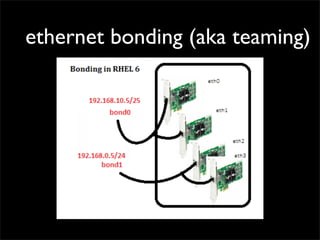
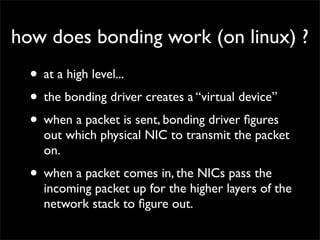
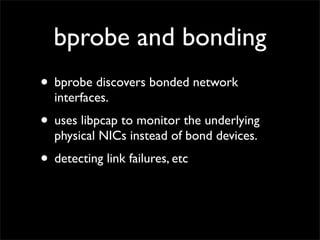
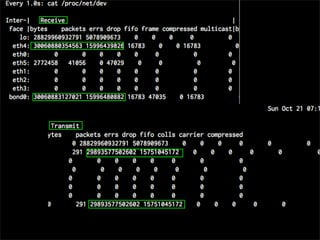
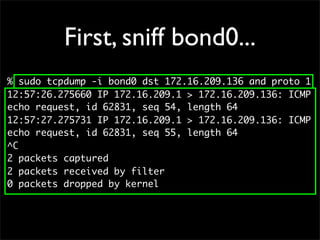
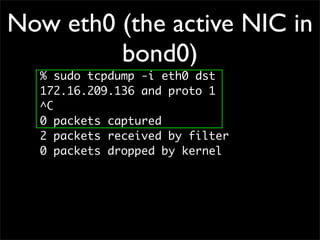
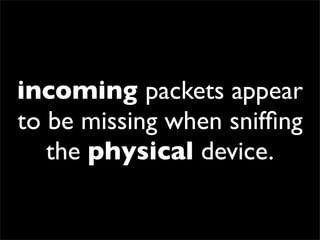
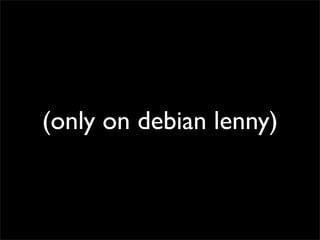
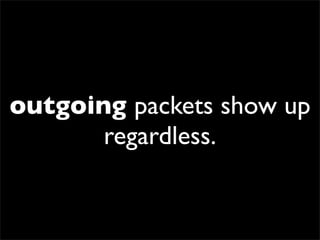
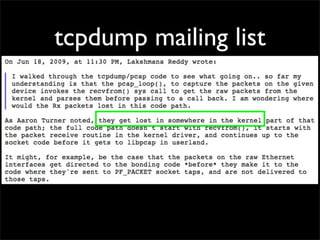
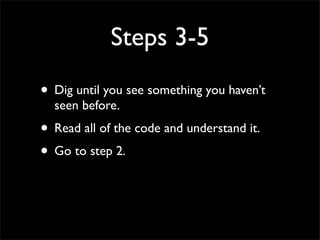
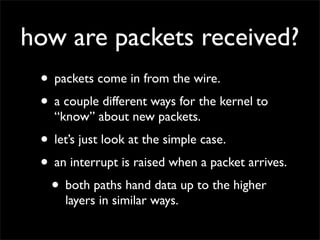
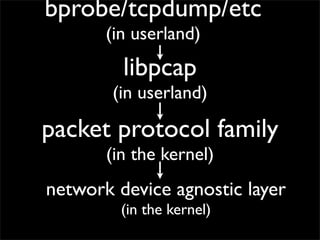
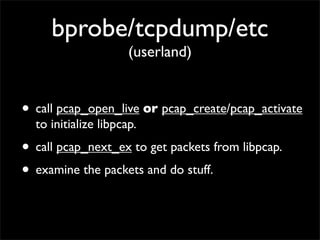
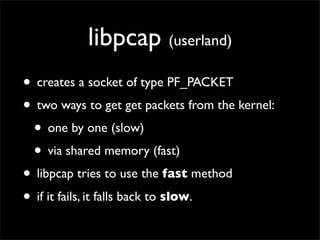
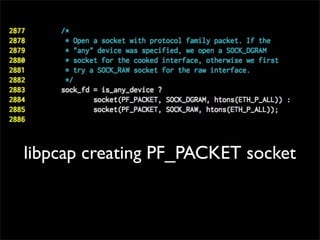
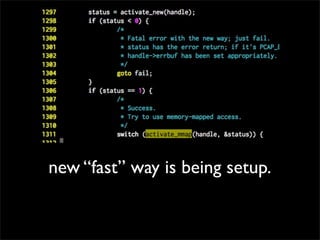
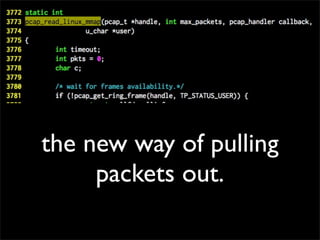
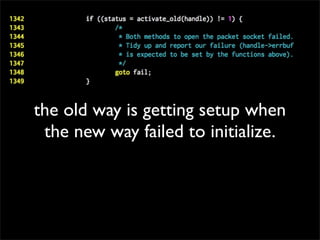
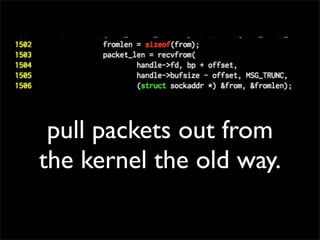
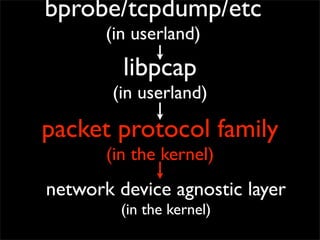
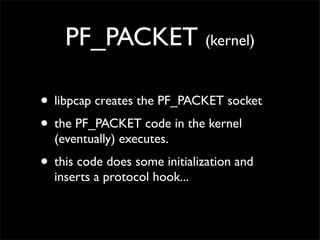
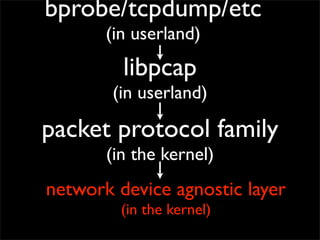
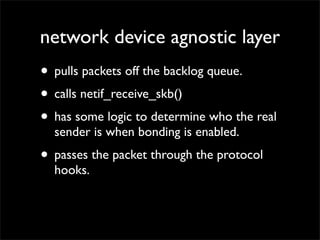
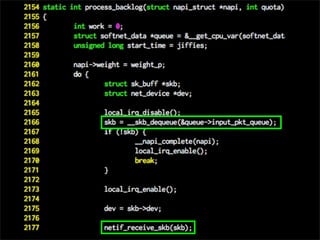
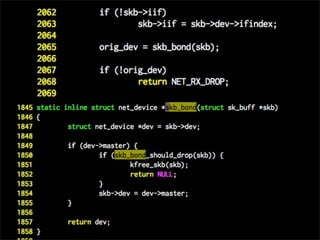
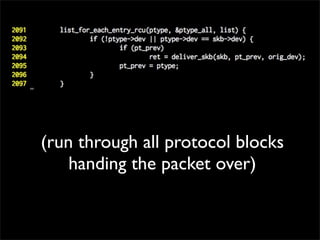
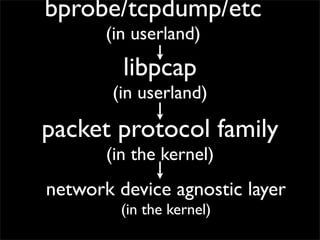
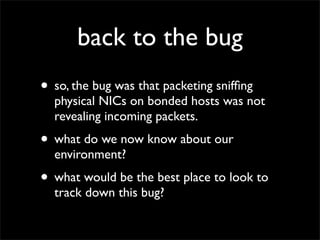
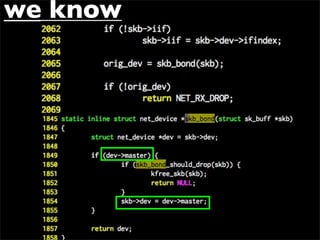
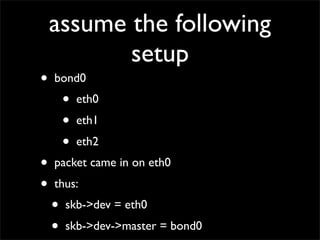
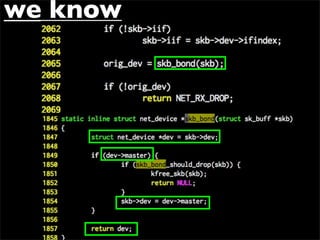
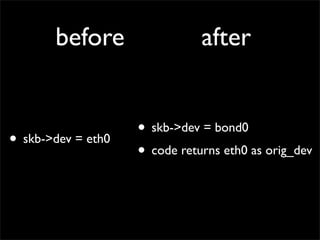
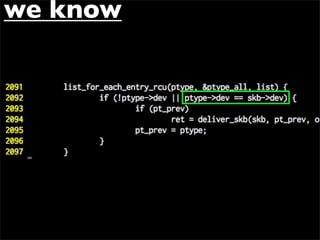
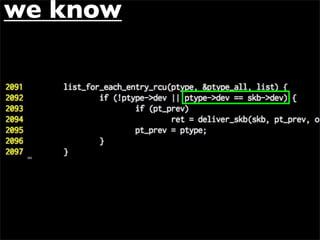
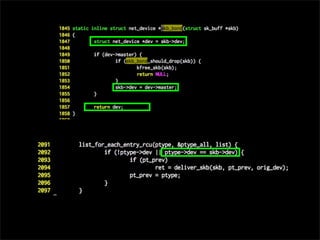
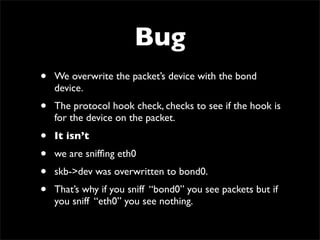
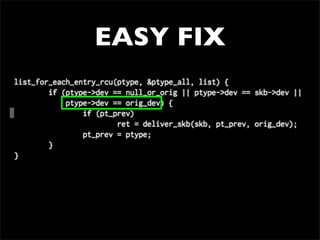
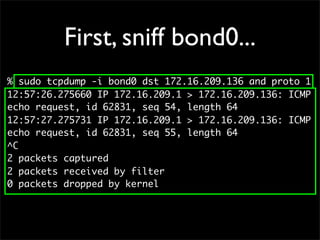
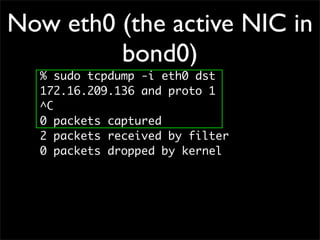
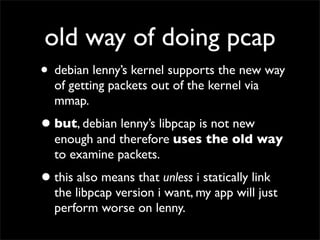
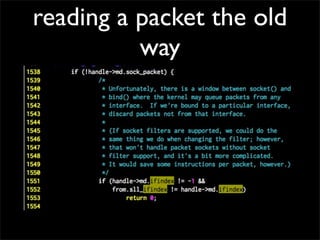
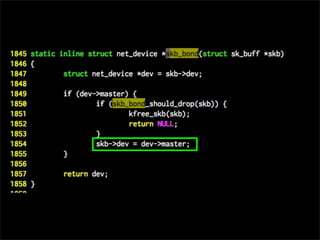
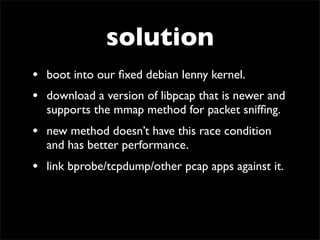
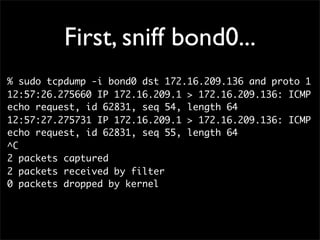
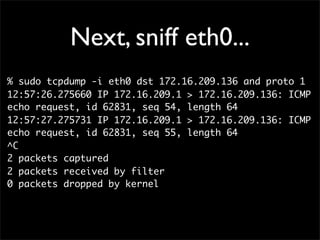
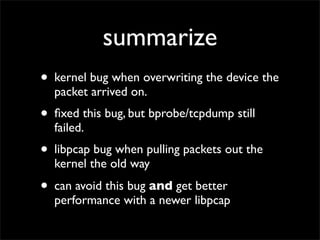
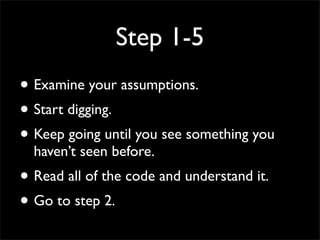
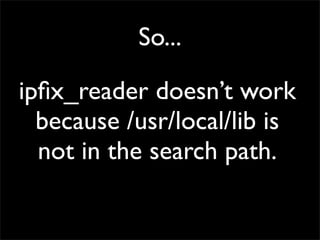
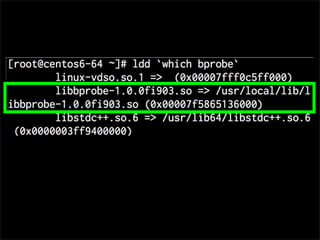
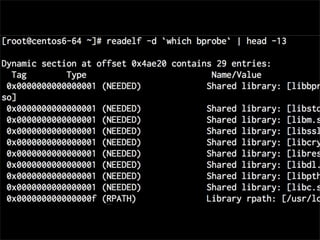
This document describes the process of debugging a packet sniffing issue when using bonded ethernet interfaces on Linux. The bug was initially found when incoming packets were not being detected when sniffing individual physical interfaces, even though outgoing packets were working. After carefully examining assumptions and digging through the kernel and libpcap code, the bug was found to be: 1) the kernel was overwriting the packet's device field, and 2) an older version of libpcap was incorrectly handling packets when using its legacy retrieval method. Updating the kernel fix and libpcap resolved the issue.