MicroOS toolbox and Distrobox allow running privileged containers on openSUSE systems. Toolbox uses a default openSUSE image but allows any image, while Distrobox supports arbitrary images out of the box. They integrate tightly with the host for development, troubleshooting, and third party software, but security is not the goal so users should be cautious. Both tools make it easy to install packages, add repositories, and have persistent home directories between sessions like a traditional system.

![Linux Containers
“Linux containers, in short, contain applications in a way that keep them isolated
from the host system that they run on.”[What are Linux containers?]
“Application containers enable the user to create and run a separate container for
multiple independent applications, or multiple services that constitute a single
application.” [What Are Containers]
“They are designed to be stateless and immutable. [...] Stateless means that any
state (persistent data of any kind) is stored outside of a container. [...] Immutable
means that a container won't be modified during its life: no updates, no patches,
no configuration changes. If you must update the application code or apply a
patch, you build a new image and redeploy it.” [Best practices for operating
containers]](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-3-2048.jpg)
![Toolbox & distrobox
Are they containers? Yes, theyʼre containers, but…
● Tightly integrated with and not at all isolated from the host
● They typically contain and runs many different applications
(even full DEs [1])
● They keep their state, i.e., youʼll find them as you left the
previous time, with all the modifications/updates/changes,
applied
What the … :-O
[1] Run Latest GNOME or KDE on Distrobox](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-4-2048.jpg)
![Keeping It Clean: Dev Work
● Dependencies for building QEMU [1] from sources:
bc bison bluez-devel brlapi-devel bzip2 ccache clang
cyrus-sasl-devel flex gcc gcc-c++ gettext-tools git
glib2-devel glusterfs-devel gtk3-devel gtkglext-devel gzip
hostname libSDL2-devel libaio-devel libasan4 libcap-devel
libcap-ng-devel libcurl-devel libfdt-devel libgcrypt-devel
libgnutls-devel libjpeg62-devel libnettle-devel libnuma-devel
libpixman-1-0-devel libpng16-devel librbd-devel
libseccomp-devel libspice-server-devel libssh-devel
libssh2-devel libtasn1-devel libudev-devel libxml2-devel
lzo-devel make makeinfo multipath-tools-devel ncurses-devel
perl pkg-config python3 python3-PyYAML python3-Sphinx
rdma-core-devel snappy-devel sparse tar usbredir-devel
virglrenderer-devel vte-devel which xen-devel zlib-devel
● Install all… Will you remember to remove them when no longer needed?
● What if, you need to try a particular version of one of those
○ E.g., from a specific repo?
○ E.g., from sources?
[1] slightly outdated](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-7-2048.jpg)
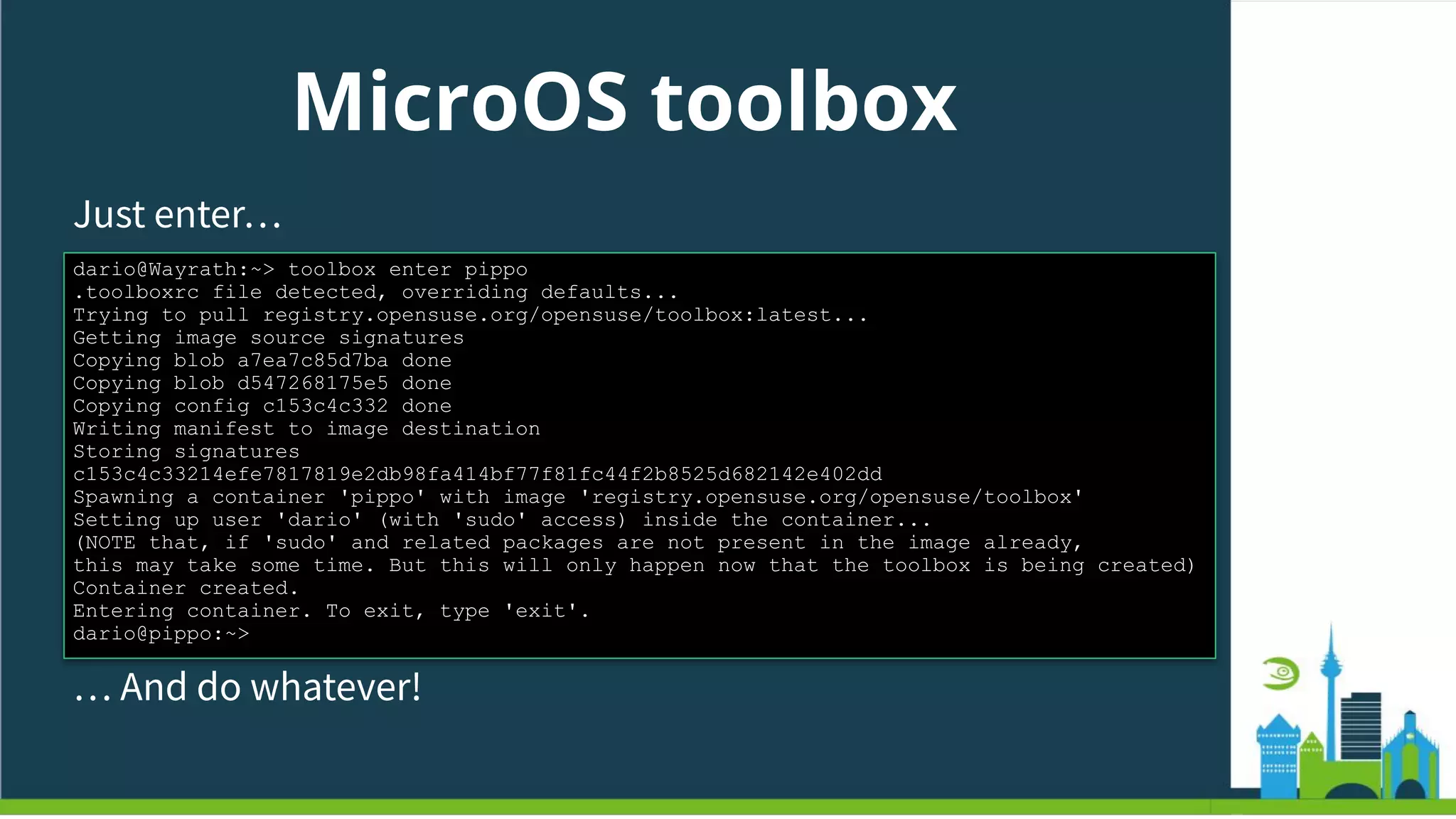
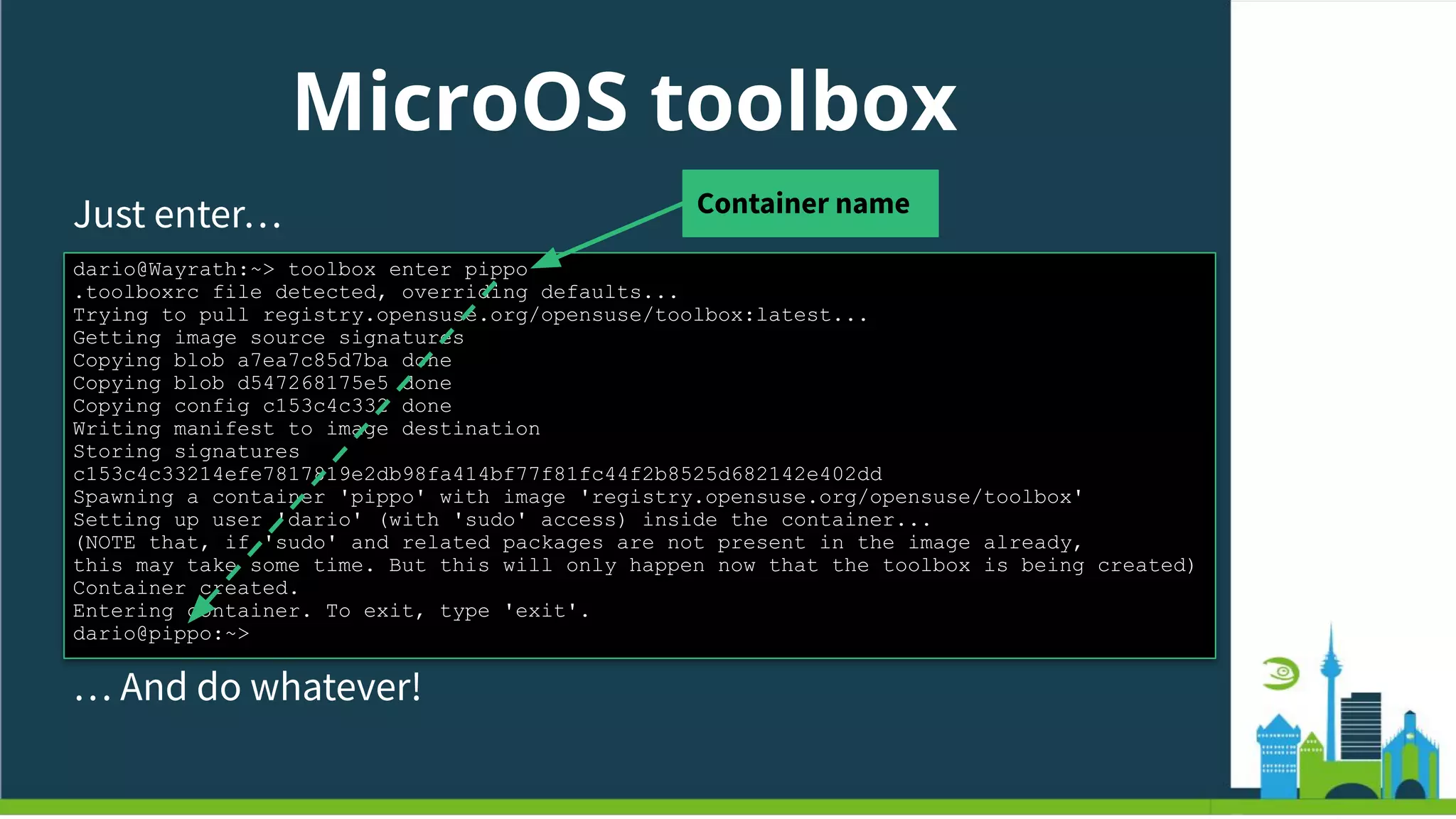
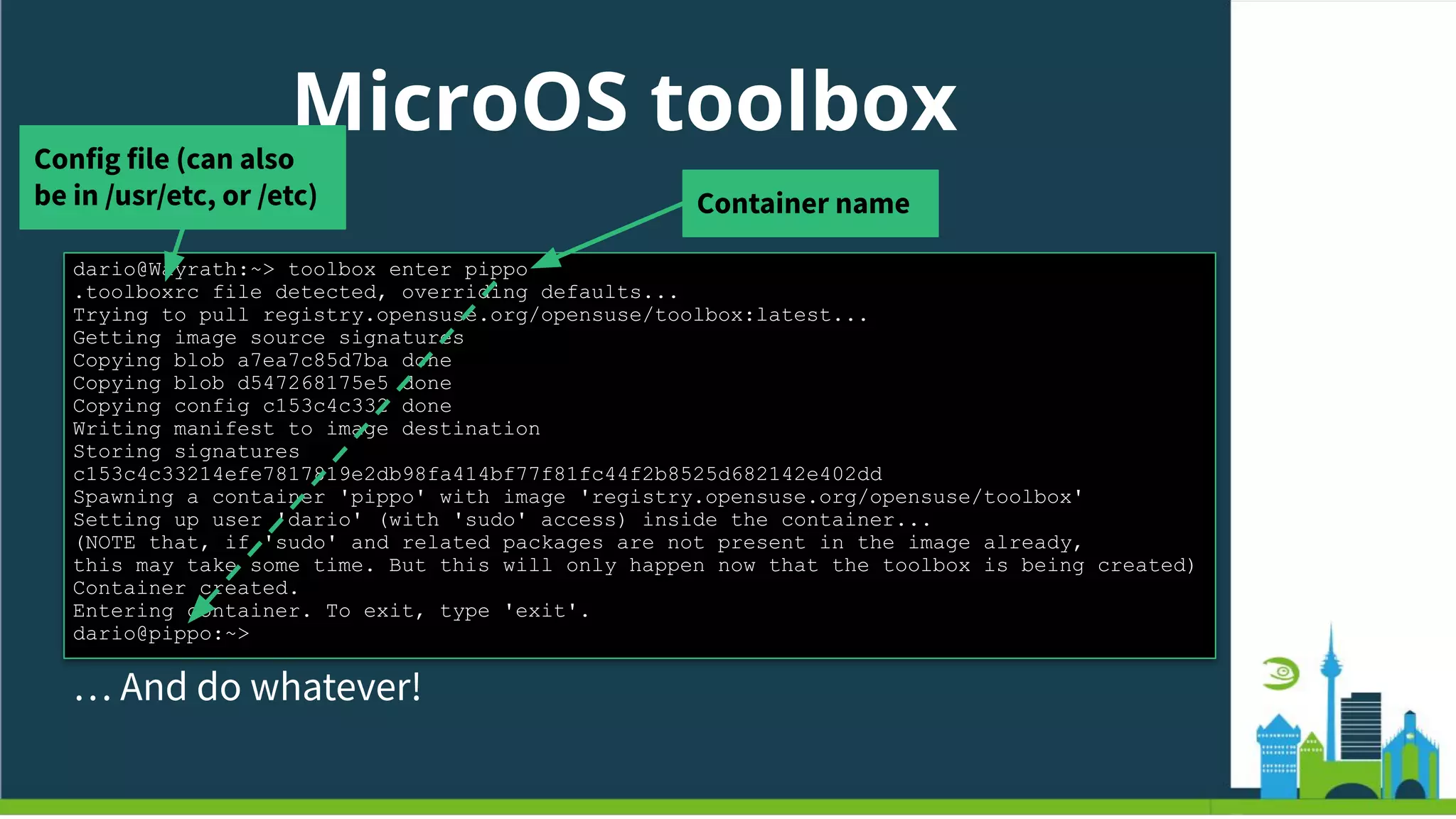
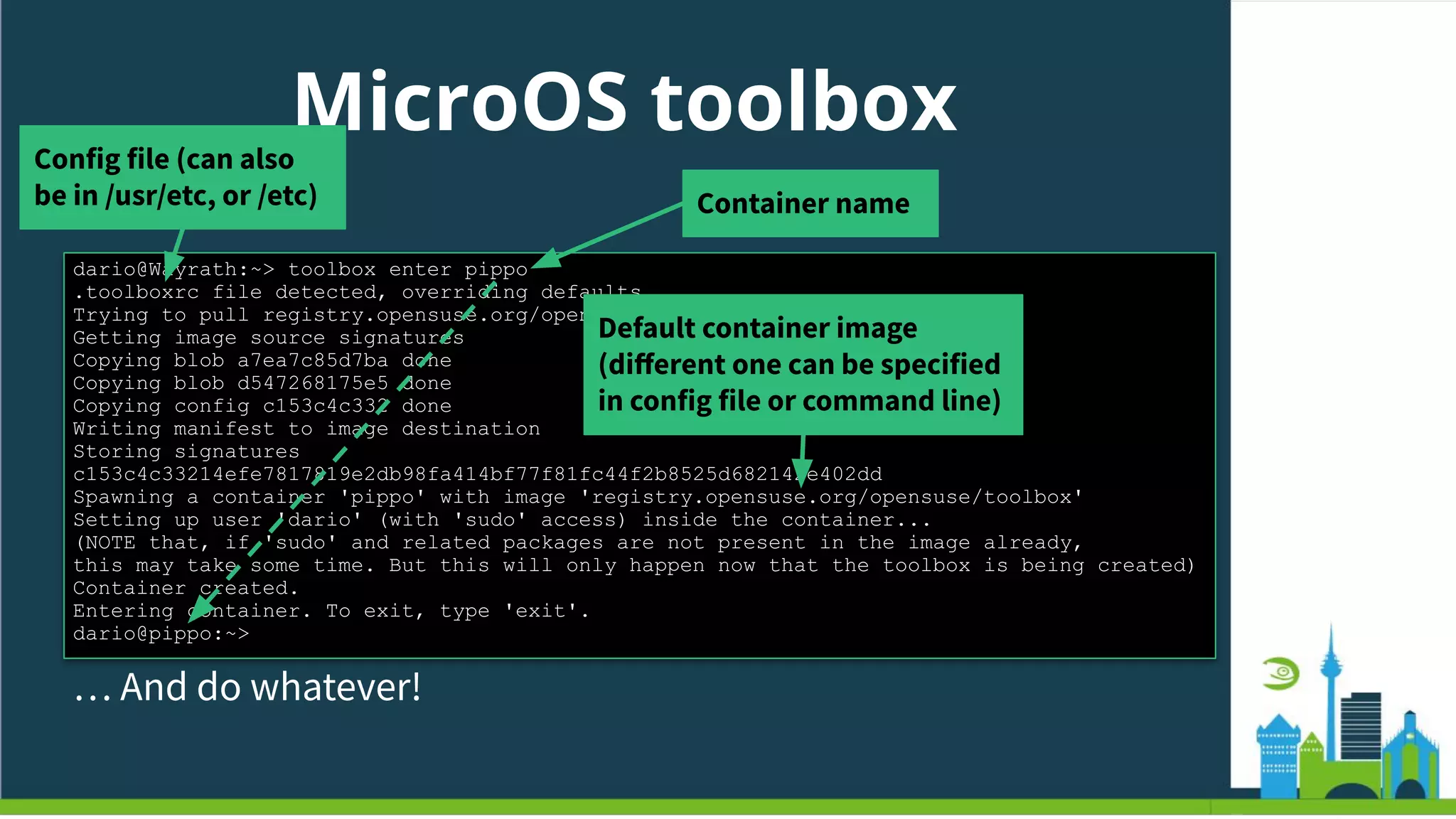
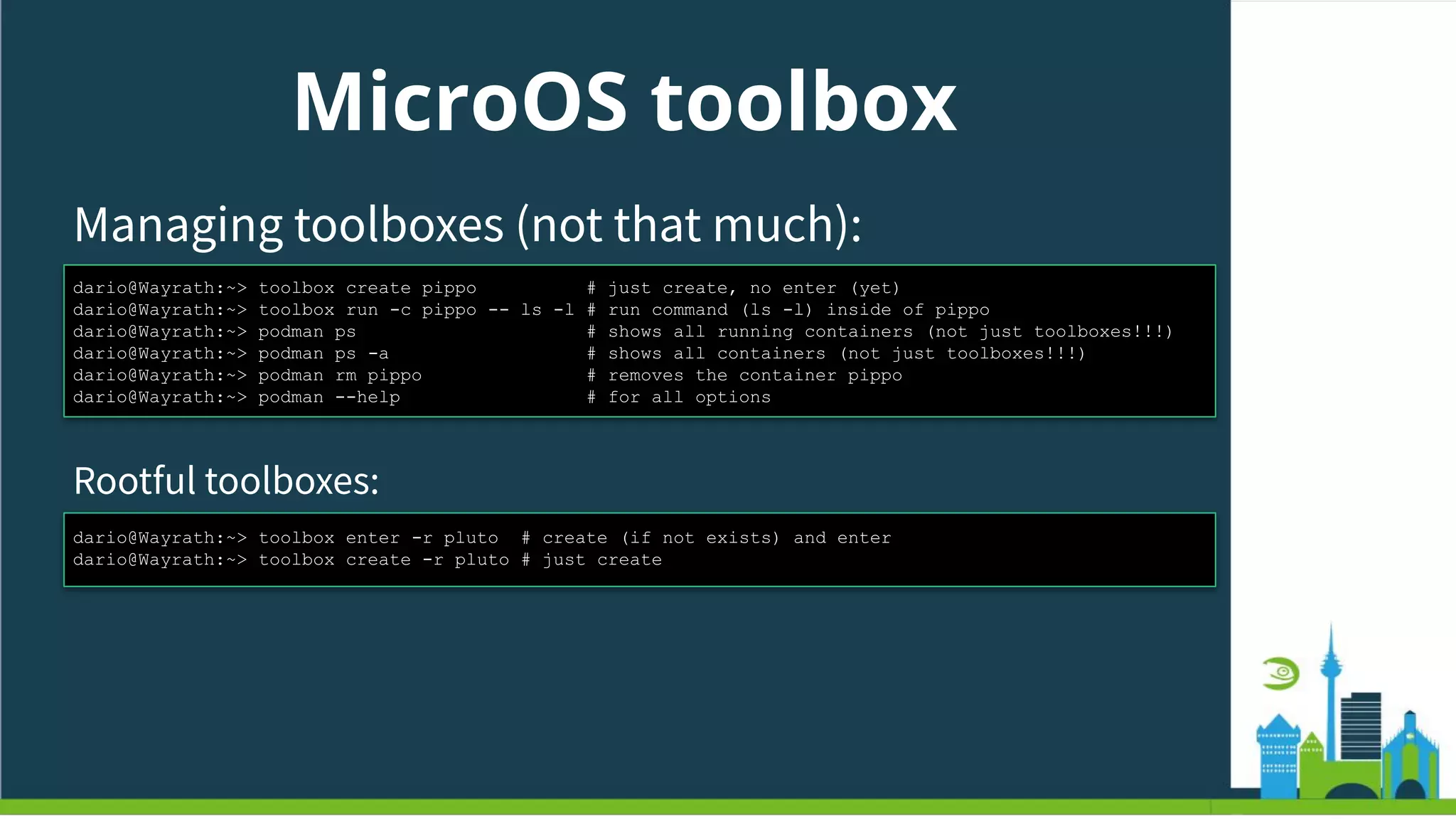
![MicroOS toolbox
A shell script that wraps the creation & launch of the container,
out of an (almost arbitrary) image
https://github.com/openSUSE/microos-toolbox
Born with the troubleshooting use-case in mind. Then evolved
If on podman, can run rootful or rootless
● openSUSE Tumbleweed:
sudo zypper in toolbox
● openSUSE MicroOS [Desktop]
Preinstalled :-)](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-13-2048.jpg)
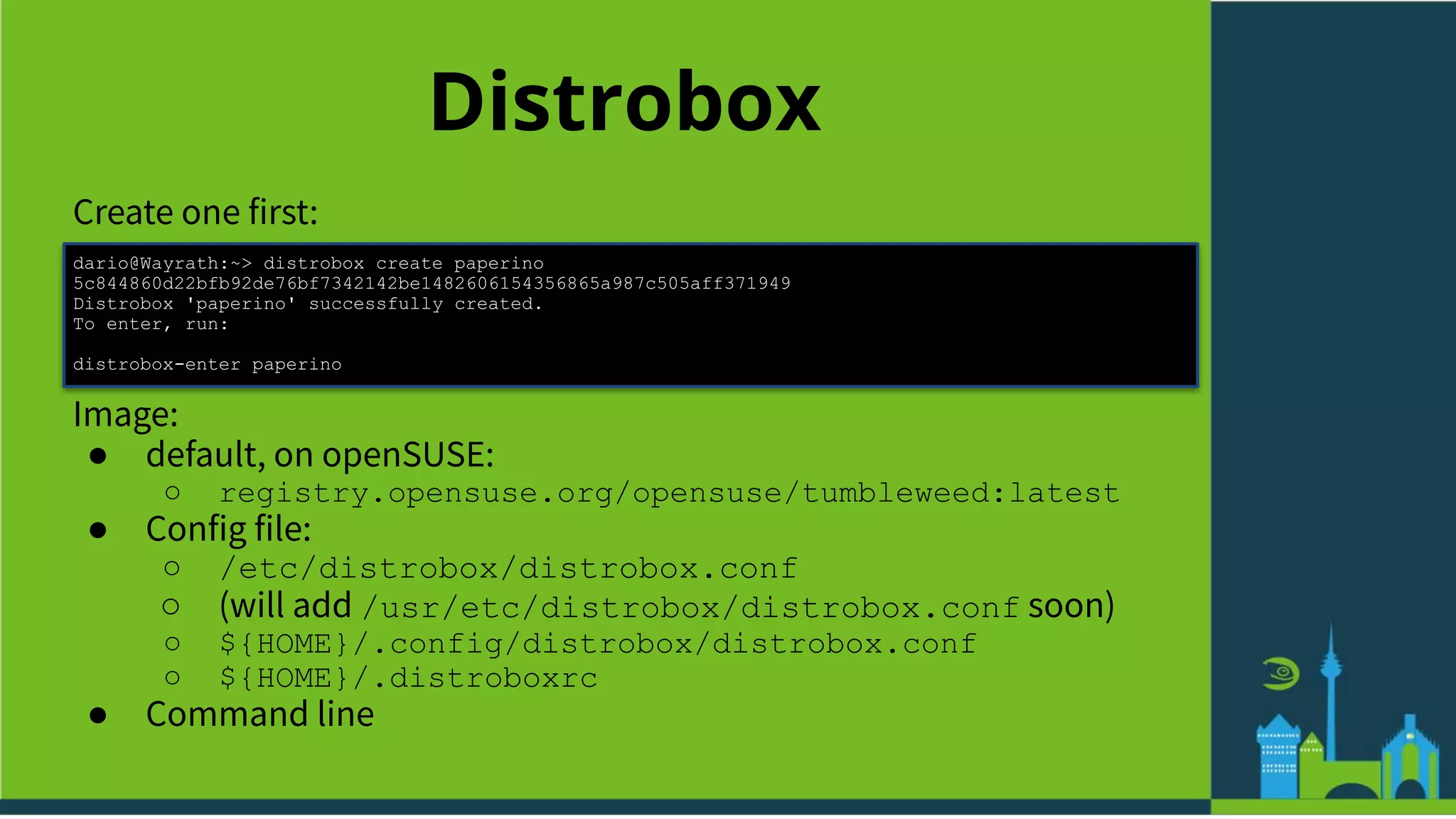
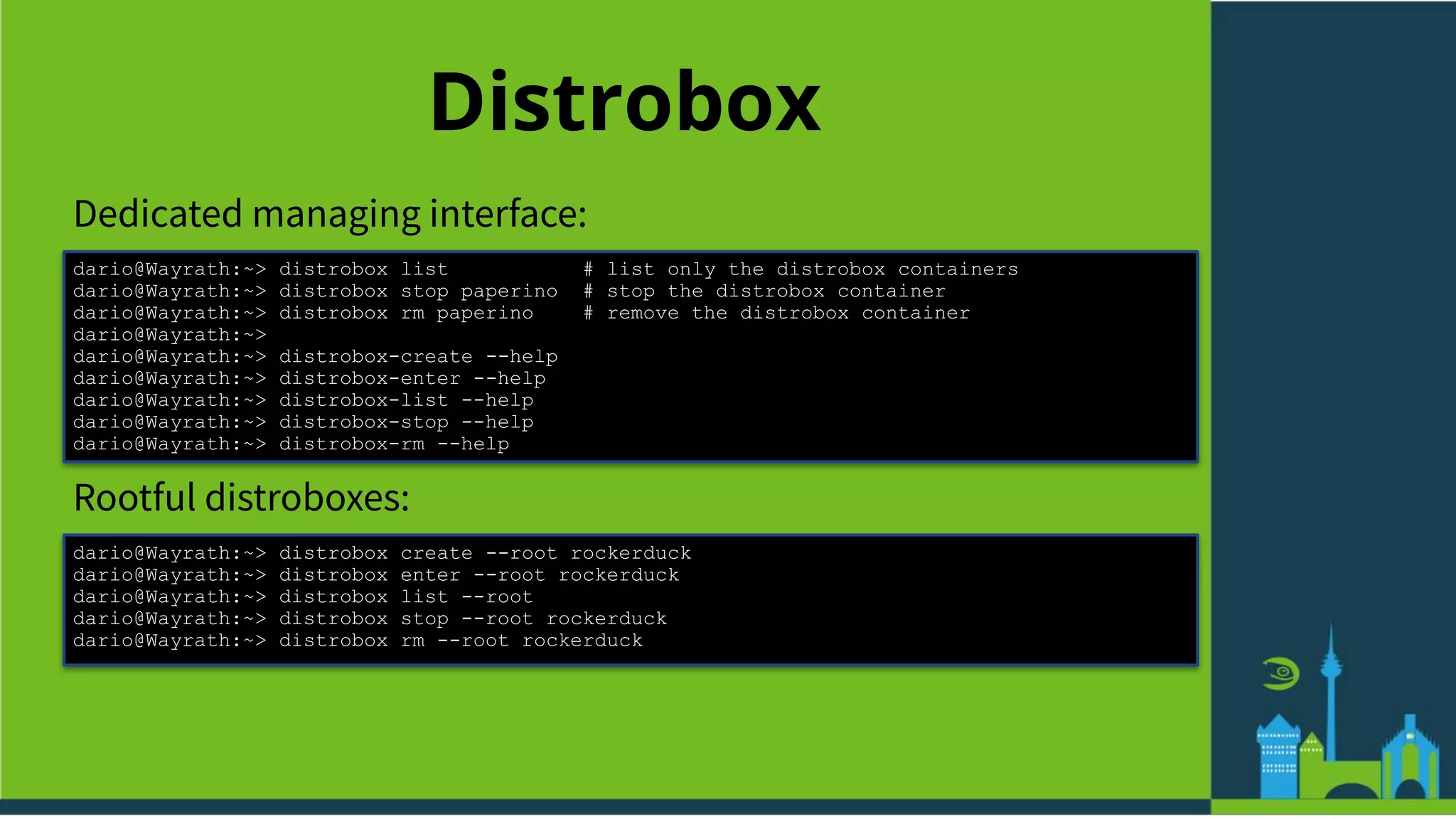
![Distrobox
Also shell script, also wraps podman/docker
https://github.com/89luca89/distrobox
Born to enhance the toolbox [1] idea and implementation with
● richer and easier UI/UX
● Arbitrary (i.e., of any distro) & out-of-the-box image support
● openSUSE Tumbleweed
sudo zypper in distrobox
● openSUSE MicroOS
sudo transactional-update pkg install
distrobox
(maybe pkcon install distrobox … “itʼs complicated”!)
[1] This implementation of it, FTR](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-19-2048.jpg)
![Distrobox
Then enter:
dario@Wayrath:~> distrobox enter paperino
Container paperino is not running.
Starting container paperino
run this command to follow along:
podman logs -f paperino
Starting container... [ OK ]
Installing basic packages... [ OK ]
Setting up read-only mounts... [ OK ]
Setting up read-write mounts... [ OK ]
Setting up host's sockets integration... [ OK ]
Integrating host's themes, icons, fonts...[ OK ]
Setting up package manager exceptions... [ OK ]
Setting up sudo... [ OK ]
Setting up groups... [ OK ]
Setting up users... [ OK ]
Executing init hooks... [ OK ]
Container Setup Complete!
dario@paperino:~>](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-21-2048.jpg)
![Distrobox
Then enter:
dario@Wayrath:~> distrobox enter paperino
Container paperino is not running.
Starting container paperino
run this command to follow along:
podman logs -f paperino
Starting container... [ OK ]
Installing basic packages... [ OK ]
Setting up read-only mounts... [ OK ]
Setting up read-write mounts... [ OK ]
Setting up host's sockets integration... [ OK ]
Integrating host's themes, icons, fonts...[ OK ]
Setting up package manager exceptions... [ OK ]
Setting up sudo... [ OK ]
Setting up groups... [ OK ]
Setting up users... [ OK ]
Executing init hooks... [ OK ]
Container Setup Complete!
dario@paperino:~>
NB: This phase takes (quite!) a while.
But only the first time!](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-22-2048.jpg)
![3D GUI Apps
How do you fancy NVIDIAʼs kmp-s in a container? :-O
Well… it works:
dario@Wayrath:~> distrobox enter paperino
dario@paperino:~> zypper addrepo --refresh https://do[...]se/tumbleweed NVIDIA
dario@paperino:~> sudo zypper in nvidia-gfxG06-kmp-default nvidia-glG06
x11-video-nvidiaG06
dario@paperino:~> sudo zypper in kernelshark
dario@paperino:~> kernelshark](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-35-2048.jpg)
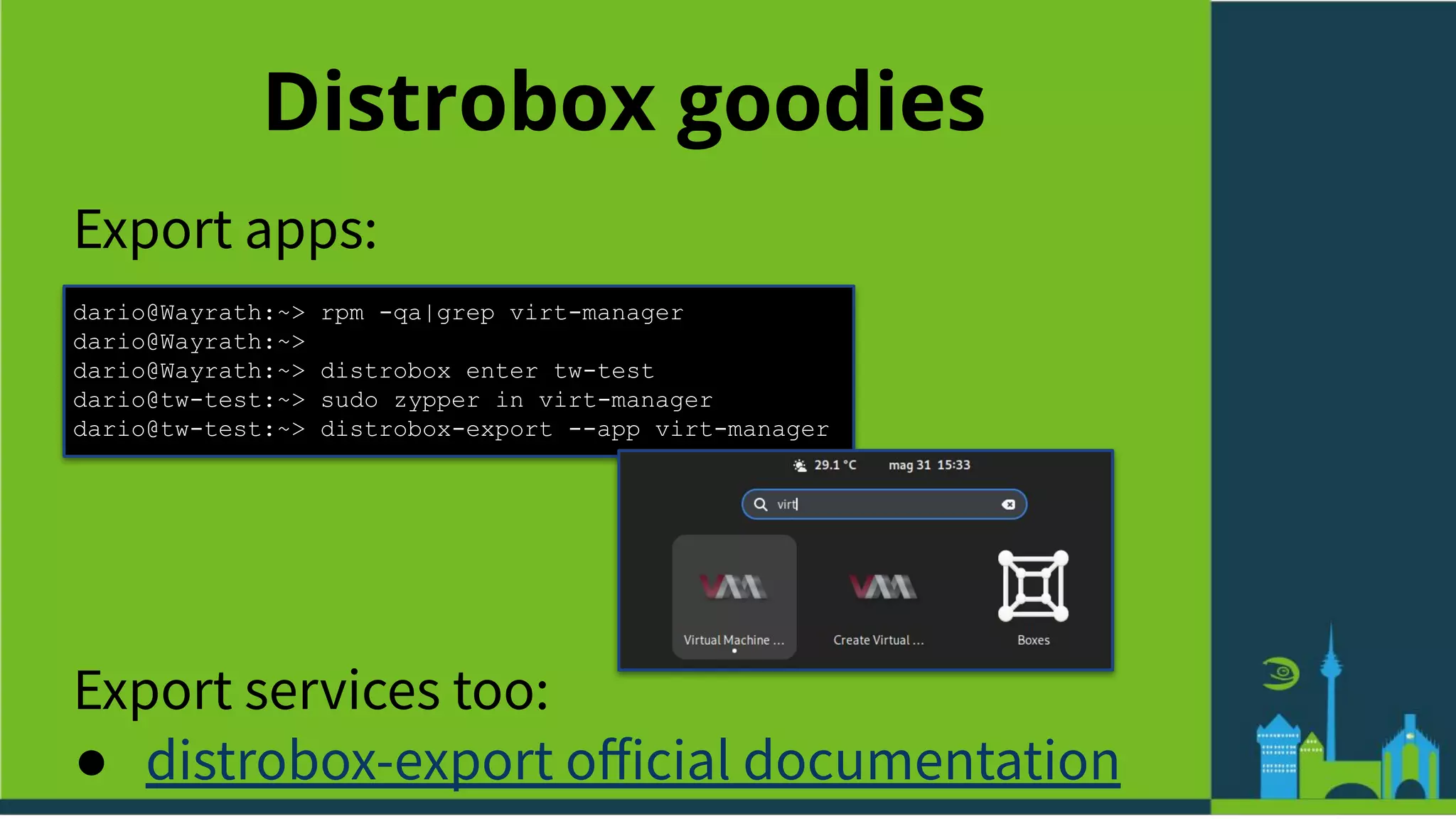
![Distrobox goodies
Systemd containers:
dario@Wayrath:~> distrobox create --root --init -n libvirt-tw
dario@Wayrath:~> distrobox enter libvirt-tw
[...]
dario@libvirt-tw:~> sudo zypper in libvirt-daemon virt-install libvirt-daemon-driver-qemu
libvirt-daemon-driver-network libvirt-daemon-driver-interface qemu-hw-usb-host
qemu-hw-display-qxl libvirt-client
dario@libvirt-tw:~> sudo systemctl enable --now libvirtd
dario@libvirt-tw:~> sudo systemctl status libvirtd
● libvirtd.service - Virtualization daemon
Loaded: loaded (/usr/lib/systemd/system/libvirtd.service; disabled; vendor preset:
disabled)
Active: active (running) since Tue 2022-05-31 15:00:06 CEST; 28min ago
TriggeredBy: ● libvirtd-admin.socket
● libvirtd-ro.socket
● libvirtd.socket
Docs: man:libvirtd(8)
https://libvirt.org
Main PID: 4620 (libvirtd)
Tasks: 18 (limit: 32768)
CPU: 476ms
CGroup: /system.slice/libvirtd.service
└─ 4620 /usr/sbin/libvirtd --timeout 120](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-38-2048.jpg)
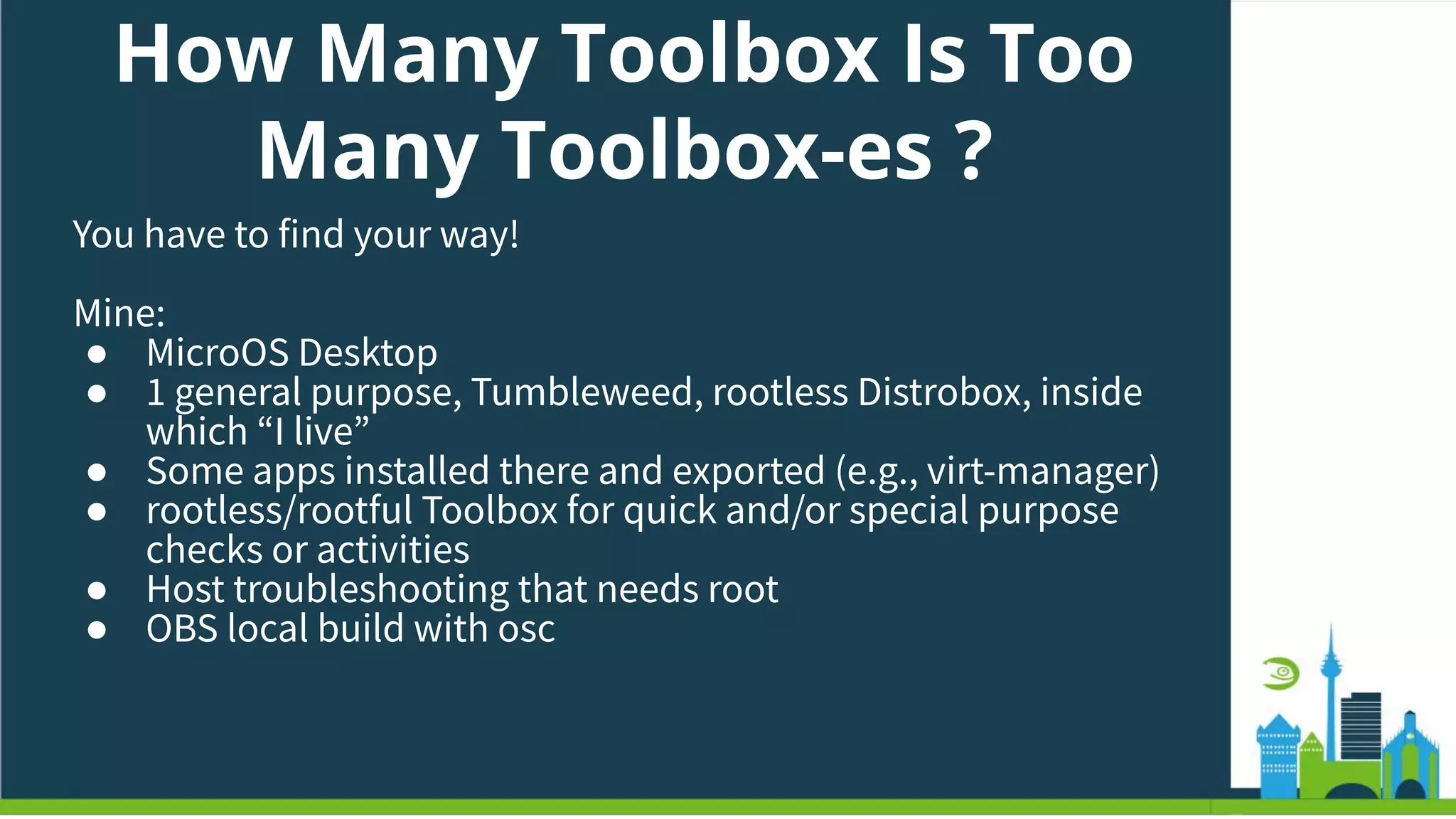
![How Many Toolbox Is Too
Many Toolbox-es ?
10-ths of [tool|distro]box-es? (E.g., one for
each project/workload/app)
● Very fine grained control
● Managing can be tricky
(Think about updating all of them!)](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-41-2048.jpg)
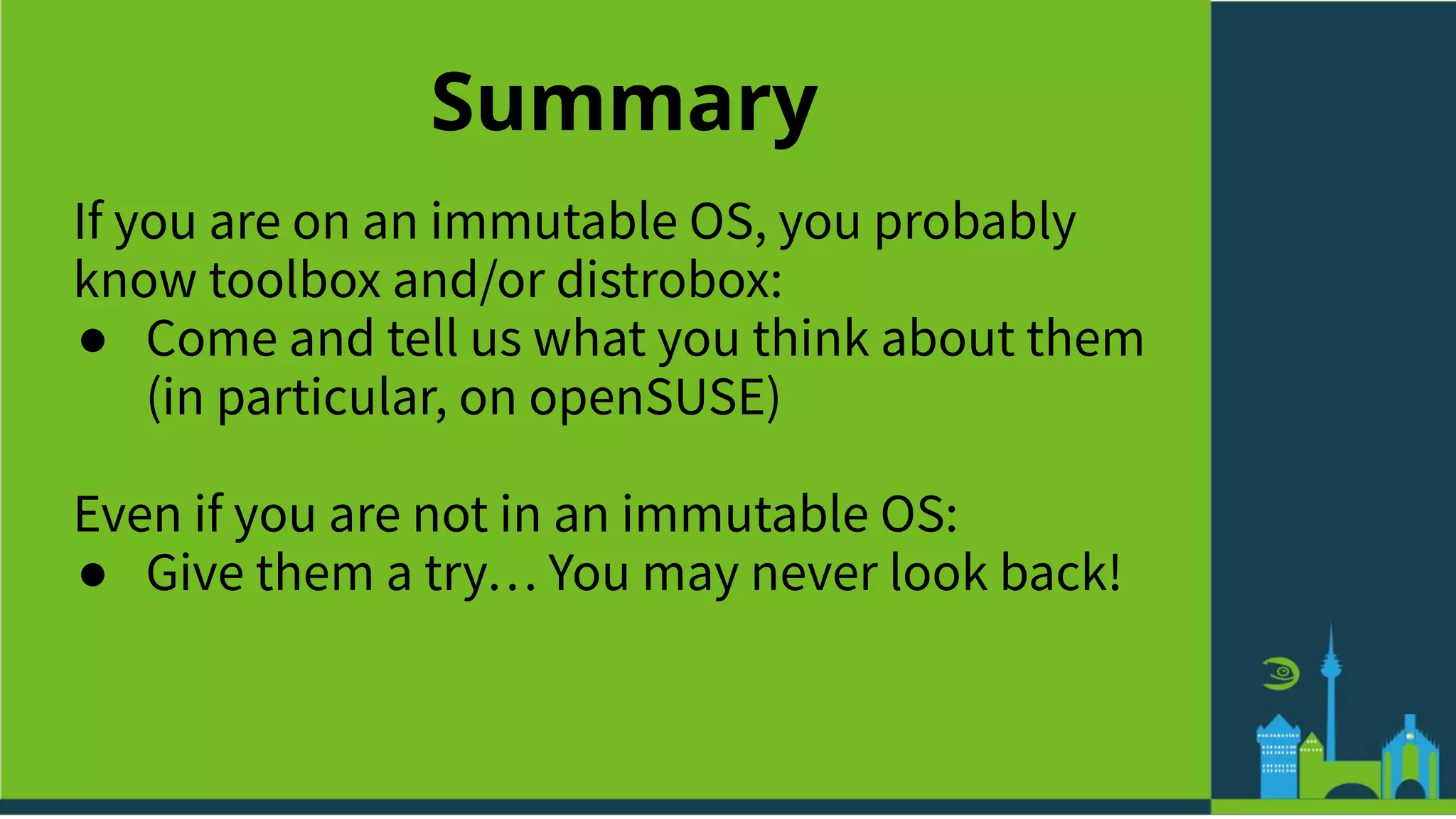
![How Many Toolbox Is Too
Many Toolbox-es ?
Only 1 [tool|distro]box to rule them all?
● Easy to manage (~= like an host)
● Can become huge, and maybe messy?
● Rootful or rootless?](https://image.slidesharecdn.com/toolboxanddistrobox-osc22-220601145603-ef8ed0db/75/A-Box-Full-of-Tools-and-Distros-42-2048.jpg)