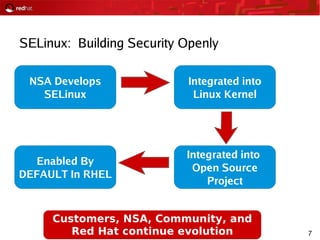
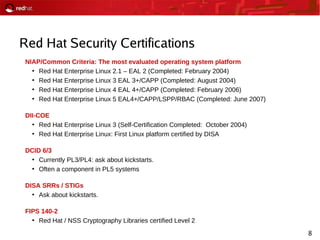
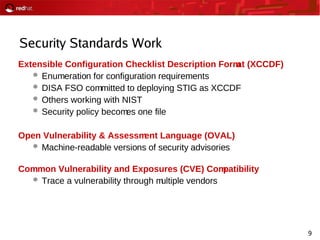
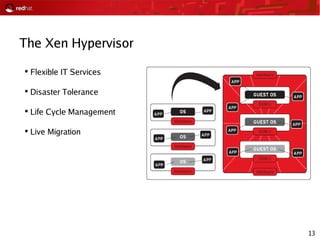
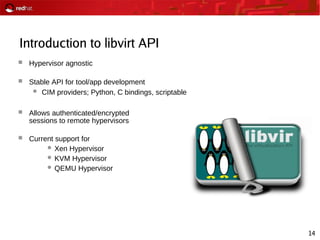
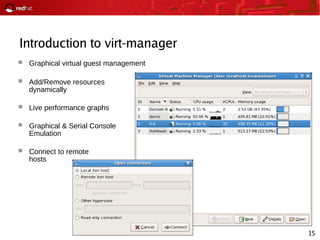
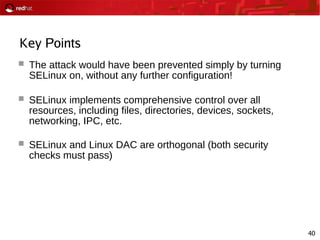
The document outlines an agenda for a Red Hat security seminar covering emerging technologies like the Xen hypervisor and virtualization, security features in Red Hat like SELinux and its role in building security openly, and questions from attendees about Red Hat's security certifications and standards work. Hands-on labs were also planned to demonstrate technologies discussed.



![47
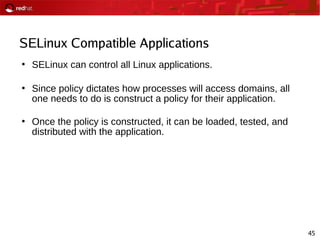
SELinux: Exploring Contexts
●
All objects have a security context
● user:role:type[:sensitivity:category]
●
Stored as extended attribute on the inode
User
● Strict: audit_u, admin_u, etc.
● Targeted: root, system_u, user_u
Role
● Targeted: files are object_r, processes are system_r
Type
● Type v. domain: httpd_exec_t v. httpd_t
●
Sensitivity: s0-s15, aka “SystemLow-SystemHigh”
●
Category: c0-c1023
●
Set math!](https://image.slidesharecdn.com/2008-03-06harrissecurityseminar-160712202003/85/2008-03-06-Harris-Corp-Security-Seminar-47-320.jpg)