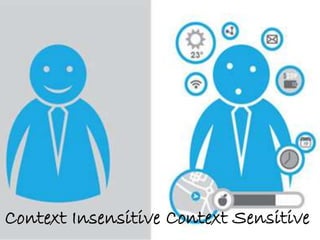
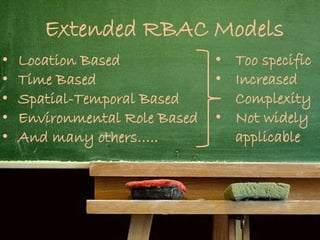
The document discusses various access control models for managing access to sensitive resources, including role-based access control (RBAC) and attribute-based access control (ABAC), highlighting their limitations and complexities. It emphasizes context-sensitive approaches that adapt to usage patterns and contextual factors for improved security in access management. Additionally, it references several studies and models exploring the integration of contextual attributes into access control mechanisms.










![References[1] Hu, Vincent C., et al. "Guide to attribute based access control (ABAC) definition
and considerations (draft)." NIST Special Publication 800 (2013): 162.
[2] Hulsebosch, R. J., et al. "Context sensitive access control." Proceedings of the
tenth ACM symposium on Access control models and technologies. ACM, 2005.
[3] Zhang, Guangsen, and Manish Parashar. "Context-aware dynamic access
control for pervasive applications." Proceedings of the Communication Networks and
Distributed Systems Modeling and Simulation Conference. 2004.
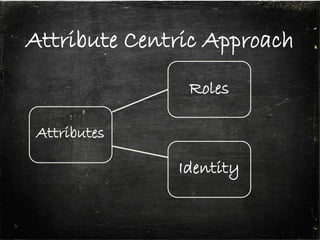
[4] Covington, Michael J., and Manoj R. Sastry. "A contextual attribute-based
access control model." On the Move to Meaningful Internet Systems 2006: OTM 2006
Workshops. Springer Berlin Heidelberg, 2006.
[5] Kulkarni, Devdatta, and Anand Tripathi. "Context-aware role-based access
control in pervasive computing systems." Proceedings of the 13th ACM symposium on
Access control models and technologies. ACM, 2008.
[6] Martin, Hervé. "A generalized context-based access control model for pervasive
environments." Proceedings of the 2nd SIGSPATIAL ACM GIS 2009 International
Workshop on Security and Privacy in GIS and LBS. ACM, 2009.
[7] Ferraiolo, David F., et al. "Proposed NIST standard for role-based access
control." ACM Transactions on Information and System Security (TISSEC) 4.3 (2001):
224-274.](https://image.slidesharecdn.com/accesscontrol-150202035111-conversion-gate01/85/Access-control-27-320.jpg)
![References[8] Hansen, Frode, and Vladimir Oleshchuk. "SRBAC: A spatial role-based access
control model for mobile systems." Proceedings of the 7th Nordic Workshop on Secure IT
Systems (NORDSEC’03). 2003.
[9] Covington, Michael J., et al. "Securing context-aware applications using
environment roles." Proceedings of the sixth ACM symposium on Access control models
and technologies. ACM, 2001.
[10] Ray, Indrakshi, Mahendra Kumar, and Lijun Yu. "LRBAC: a location-aware
role-based access control model." Information Systems Security. Springer Berlin
Heidelberg, 2006. 147-161.
[11] Ray, Indrakshi, and Manachai Toahchoodee. "A spatio-temporal role-based
access control model." Data and Applications Security XXI. Springer Berlin Heidelberg,
2007. 211-226.
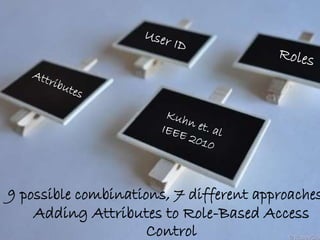
[12] Kuhn, D. Richard, Edward J. Coyne, and Timothy R. Weil. "Adding attributes
to role-based access control." Computer 43.6 (2010): 79-81.
[13] Kim, Young-Gab, et al. "Context-aware access control mechanism for ubiquitous
applications." Advances in Web Intelligence. Springer Berlin Heidelberg, 2005. 236-242.
[14] Shen, Hai-bo, and Fan Hong. "An attribute-based access control model for web
services." Parallel and Distributed Computing, Applications and Technologies, 2006.
PDCAT'06. Seventh International Conference on. IEEE, 2006.
[15] Al-Muhtadi, Jalal, et al. "Cerberus: a context-aware security scheme for smart
spaces." Pervasive Computing and Communications, 2003.(PerCom 2003). Proceedings of
the First IEEE International Conference on. IEEE, 2003.](https://image.slidesharecdn.com/accesscontrol-150202035111-conversion-gate01/85/Access-control-28-320.jpg)

