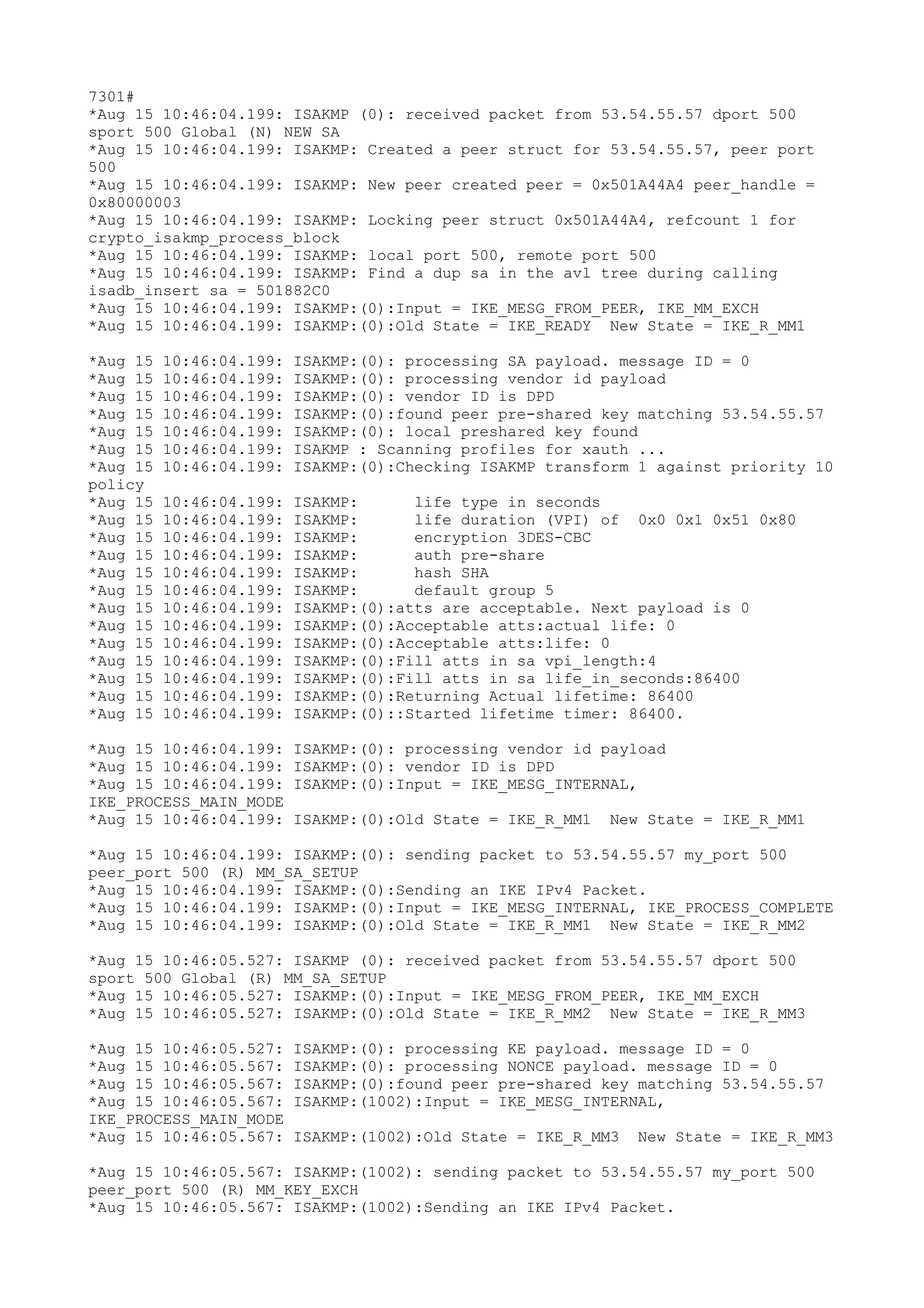
The document contains log messages from an IPsec VPN setup process between two devices with IP addresses 53.54.55.56 and 53.54.55.57. It shows the IKE/ISAKMP phase 1 negotiation to establish an SA and authentication using pre-shared keys. It then shows the phase 2 IKE negotiation to establish IPsec SAs for encryption and the IPsec tunnel coming up.