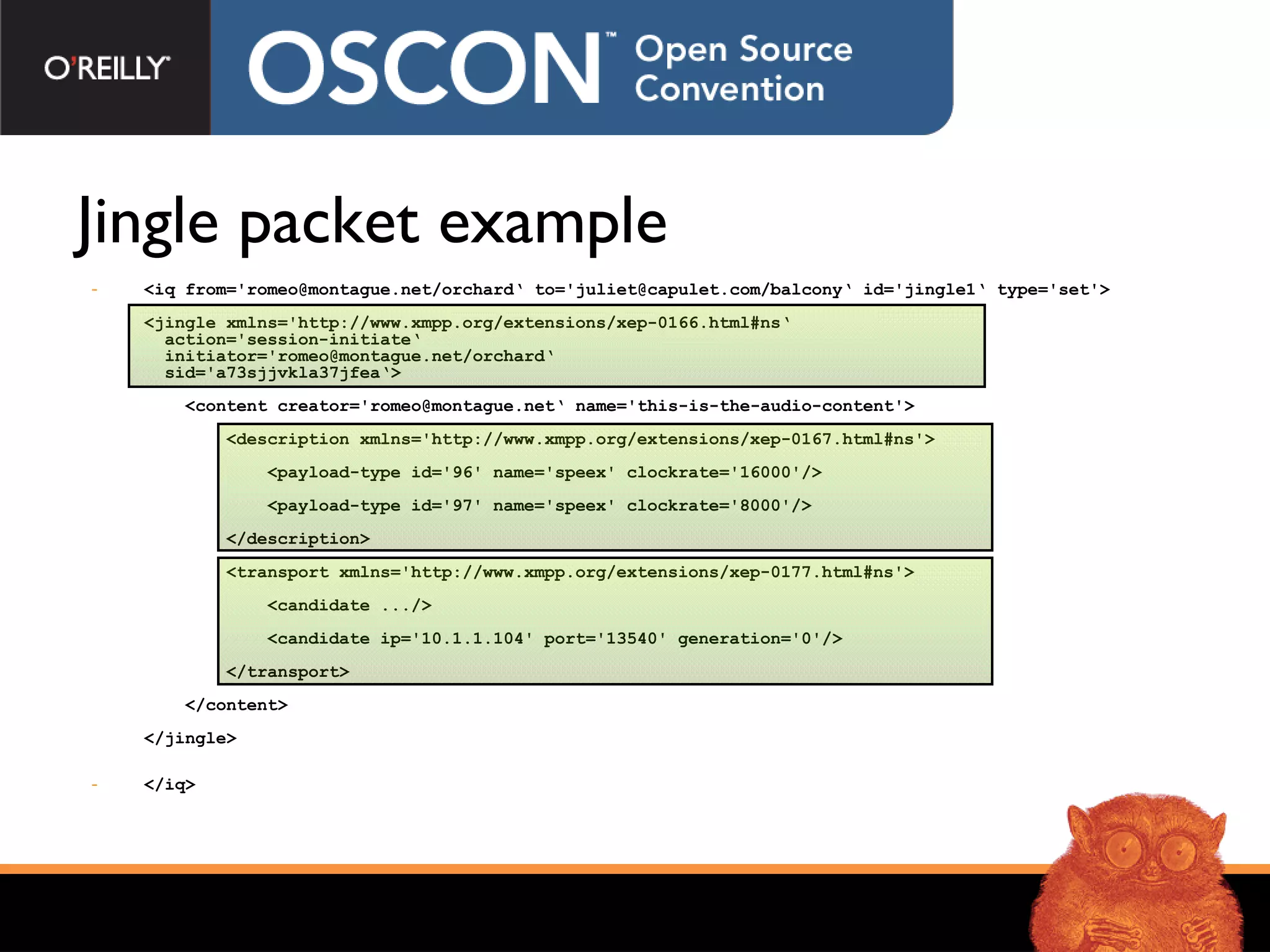
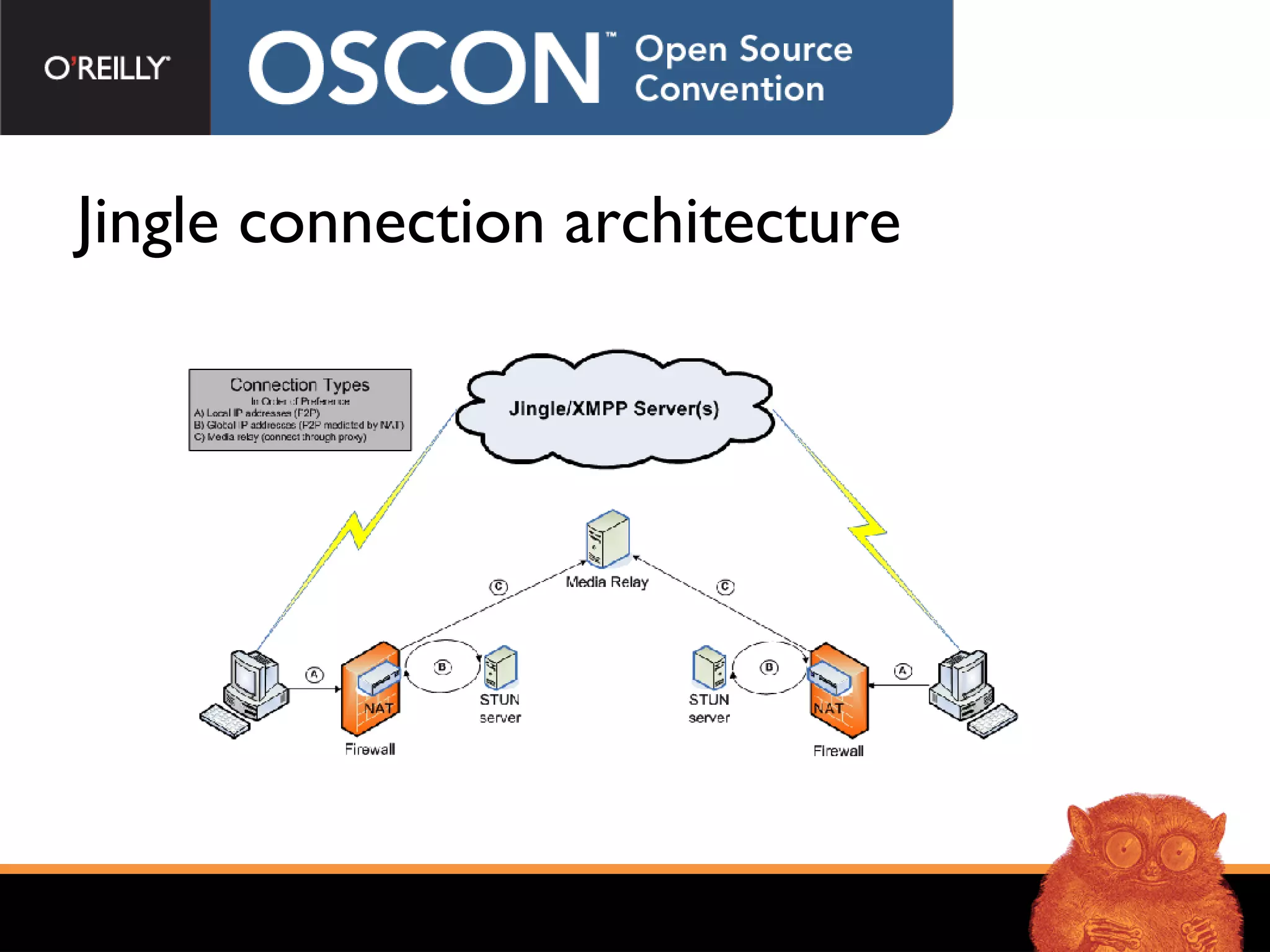
The document discusses Jingle, an open standard protocol for real-time communication like voice and video calls over the XMPP protocol. Jingle allows for peer-to-peer connections using techniques like STUN and ICE to traverse NATs and firewalls, with the ability to fallback to using media servers. It describes the Jingle protocol which negotiates sessions and transports in three steps. Open source libraries and servers like libjingle and Openfire support Jingle implementations.












![“ Crazy stuff”: punching through NATs Step 1: use a STUN server to find your public IP address Me: Hey STUN server, I don’t know my IP Address. Can you help? NUTS (the STUN server): Looking at the packet you sent me, I see that the IP address of your NAT device is AAA.BBB.CCC.DDD Me: Sweet! Step 2: figure out more stuff using the STUN server Me: Ok, now I want to check to see what my NAT device does with ports. Does the public port change when I connect to different IP addresses? NUTS: Well, good question. I have another IP address you can connect to in order to try that. Me: Awesome, I tried that out and now I know more about my NAT device. Based on my local addresses, what you told me, plus what the other guy told me, I now have have a bunch of address/port options I can try with the other party. NUTS: No problem, glad to help! Buh-bye. Step 3: connectivity checking to try to create a hole Me: Can you hear me on this IP/port? You: … [Silence] Me: Hmm, the last one didn’t work. How about this one? You: … [Silence] Me: This is taking awhile… arg! How about this one? You: I hear you, I hear you! Yay, we found a hole. (Punching holes works better with UDP vs. TCP)](https://image.slidesharecdn.com/jingle-cutting-edge-voip3446/75/Jingle-Cutting-Edge-VoIP-19-2048.jpg)


![Questions? Contact me via IM or email: [email_address] Resources http://www.xmpp.org http://www.igniterealtime.org Secure Communications with Jabber Peter Saint-Andre Time: 11:35AM - 12:20PM Location: D137-138](https://image.slidesharecdn.com/jingle-cutting-edge-voip3446/75/Jingle-Cutting-Edge-VoIP-25-2048.jpg)