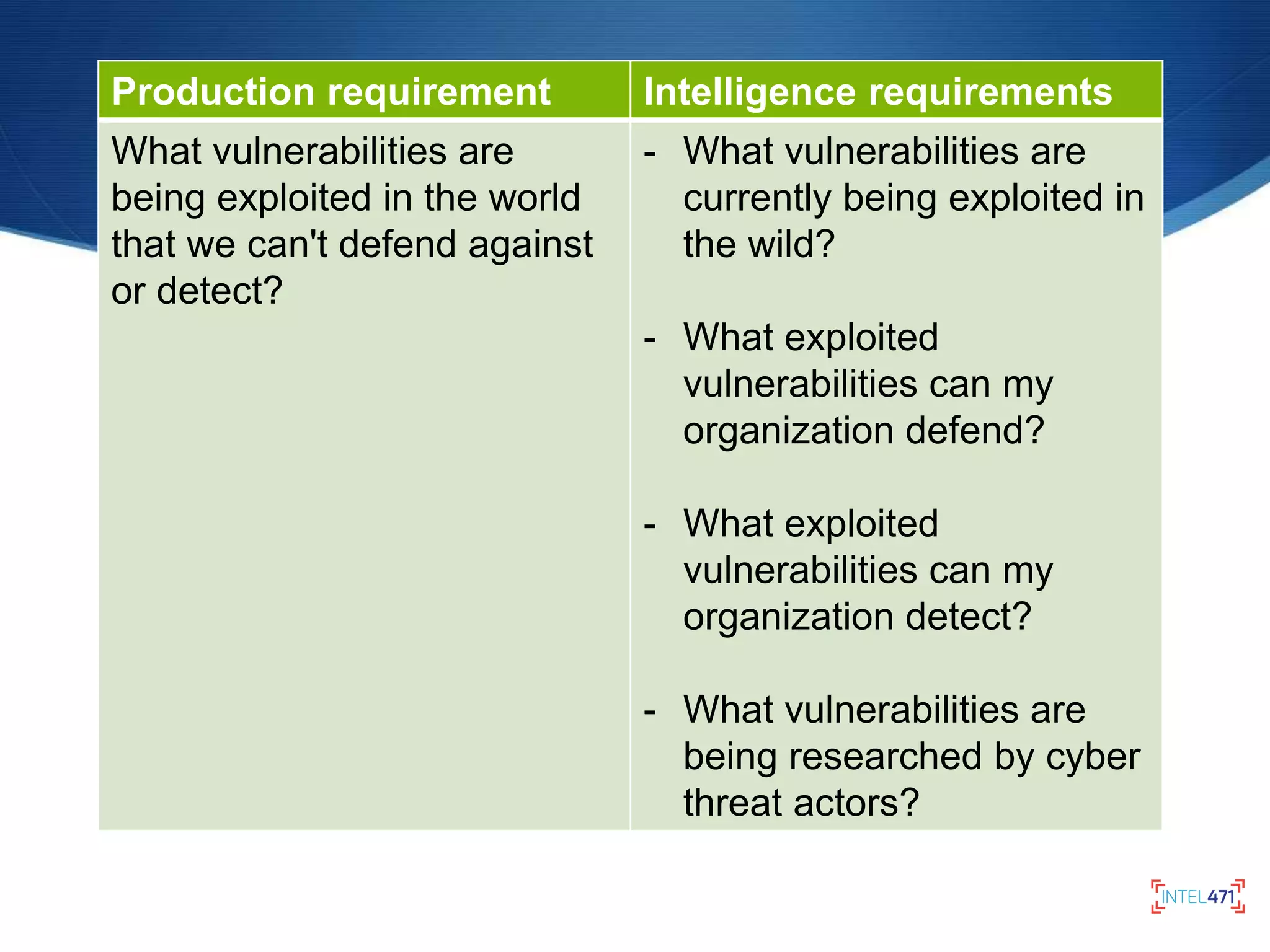
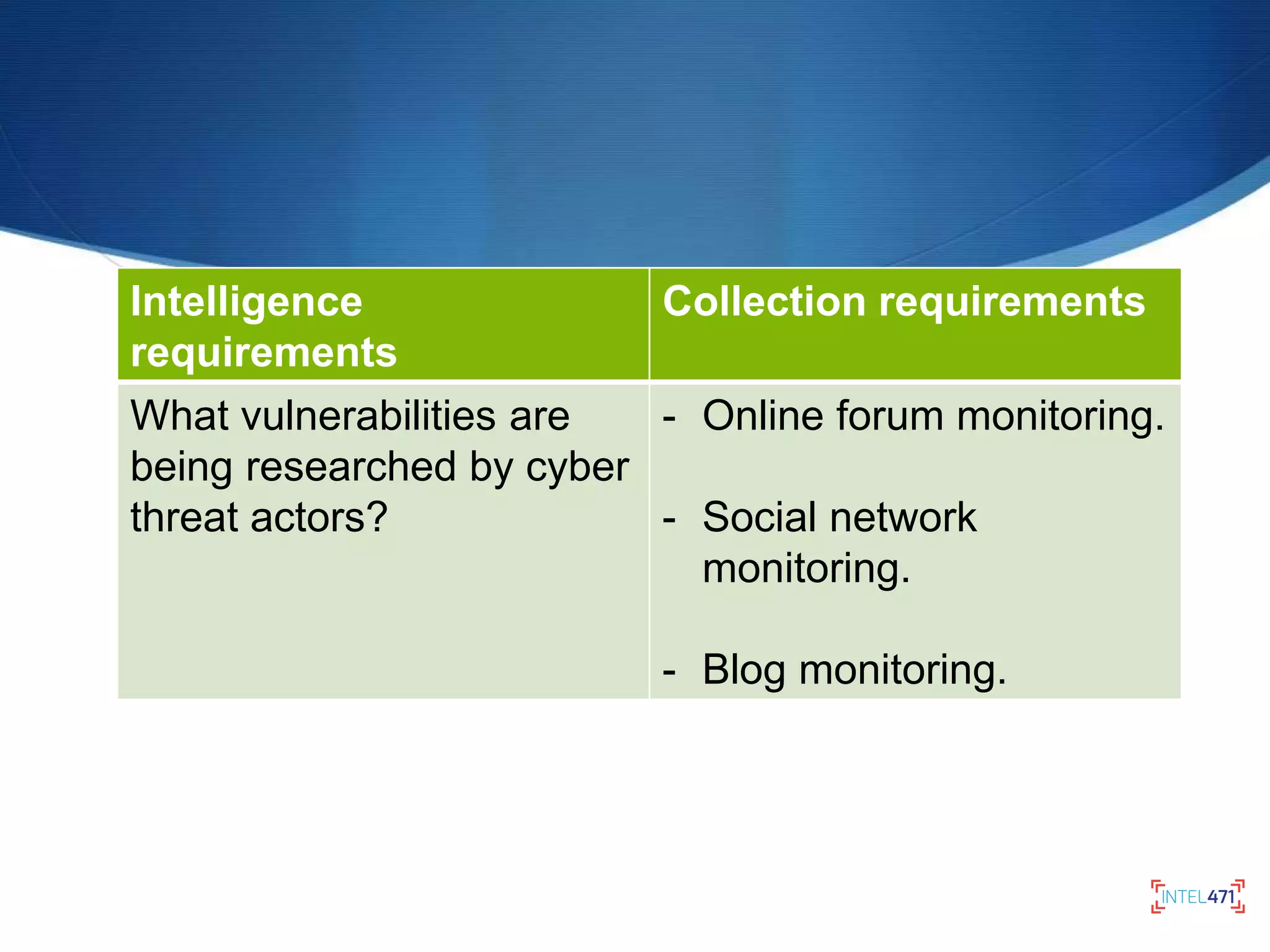
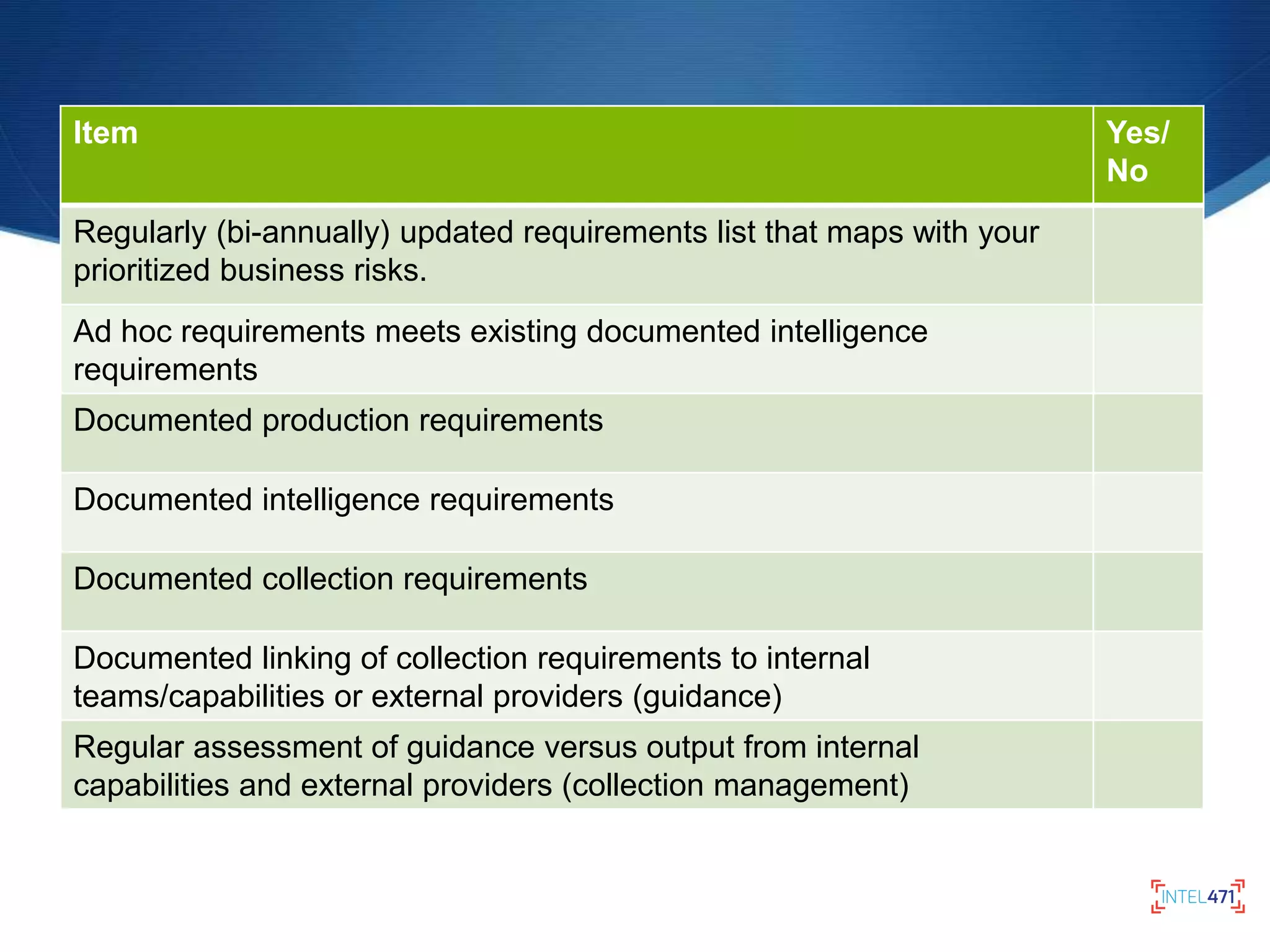
The document discusses the components and processes of cyber threat intelligence, emphasizing the importance of defining intelligence requirements, production, and collection to address potential threats effectively. It outlines the maturity of intelligence programs based on their ability to assess business risks and produce relevant intelligence outputs. Additionally, it highlights the need for continual updates to requirements, collaboration with other organizations, and measures for evaluating the effectiveness of intelligence products.