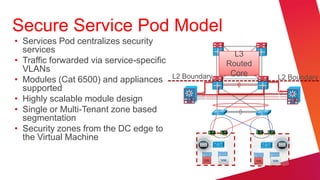
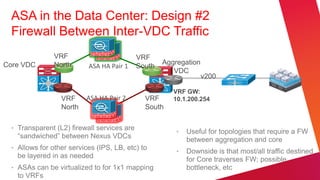
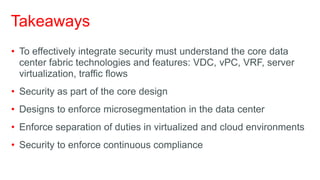
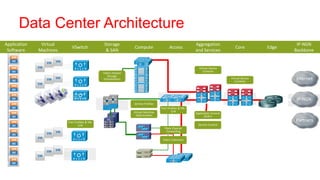
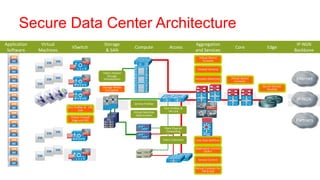
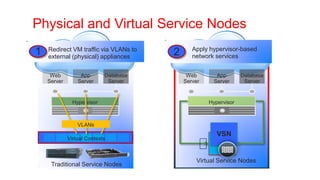
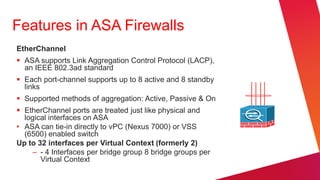
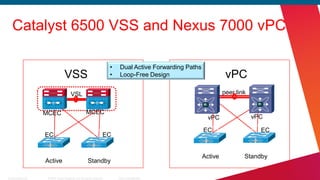
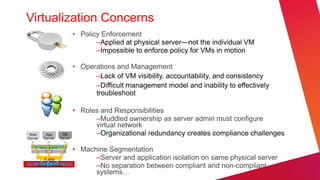
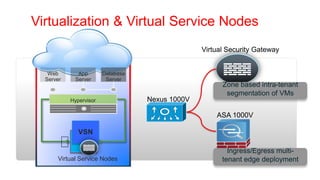
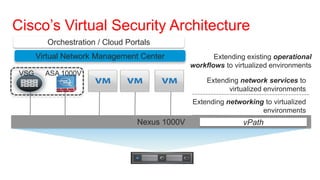
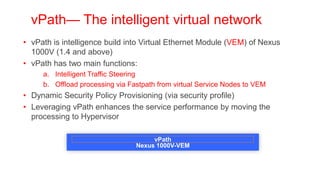
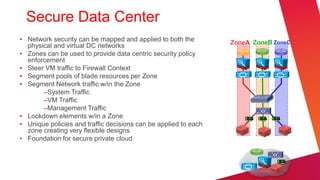
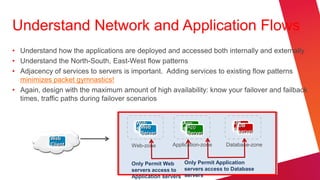
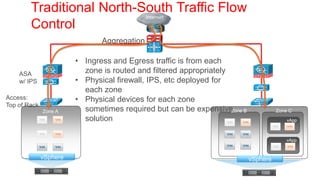
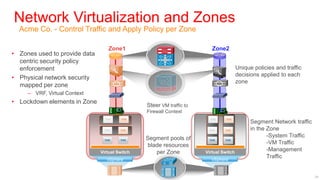
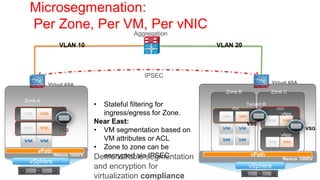
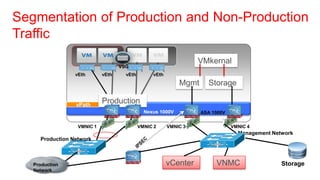
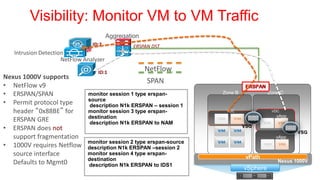
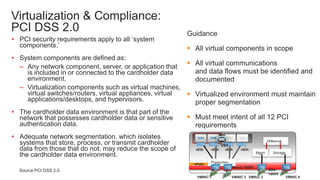
The document outlines best practices and security considerations for integrating security within data center virtualization, emphasizing the importance of understanding core data center technologies. Key takeaways include implementing microsegmentation, enforcing separation of duties, and ensuring continual compliance with standards like PCI. It also details various security components, challenges, and architectural designs essential for establishing a secure and efficient data center environment.






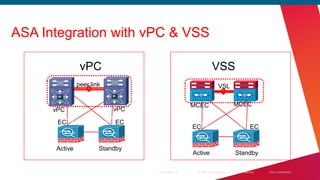

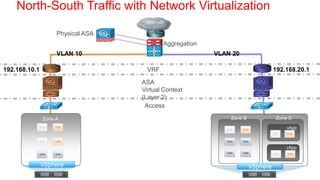

![ASA Details
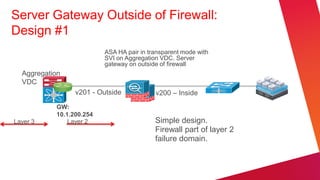
v201 - Outside v205 – Service-Out
BVI-1 BVI-2
10.1.204.199
10.1.200.199
[Po1.204]
[Po1.200]
[Po1.201] [Po1.205]
v200 – Inside v204 – Service-In
channel-group 1 mode passive
5585-1 5585-2
Twain Voltaire
vPC10
vPC9
7k-1 7k-2
AGG- AGG-
VDC VDC Port Channel Load-Balancing Configuration:
channel-group 1 mode active System: src-dst ip](https://image.slidesharecdn.com/data-center-security-and-virtualization-cisco-plus-grobson-120606075037-phpapp02/85/Security-and-Virtualization-in-the-Data-Center-42-320.jpg)