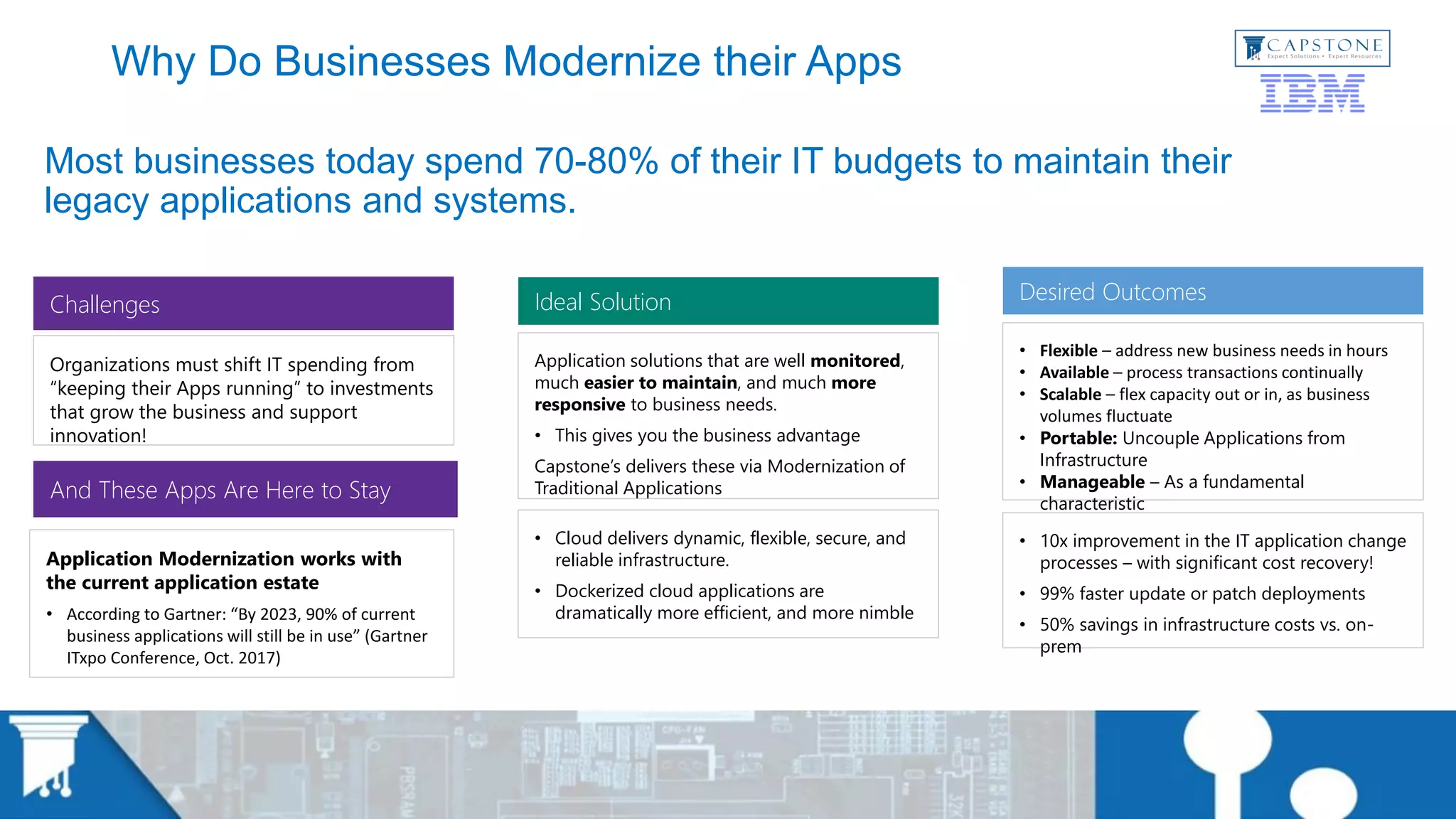
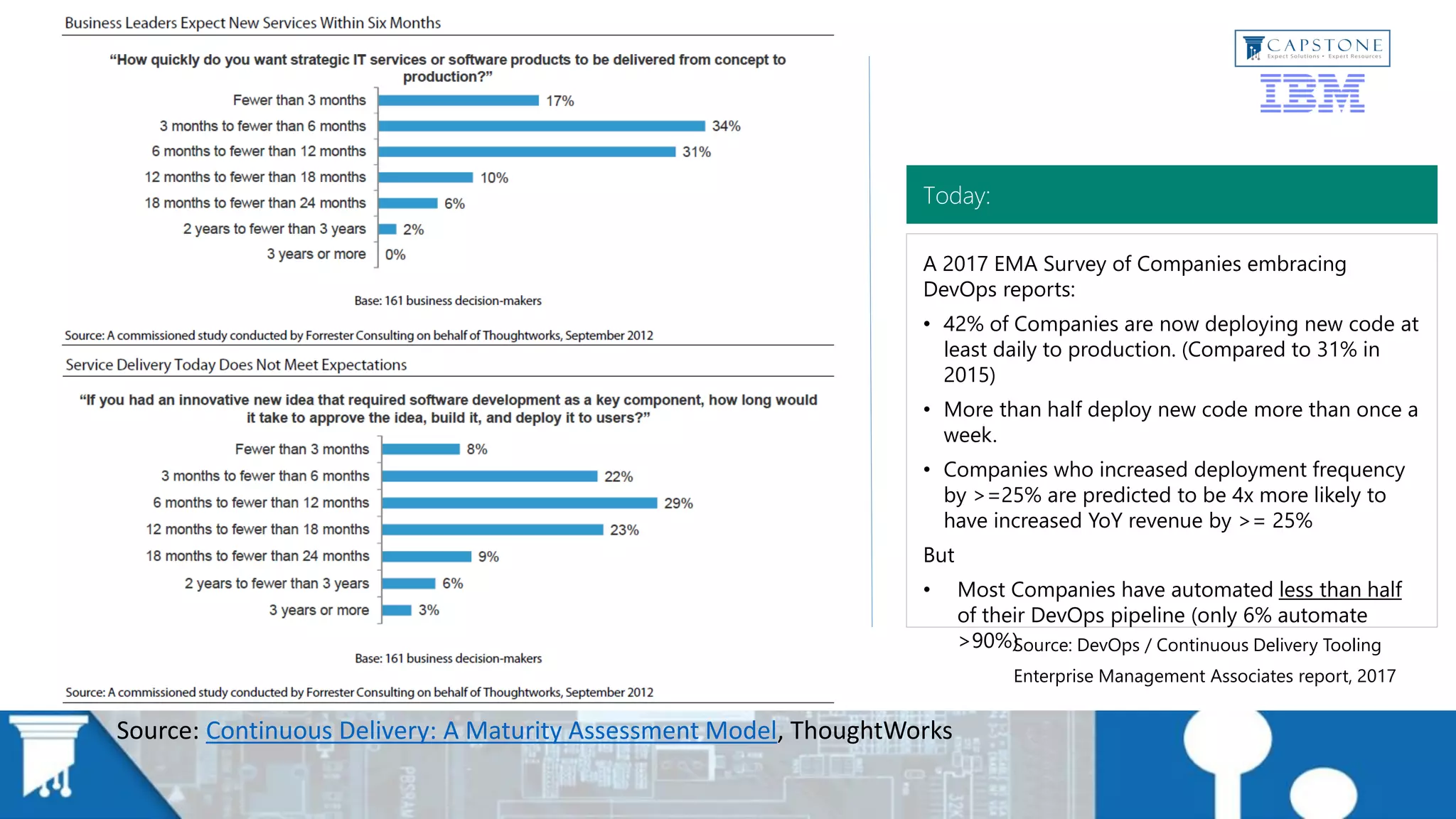
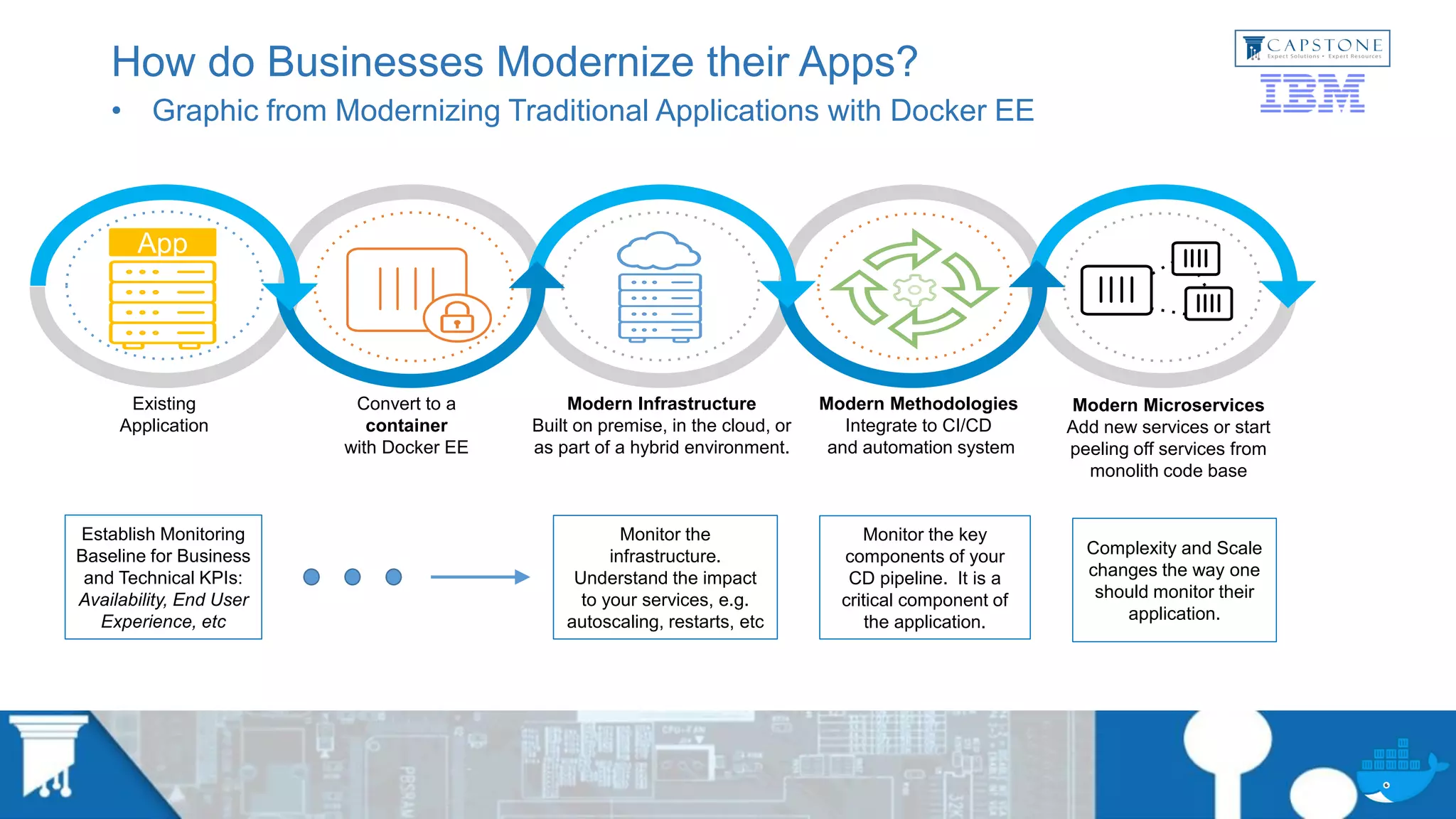
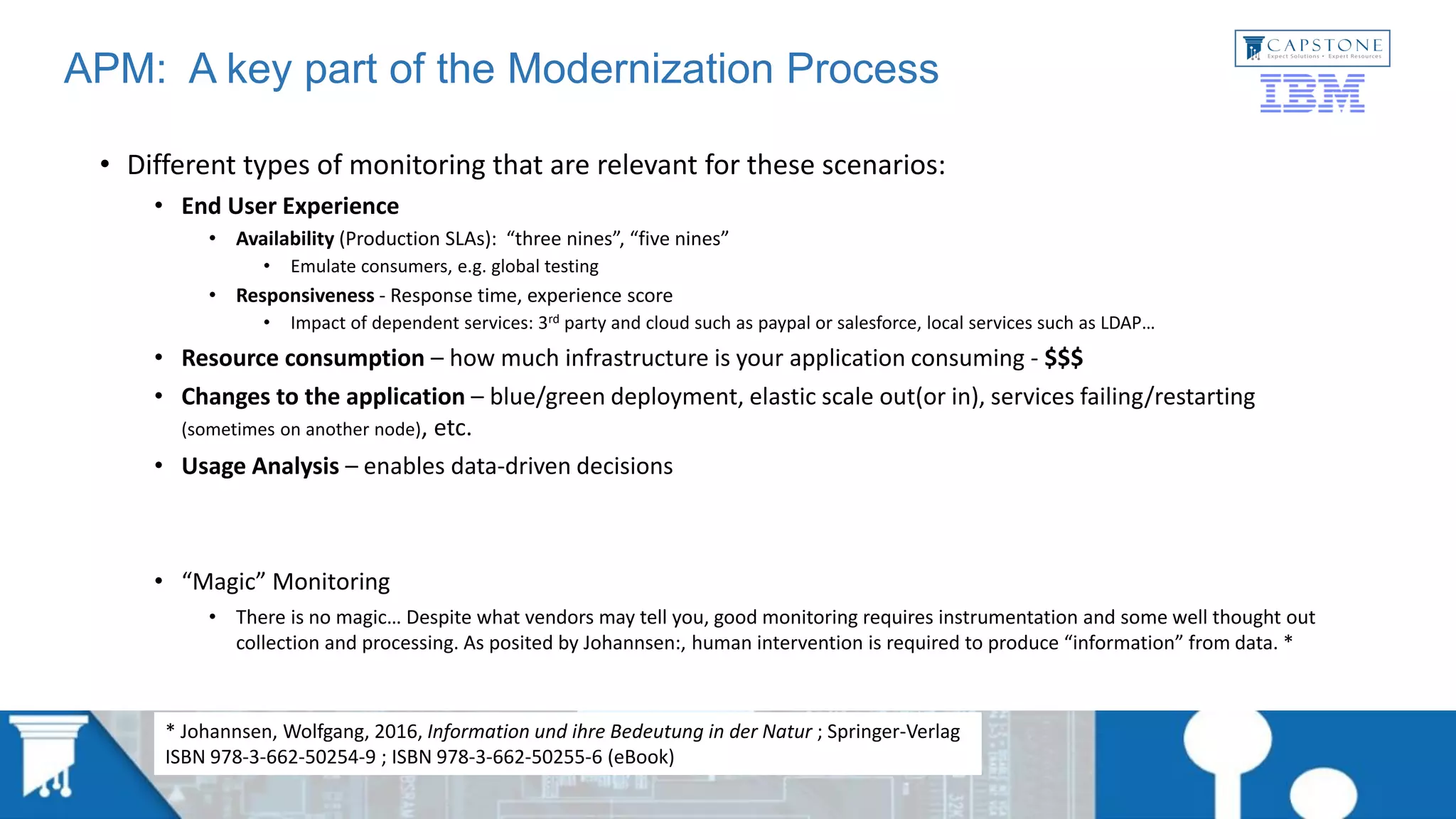
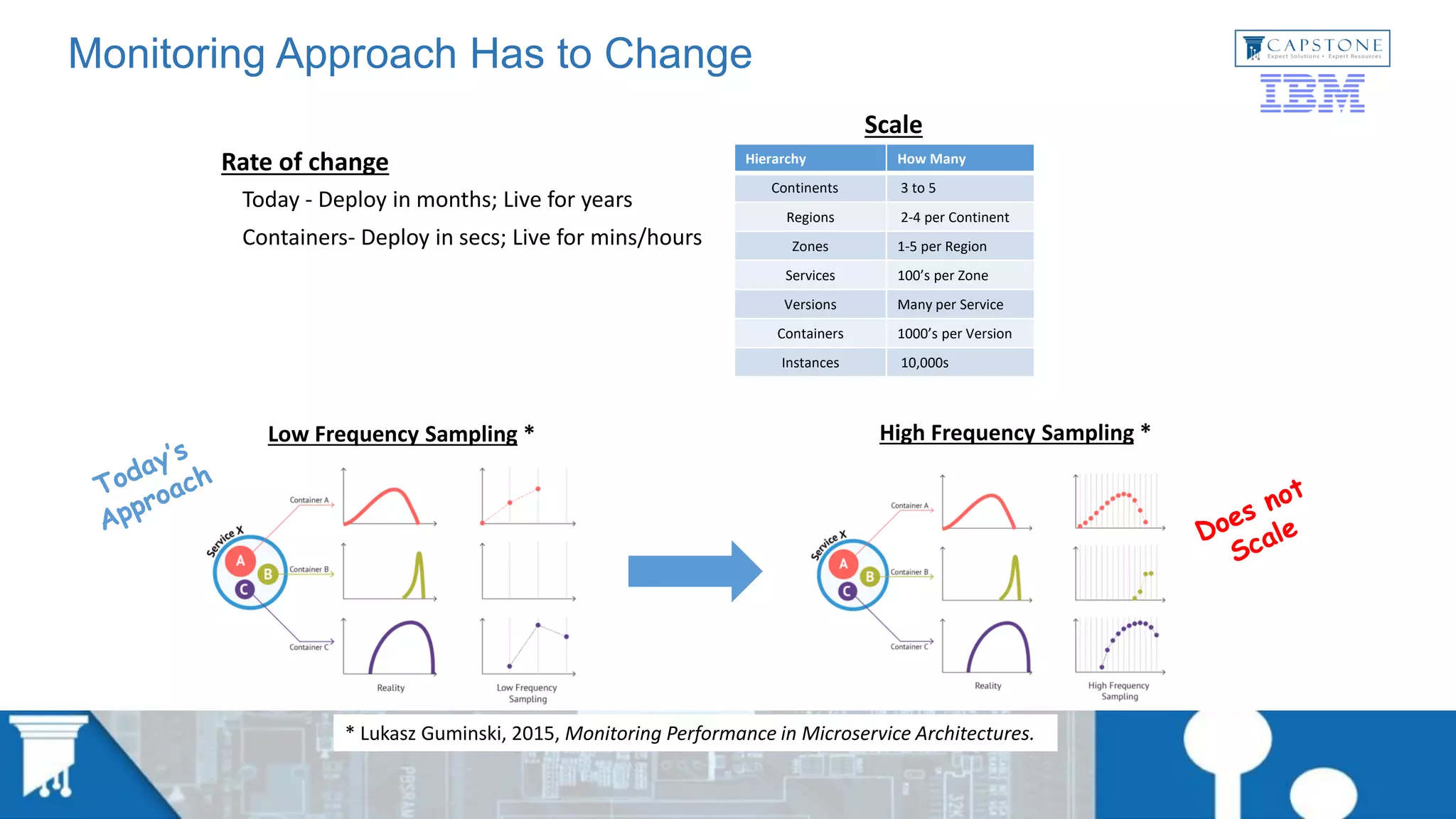
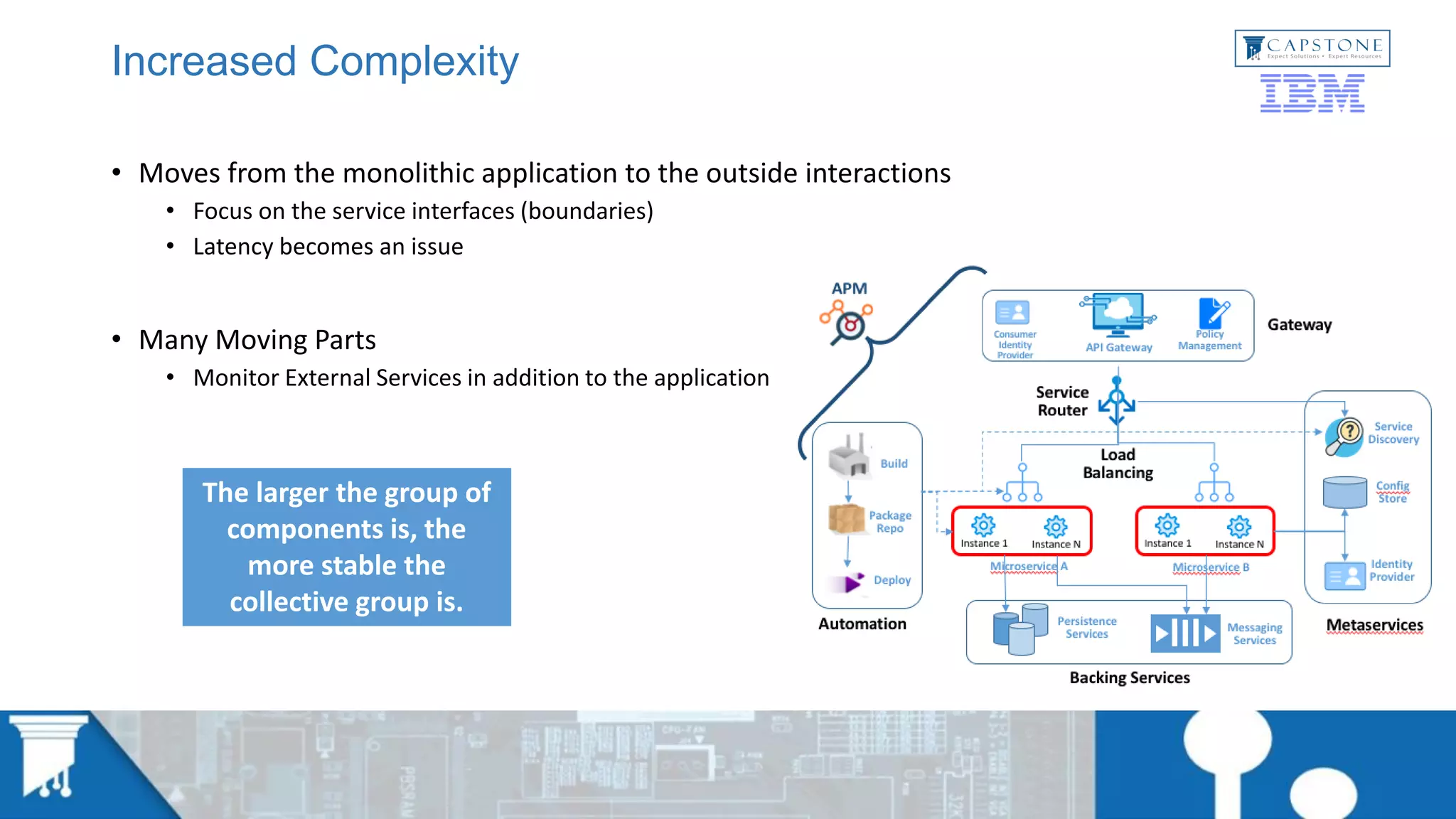
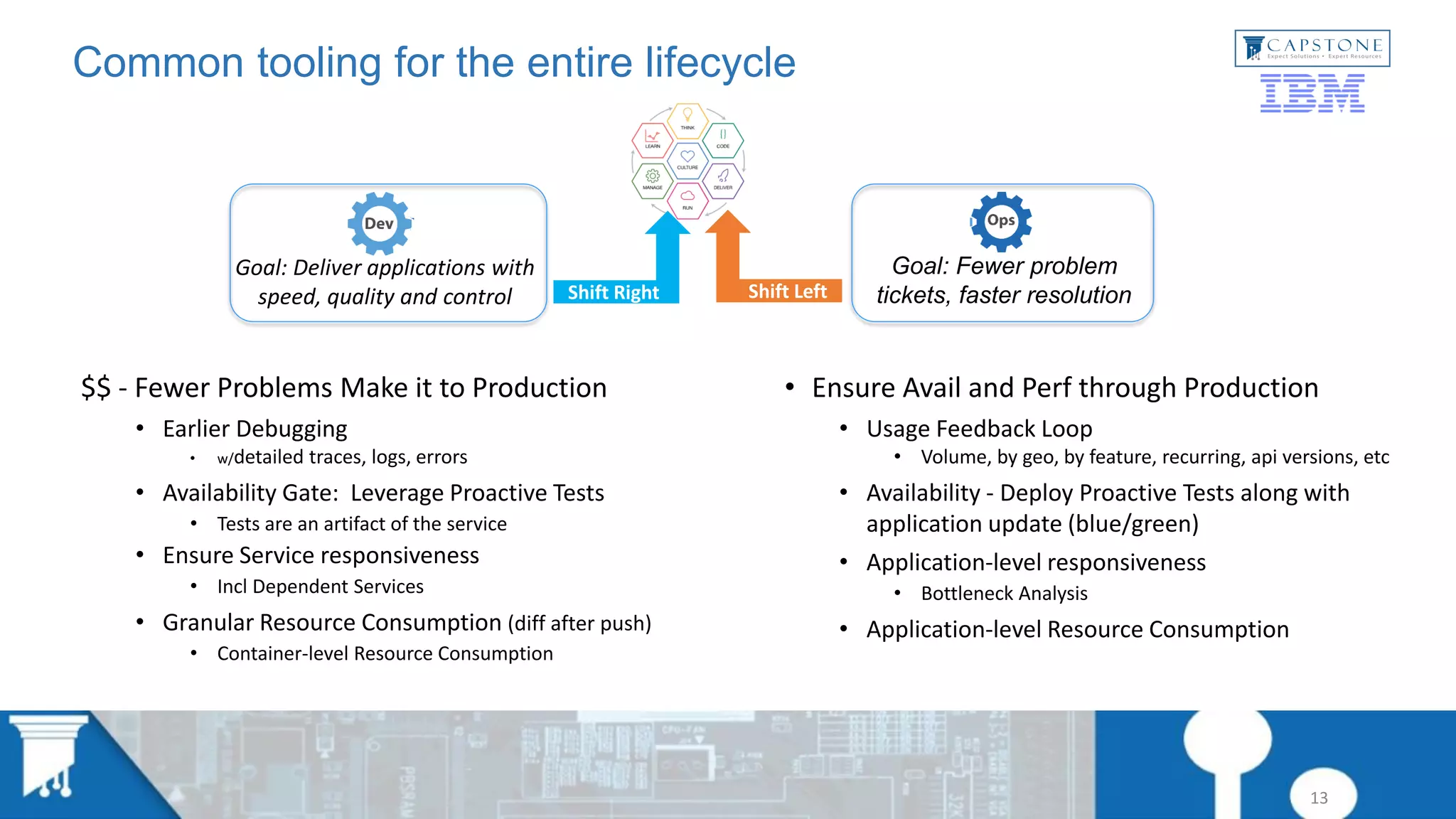
This document discusses application modernization and why application performance monitoring (APM) is important during the modernization process. It provides an overview of common business reasons for modernizing applications, such as increasing flexibility, availability, scalability and portability. The document then discusses common challenges of modernization and provides examples of how companies approach modernizing applications. It emphasizes the importance of APM throughout the modernization lifecycle to deliver applications with speed, quality and control. The document concludes with examples of client experiences modernizing applications and lessons learned regarding monitoring tools in containerized/cloud environments.