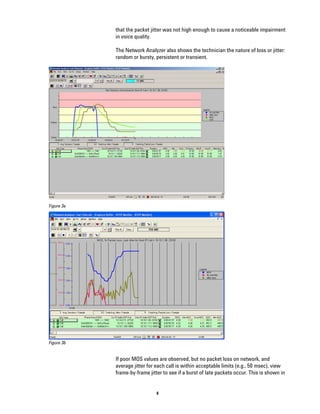
This document discusses how MPLS can help address challenges with delivering VoIP over IP networks. MPLS allows traffic engineering to provide quality of service for real-time VoIP traffic. It enables differentiation of VoIP, data, and video traffic. MPLS is used by many service providers to guarantee bandwidth for VoIP through defined label switched paths. Non-intrusive testing of VoIP quality from a single network point allows detection of customer-impacting problems for efficient diagnosis and resolution.