The document provides an overview of a data protection seminar, including:
- The agenda which covers understanding data protection law, practical tips for marketers, and a question period.
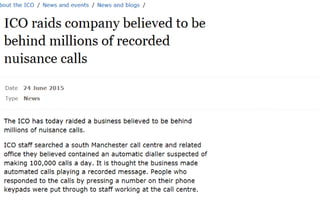
- An introduction to why data protection is important for protecting information, avoiding reputational damage, making good business sense, and avoiding enforcement actions.
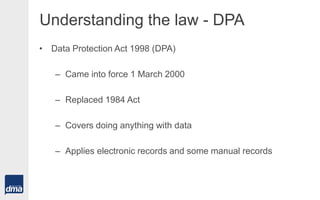
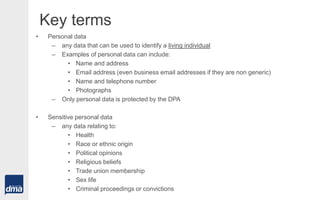
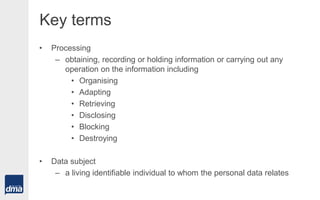
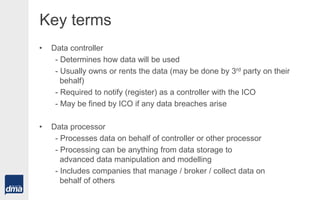
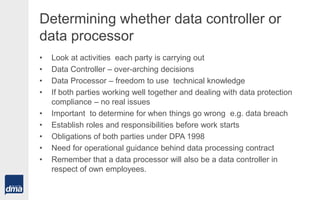
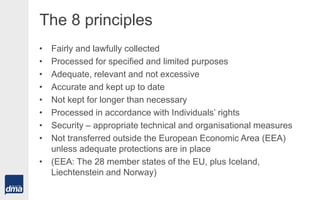
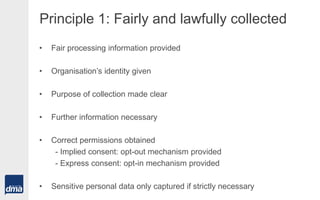
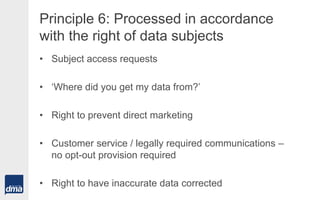
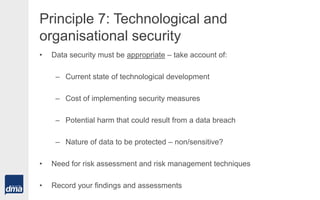
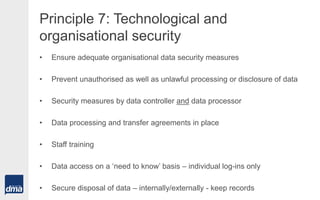
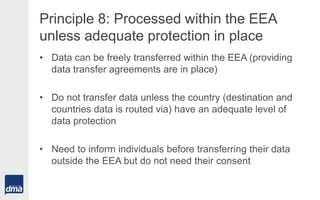
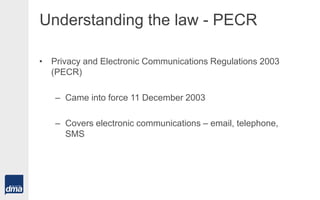
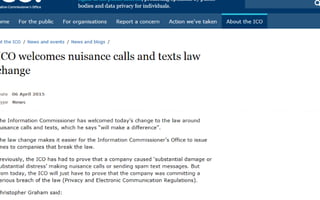
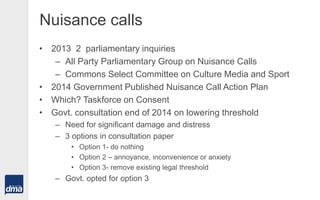
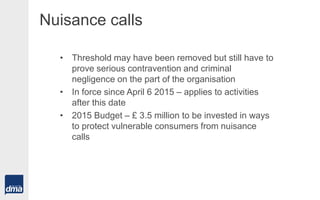
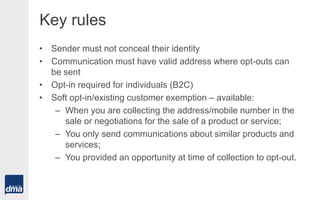
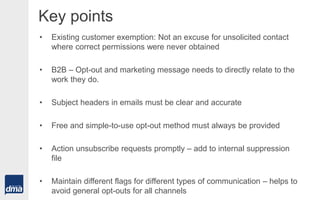
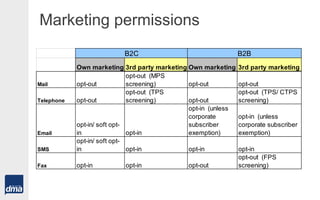
- A summary of the key aspects of the Data Protection Act 1998 and Privacy and Electronic Communications Regulation 2003, including definitions, principles, and rules regarding marketing communications.
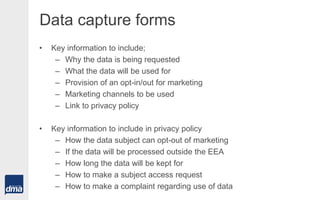
- Practical tips for marketers regarding data capture, obtaining permissions, and regaining lost permissions in compliance with regulations.