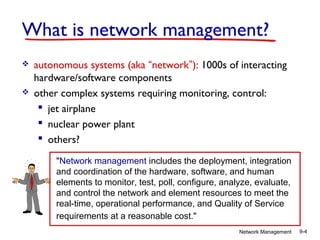
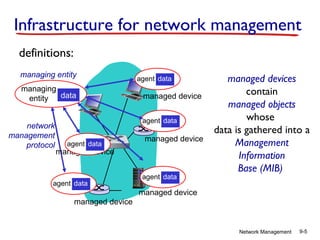
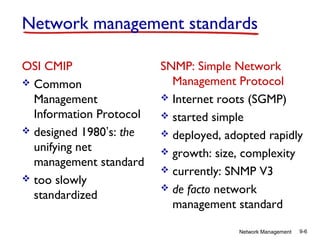
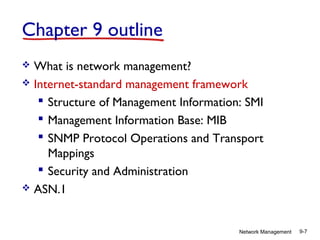
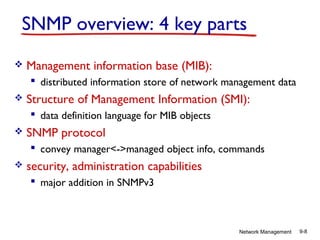
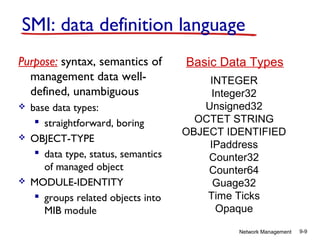
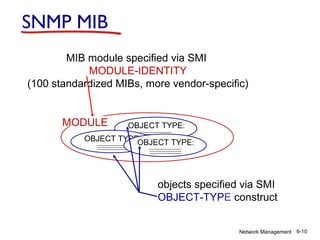
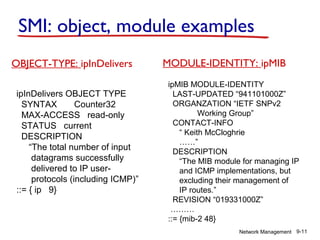
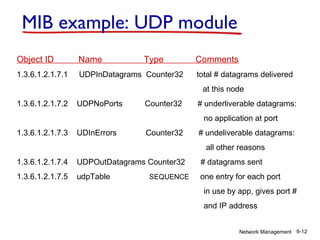
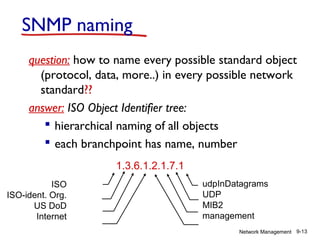
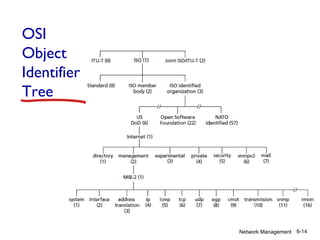
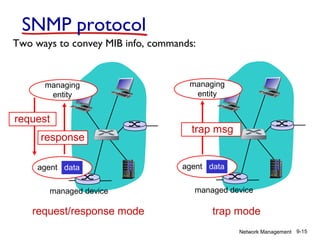
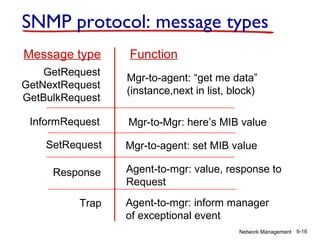
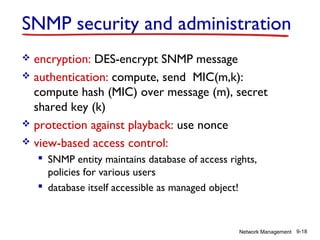
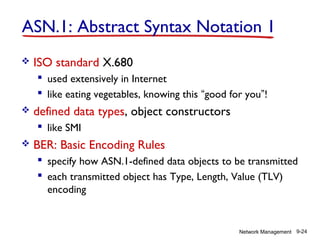
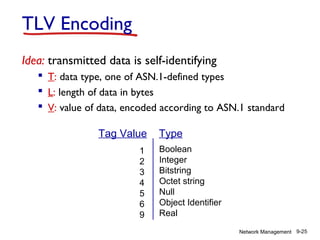
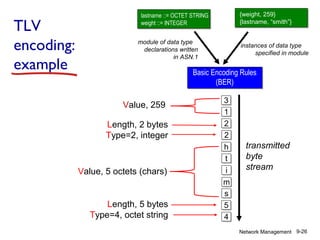
The document discusses network management and the Internet standard framework. It describes the key components of the framework, including the Structure of Management Information (SMI) which defines management objects, the Management Information Base (MIB) which stores the managed objects, and the Simple Network Management Protocol (SNMP) used to communicate between managing and managed devices. The framework also includes security and administration capabilities added in SNMPv3.