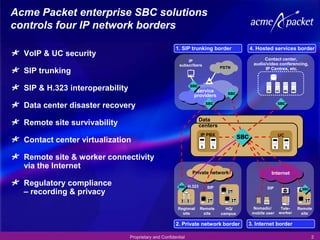
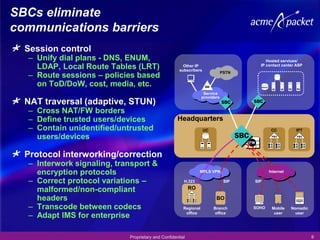
1) The document discusses Acme Packet's enterprise session border controller (SBC) solutions which control four IP network borders, including SIP trunking, private networks, public internet, and hosted services.
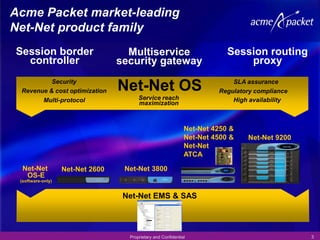
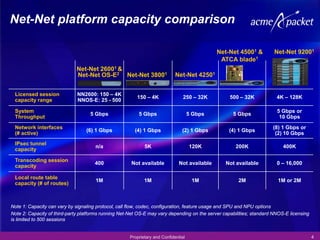
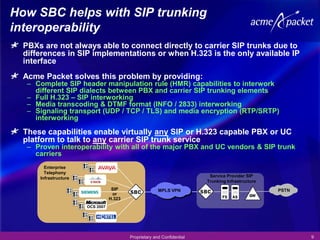
2) It provides an overview of Acme Packet's SBC product portfolio including the Net-Net product family and their session capacity, throughput, and features for securing SIP trunking and enabling interoperability.
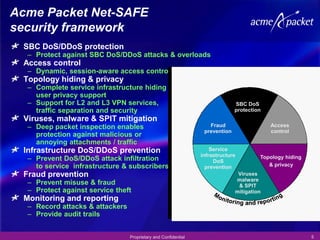
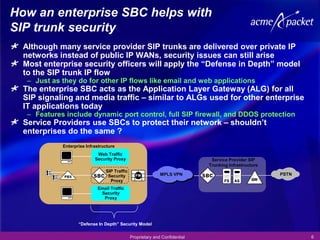
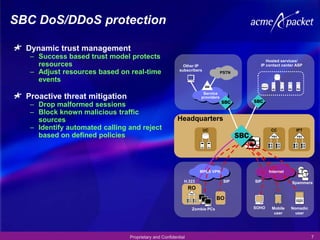
3) The SBC helps secure SIP trunking by acting as an application layer gateway, providing dynamic port control, full SIP firewalling, and DDOS protection to establish a "defense in depth" security model for SIP trunk traffic.