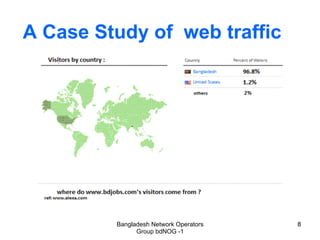
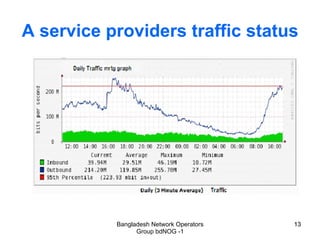
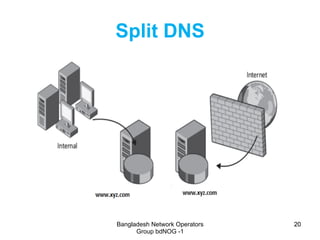
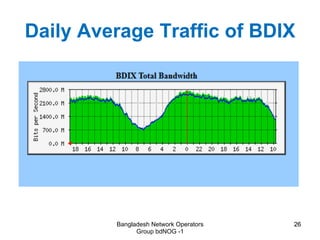
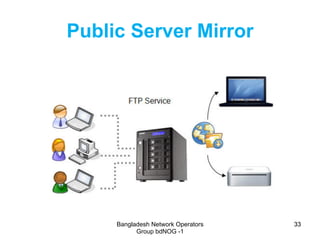
This document discusses the lack of local internet content in Bangladesh and proposes several solutions. It notes that most internet traffic and popular websites in Bangladesh originate from outside the country. It then suggests deploying local web hosting, split DNS, internet exchange points, content delivery network peering, public server mirrors, and IPv6 to help overcome this issue. This would increase local internet content, improve browsing speeds, reduce bandwidth costs, and create new economic opportunities in Bangladesh.