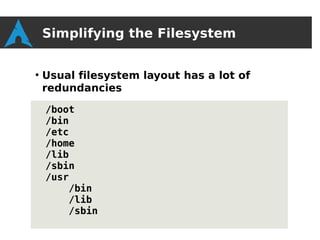
Arch Linux is a lightweight and flexible Linux distribution that offers rolling releases of packages. It aims for simplicity in package building and minimal customization from upstream sources. The community is involved in package creation and management through the Arch User Repository and Trusted Users roles. Future plans include continuing to provide timely package updates, expanding architecture support, and further simplifying the filesystem structure.
![Packaging - Repositories
[core]
●
needed for building, booting and installing
●
~200 packages
●
updates must go through the [testing]
repository
[extra]
●
commonly used packages (>5% of users)
[community]
●
less commonly used packages (>1% of
users)](https://image.slidesharecdn.com/archlinux-tgundersen-130407073604-phpapp01/85/Distro-Recipes-2013-Introduction-to-Arch-Linux-a-simple-rolling-release-distribution-10-320.jpg)
![Community - Developers
●
1 Project Leader
●
Deals with legal matters (exclusively)
●
33 Developers / Junior Developers
●
Runs infrastructure
●
Packages the packages in the official [core]
and [extra] repositories](https://image.slidesharecdn.com/archlinux-tgundersen-130407073604-phpapp01/85/Distro-Recipes-2013-Introduction-to-Arch-Linux-a-simple-rolling-release-distribution-21-320.jpg)
![Community – Trusted Users
●
37 Trusted Users (Tus)
●
Disjont form the Developers
●
Runs the Arch User Repository (AUR)
●
Packages the semi-official packages in the
[community] repository
●
Ran as a democracy, governed by formal by-
laws
●
New TUs may apply to join](https://image.slidesharecdn.com/archlinux-tgundersen-130407073604-phpapp01/85/Distro-Recipes-2013-Introduction-to-Arch-Linux-a-simple-rolling-release-distribution-23-320.jpg)
![Community – AUR
●
Repository of PKGBUILDs
●
Anyone may sign-up and upload PKGBUILDs
●
Absolutely no quality-control of the
resulting packages, but some style
guidelines on the PKGBUILDs themselves
●
Popular, high-quality PKGBUILDS are often
picked up by TU's and added to the
[community] repository](https://image.slidesharecdn.com/archlinux-tgundersen-130407073604-phpapp01/85/Distro-Recipes-2013-Introduction-to-Arch-Linux-a-simple-rolling-release-distribution-24-320.jpg)
![Example - systemd
Over the next two years...
●
Unified the legacy Arch init system and
systemd
●
systemd moved from the AUR to
[community]
●
The systemd packager was invited to join
the dev team and moved systemd to [extra]
●
systemd moved to [core]
●
The legacy init system was deprecated and
systemd is now our only supported init
system](https://image.slidesharecdn.com/archlinux-tgundersen-130407073604-phpapp01/85/Distro-Recipes-2013-Introduction-to-Arch-Linux-a-simple-rolling-release-distribution-29-320.jpg)