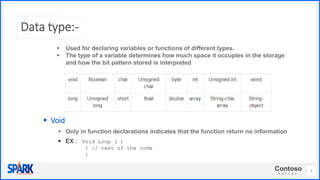
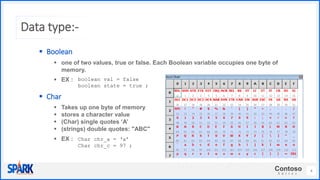
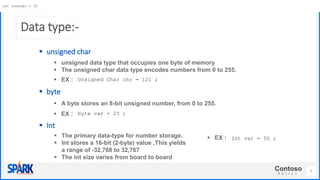
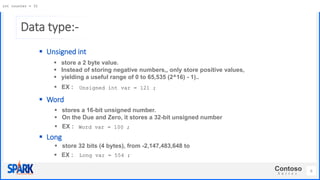
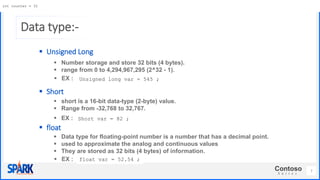
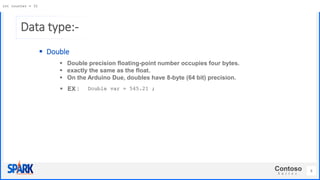
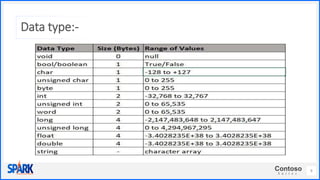
The document introduces the Arduino microcontroller board and its data types. It explains that Arduino is an open-source hardware board that contains a microcontroller and USB port to simplify creating control systems without requiring sophisticated circuit design. It then discusses the various data types used in Arduino programming, including boolean, char, byte, int, long, float, and double to store different sizes of numeric values or characters.