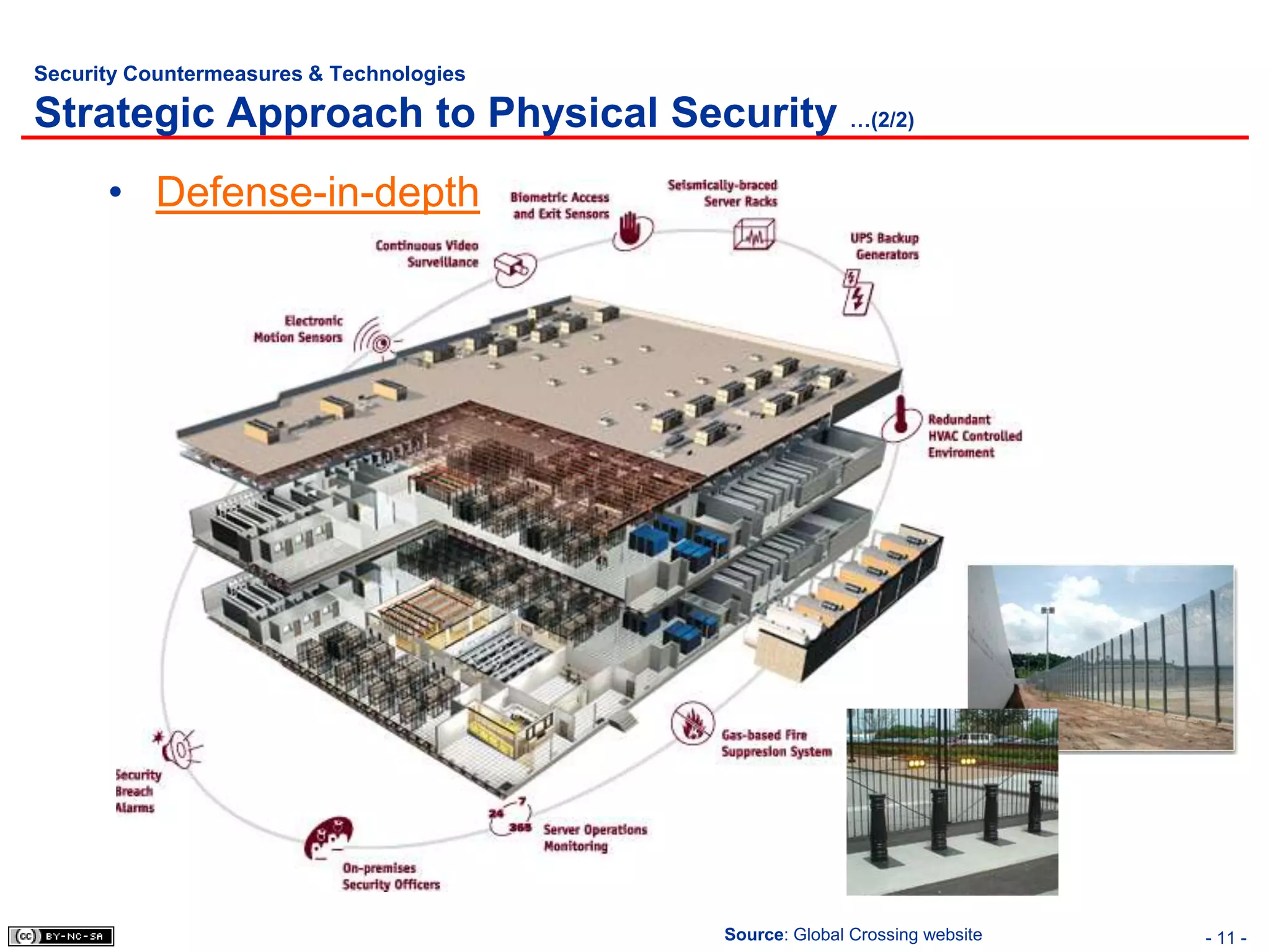
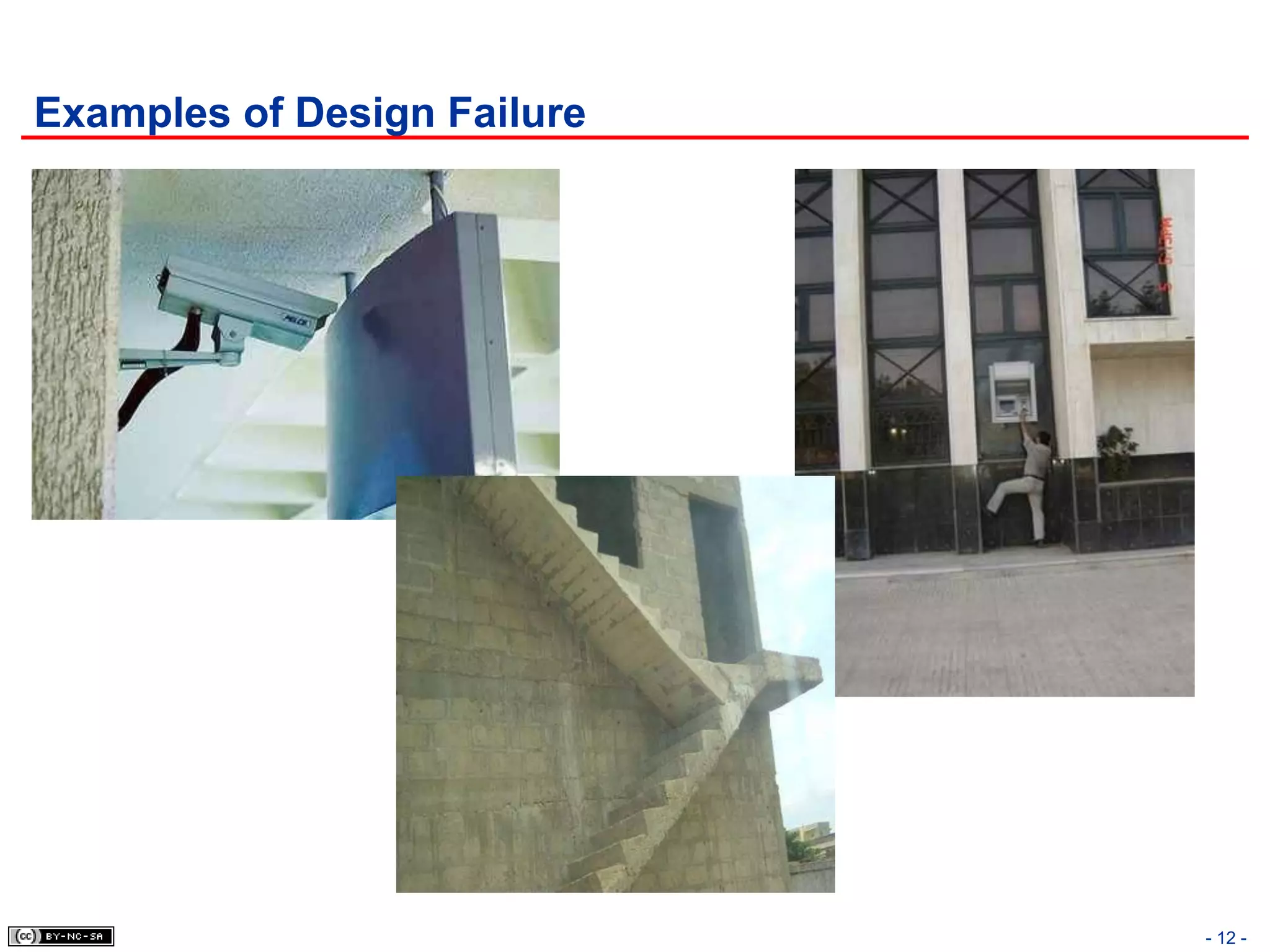
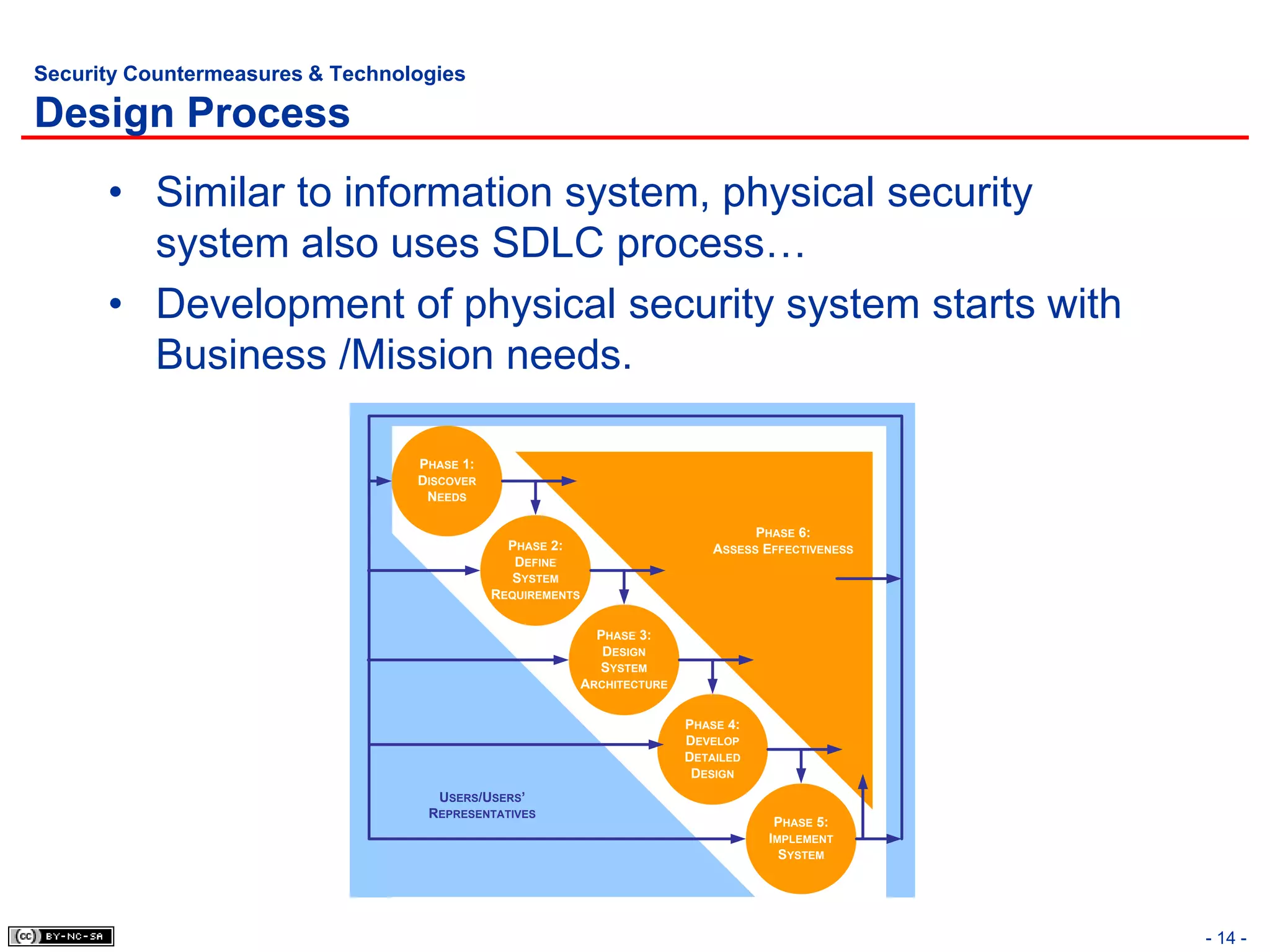
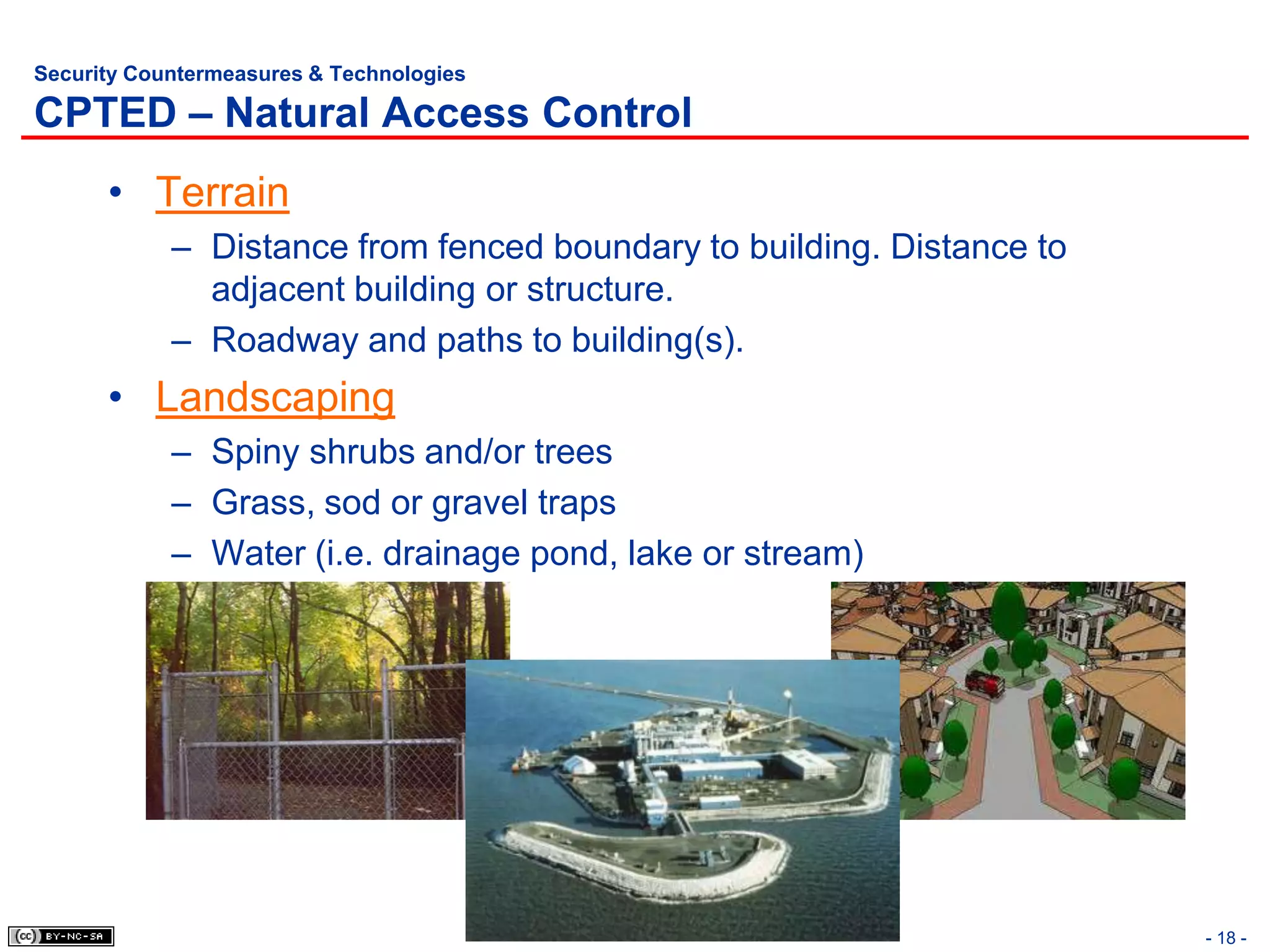
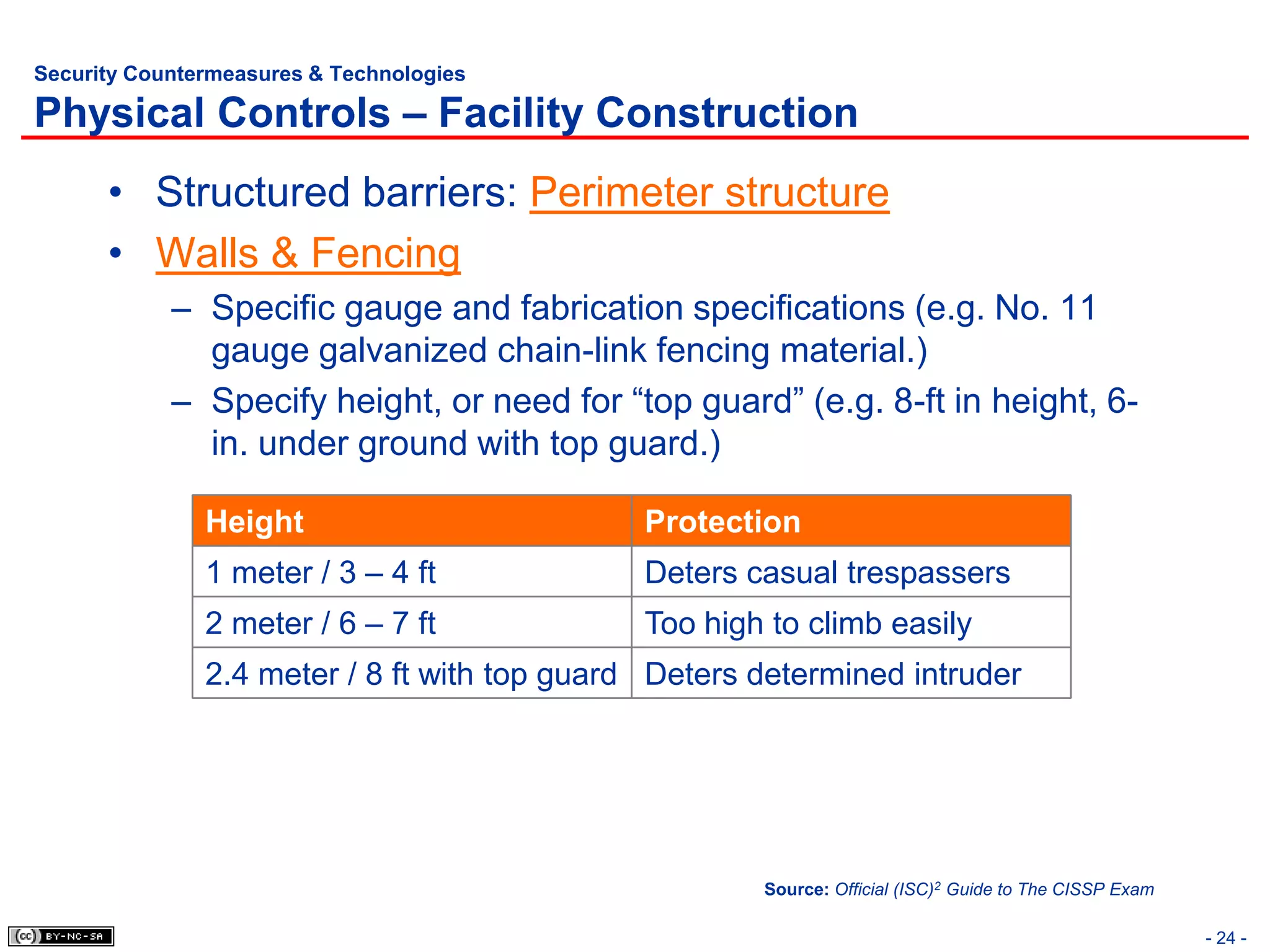
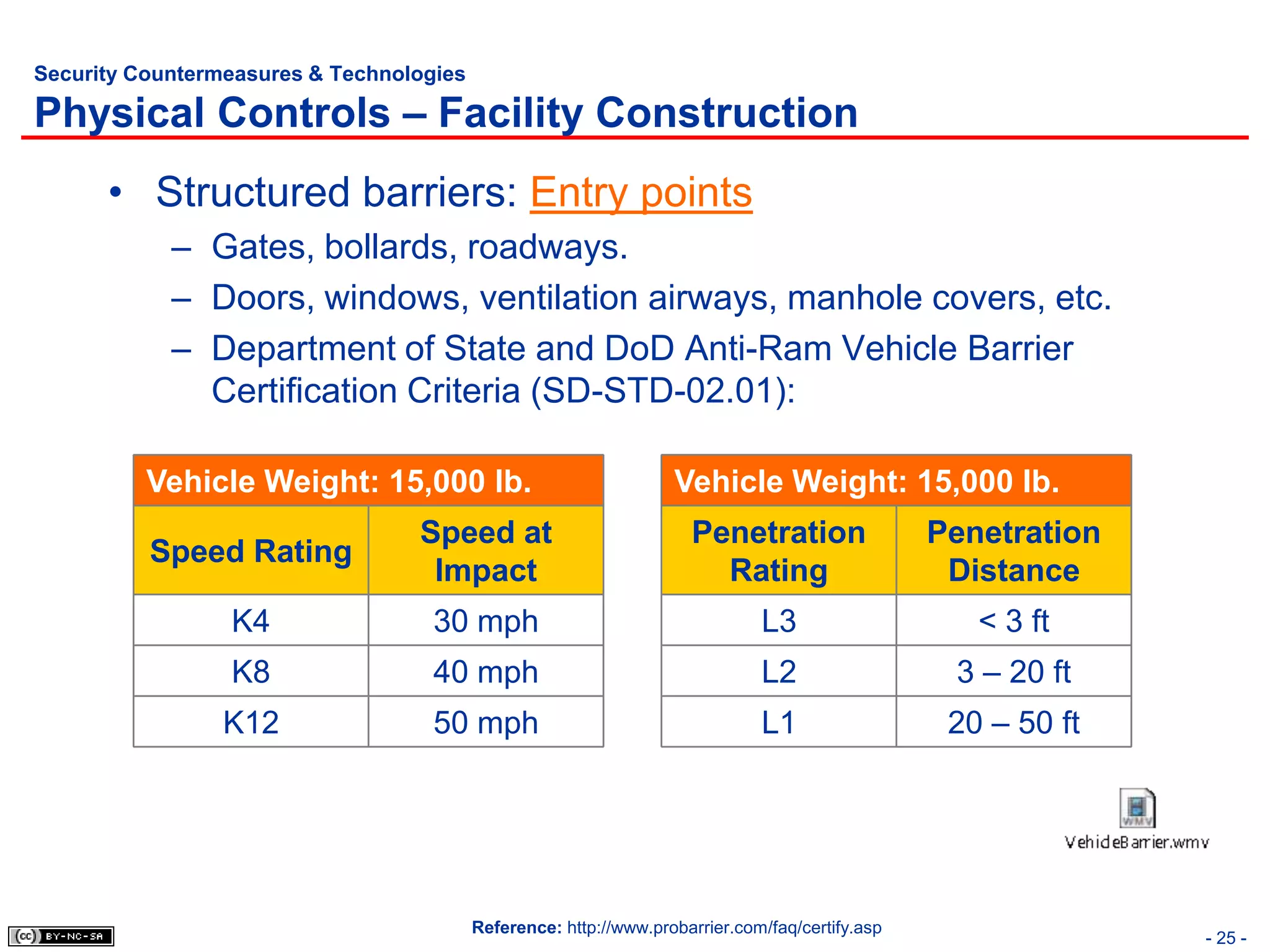
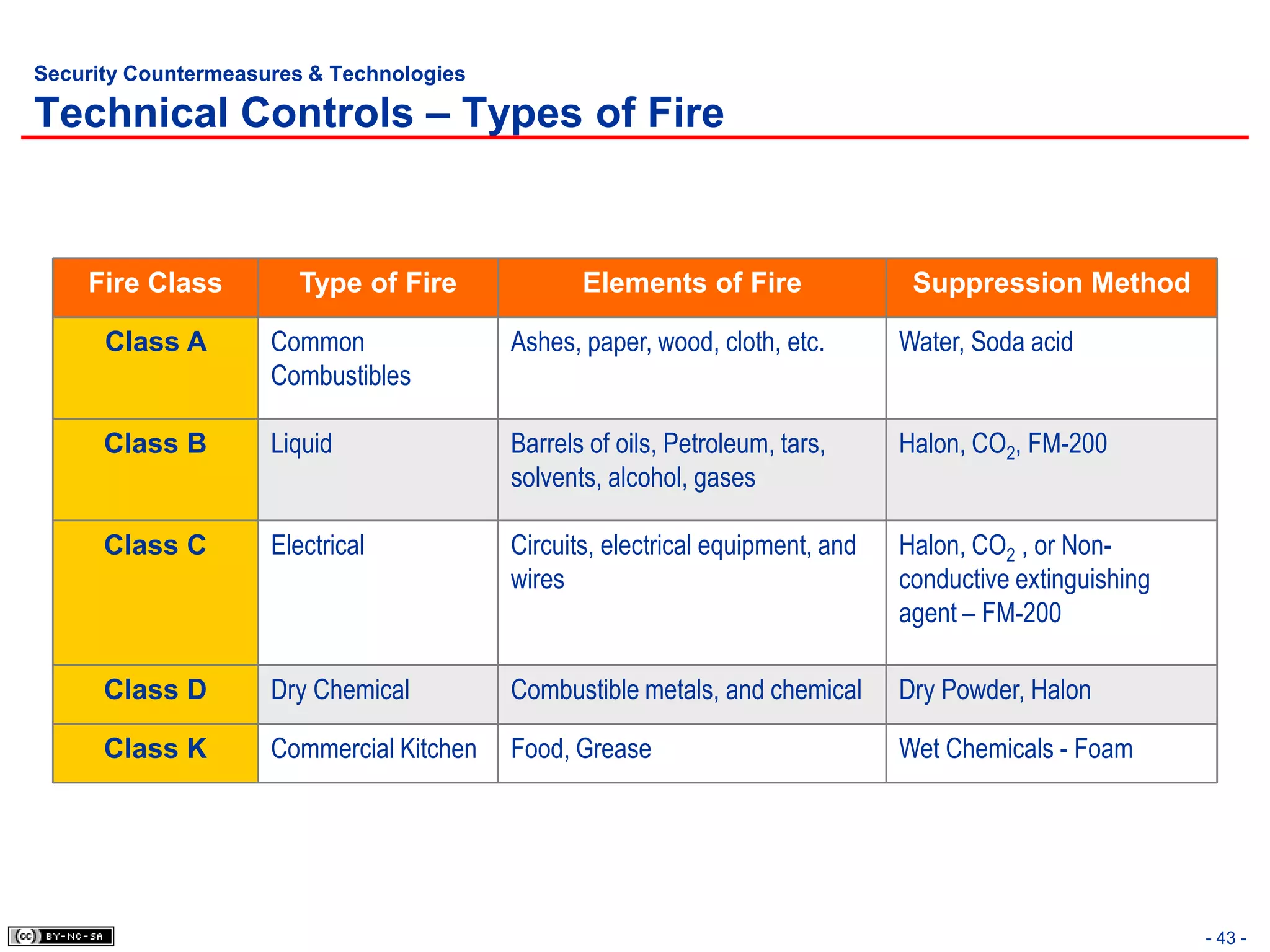
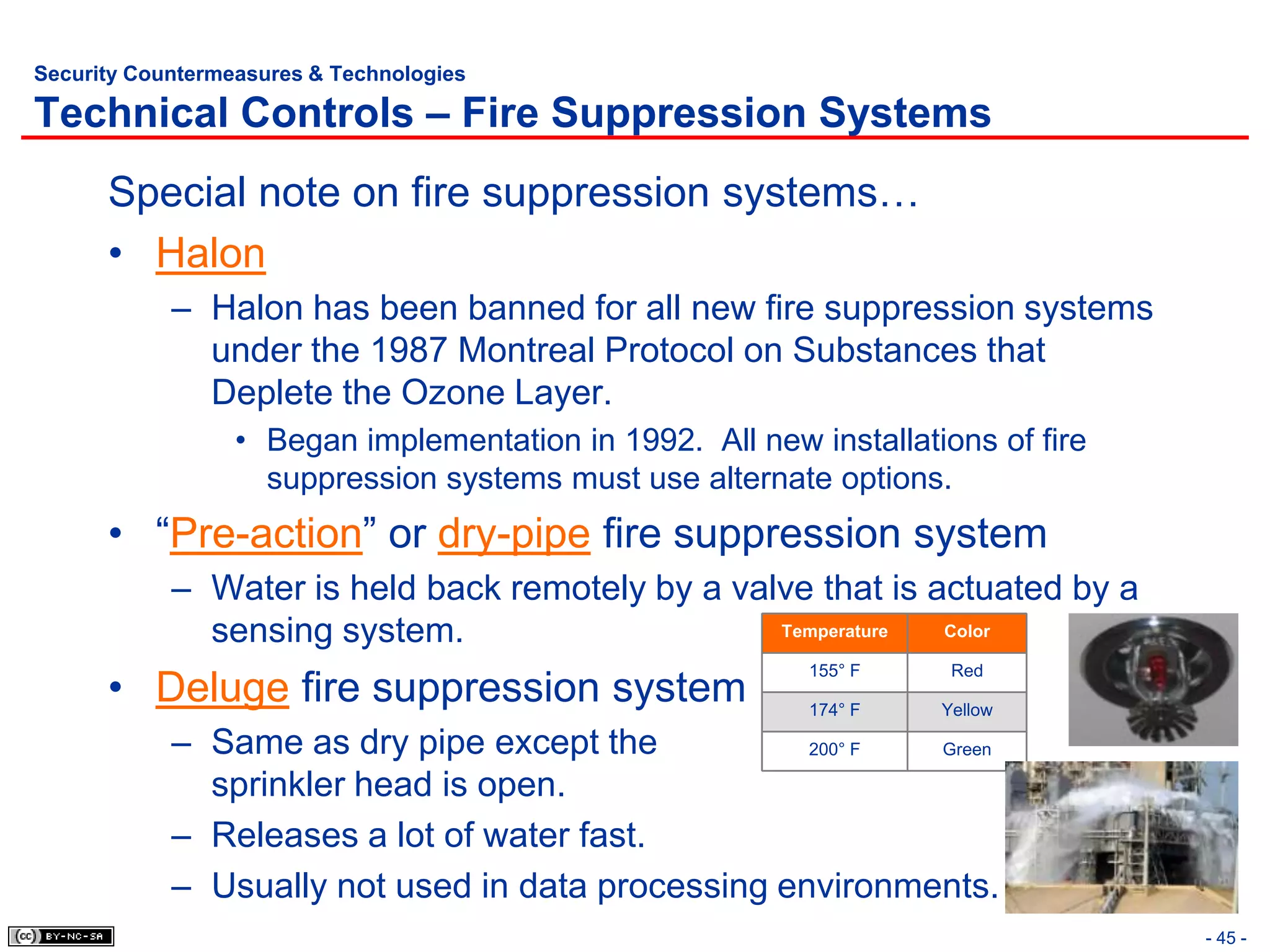
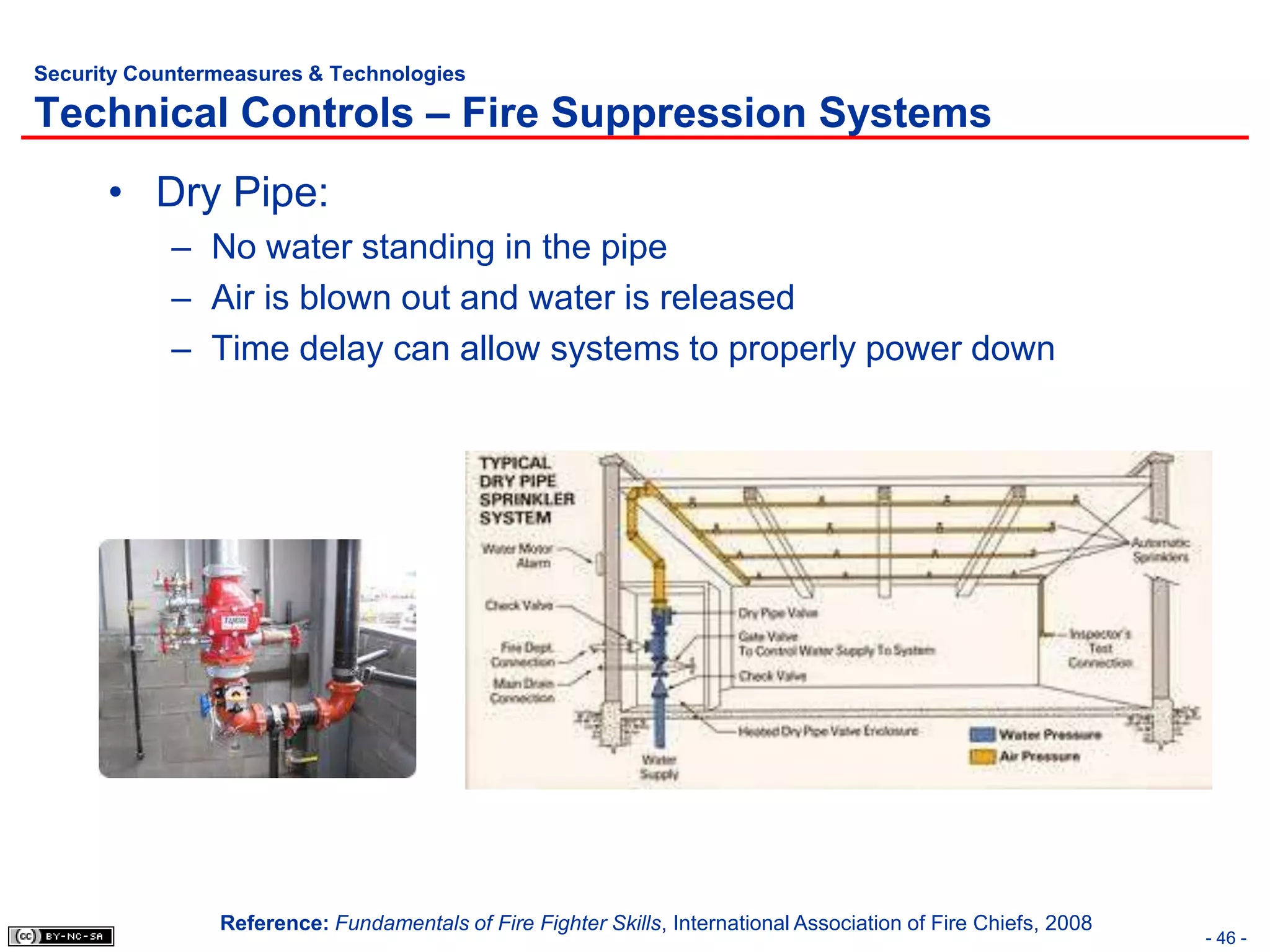
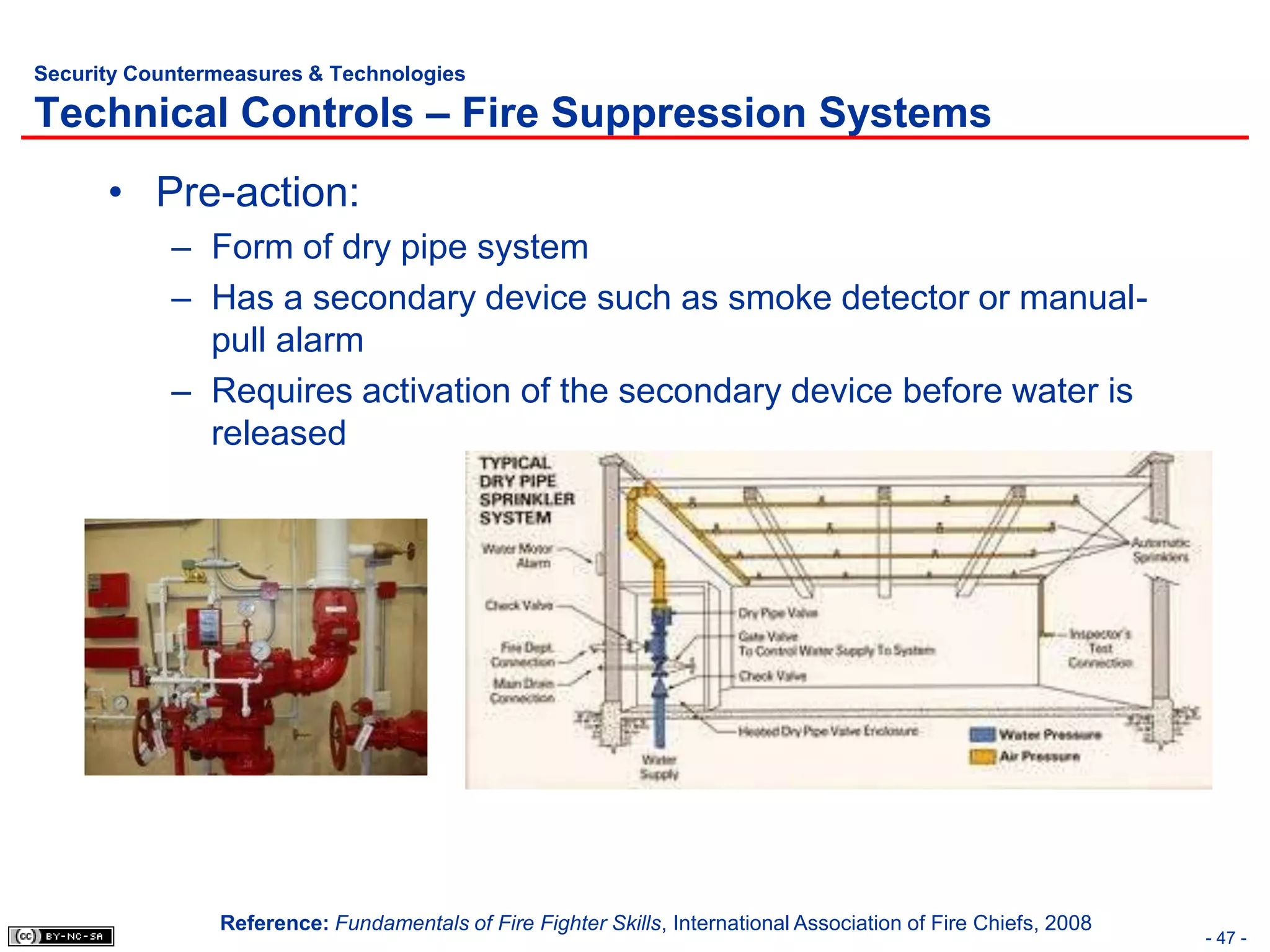
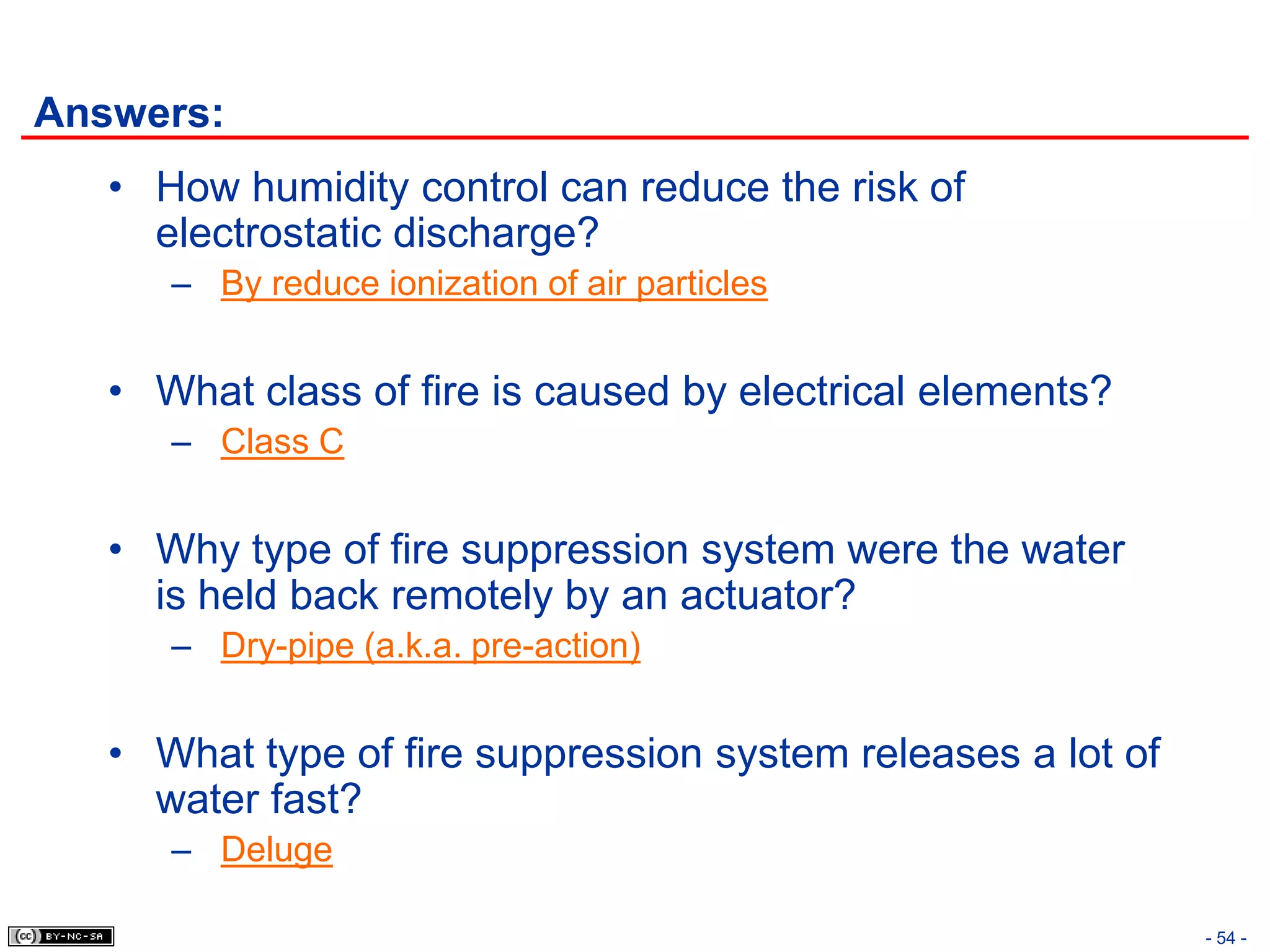
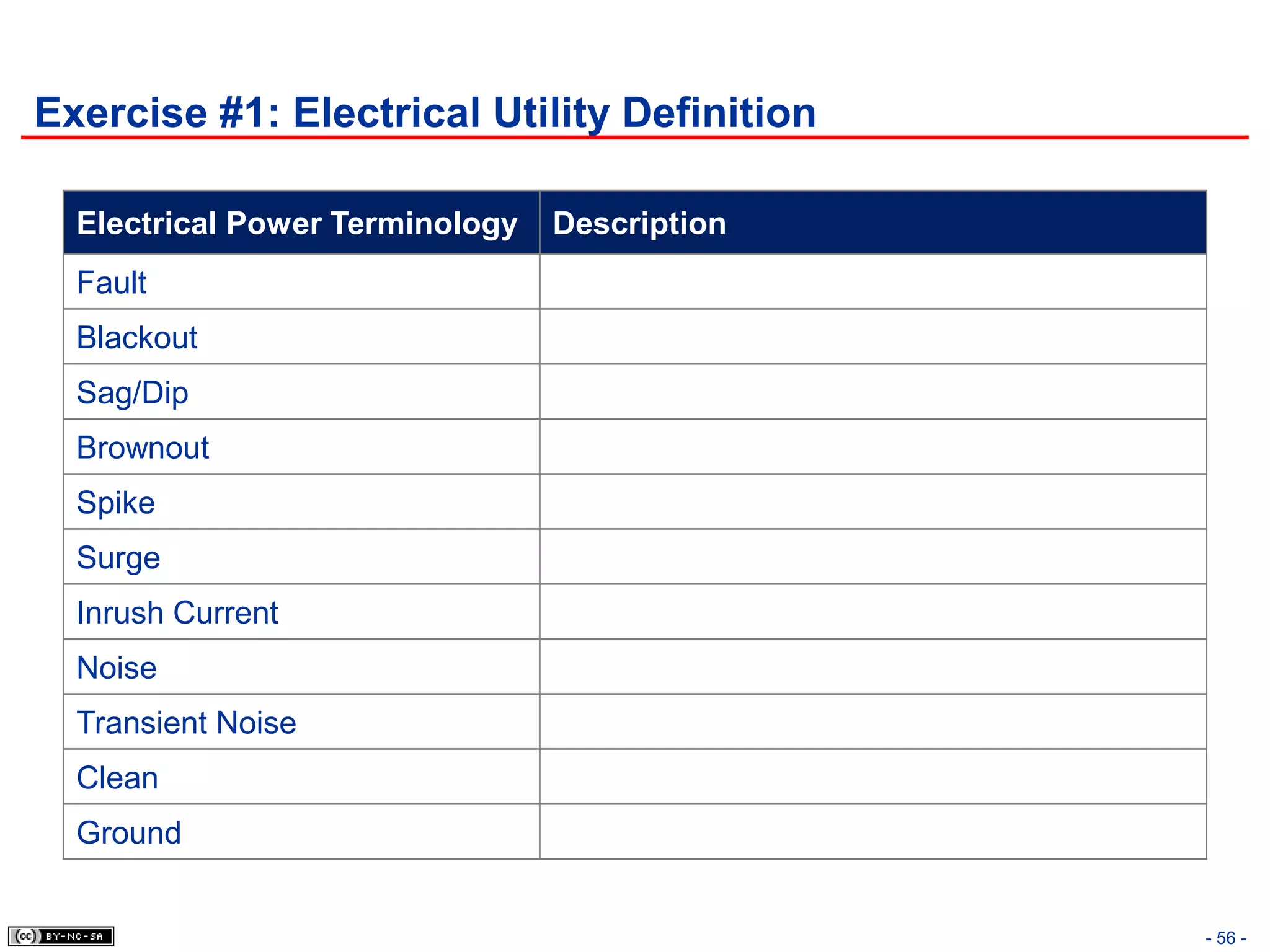
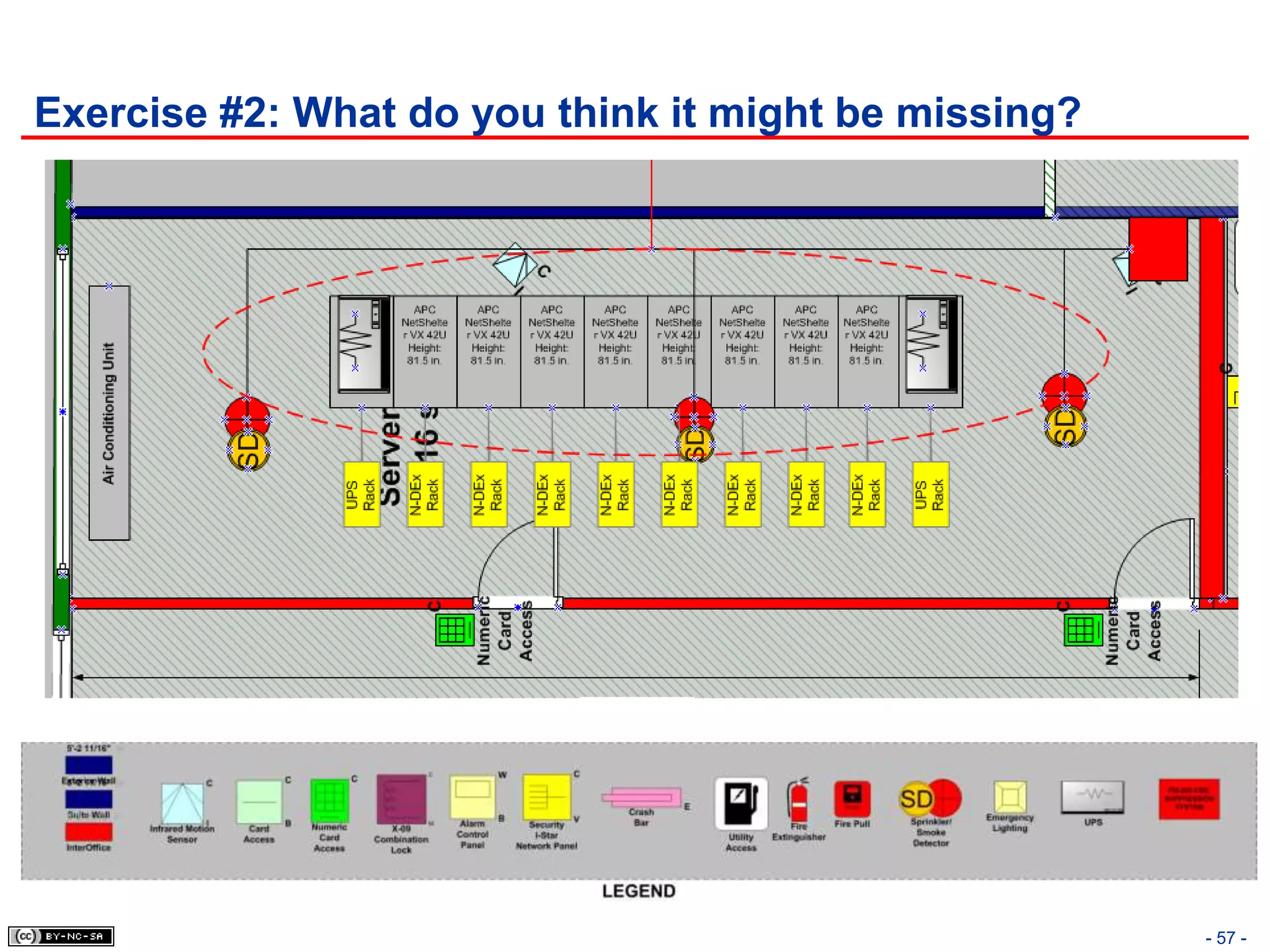
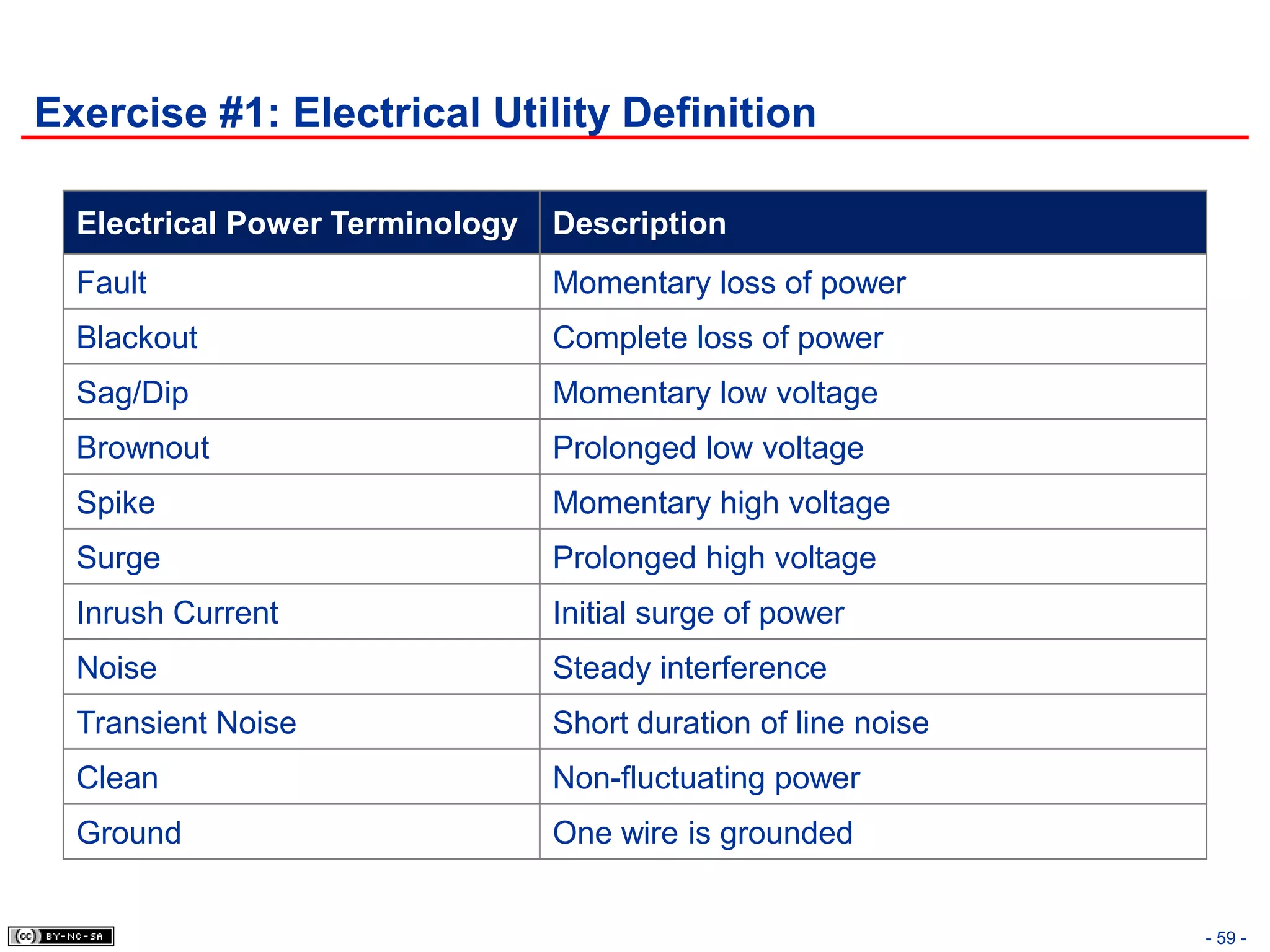
This document discusses the Physical (Environmental) Security domain of the CISSP Common Body of Knowledge. It covers topics such as defining physical security, types of threats to the physical environment like natural/environmental and man-made/political events. It also discusses security countermeasures and technologies to protect physical assets, including administrative, technical, and physical controls. Specific controls covered include perimeter security, building access controls, data center security, and the strategic application of crime prevention through environmental design principles.