Embed presentation
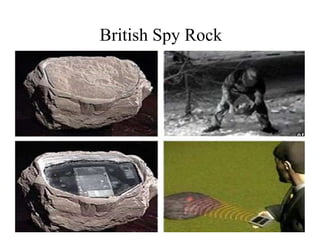
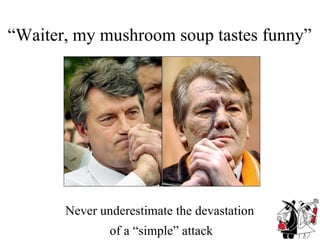
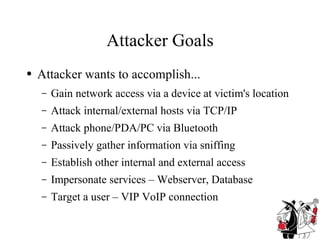
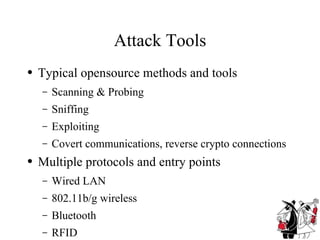
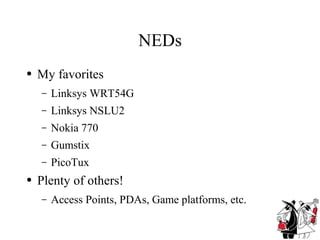
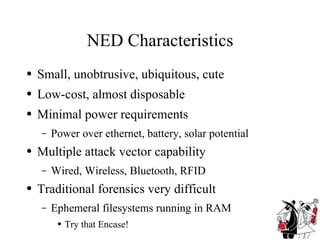
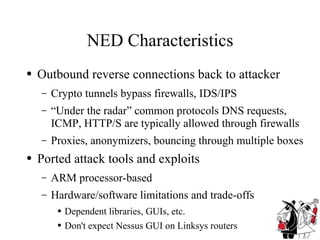
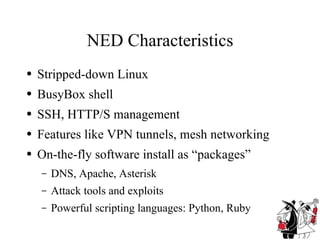
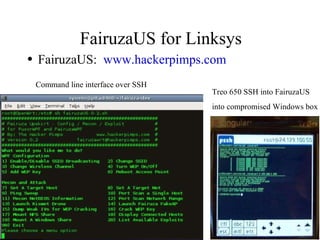

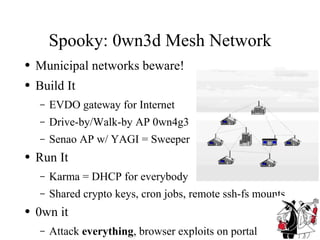


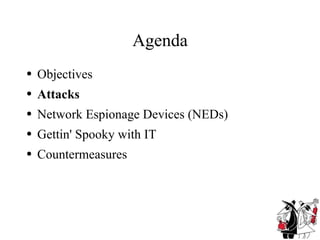
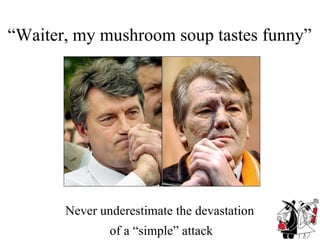
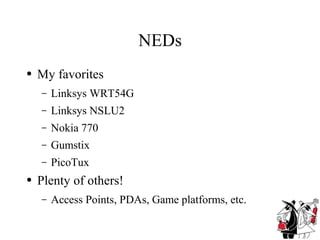
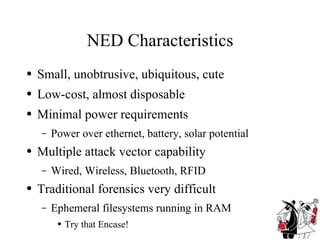
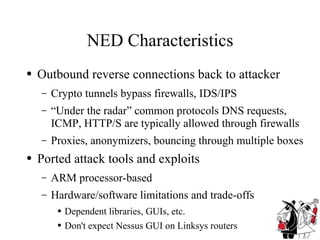
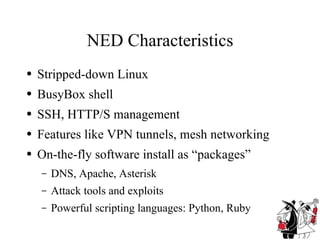
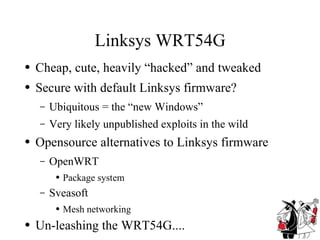
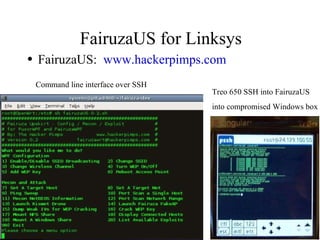
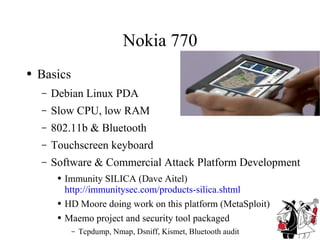
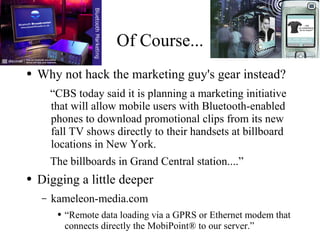
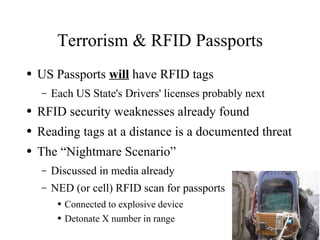
This document summarizes a presentation about low-cost devices that can be used for network espionage. It describes various small, inexpensive devices like wireless routers and PDAs that have been modified to perform attacks and surveillance through their networking capabilities. Examples like the Linksys WRT54G wireless router and Nokia 770 PDA are provided. The presentation outlines how these network espionage devices (NEDs) work, potential attacks they enable, and recommendations for security countermeasures.