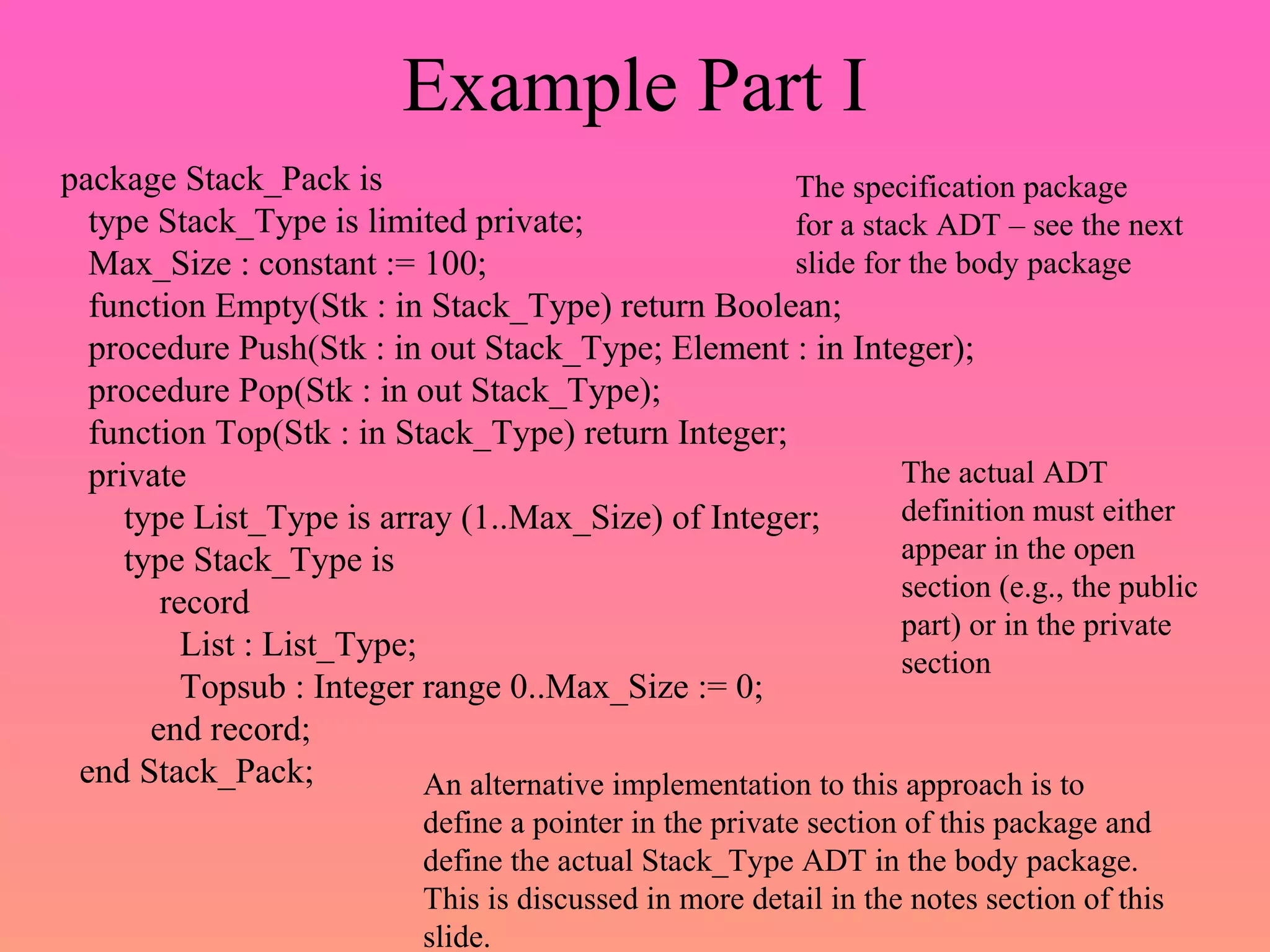
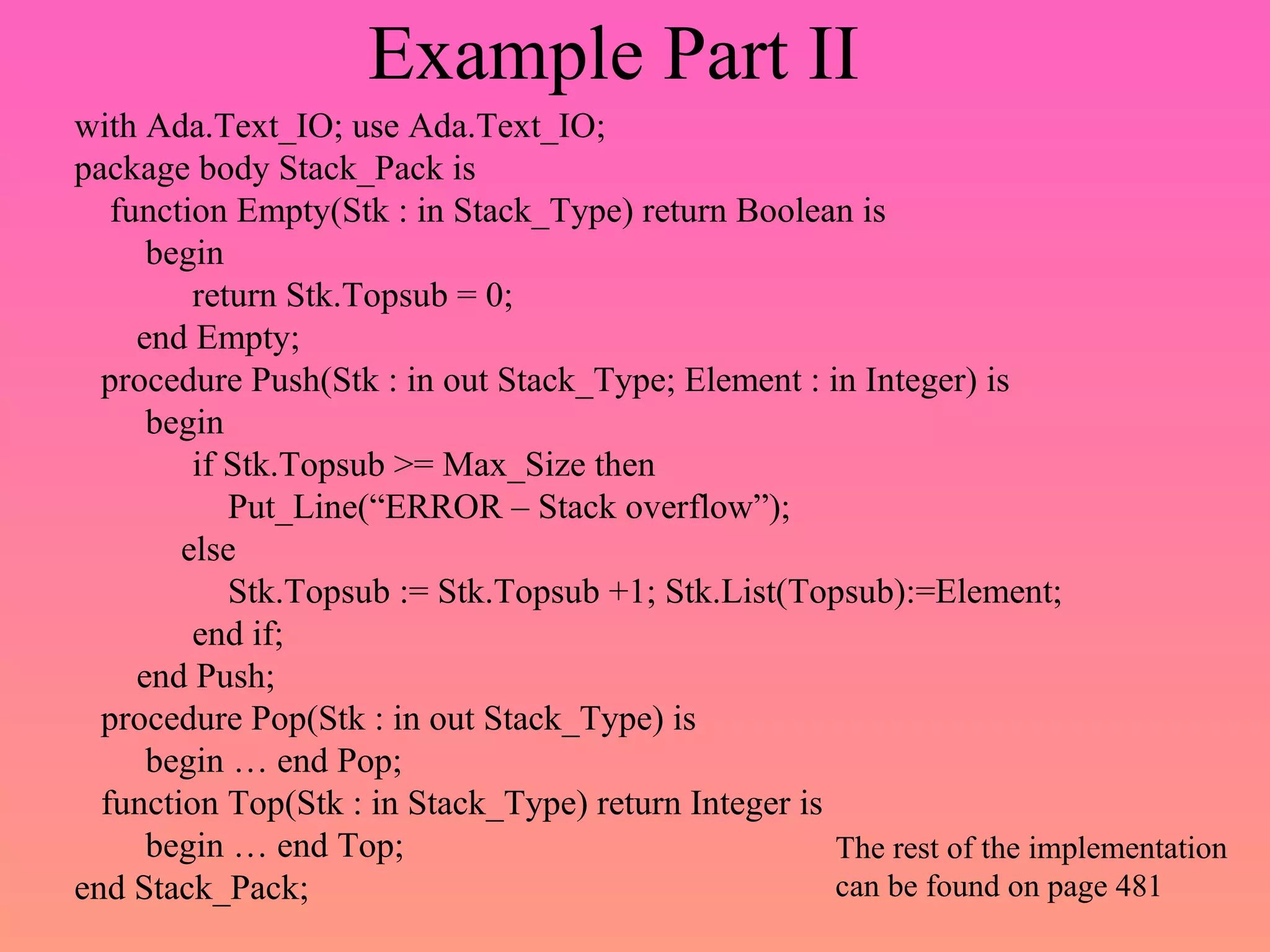
This document discusses abstract data types (ADTs) and their implementation in various programming languages. It covers the key concepts of ADTs including data abstraction, encapsulation, information hiding, and defining the public interface separately from the private implementation. It provides examples of ADTs implemented using modules in Modula-2, packages in Ada, classes in C++, generics in Java and C#, and classes in Ruby. Parameterized and encapsulation constructs are also discussed as techniques for implementing and organizing ADTs.
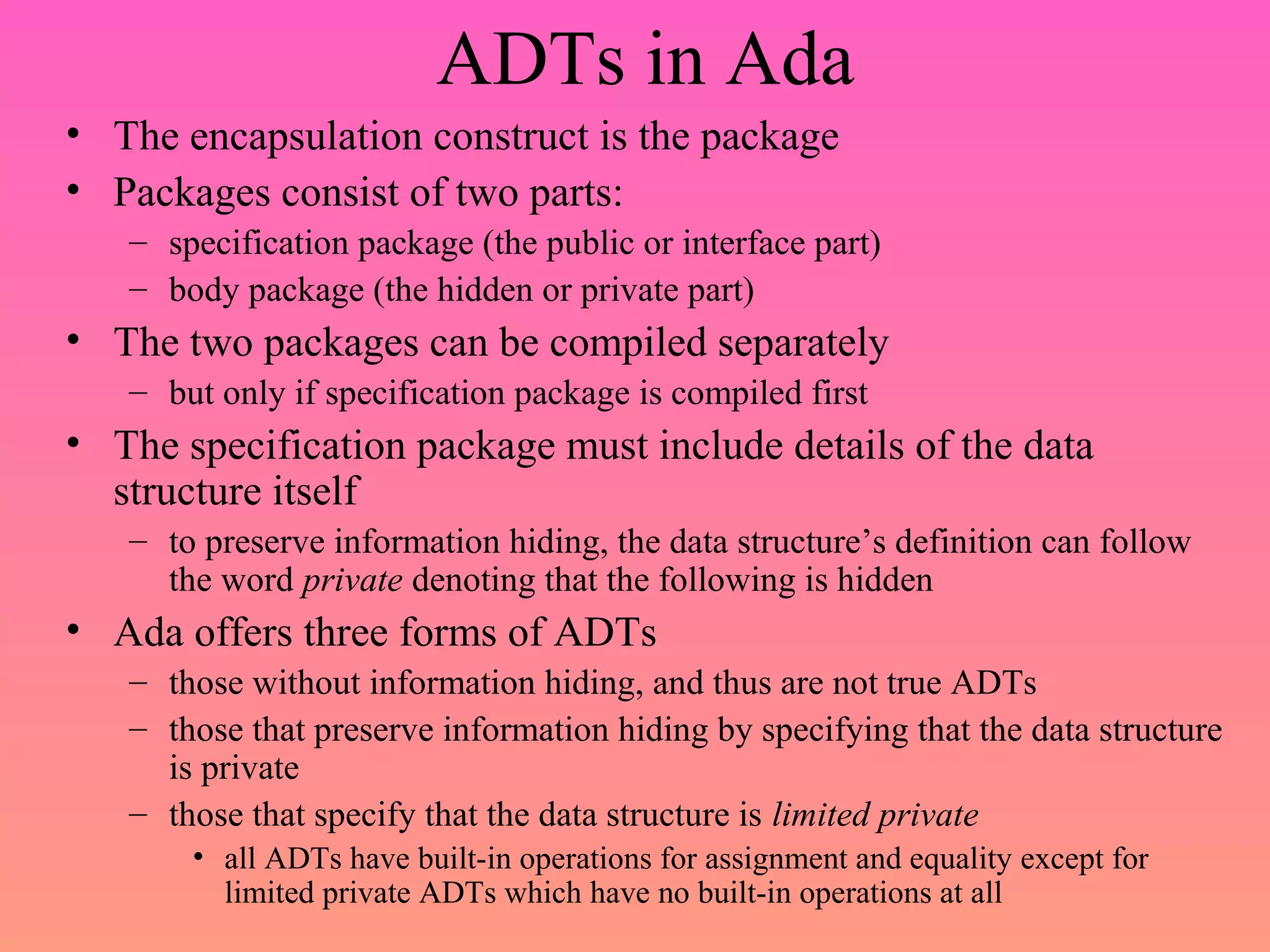
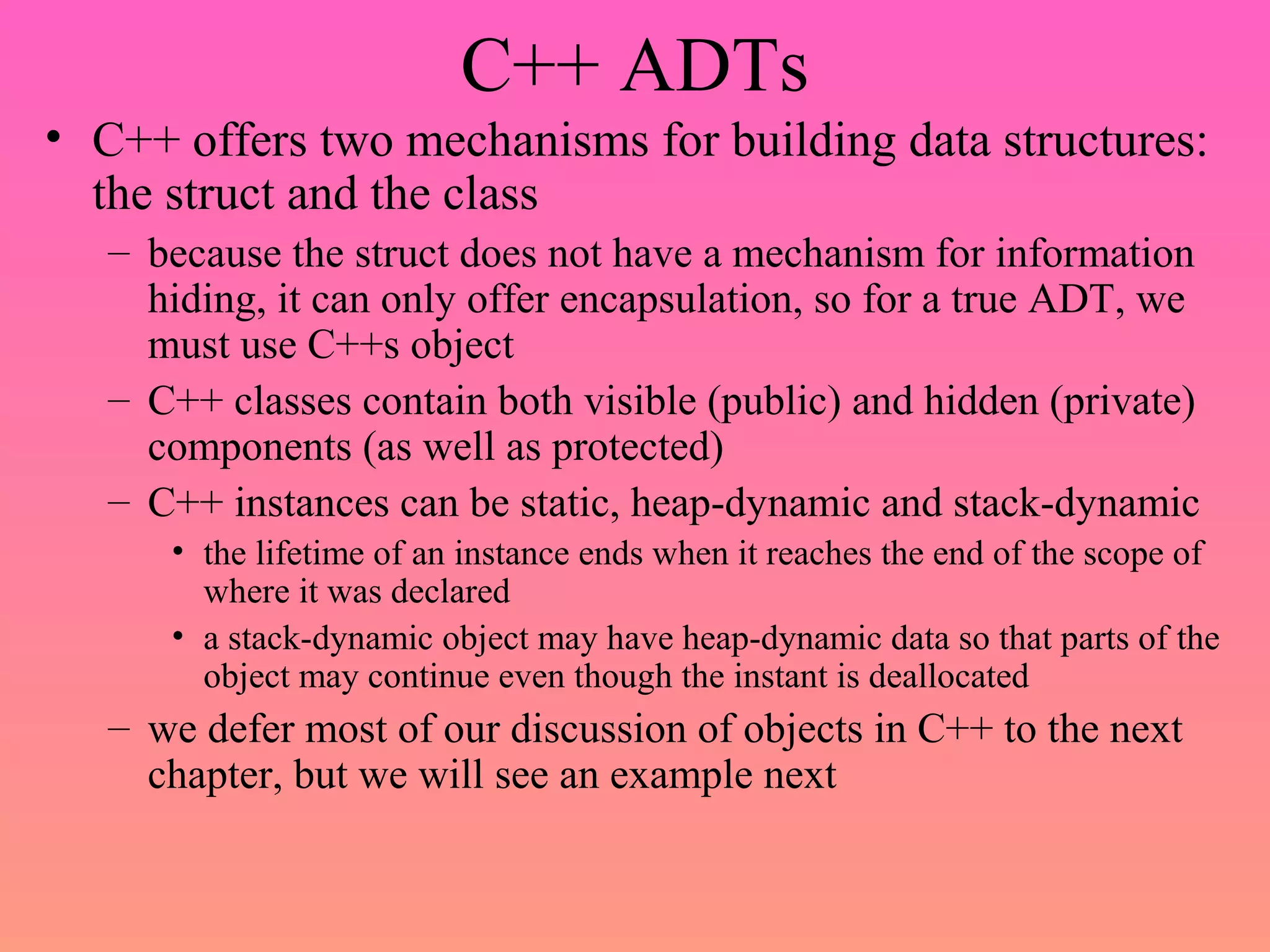
![C++ Example
#include <iostream.h>
class stack {
private:
int *stackPtr;
int max;
int topPtr;
public:
stack( ) { // constructor
stackPtr = new int [100];
max = 99;
topPtr = -1;
}
~stack( ) {delete [ ] stackPtr;} // destructor
void push(int number) {…} // details omitted
void pop( ) {…}
int top( ) {…}
int empty( ) {…}
Unlike the Ada example, in C++, the
entire definition is encapsulated in one
location
Information hiding is preserved through
the use of a private part with the interface
being defined in the public part
Any methods that are to be defined in this
class but not accessible outside of the
class would also be defined in the private
section](https://image.slidesharecdn.com/9t5tslperc28pjdgownk-signature-2af3eeb95c08314eaf1f6d5133dc61d49d795c63bf59d0729c5231a5389fe223-poli-160505171055/75/Abstract-data-types-8-2048.jpg)