X / DRM (Direct Rendering Manager) Architectural Overview
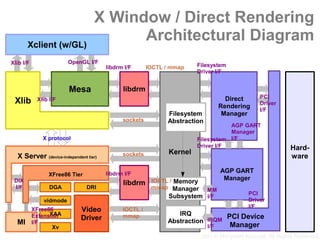
- 1. X Window / Direct Rendering Architectural Diagram Xclient (w/GL) OpenGL I/F Xlib I/F Filesystem libdrm I/F IOCTL / mmap Driver I/F Mesa libdrm PCI Direct Xlib Xlib I/F Driver Rendering I/F Manager Filesystem sockets Abstraction AGP GART Manager X protocol Filesystem I/F Driver I/F Hard- Kernel sockets X Server (device-independent tier) ware AGP GART libdrm I/F XFree86 Tier Manager DIX IOCTL / Memory libdrm I/F DGA DRI mmap Manager MM PCI Subsystem I/F Driver vidmode I/F Video XFree86 IOCTL / IRQ XAA PCI Device Extension mmap Driver Abstraction IRQM MI I/F Manager I/F Xv 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 2. X Window / Indirect Rendering Architectural Diagram Xclient (w/GL) OpenGL I/F Xlib I/F Filesystem Driver I/F Mesa PCI Direct Xlib Xlib I/F Driver Rendering I/F Manager Filesystem sockets Abstraction AGP GART Manager X protocol Filesystem I/F Driver I/F Hard- Kernel sockets X Server (DIX) ware GLX Mesa AGP GART XFree86 Tier libdrm I/F Manager DIX IOCTL / Memory libdrm I/F DGA DRI mmap Manager MM PCI Subsystem I/F Driver vidmode I/F Video XFree86 IOCTL / IRQ XAA PCI Device Extension mmap Driver Abstraction IRQM MI I/F Manager I/F Xv 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 3. Address Space Layout Kernel Space Graphics MMIO Aperture Space Physical User Space Address Space Actual RAM Space GART 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 4. Direct Memory Access 1. Queueing Kernel Space Graphic Controller Instruction Buffer DMA FIFO Transfer Marked Consistent IOCTL (BLIT etc.) User Space Some Process 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 5. Direct Memory Access 2. Bitmap Block Transfer (Blit) Kernel Space Graphic Controller Active Entry FIFO Parse & User Space Dispatch Some Marked Process Blit Engine Consistent DMA Transfer Another Process 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 6. DRM IOCTL I/F AUTH (GET_MAGIC / AUTH_MAGIC) ● VERSION (GET / SET) ● BUSID (GET / SET) ● MAP (ADD / RM) ● CTX (ADD / RM / GET / SWITCH / NEW / ● RESERVE) LOCK (LOCK / UNLOCK) ● AGP operations ● Device-specific operations ● 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 7. DRM Authentication 1. Retrieve Magic Cookie (drmGetMagic()) Cookie Manager Mesa libdrm 2. Generate Direct Xlib Magic Rendering Manager Cookie 3. Send Magic X protocol (XF86DRIAuthConnection()) 4. Authenticate Cookie (drmAuthMagic()) Kernel X Server XFree86 Tier libdrm DRI 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 8. DRM Authentication (Userland Wrappers) libdrm/xf86drm.c: (formally: xc/programs/Xserver/hw/xfree86/os-support/linux/drm/xf86drm.c) int drmGetMagic(int fd, drm_magic_t * magic) { drm_auth_t auth; *magic = 0; if (ioctl(fd, DRM_IOCTL_GET_MAGIC, &auth)) return -errno; *magic = auth.magic; return 0; } 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 9. DRM Authentication (Userland Wrappers) xc/programs/Xserver/hw/xfree86/dri/dri.c: Bool DRIAuthConnection(ScreenPtr pScreen, drm_magic_t magic) { DRIScreenPrivPtr pDRIPriv = DRI_SCREEN_PRIV(pScreen); if (drmAuthMagic(pDRIPriv->drmFD, magic)) return FALSE; return TRUE; } libdrm/xf86drm.c: (formally: xc/programs/Xserver/hw/xfree86/os-support/linux/drm/xf86drm.c) int drmAuthMagic(int fd, drm_magic_t magic) { drm_auth_t auth; auth.magic = magic; if (ioctl(fd, DRM_IOCTL_AUTH_MAGIC, &auth)) return -errno; return 0; } 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 10. DRM Authentication (linux/drivers/char/drm/drm_drv.c: IOCTL Dispatch Table) static drm_ioctl_desc_t drm_ioctls[] = { [DRM_IOCTL_NR(DRM_IOCTL_VERSION)] = {drm_version, 0}, [DRM_IOCTL_NR(DRM_IOCTL_GET_UNIQUE)] = {drm_getunique, 0}, [DRM_IOCTL_NR(DRM_IOCTL_GET_MAGIC)] = {drm_getmagic, 0}, [DRM_IOCTL_NR(DRM_IOCTL_IRQ_BUSID)] = {drm_irq_by_busid, DRM_MASTER|DRM_ROOT_ONLY}, [DRM_IOCTL_NR(DRM_IOCTL_GET_MAP)] = {drm_getmap, 0}, [DRM_IOCTL_NR(DRM_IOCTL_GET_CLIENT)] = {drm_getclient, 0}, [DRM_IOCTL_NR(DRM_IOCTL_SET_VERSION)] = {drm_setversion, DRM_MASTER|DRM_ROOT_ONLY}, [DRM_IOCTL_NR(DRM_IOCTL_AUTH_MAGIC)] = {drm_authmagic, DRM_AUTH|DRM_MASTER|DRM_ROOT_ONLY}, [DRM_IOCTL_NR(DRM_IOCTL_ADD_CTX)] = {drm_addctx, DRM_AUTH|DRM_ROOT_ONLY}, [DRM_IOCTL_NR(DRM_IOCTL_GET_CTX)] = {drm_getctx, DRM_AUTH}, ... 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 11. DRM Authentication (linux/drivers/char/drm/drm_drv.c: IOCTL Dispatcher) if (nr < DRIVER_IOCTL_COUNT) ioctl = &drm_ioctls[nr]; else if ((nr >= DRM_COMMAND_BASE) && (nr < DRM_COMMAND_BASE + dev->driver->num_ioctls)) ioctl = &dev->driver->ioctls[nr - DRM_COMMAND_BASE]; else goto err_i1; func = ioctl->func; /* is there a local override? */ if ((nr == DRM_IOCTL_NR(DRM_IOCTL_DMA)) && dev->driver->dma_ioctl) func = dev->driver->dma_ioctl; if (!func) { DRM_DEBUG(quot;no functionnquot;); retcode = -EINVAL; } else if (((ioctl->flags & DRM_ROOT_ONLY) && !capable(CAP_SYS_ADMIN)) || ((ioctl->flags & DRM_AUTH) && !priv->authenticated) || ((ioctl->flags & DRM_MASTER) && !priv->master)) { retcode = -EACCES; } else { retcode = func(inode, filp, cmd, arg); } 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 12. DRM Authentication (linux/drivers/char/drm/drm_auth.c: Cookie Issuer) int drm_getmagic(struct inode *inode, struct file *filp, unsigned int cmd, unsigned long arg) { ... typedef unsigned int drm_magic_t; /* Find unique magic */ if (priv->magic) { typedef struct drm_auth { auth.magic = priv->magic; drm_magic_t magic; } else { do { } drm_auth_t; spin_lock(&lock); if (!sequence) ++sequence;/* reserve 0 */ auth.magic = sequence++; spin_unlock(&lock); } while (drm_find_file(dev, auth.magic)); priv->magic = auth.magic; drm_add_magic(dev, priv, auth.magic); } DRM_DEBUG(quot;%unquot;, auth.magic); if (copy_to_user((drm_auth_t __user *) arg, &auth, sizeof(auth))) return -EFAULT; return 0; } 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 13. DRM Authentication (linux/drivers/char/drm/drm_auth.c: Cookie Verifier) int drm_authmagic(struct inode *inode, struct file *filp, unsigned int cmd, unsigned long arg) { drm_file_t *priv = filp->private_data; drm_device_t *dev = priv->head->dev; drm_auth_t auth; drm_file_t *file; if (copy_from_user(&auth, (drm_auth_t __user *) arg, sizeof(auth))) return -EFAULT; DRM_DEBUG(quot;%unquot;, auth.magic); if ((file = drm_find_file(dev, auth.magic))) { file->authenticated = 1; drm_remove_magic(dev, auth.magic); return 0; } return -EINVAL; } 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 14. DRM Authentication (linux/drivers/char/drm/drm_auth.c: Cookie Keeper) static drm_file_t *drm_find_file(drm_device_t * dev, drm_magic_t magic) { drm_file_t *retval = NULL; drm_magic_entry_t *pt; int hash = drm_hash_magic(magic); mutex_lock(&dev->struct_mutex); for (pt = dev->magiclist[hash].head; pt; pt = pt->next) { if (pt->magic == magic) { retval = pt->priv; break; } } mutex_unlock(&dev->struct_mutex); return retval; } 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 15. Graphic Address Remapping Table (GART) SAREA Frame Buffer Phy-Phy Address Translation Texture Buffer Process #1 (by AGP controller) Graphics MMIO Aperture Virtual Space Memory Space Physical Process #2 Address Space Actual Virtual RAM Memory Space Space GART Phy-Virt Address Translation (by MMU) 2007 © Moriyoshi Koizumi. All Rights Reserved.
- 16. AGPGART IOCTL I/F ACQUIRE ● SETUP ● RESERVE ● PROTECT ● ALLOCATE / DEALLOCATE ● BIND / UNBIND ● 2007 © Moriyoshi Koizumi. All Rights Reserved.