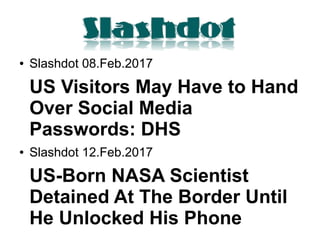
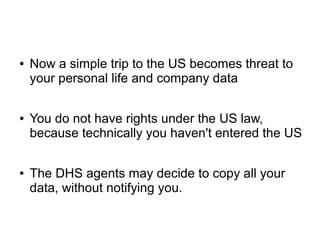
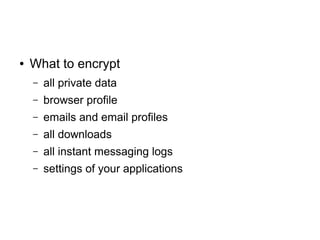
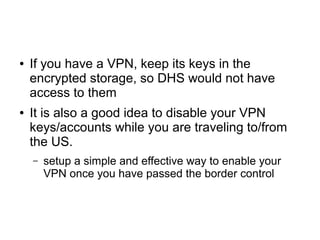
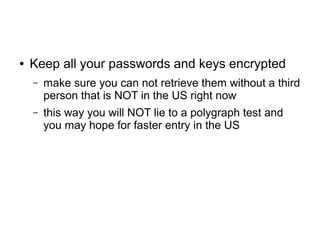
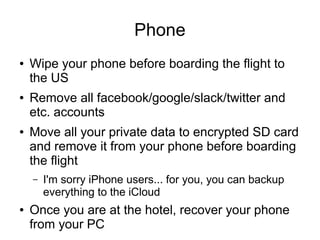
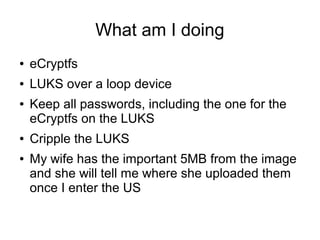
The document discusses concerns about personal data security when traveling to the US, particularly focusing on the demands of DHS agents for social media passwords and the potential consequences. It highlights the legal implications of data storage under EU privacy laws and provides strategies for travelers to protect their sensitive information, including encryption and data management practices. The author shares personal measures taken to secure data while navigating these issues.