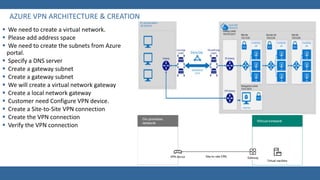
Azure virtual networks (VNet) allow users to logically isolate their Azure resources and expand their on-premises network to Azure. A VNet acts as a representation of a user's network in the cloud, allowing them to control IP addresses, DNS settings, security policies, and more. VNets can be segmented into subnets and connected to on-premises networks through options like site-to-site VPNs or Azure ExpressRoute. This provides enterprise-scale networking capabilities with connectivity and isolation similar to a traditional on-premises environment.