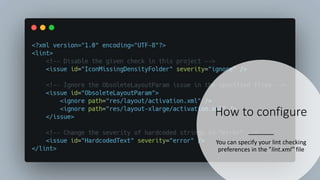
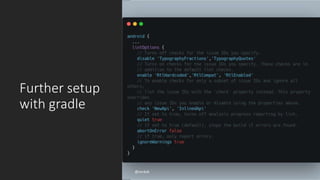
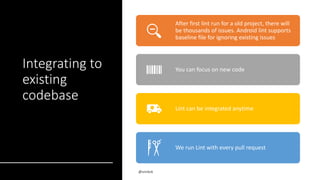
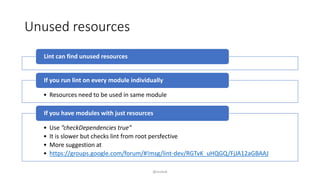
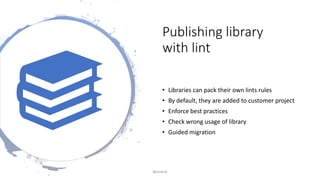
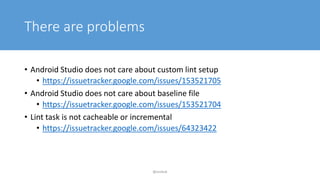
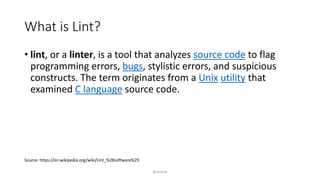
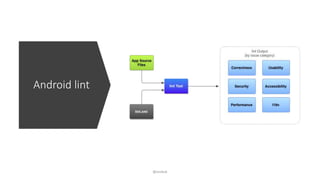
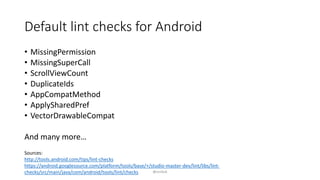
The document explains lint, a tool used for analyzing source code to identify errors and improve quality, particularly in Android development. It covers how to run lint checks, configure preferences, and integrate it into existing projects, while also mentioning the creation of custom lint rules and addressing common issues encountered. Specific lint checks and their potential impact on the build process are highlighted, along with sources for further information.

![How to run
Android lint
• ./gradlew lint
• ./gradlew lintDebug
With gradle task
• lint [flags] <project directory>
With CLI tool – “android_sdk/tools”
@snnkzk](https://image.slidesharecdn.com/androidlintpresentation-200429183620/85/Android-lint-presentation-5-320.jpg)