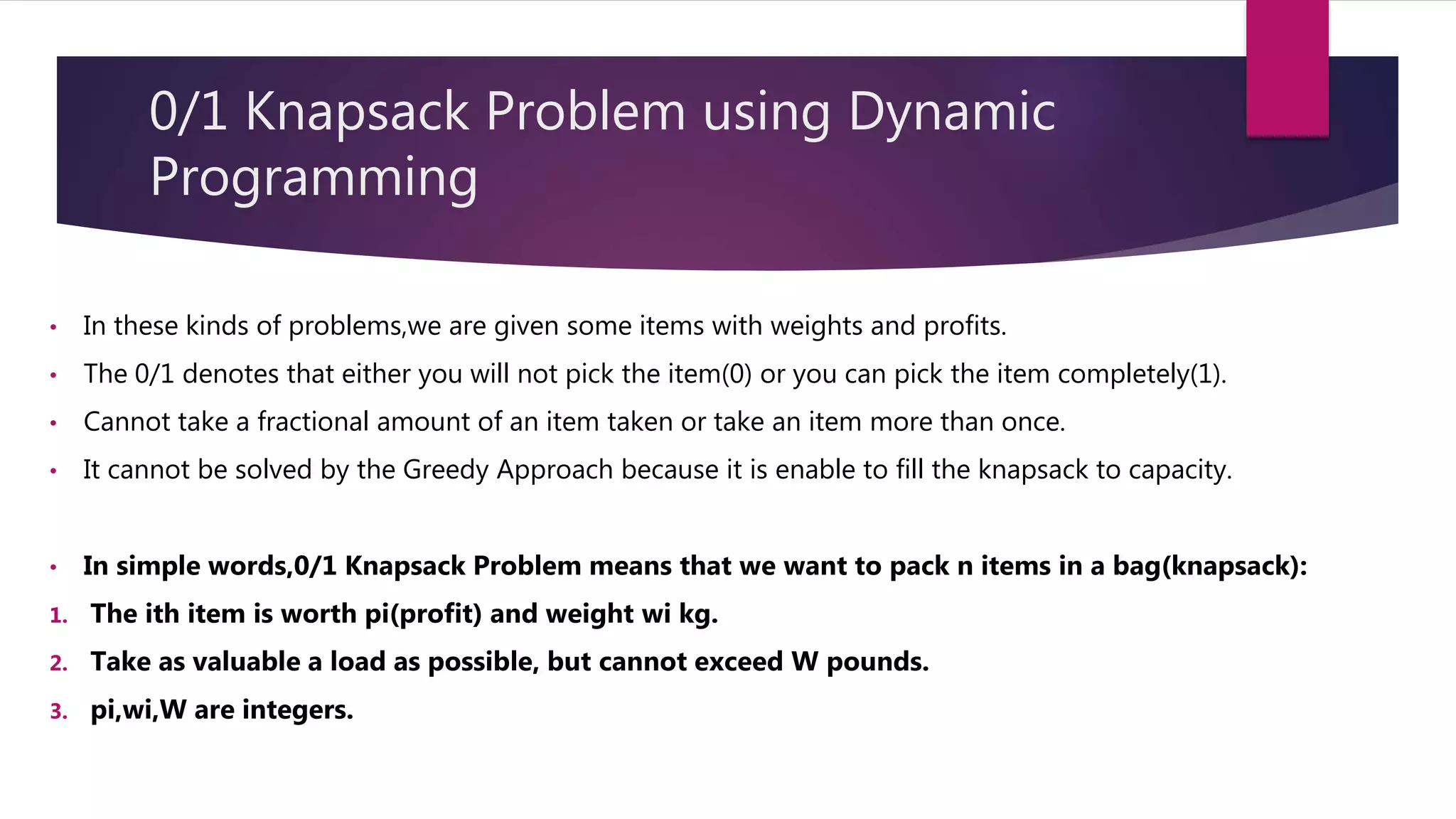
The document discusses various algorithms design approaches and patterns including divide and conquer, greedy algorithms, dynamic programming, backtracking, and branch and bound. It provides examples of each along with pseudocode. Specific algorithms discussed include binary search, merge sort, knapsack problem, shortest path problems, and the traveling salesman problem. The document is authored by Ashwin Shiv, a second year computer science student at NIT Delhi.























![Algorithm
Knapsack(n,cw)
1. int M[][] = new int[n + 1][cw + 1];//Build a memoization matrix in bottom up manner.
2. for i<-0 to n
3. for w<-0 to cw
4. if (i == 0 || w == 0) then
5. M[i][w] = 0;
6. else if(gwt[i - 1]<= w) then
7. M[i][w] = max(pro[i - 1] + M[i - 1][w - gwt[i - 1]], M[i - 1][w])
8. else
9. M[i][w] = M[i - 1][w]
10. return M[n][cw]](https://image.slidesharecdn.com/algorithmsdesignpatternsashwinshiv-210804160830/75/Algorithms-Design-Patterns-29-2048.jpg)

