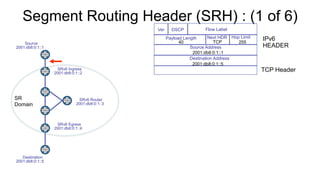
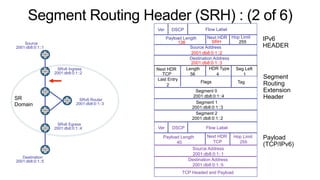
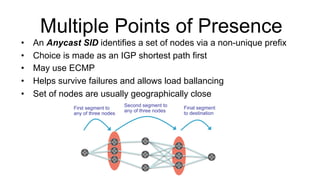
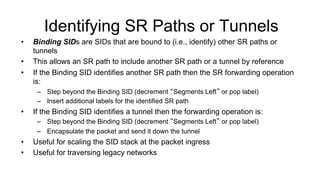
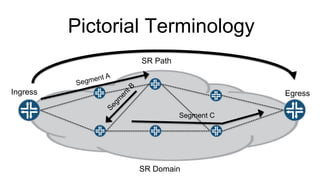
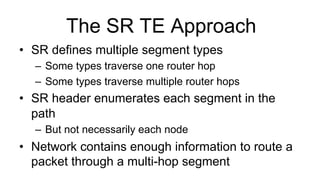
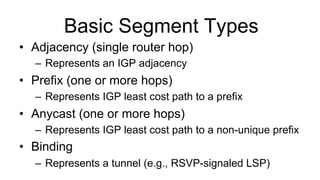
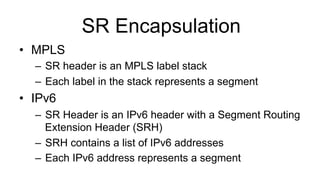
Segment Routing (SR) is a tunneling and traffic engineering technology that allows routers to steer traffic along an SR path that may differ from the normal shortest path. An SR path is divided into segments that connect points within the SR domain. Segments are represented by Segment Identifiers (SIDs) that can identify single hops or multiple hops. The SR header or MPLS label stack enumerates the segments in the path to forward packets. SR supports various segment types including adjacency, prefix, anycast, and binding segments. SR provides traffic engineering capabilities and flexibility in path selection within the domain.
![OAM
• MPLS Continuity Verification [ RFC 6428 ]
• MPLS Loss & Delay Measurement [ RFC 6374 & RFC
6375 ]
• MPLS Self-ping [RFC 7746]
• MPLS Ping [ RFC 8026 ]
– Ping Mode using NIL FEC
– Trace mode if every router in path copies TTL on pop
• MPLS-aware trace [RFC 4950]
– If every router in path copies TTL on pop](https://image.slidesharecdn.com/1bonicatutorialsegmentrouting-210622110219/85/1-bonica-tutorial_segment_routing-20-320.jpg)