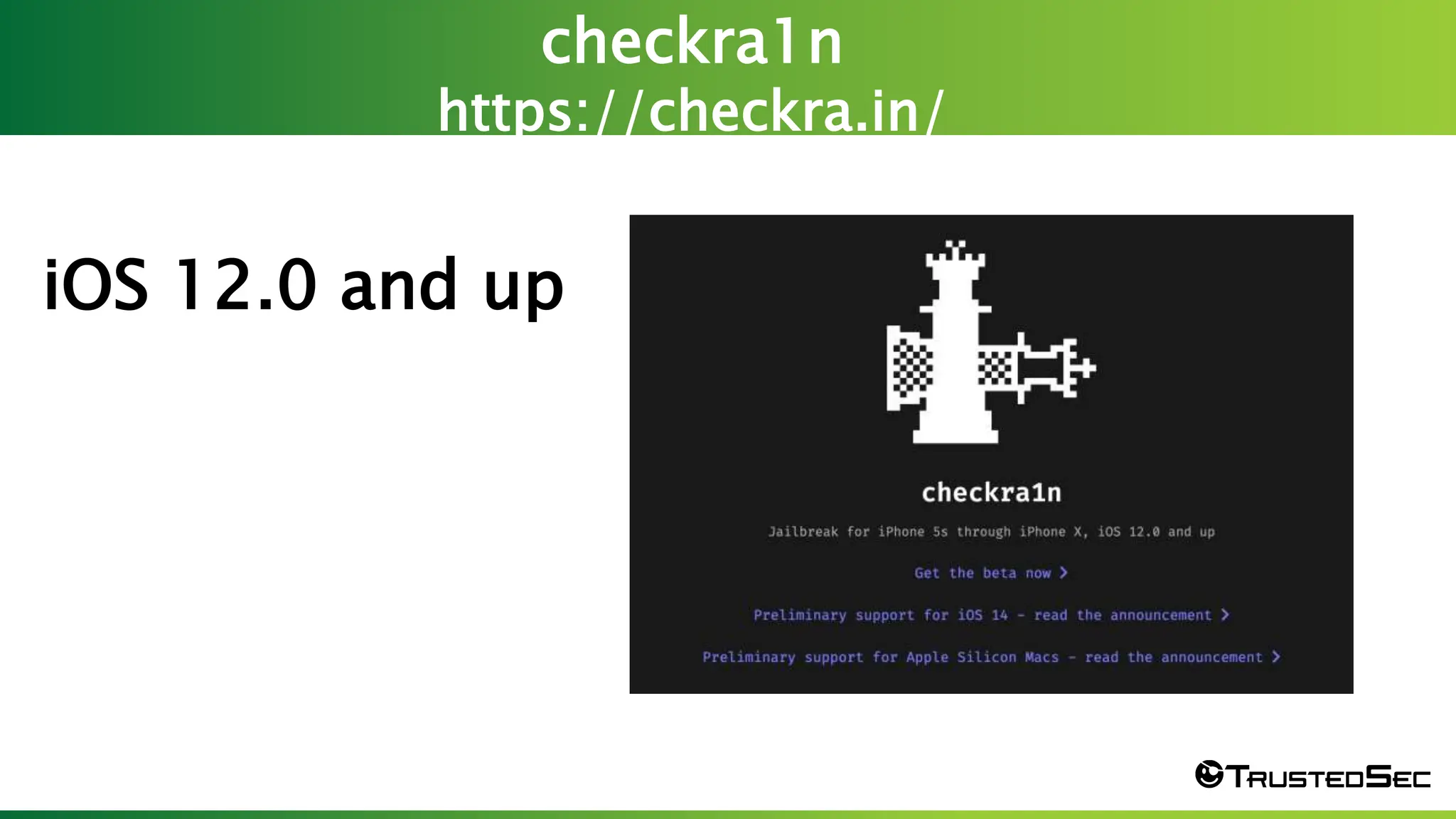
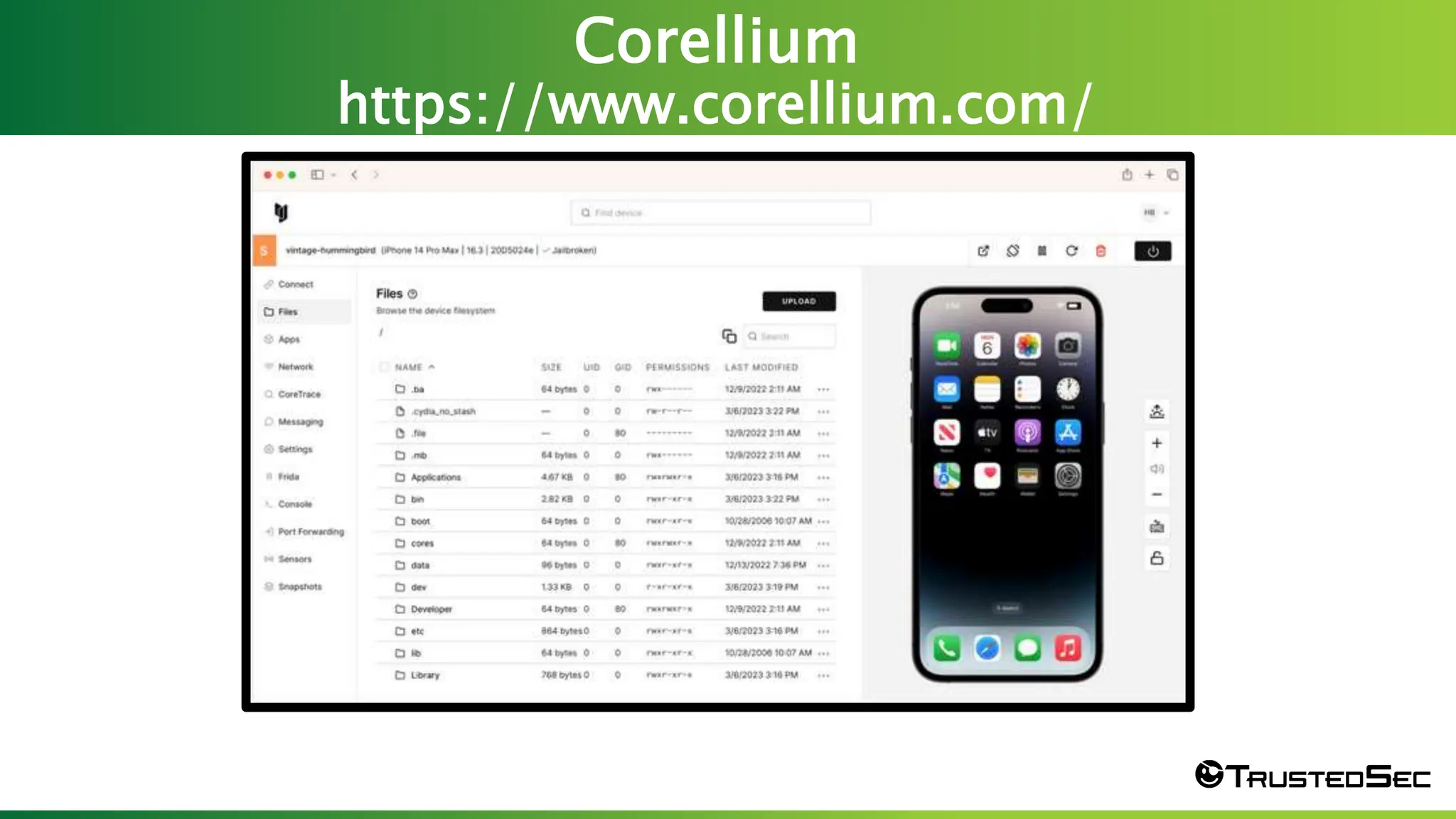
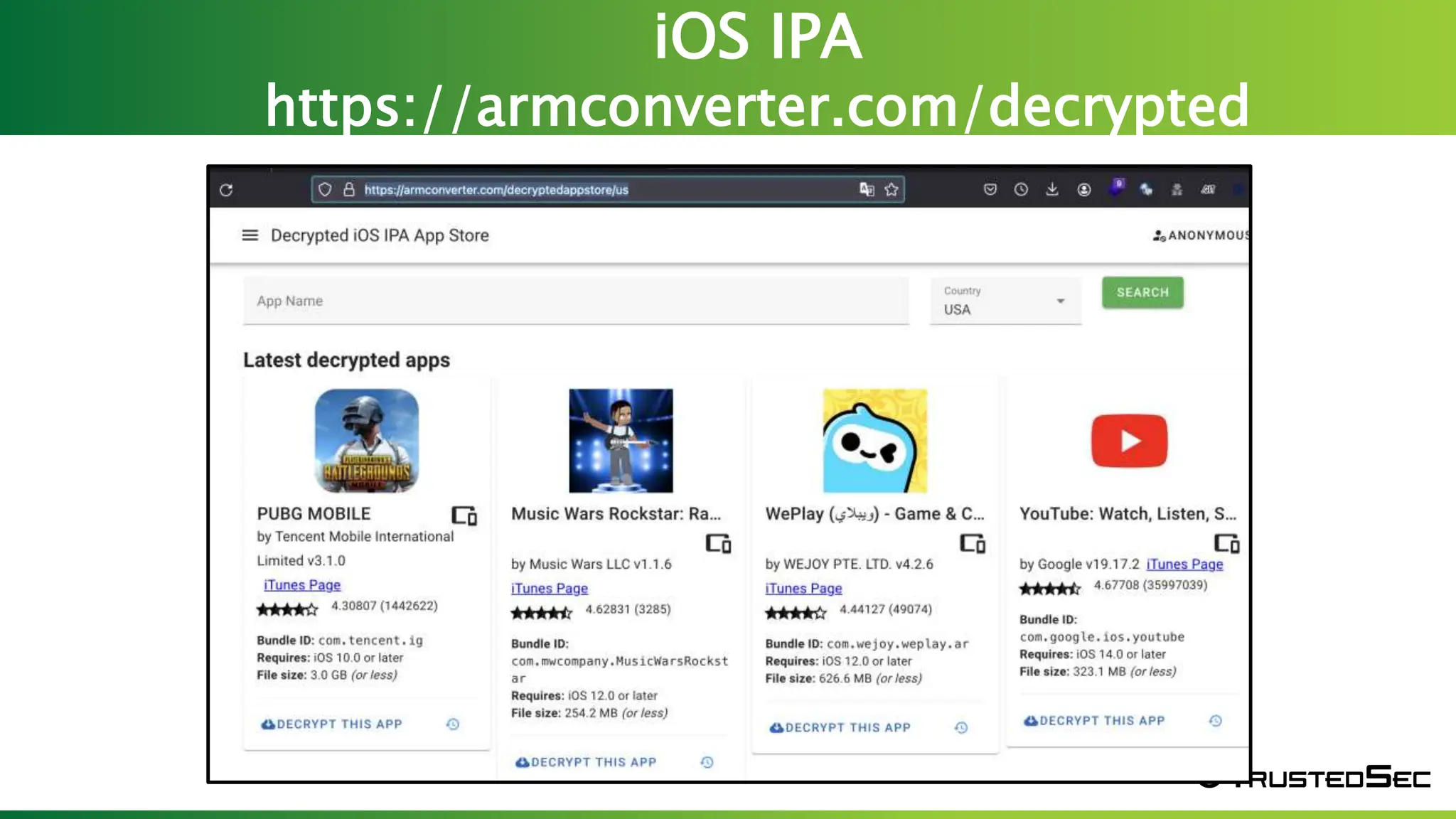
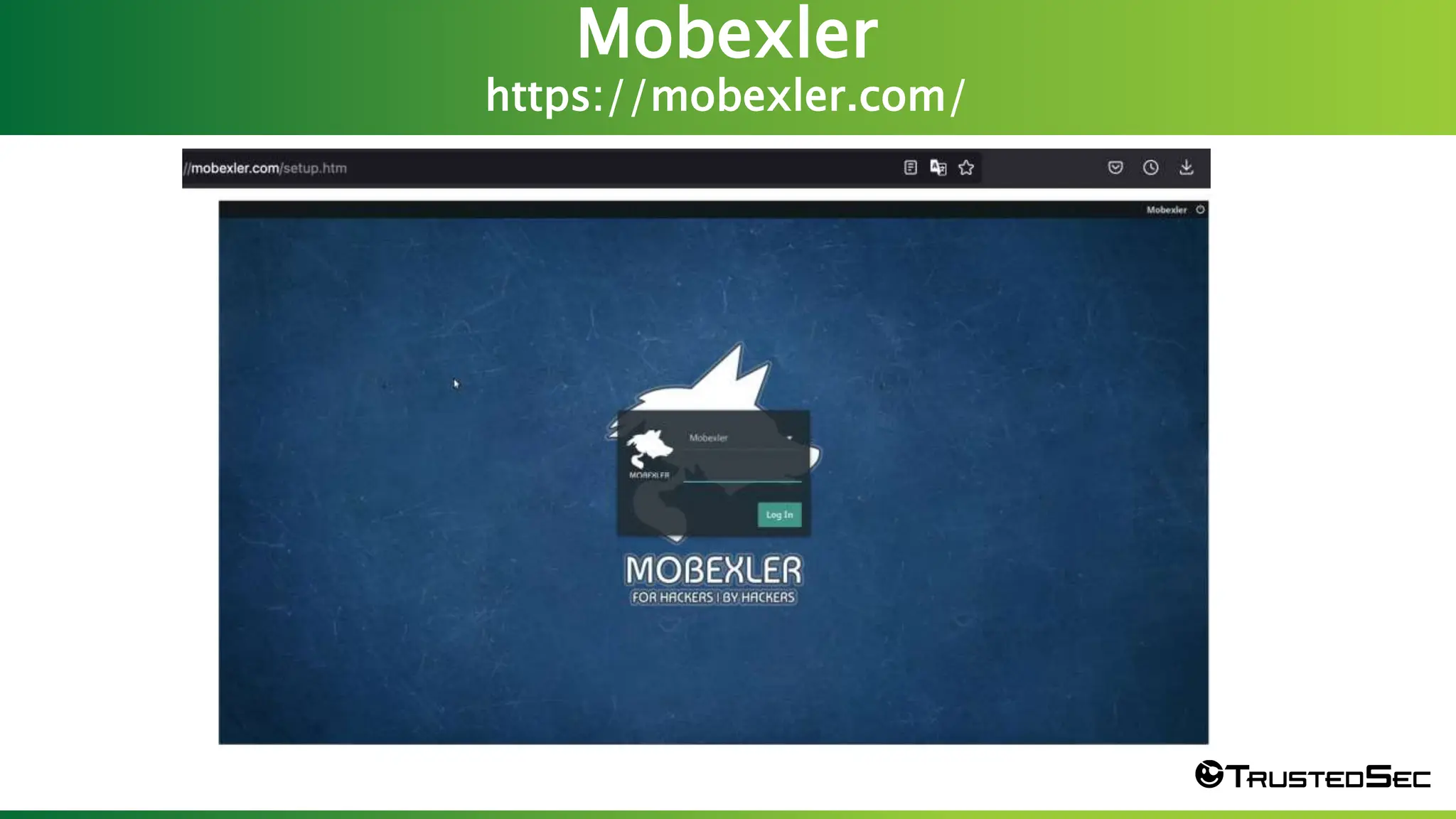
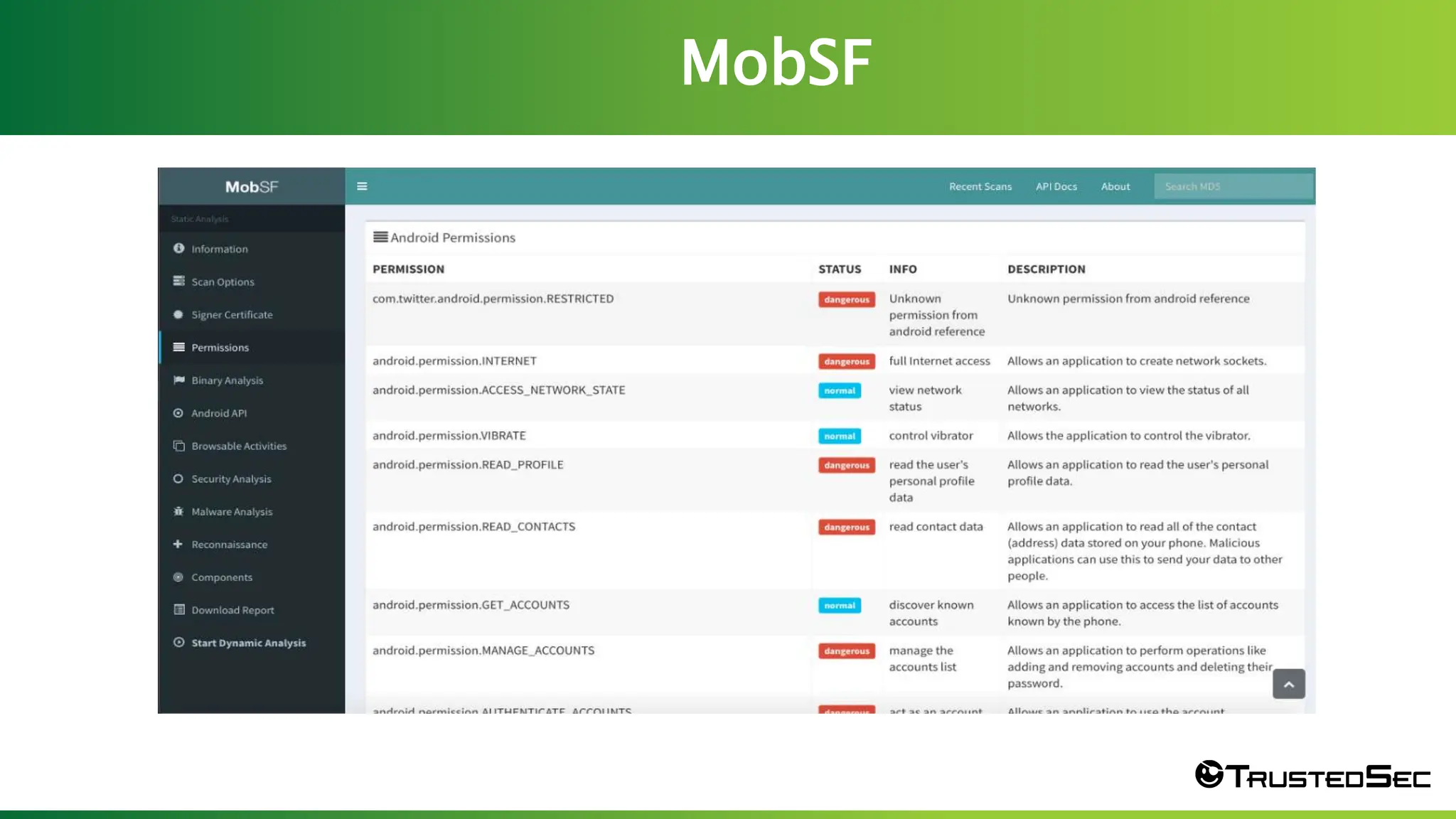
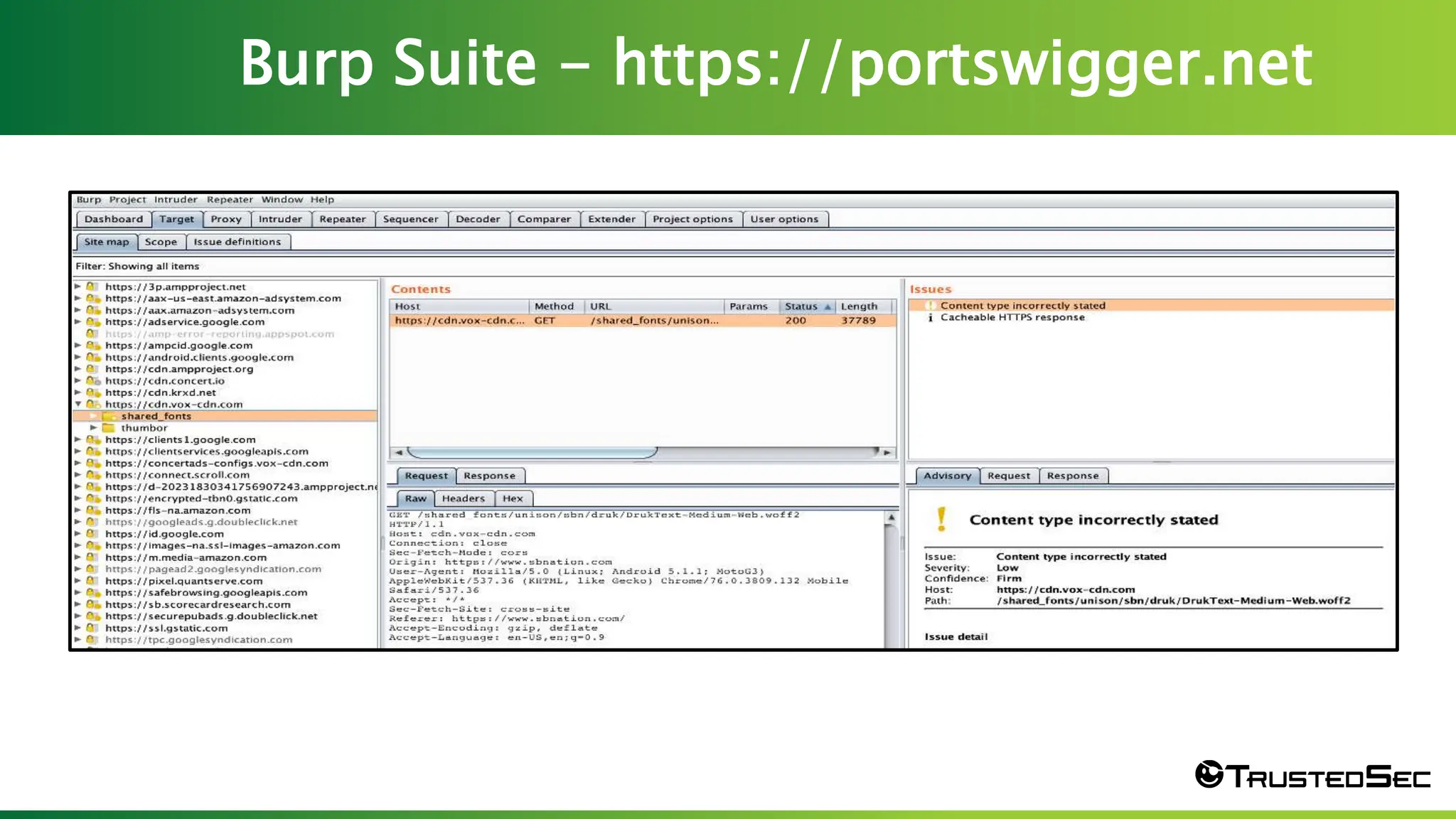
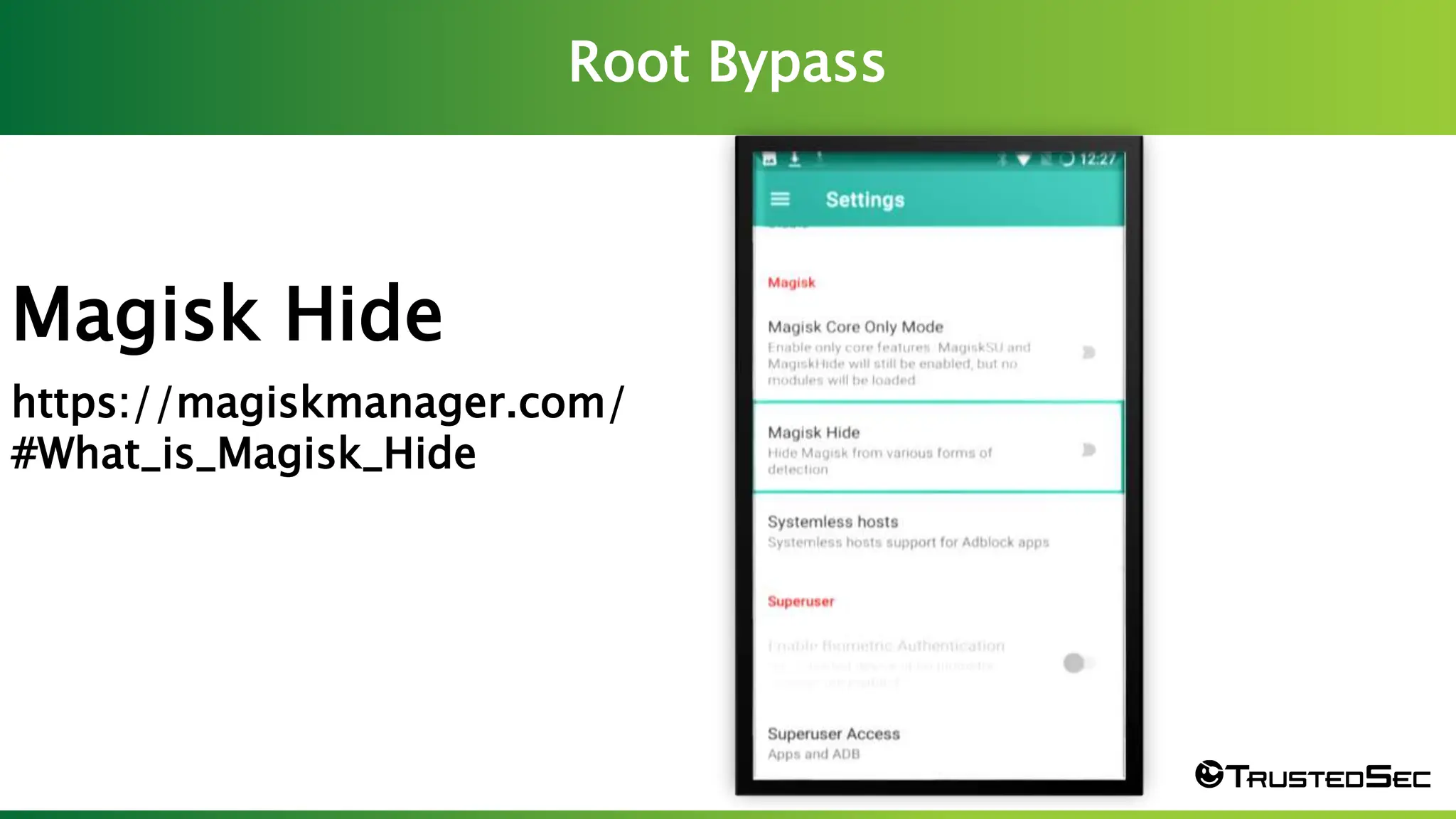
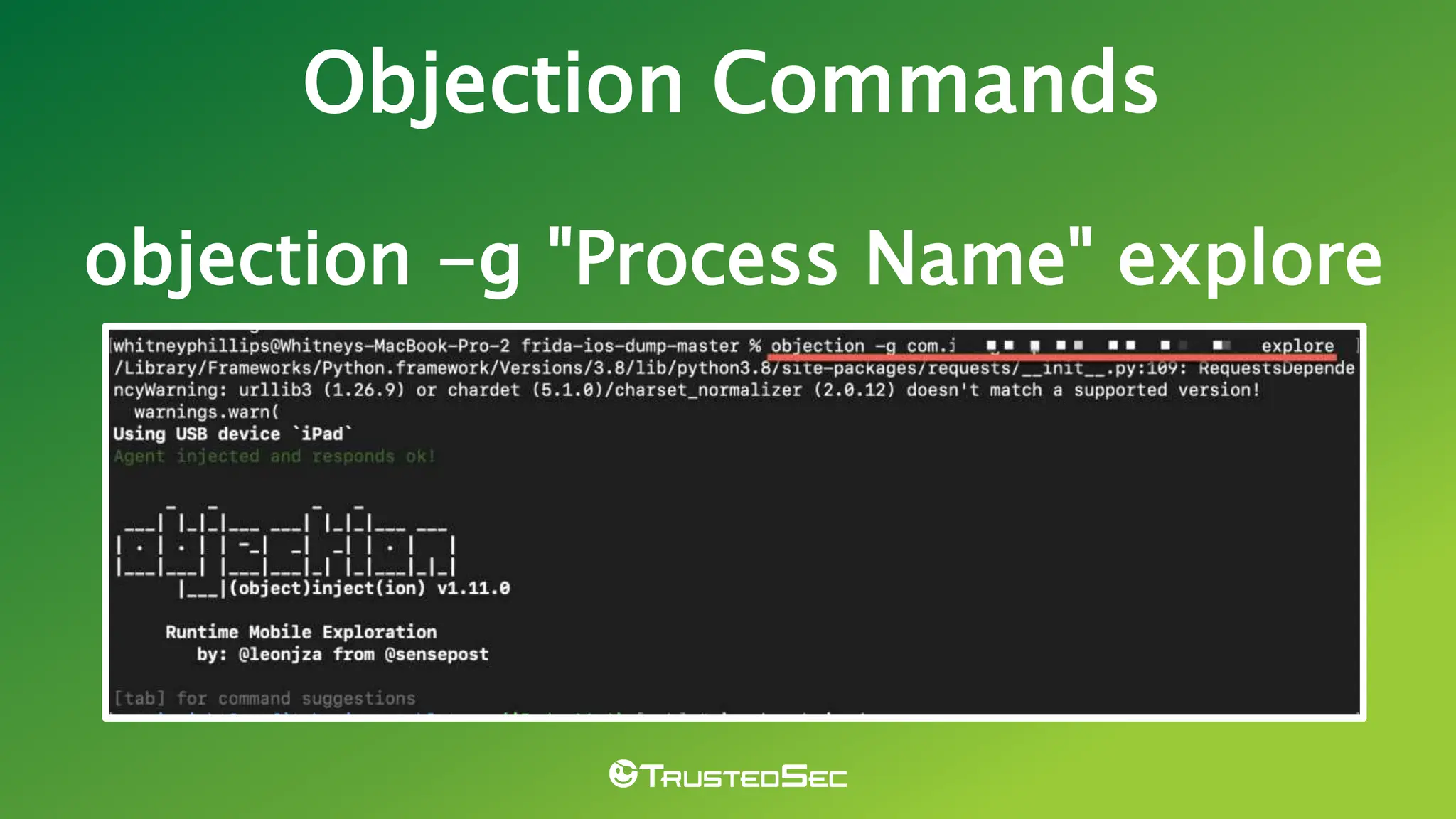
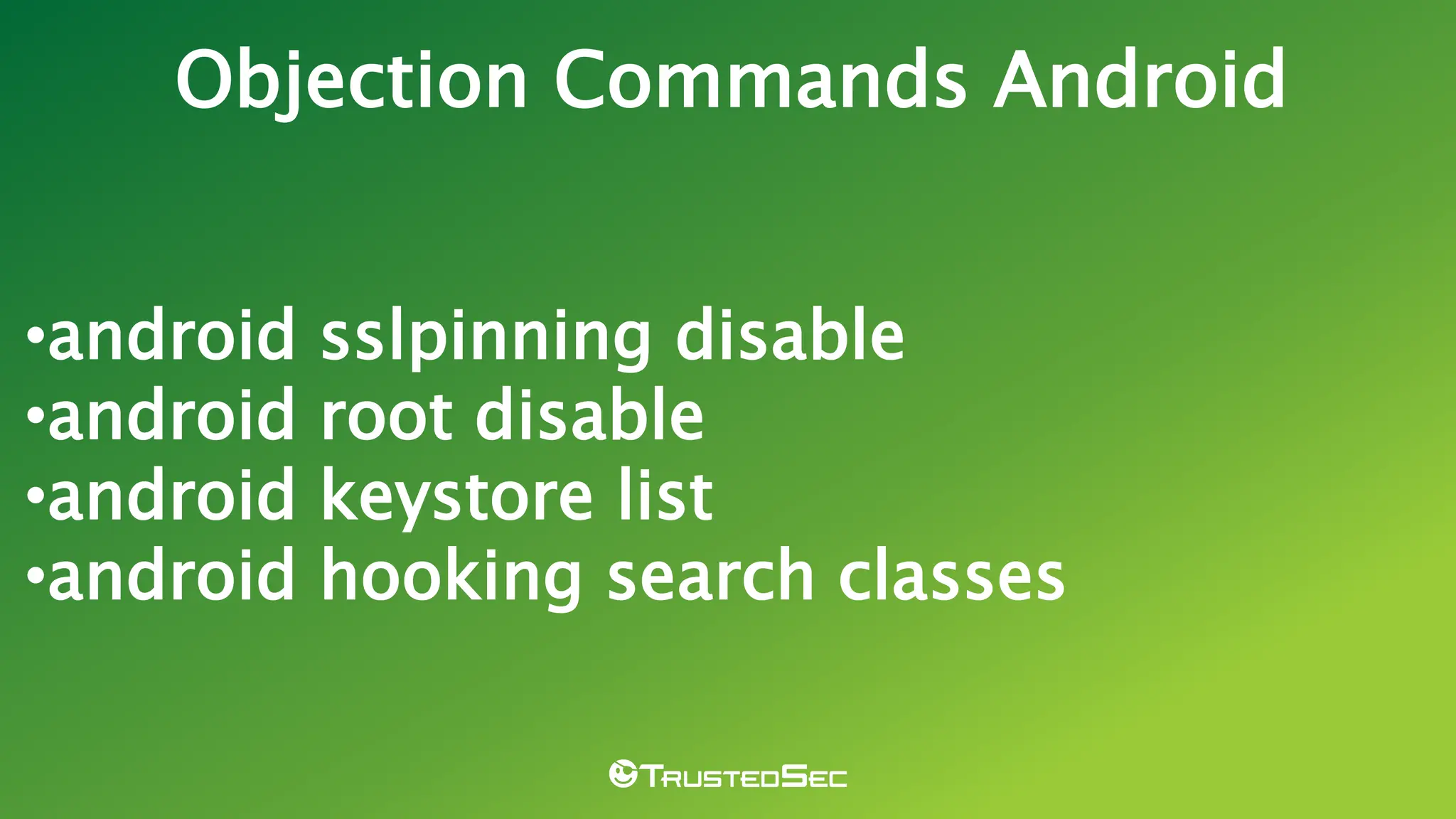
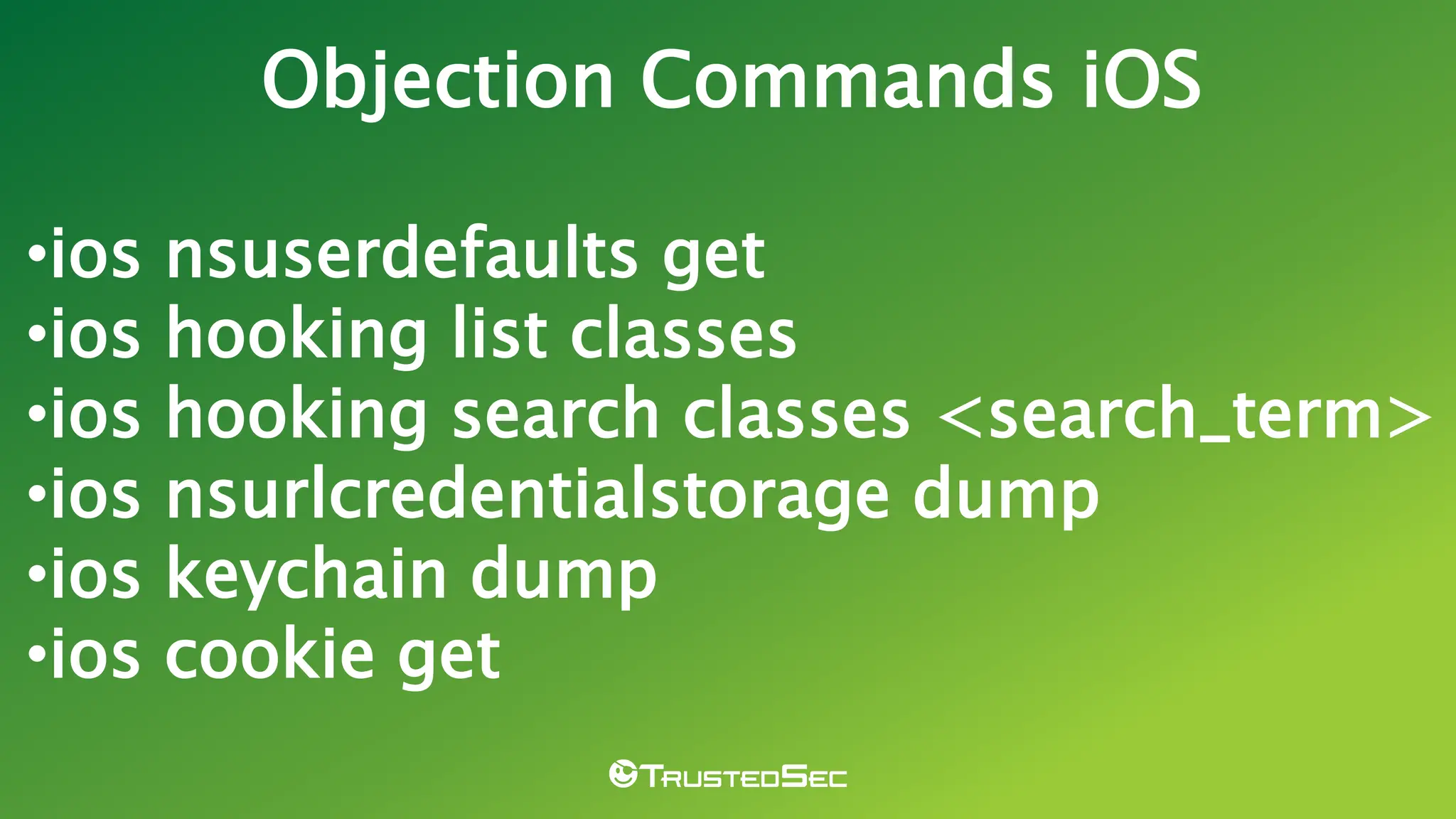
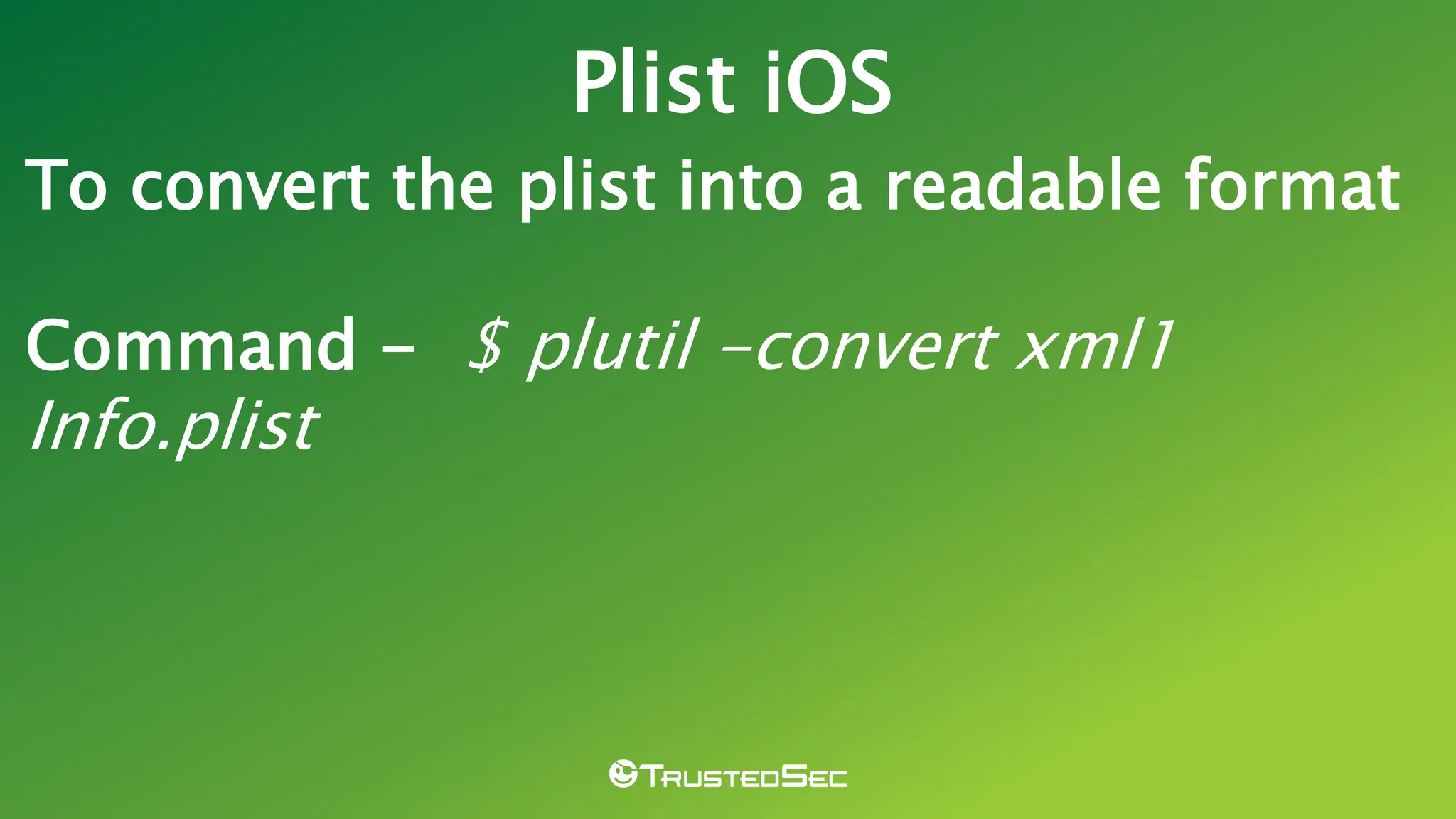
This document is a beginner's guide to mobile application penetration testing, presented by Whitney Phillips, who has over 12 years of experience in IT and information security. It covers various tools and techniques such as rooting/jailbreaking devices, obtaining and sideloading applications, and methods to bypass security features like SSL pinning. Additionally, it includes resources for further learning, including blogs and testing guides.