This document provides an overview of the new features in Ada 2012 including:
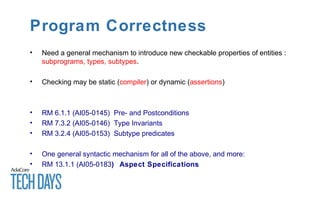
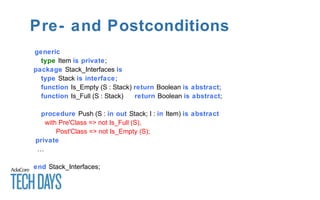
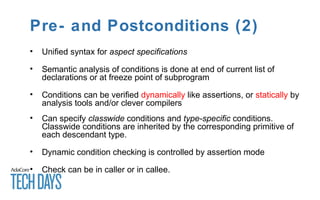
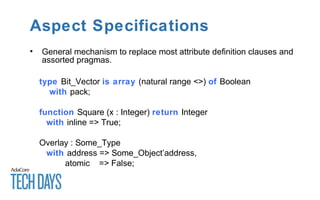
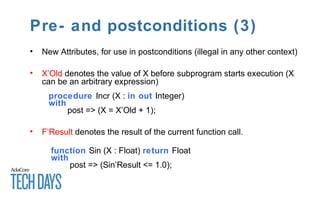
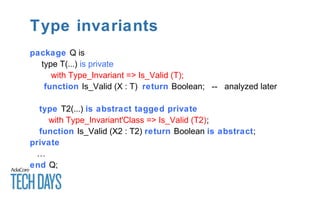
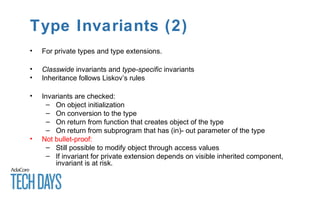
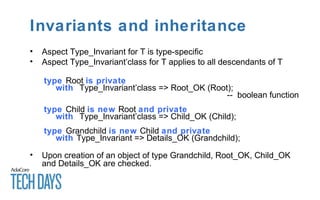
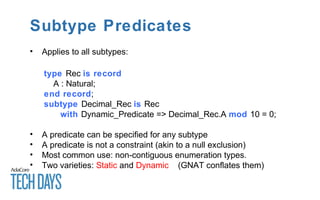
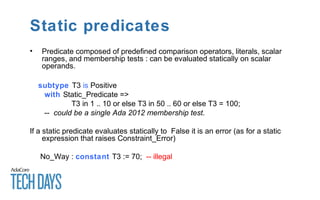
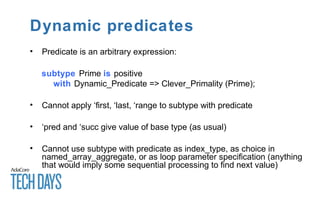
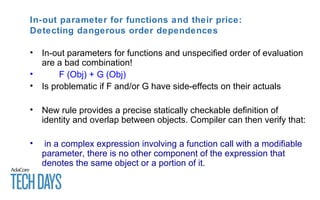
- Improved support for program correctness through pre- and postconditions, type invariants, and subtype predicates.
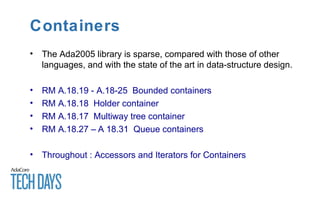
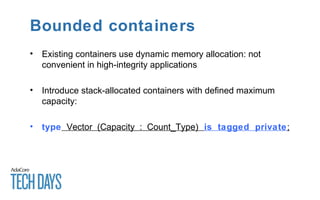
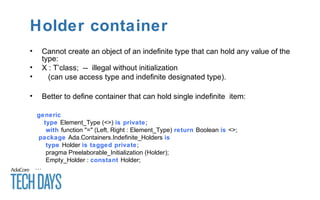
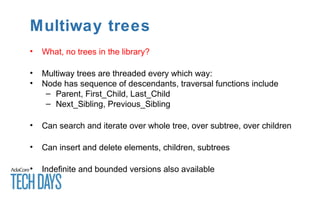
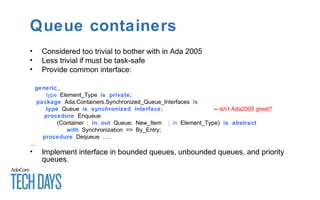
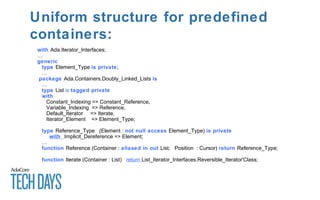
- New and improved container libraries including bounded containers, holder containers, and multiway trees.
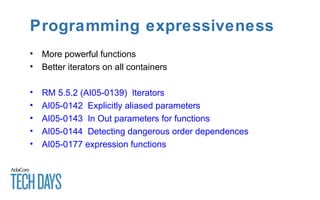
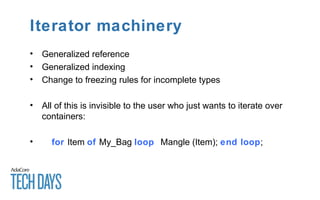
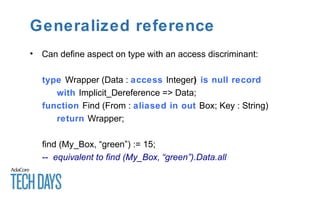
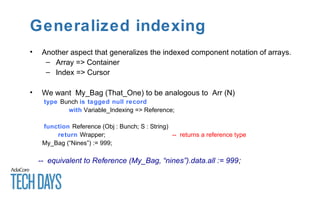
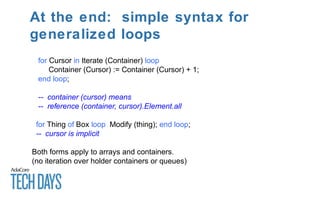
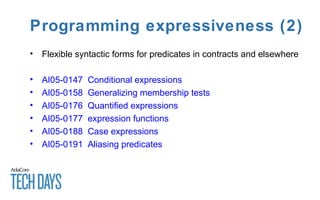
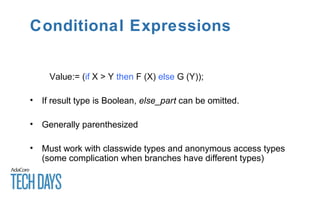
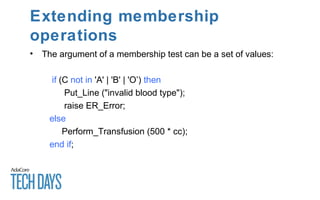
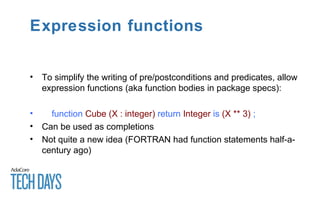
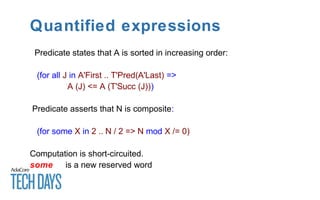
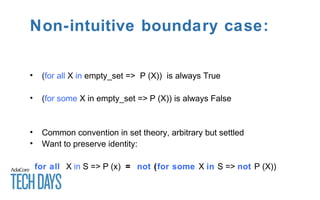
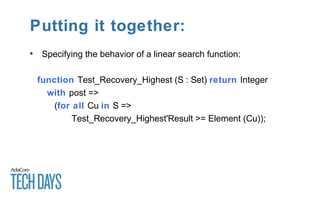
- Increased programming expressiveness through features like conditional expressions, quantified expressions, expression functions, and case expressions.
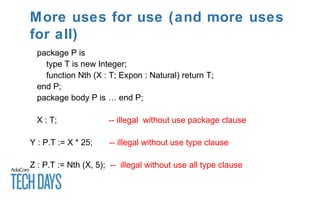
- Enhancements to visibility rules and the use of incomplete types.
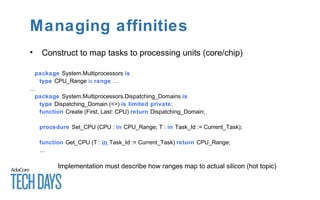
- New concurrency and real-time constructs for managing resources on multicore systems.