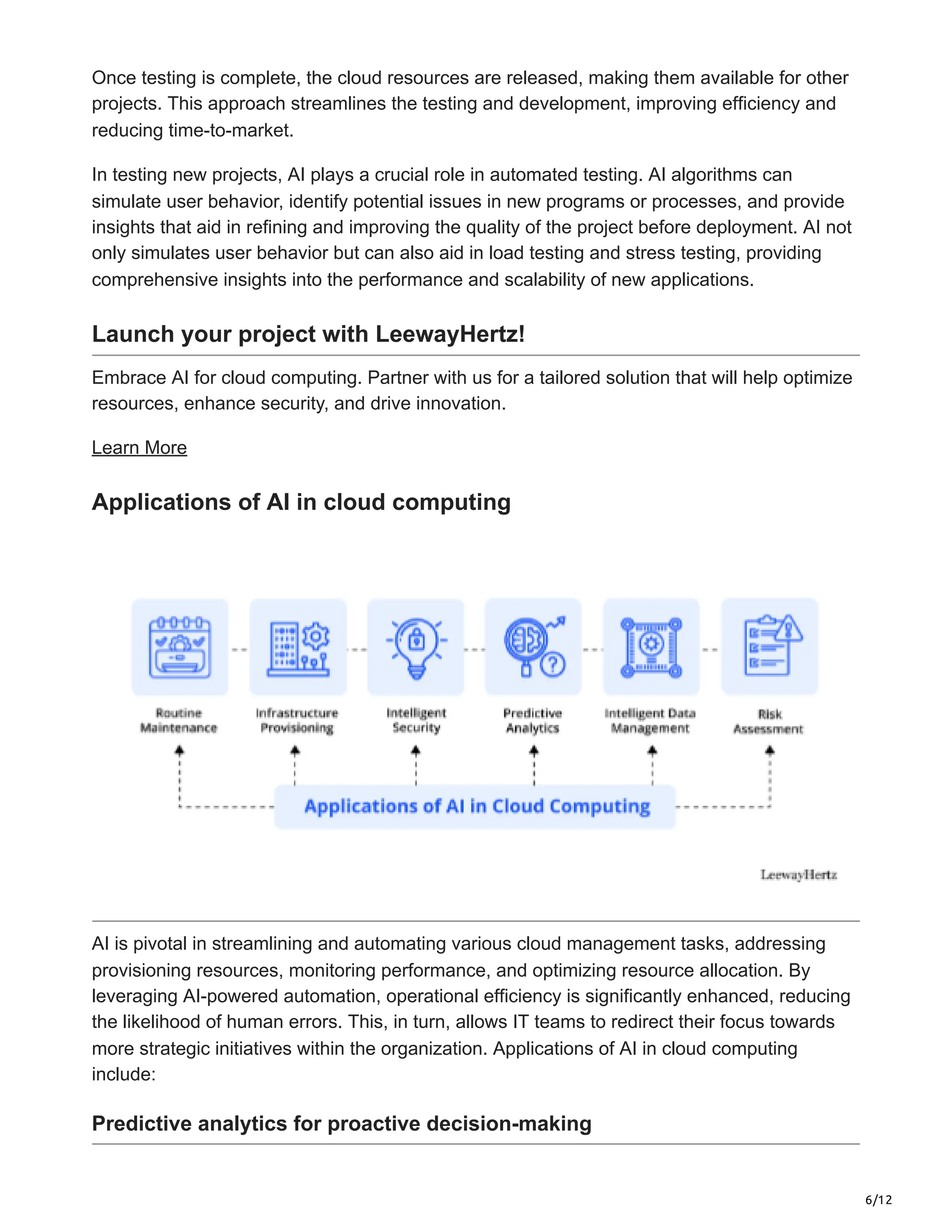
The document discusses the transformative role of cloud computing and artificial intelligence (AI) in enhancing data storage, processing, and application development. It highlights the benefits of cloud-based services, including scalability, security, and intelligent automation, while projecting significant growth in the cloud AI market. The integration of AI enhances operational efficiency, security, and resource optimization across various applications in cloud computing environments.