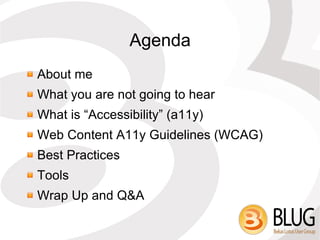
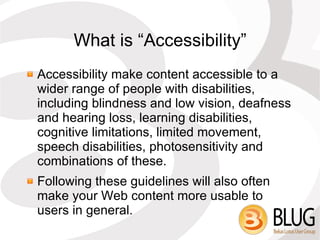
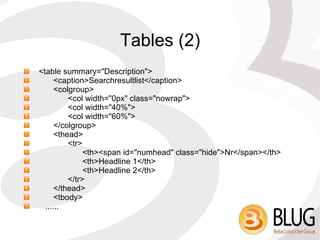
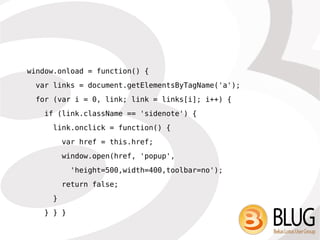
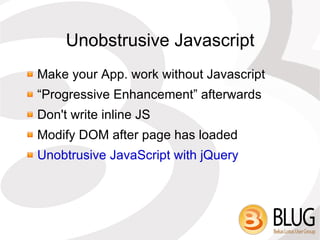
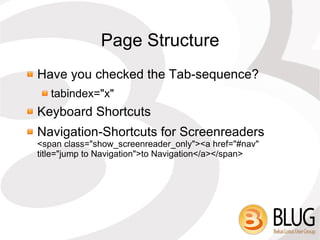
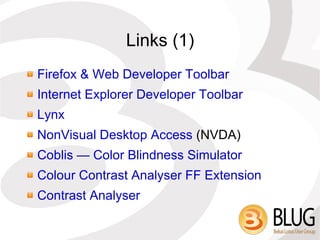
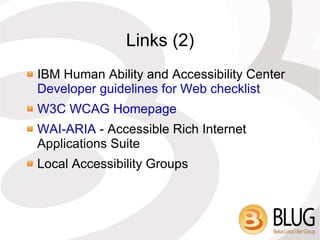
The document discusses web accessibility, emphasizing the importance of making content usable for individuals with disabilities. It highlights the Web Content Accessibility Guidelines (WCAG) and provides best practices for web developers, including the use of tables, metadata, and unobtrusive JavaScript. The author, Martin Leyrer, stresses that accessibility is an ongoing process rather than a one-time task.