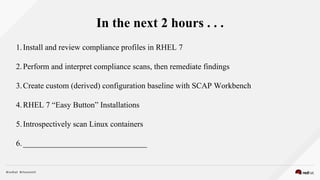
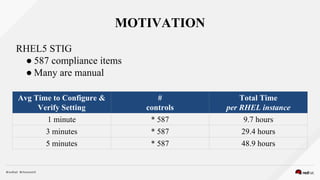
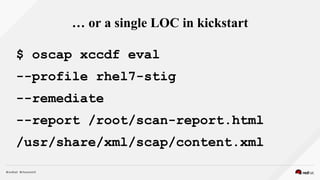
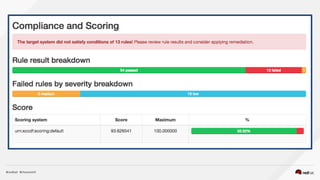
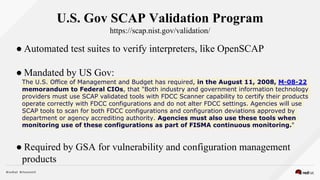
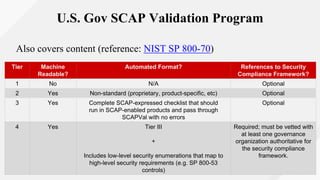
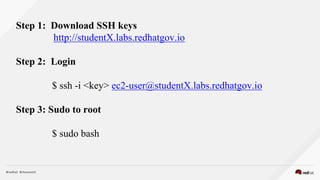
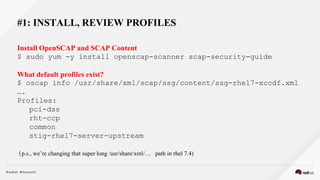
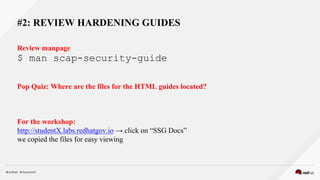
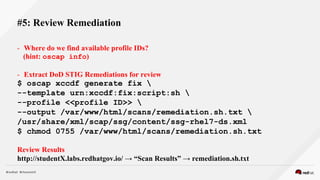
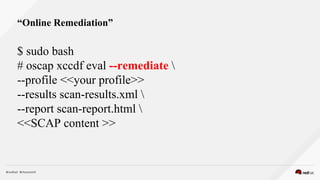
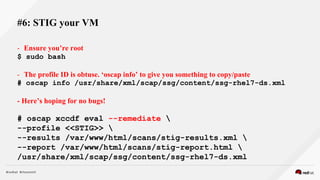
This document provides an agenda for an OpenSCAP workshop that will explore scanning, reporting, and remediation using OpenSCAP tools and SCAP content. The workshop will include installing and reviewing compliance profiles in RHEL 7, performing and interpreting compliance scans and remediating findings, and creating a custom configuration baseline. It outlines the tasks to be completed which include installing OpenSCAP and SCAP content, reviewing available profiles and hardening guides, performing a local scan and reviewing results, extracting and reviewing remediation scripts, scanning a VM with the DISA STIG profile, and demonstrating the SCAP Workbench tool.