Embed presentation
Download to read offline


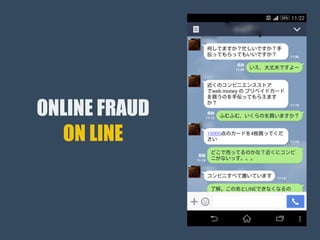

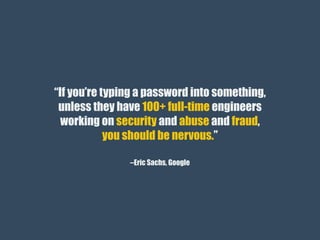

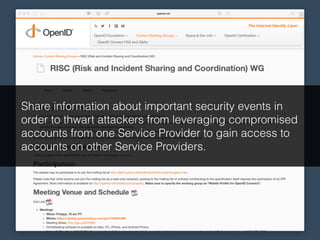

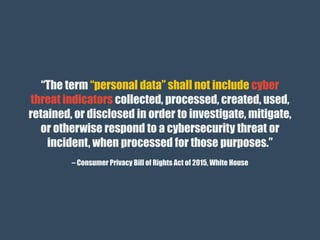
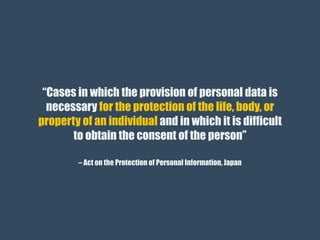
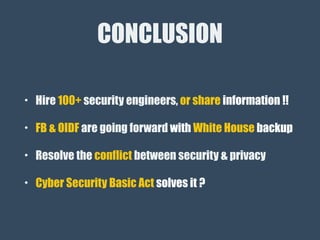

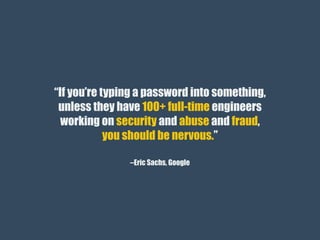
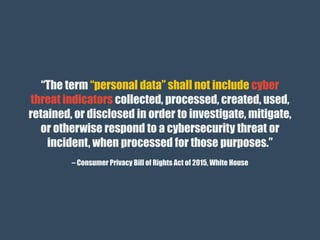
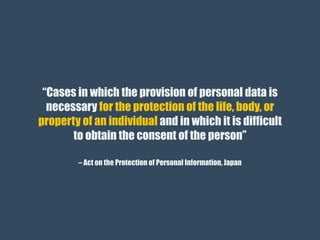
The document discusses the importance of threat information sharing in the private sector to prevent account compromises and enhance security. It emphasizes the need for significant investment in security personnel and the balance between security measures and privacy rights as outlined in various legislative acts. The conclusion suggests collaboration among companies and legislative support to enhance cybersecurity while addressing privacy concerns.