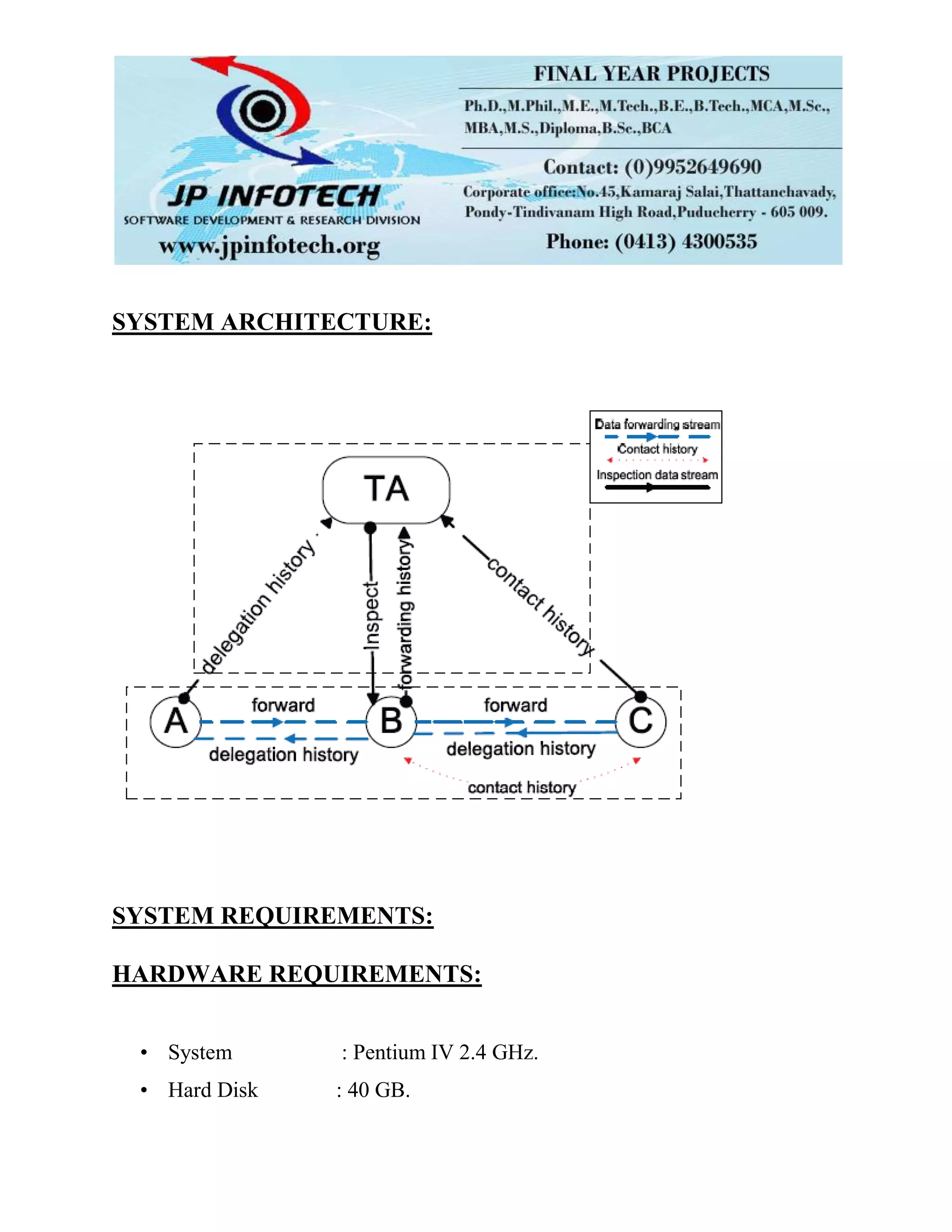
The document presents iTrust, a probabilistic misbehavior detection scheme designed to enhance routing security in delay/disruption tolerant networks (DTNs) by utilizing a periodically available trusted authority to assess node behavior. It addresses the challenges posed by malicious and selfish behaviors that threaten routing efficiency, proposing a game theoretical approach to optimize misbehavior detection with reduced costs. The scheme aims to improve overall security and efficiency while minimizing the transmission overhead associated with detecting misbehaving nodes.