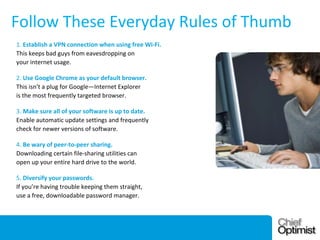
This document discusses the importance of data security and provides information about common security threats. It notes that there were over 800 data breaches in 2011 compromising 174 million records, with the majority of attacks being external and involving digital hacking. Common motives for attacks are fraud, activism, and industrial espionage. The top three security threats are malware, internet-facing applications, and social engineering. Social engineering, which involves deceiving people, is particularly effective since humans are often the weakest link. The document provides tips for improving security such as training employees, performing security audits, asking key questions, and following basic security practices like using VPNs and updating software.