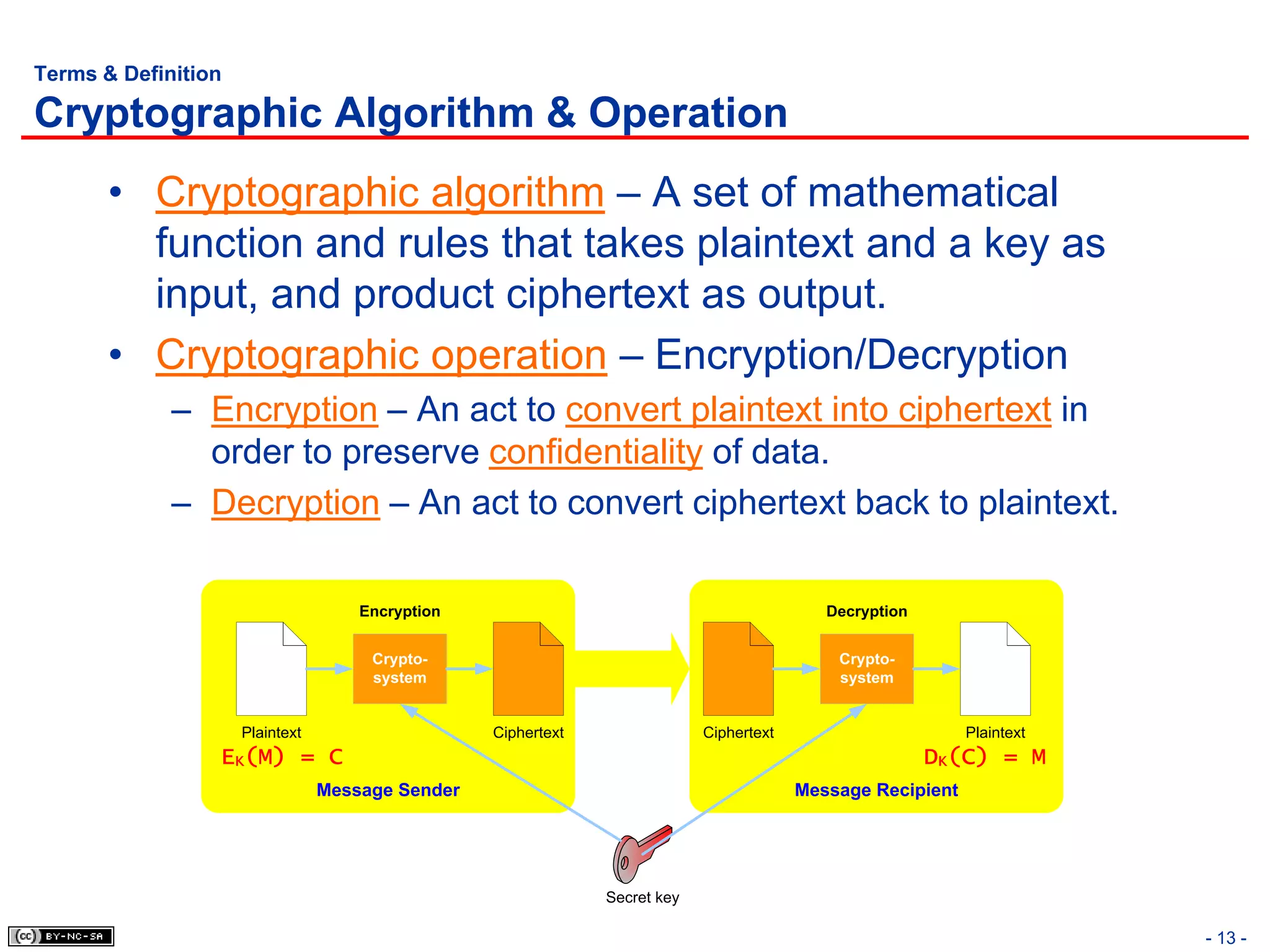
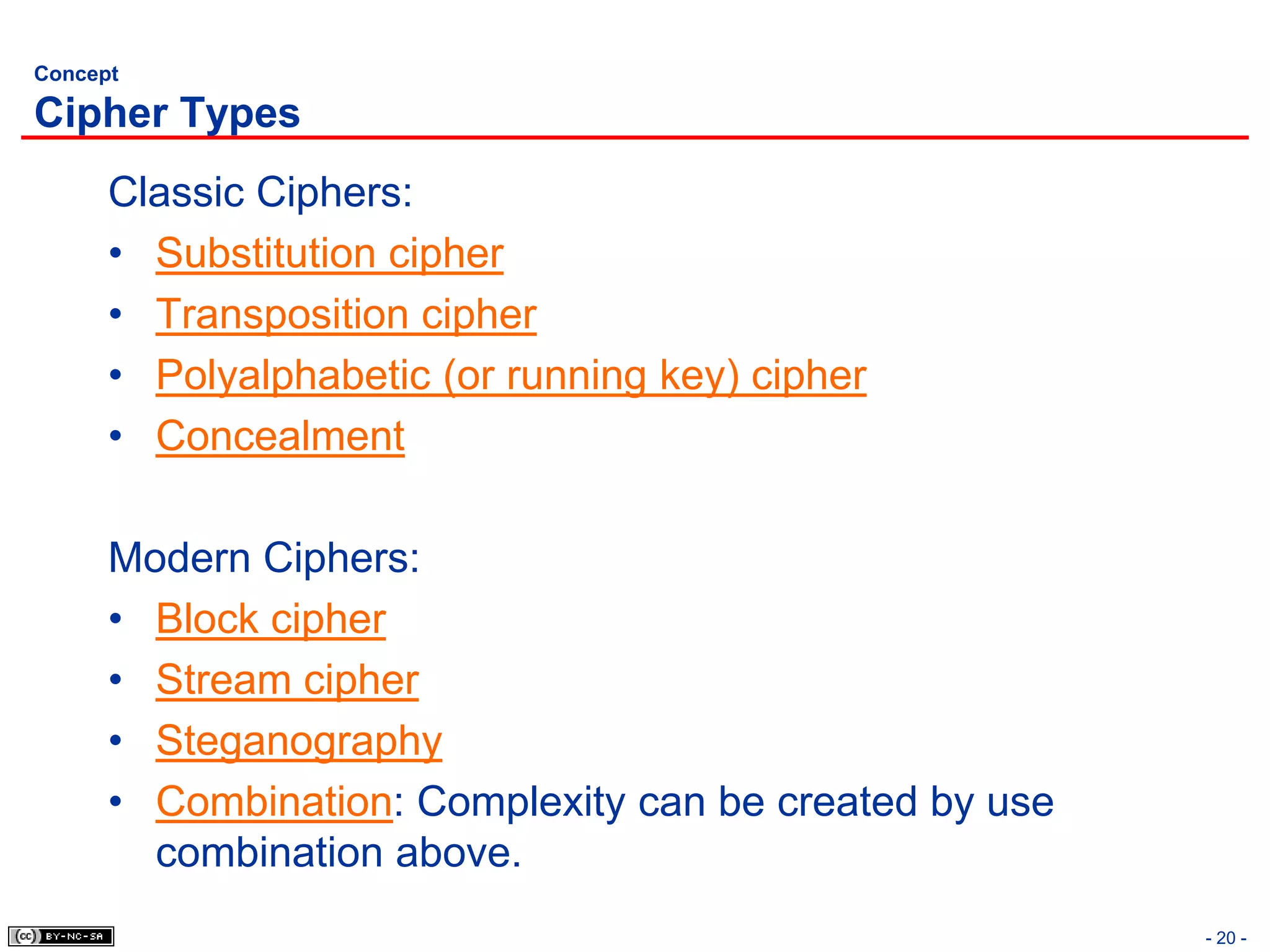
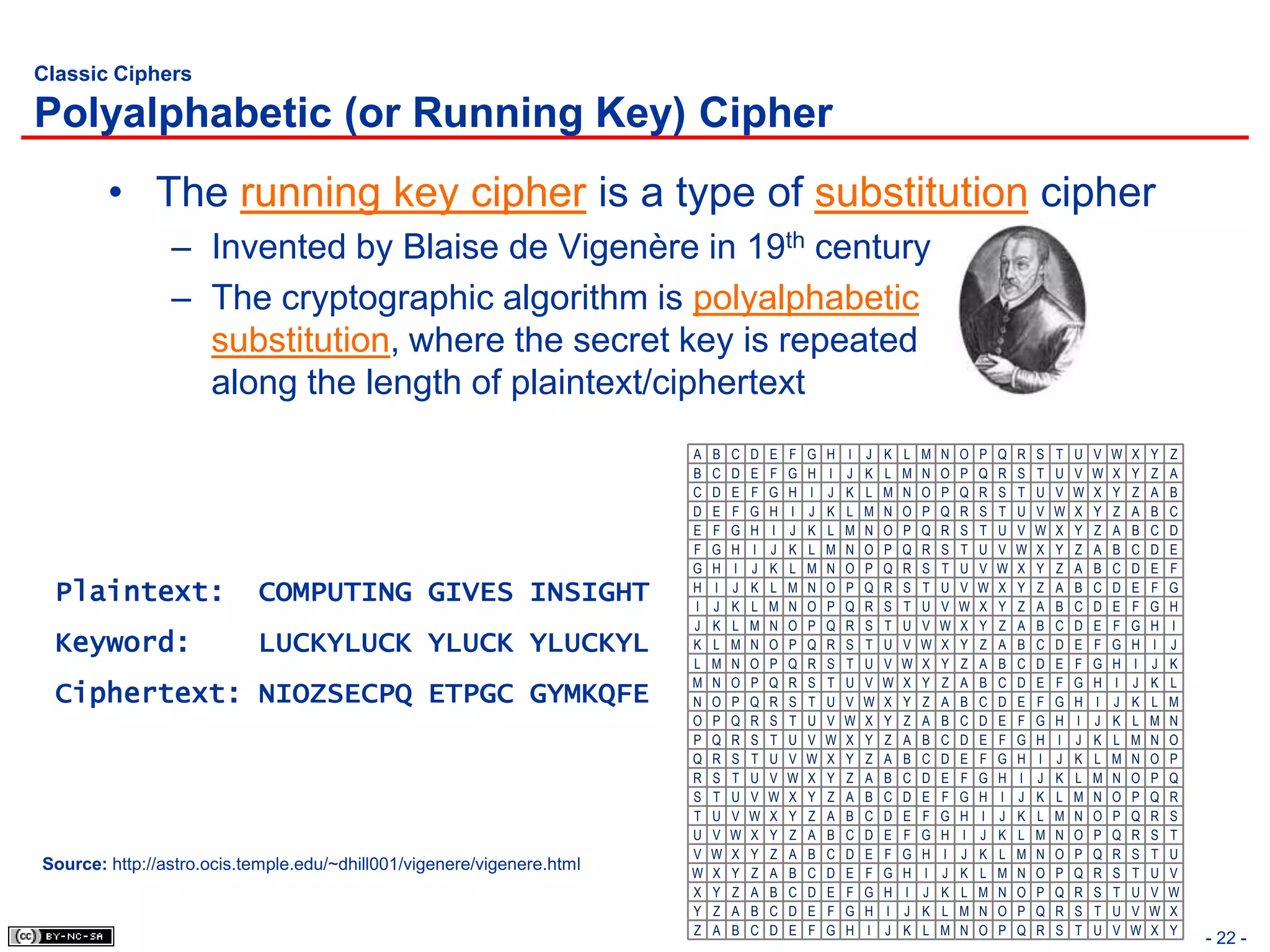
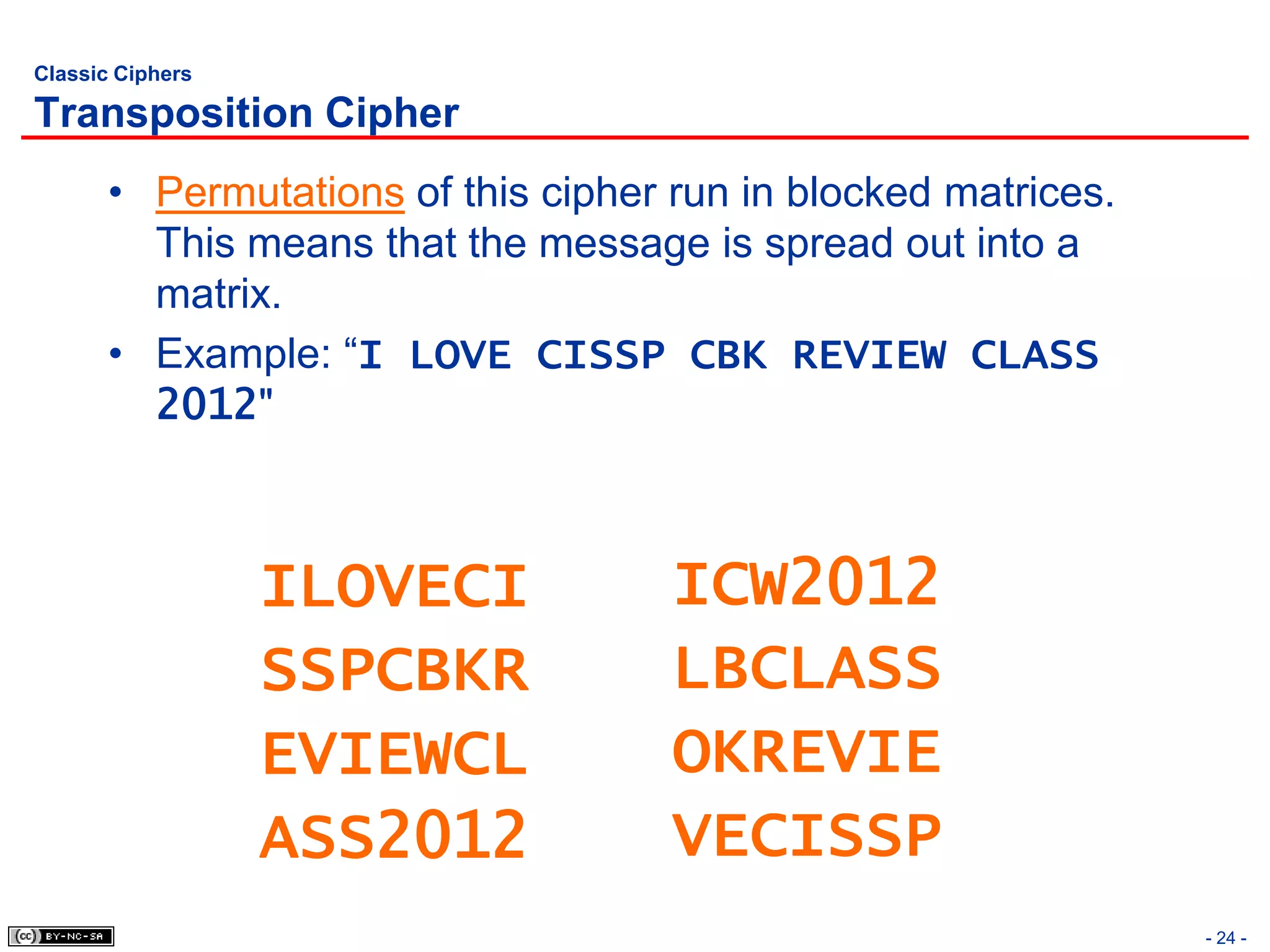
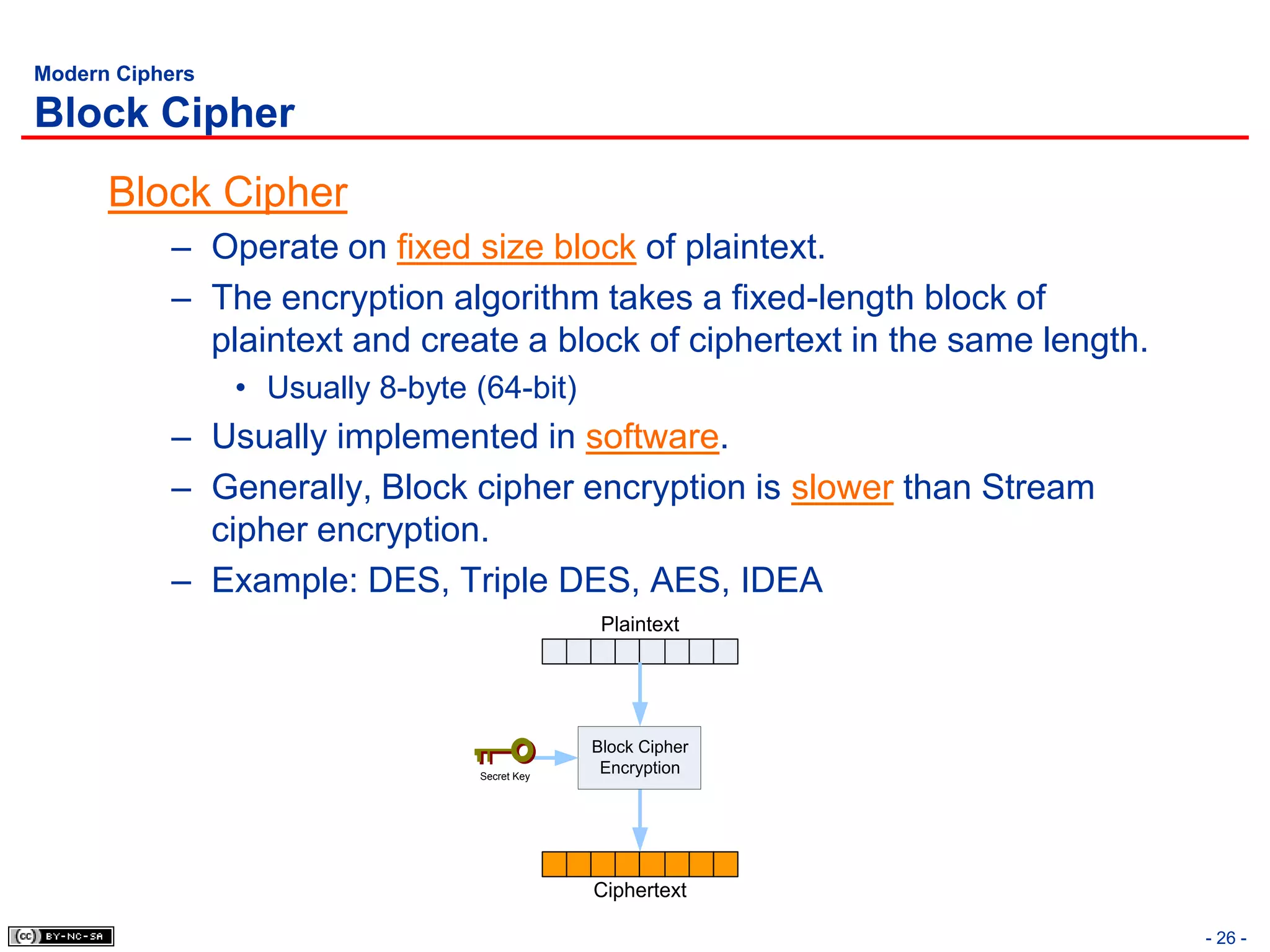
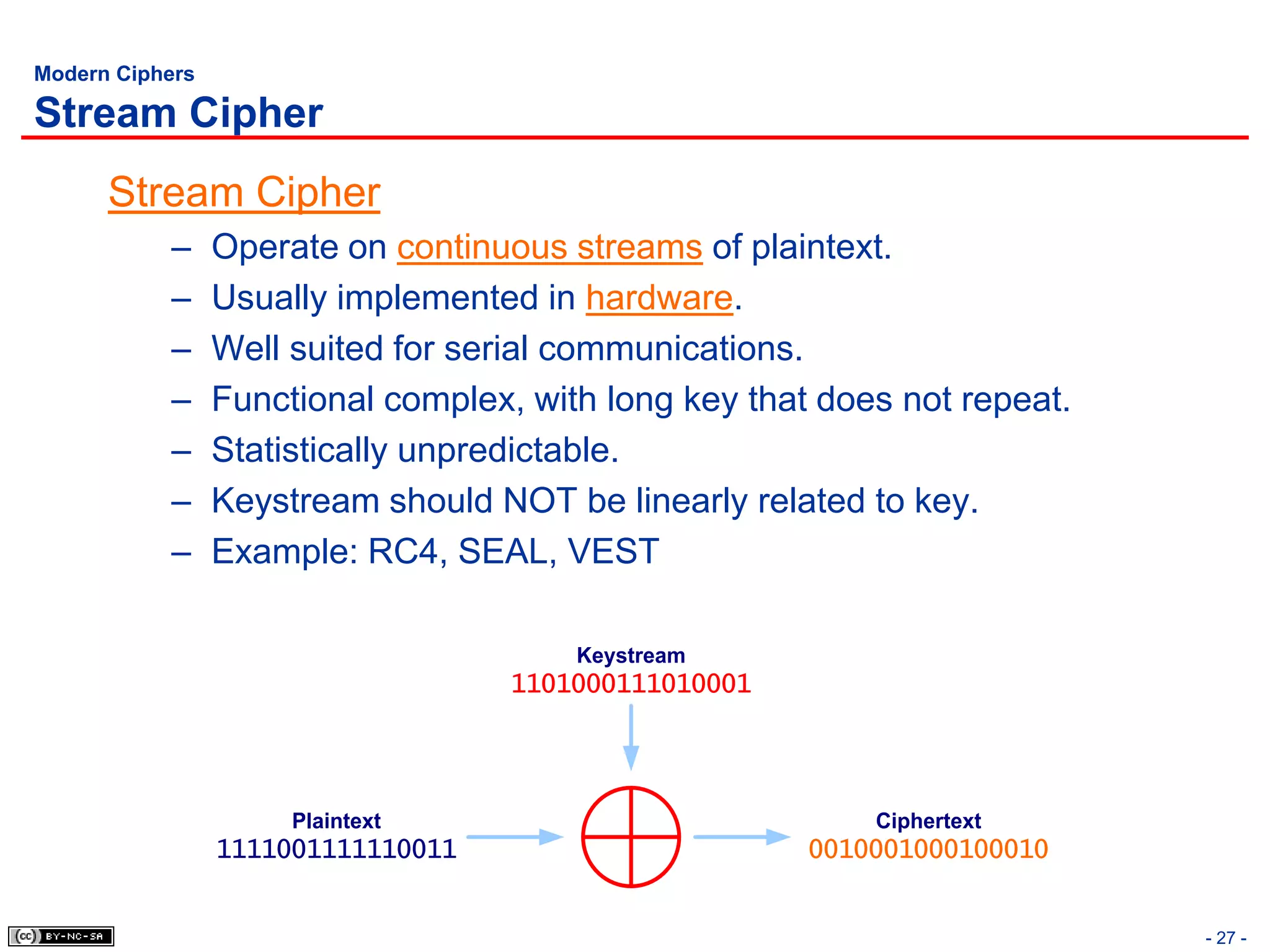
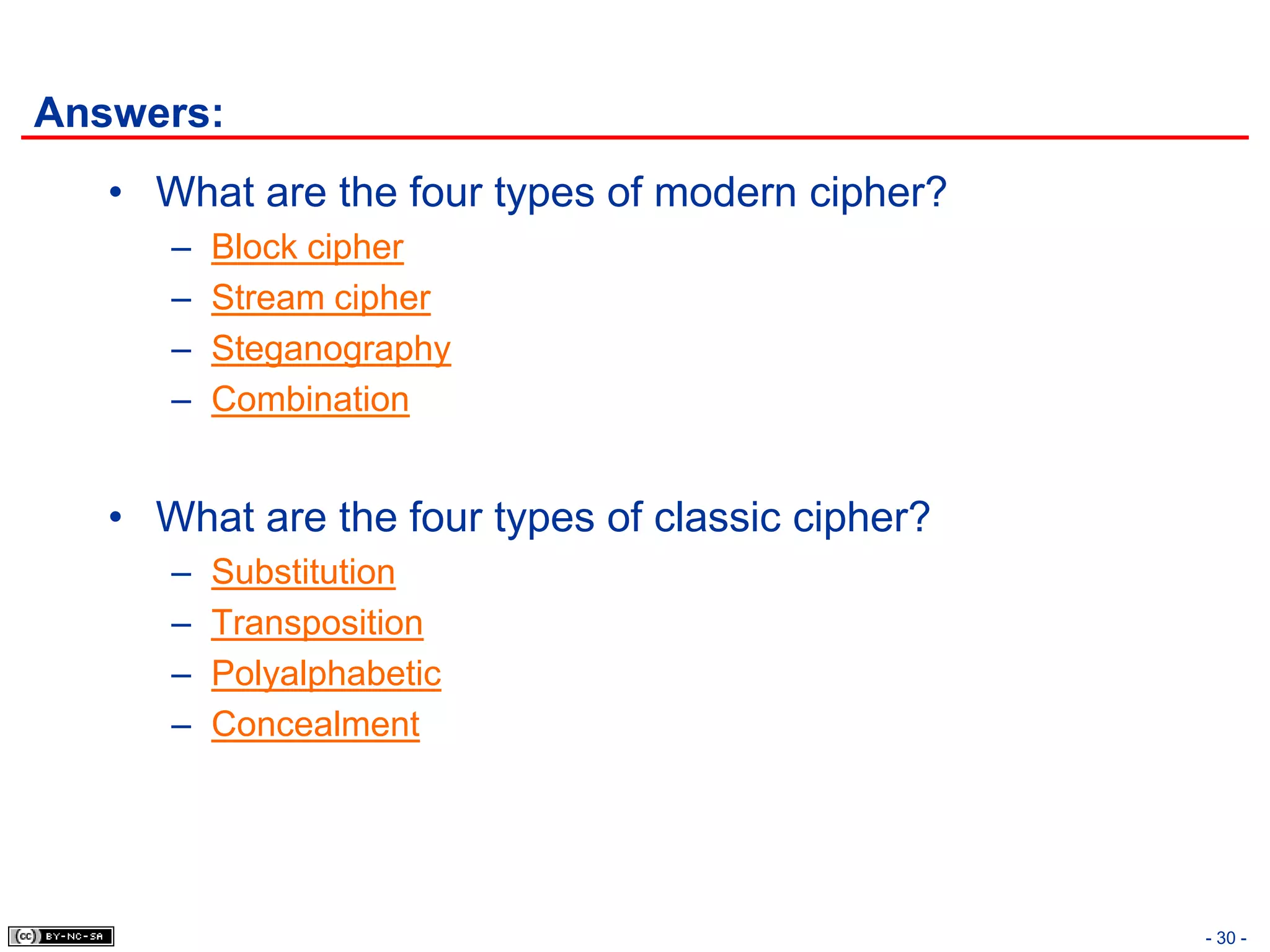
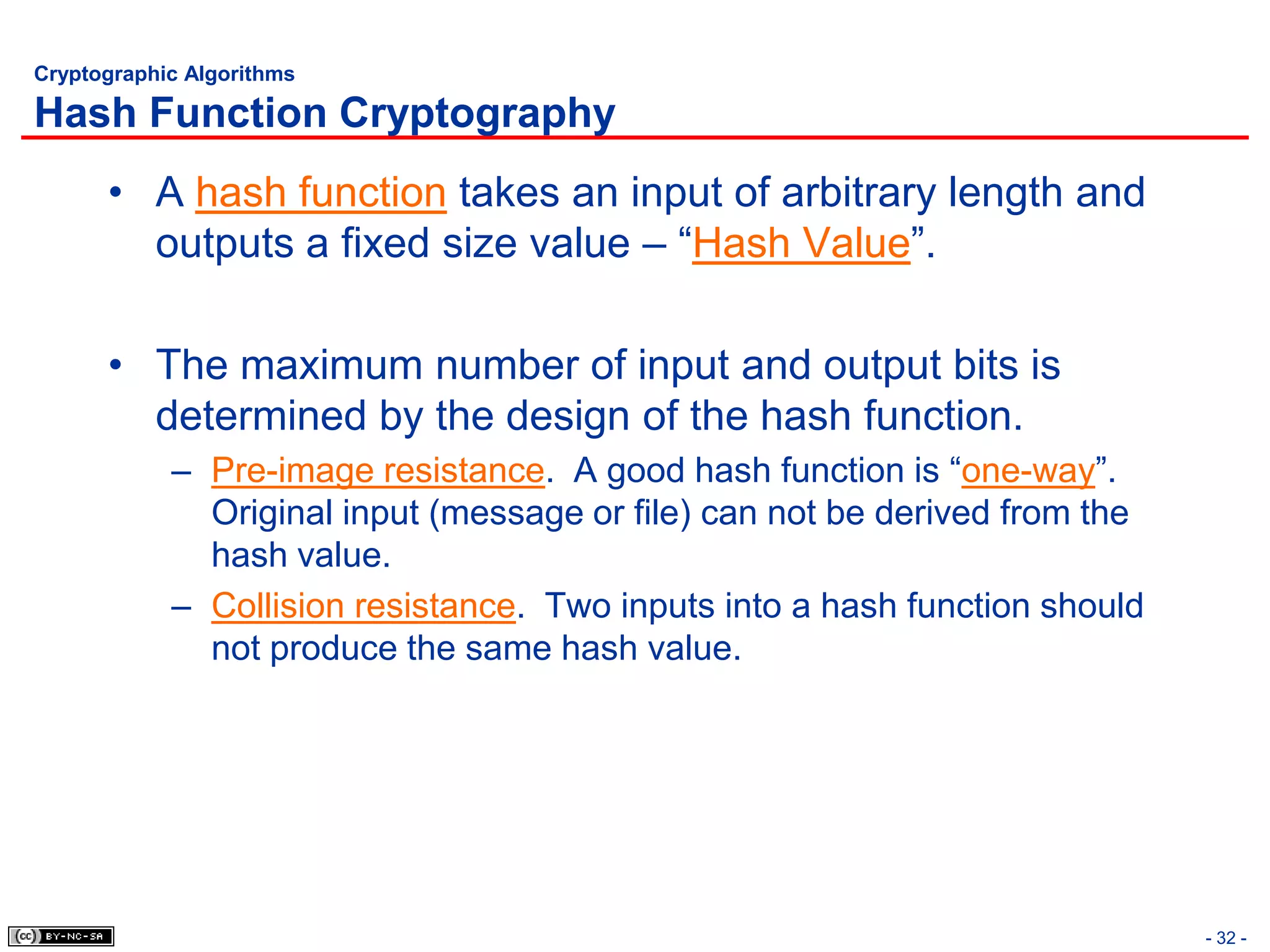
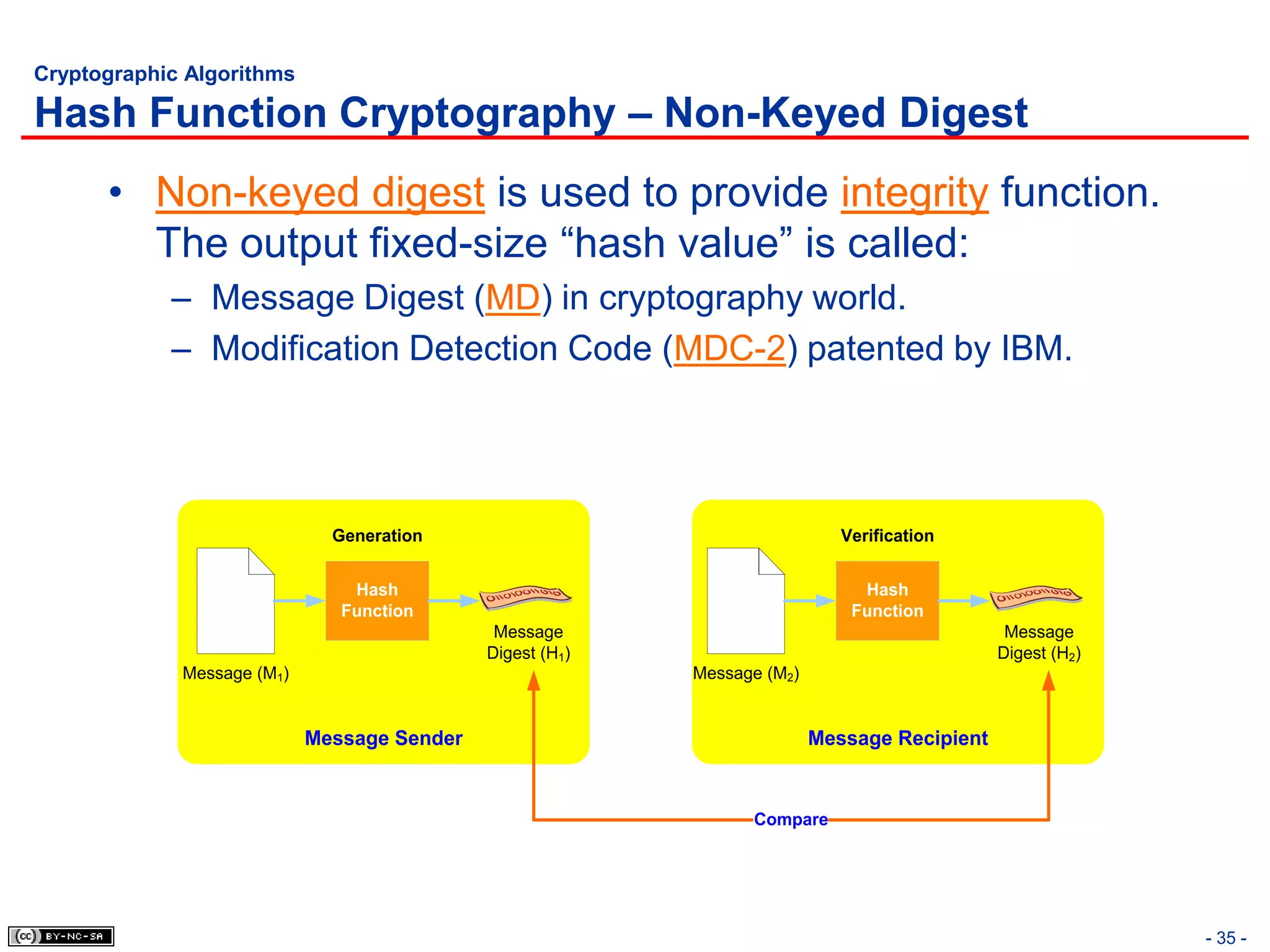
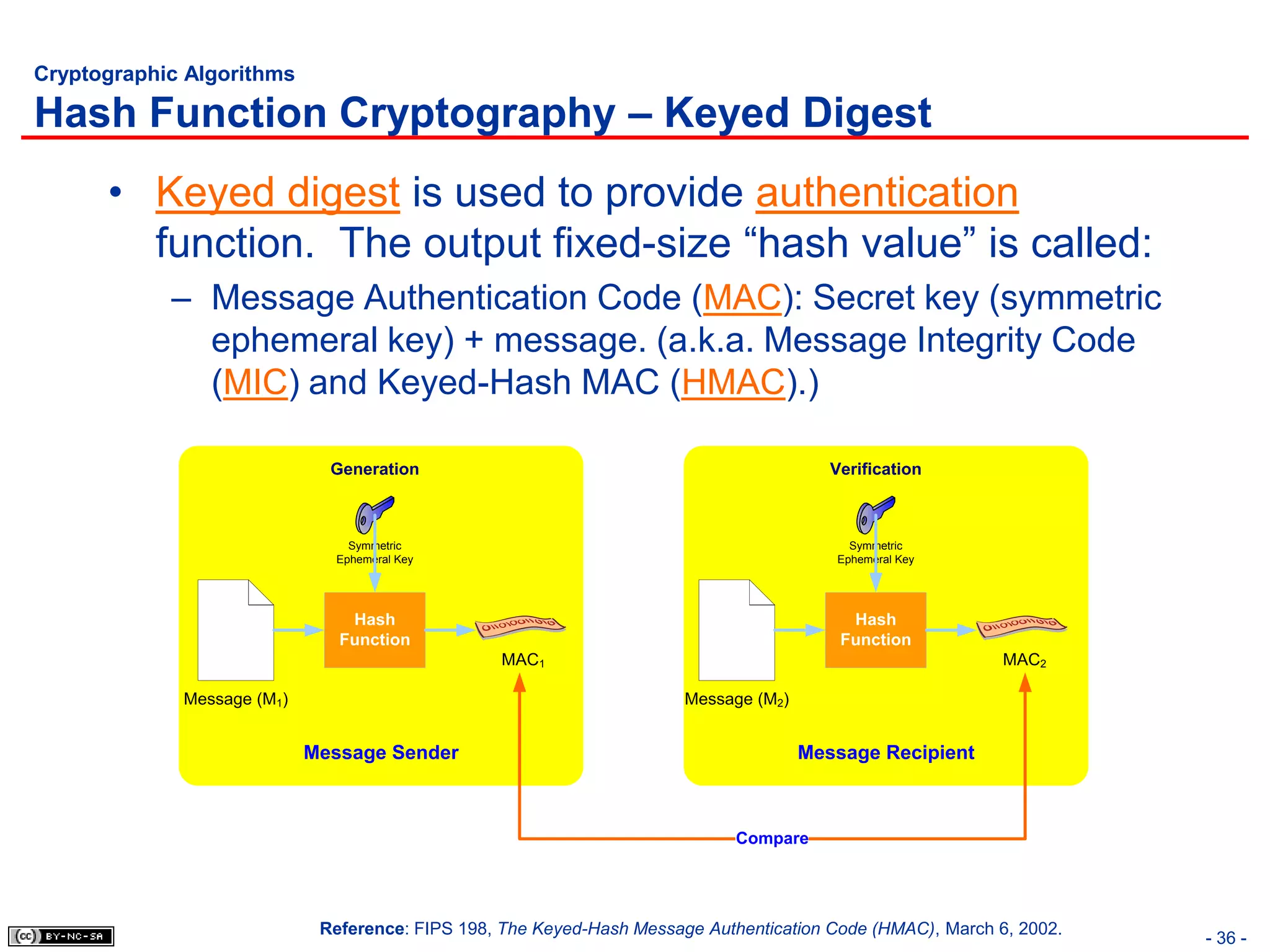
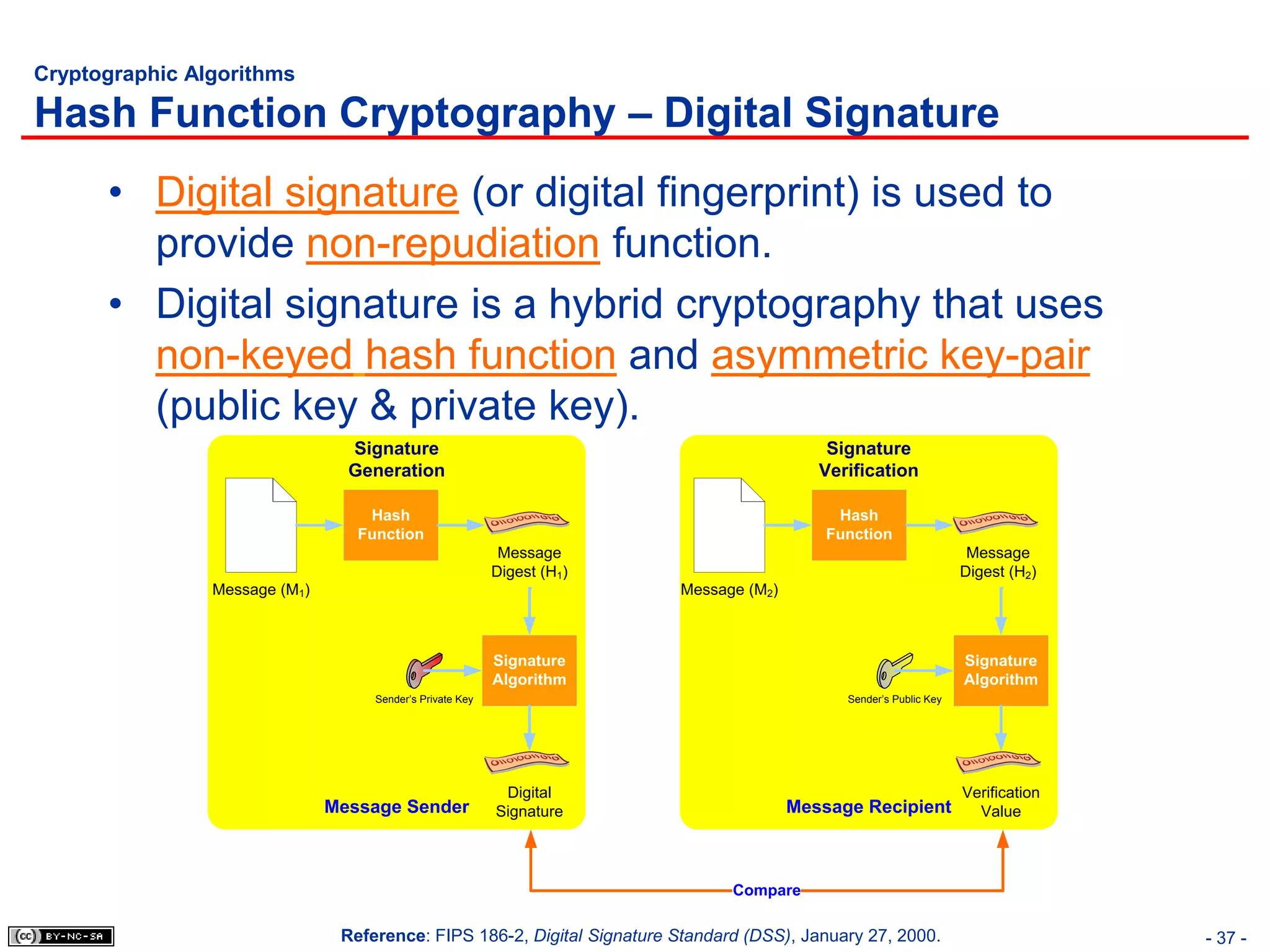
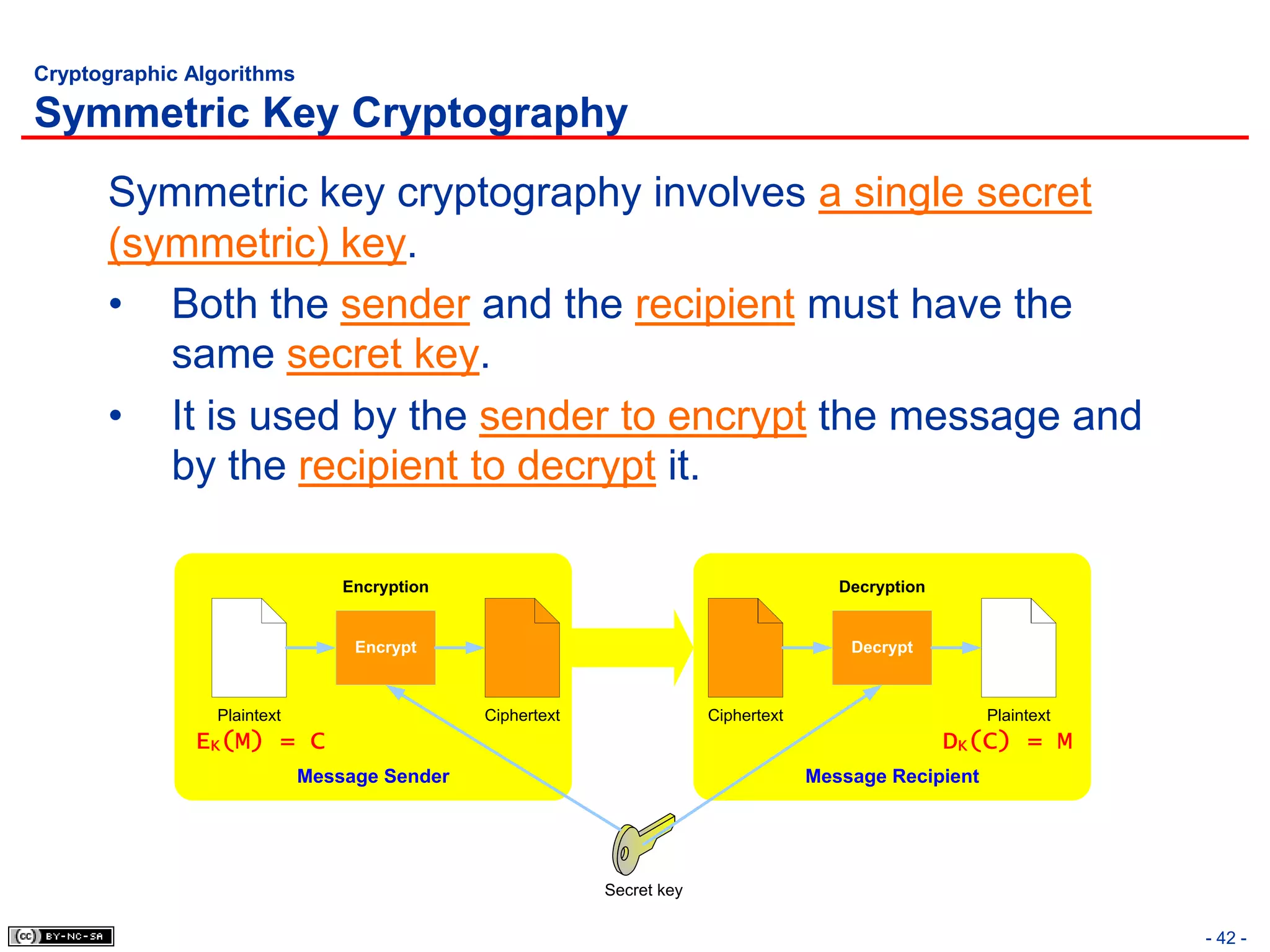
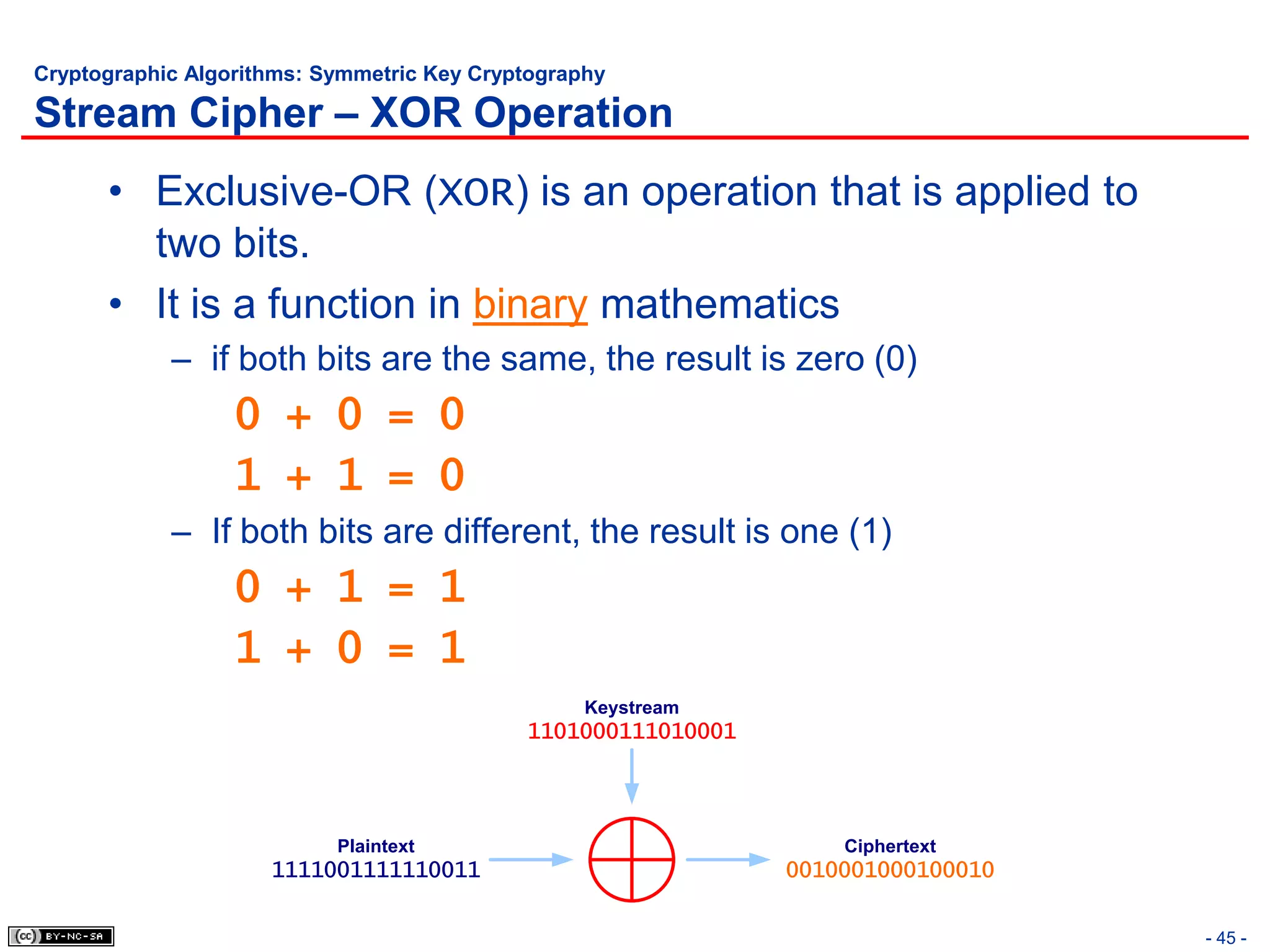
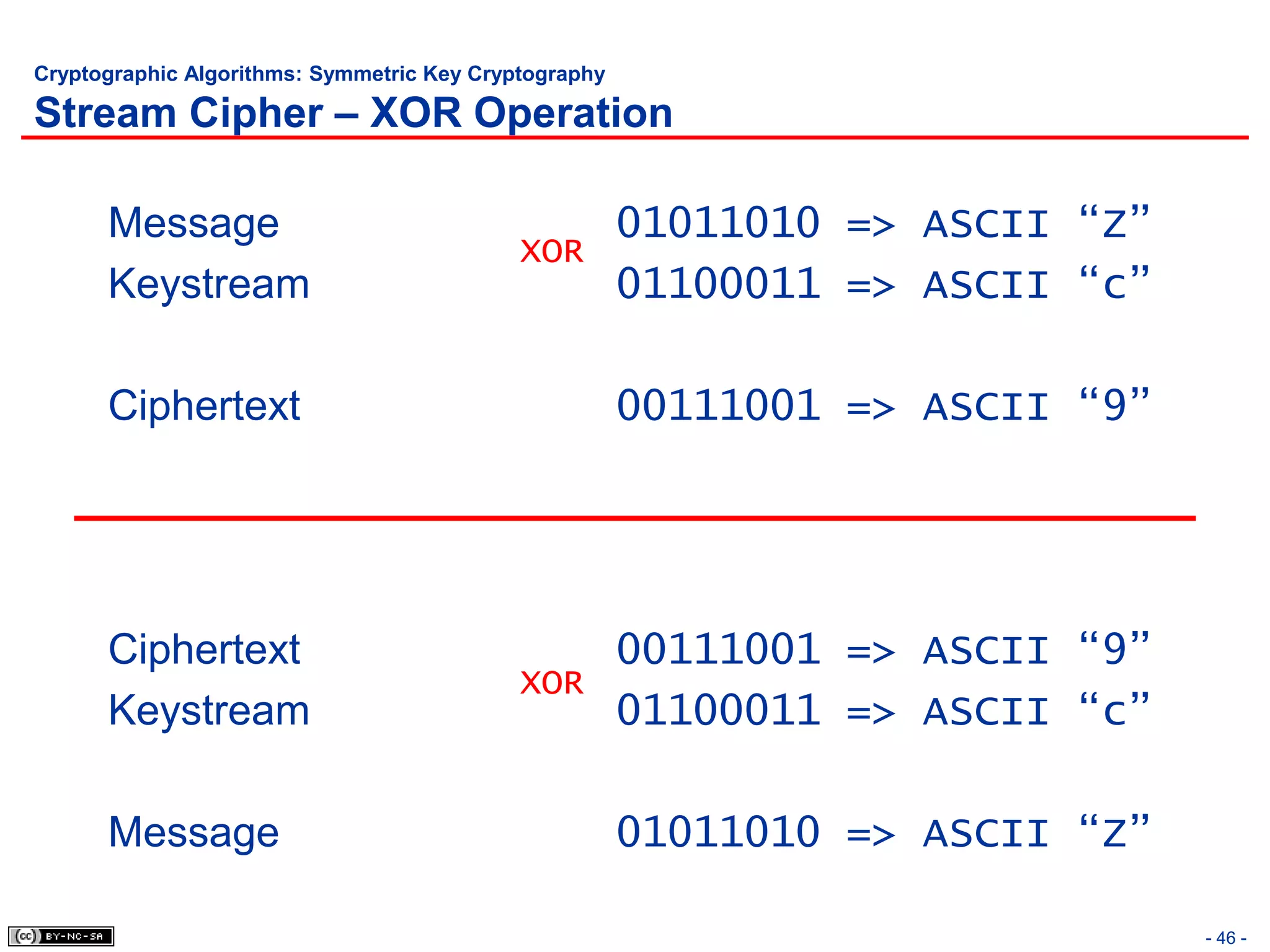
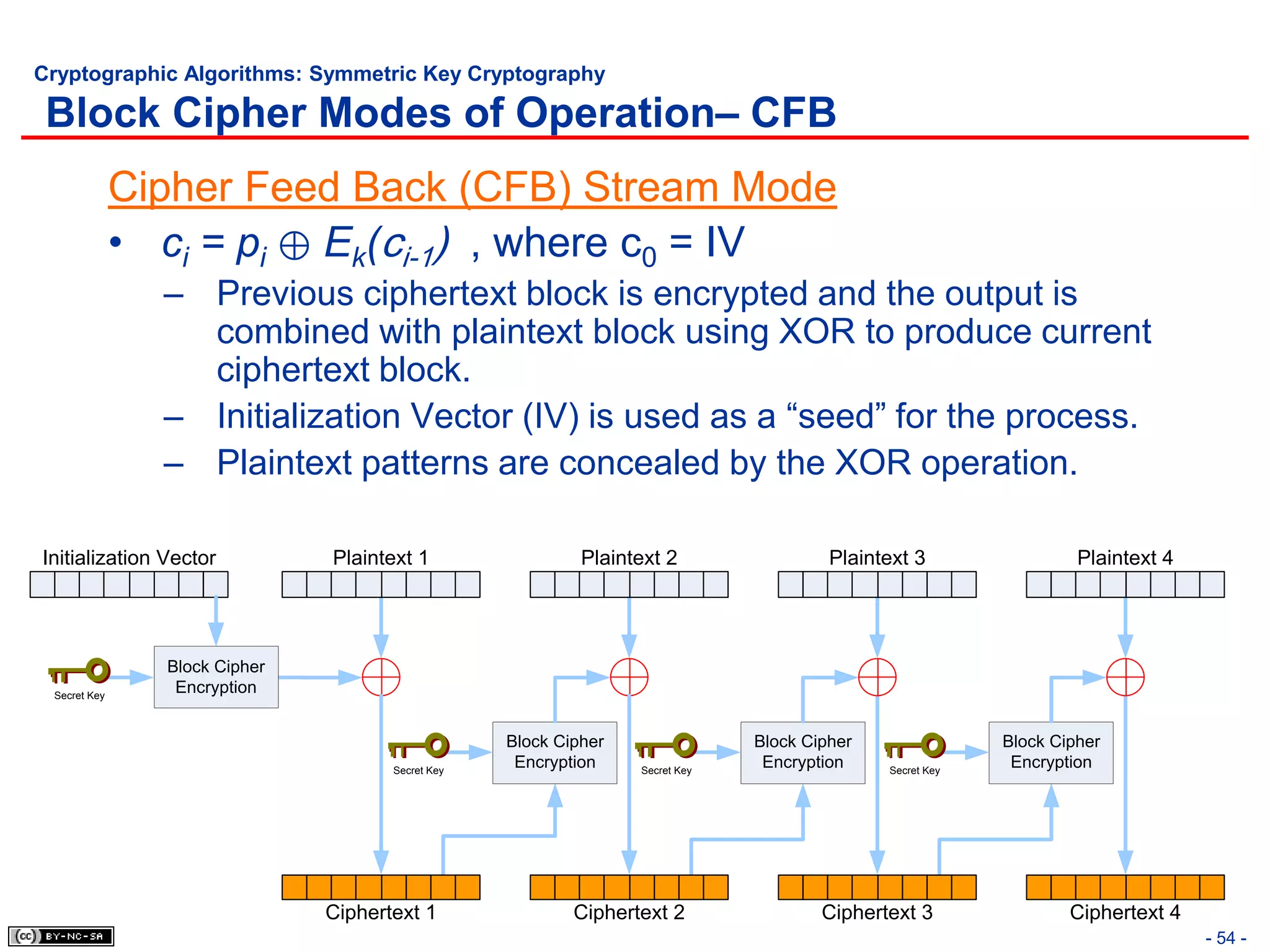
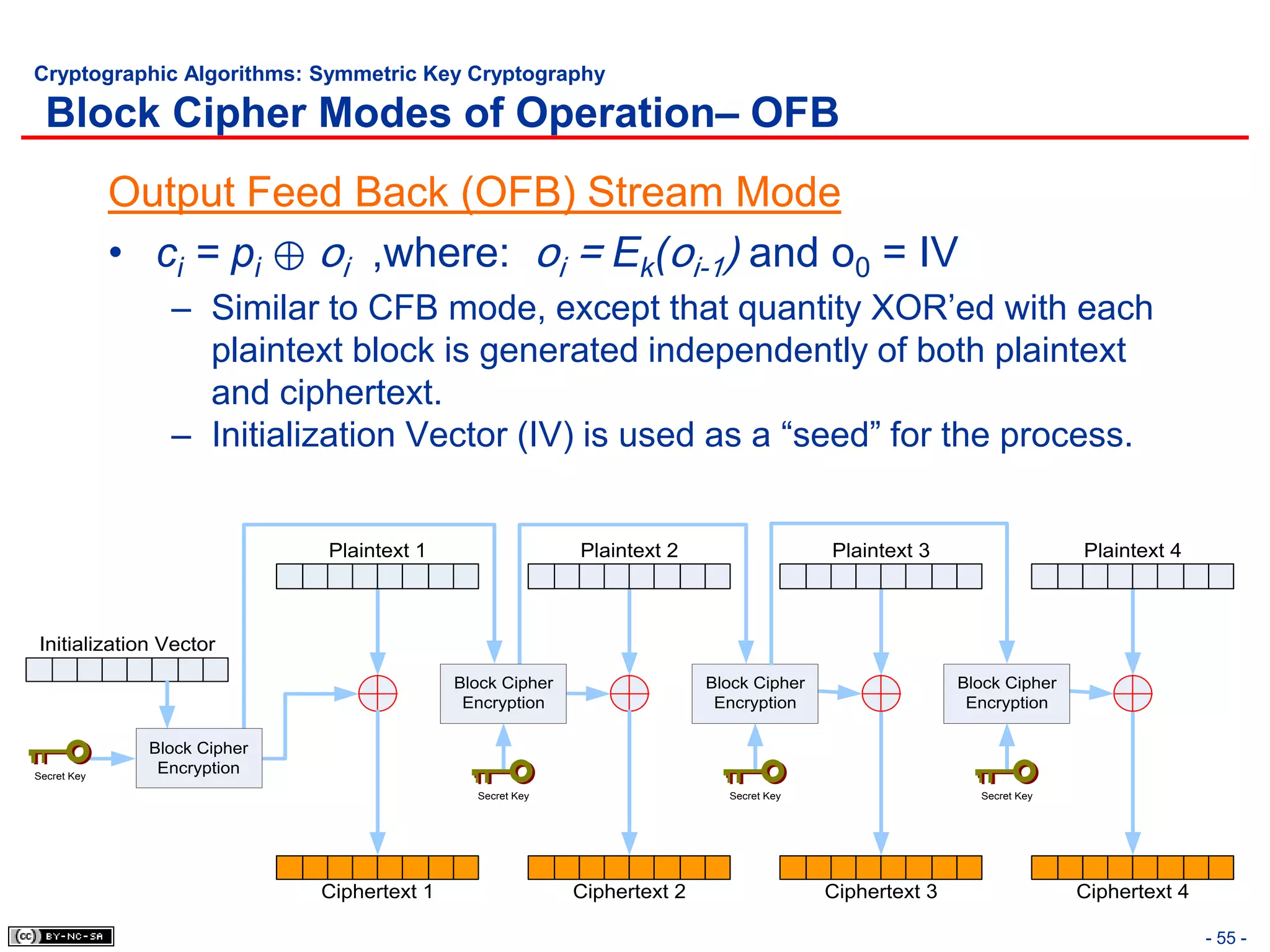
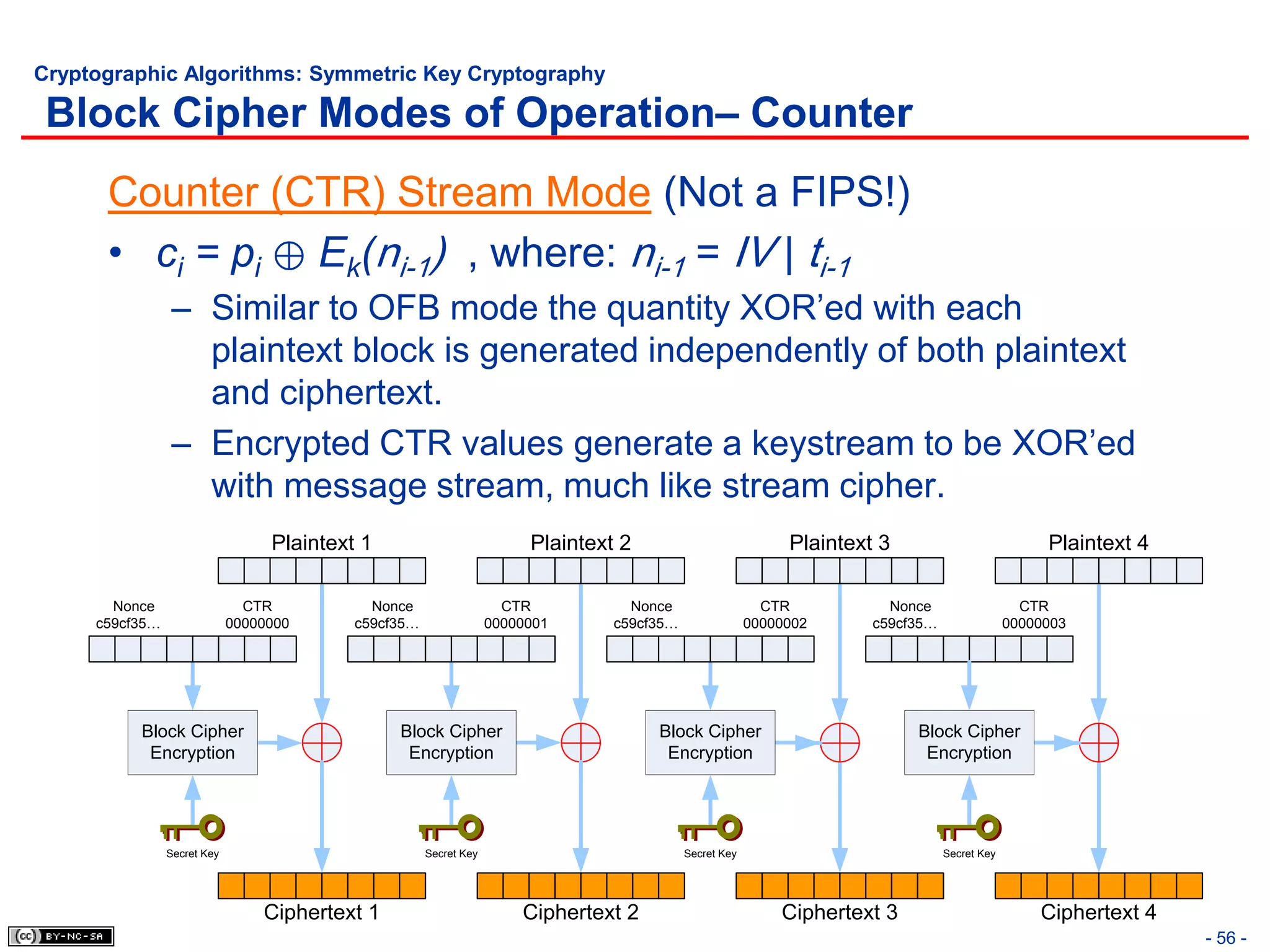
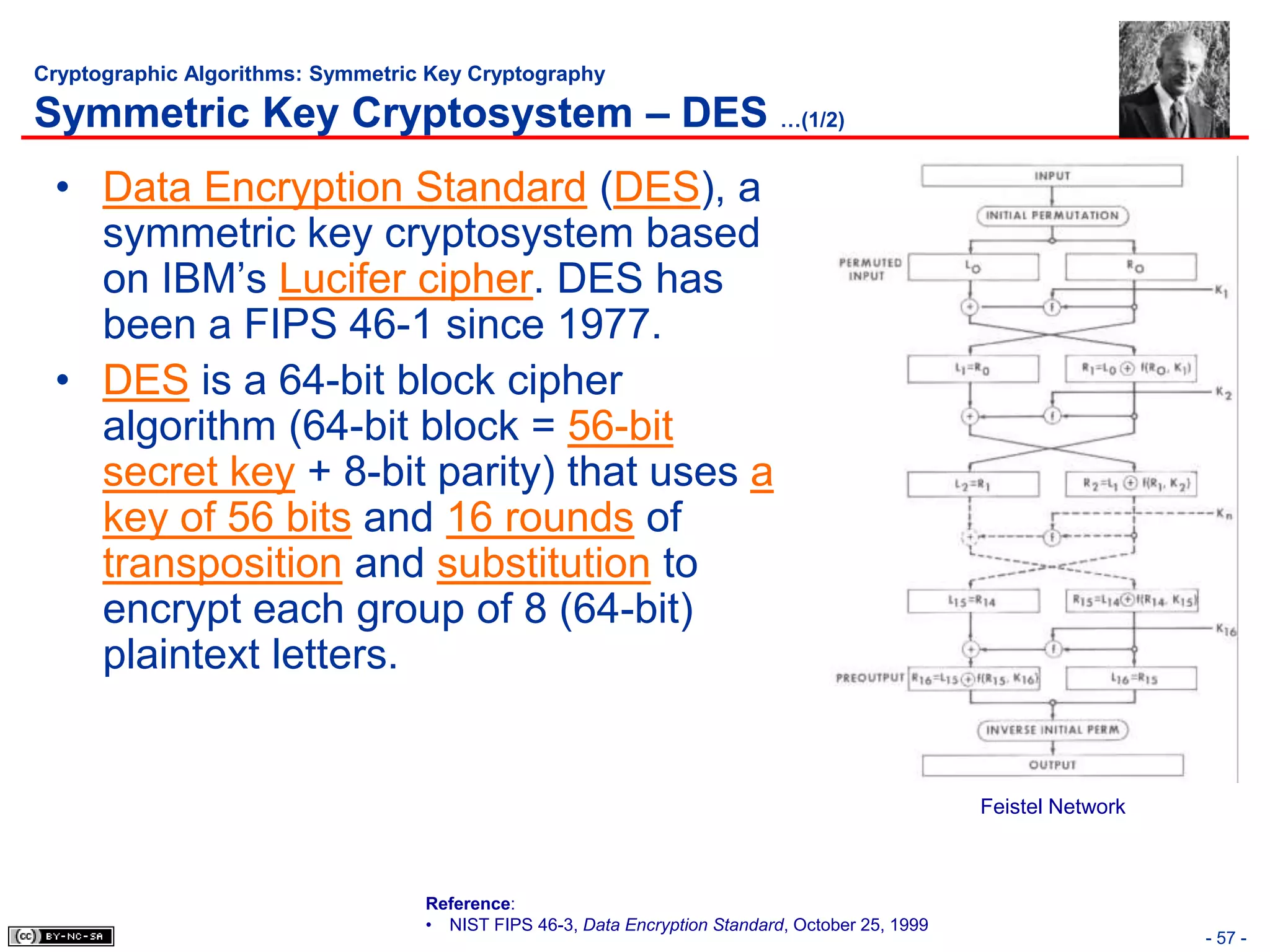
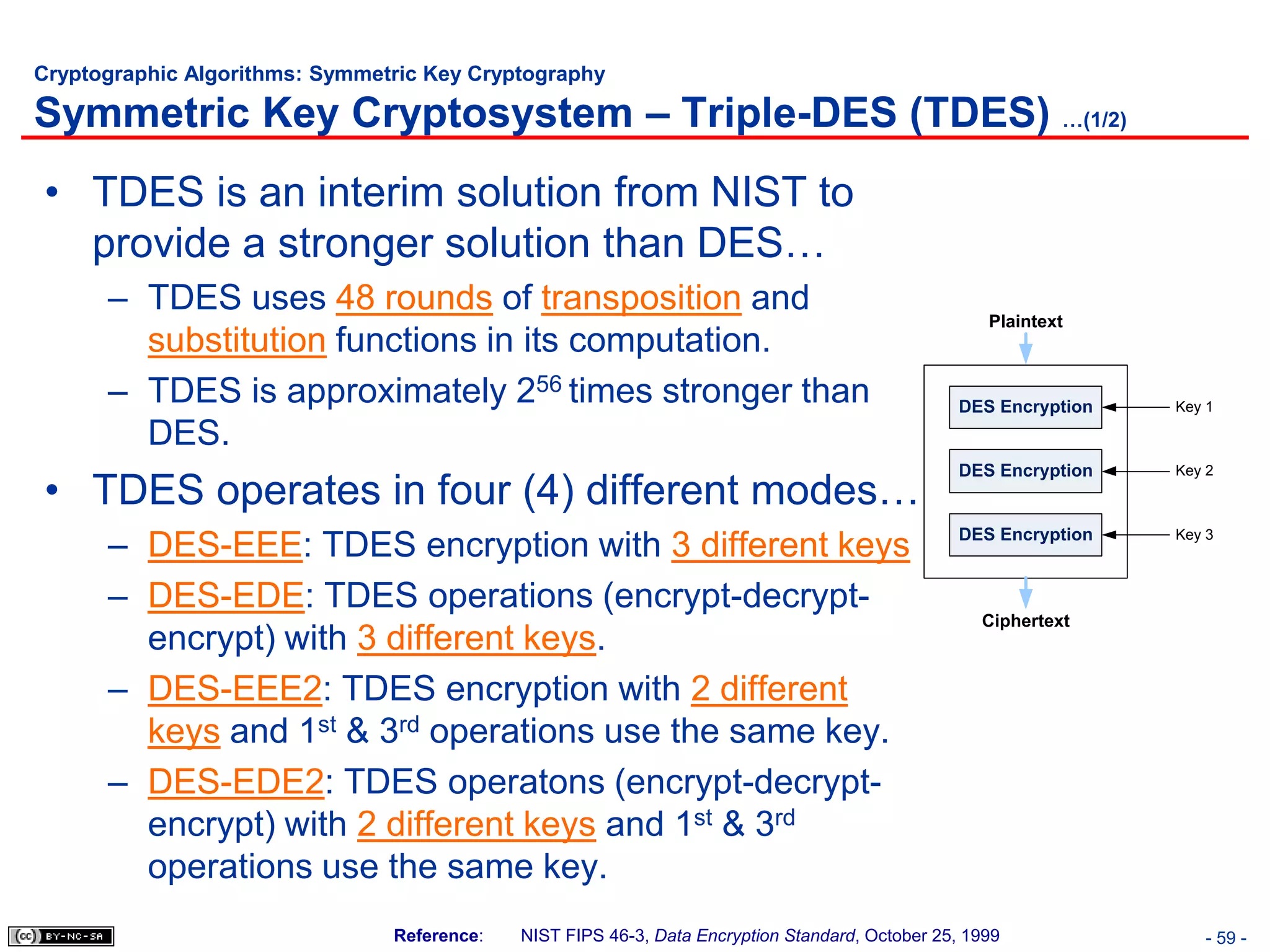
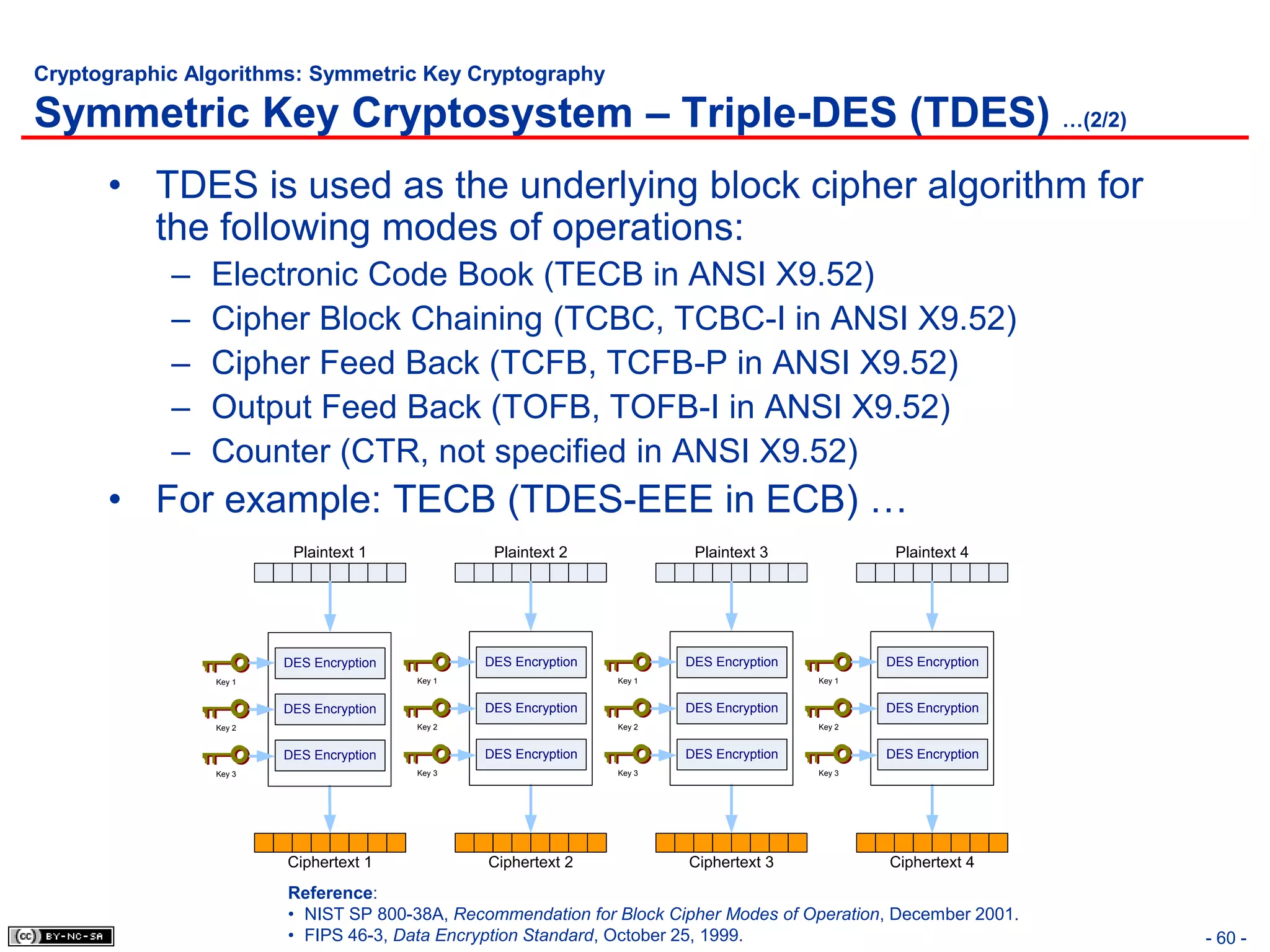
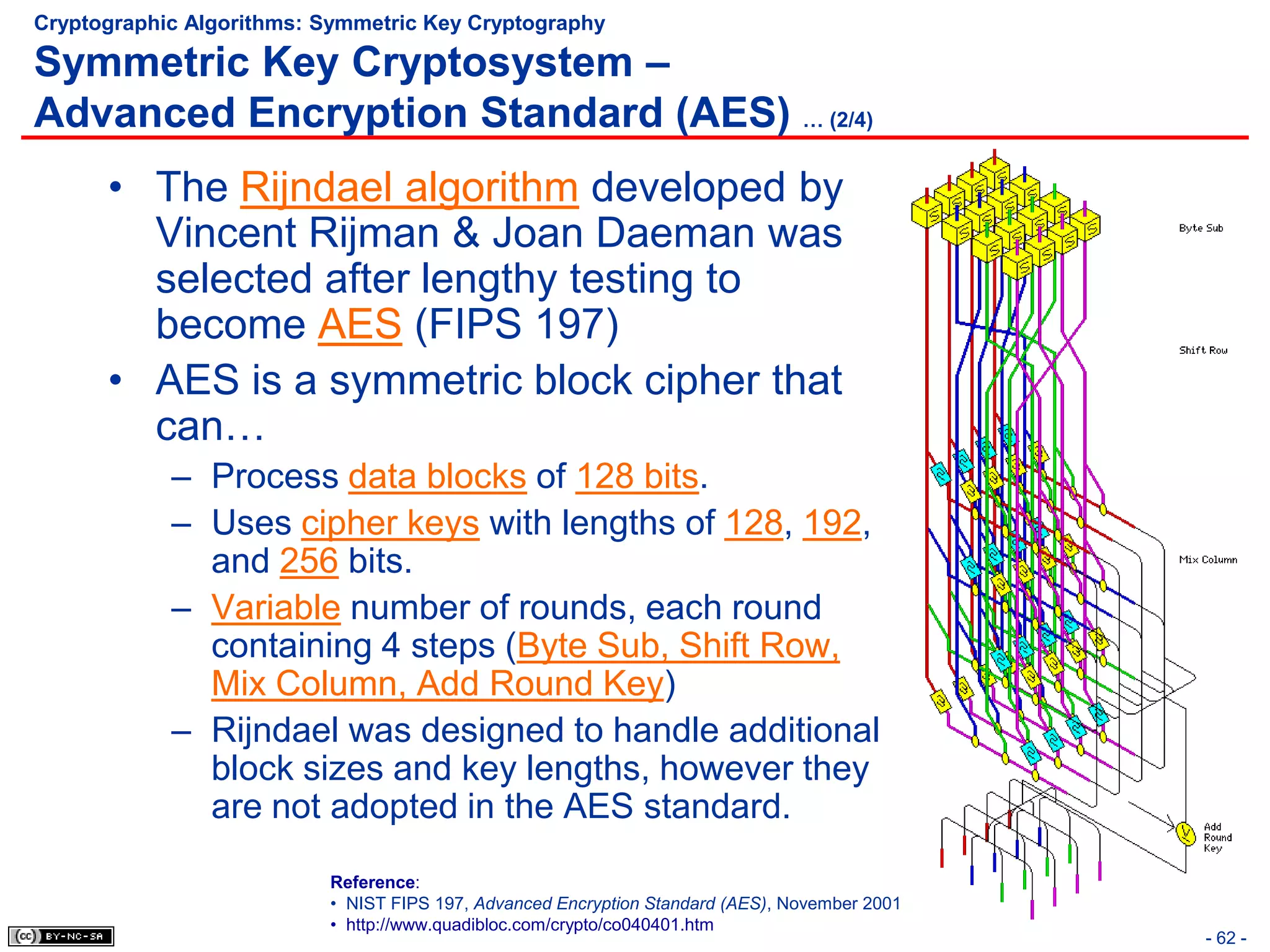
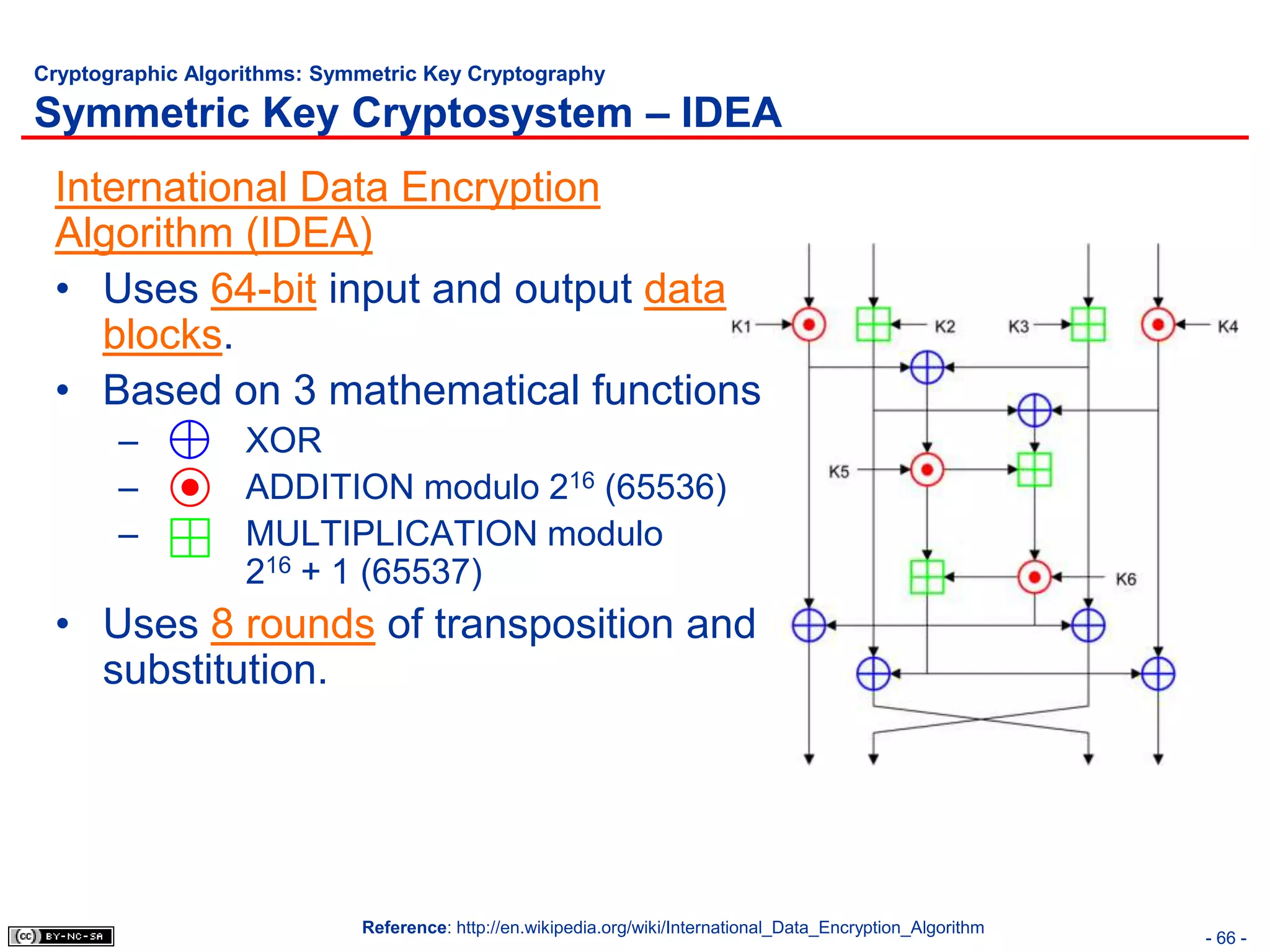
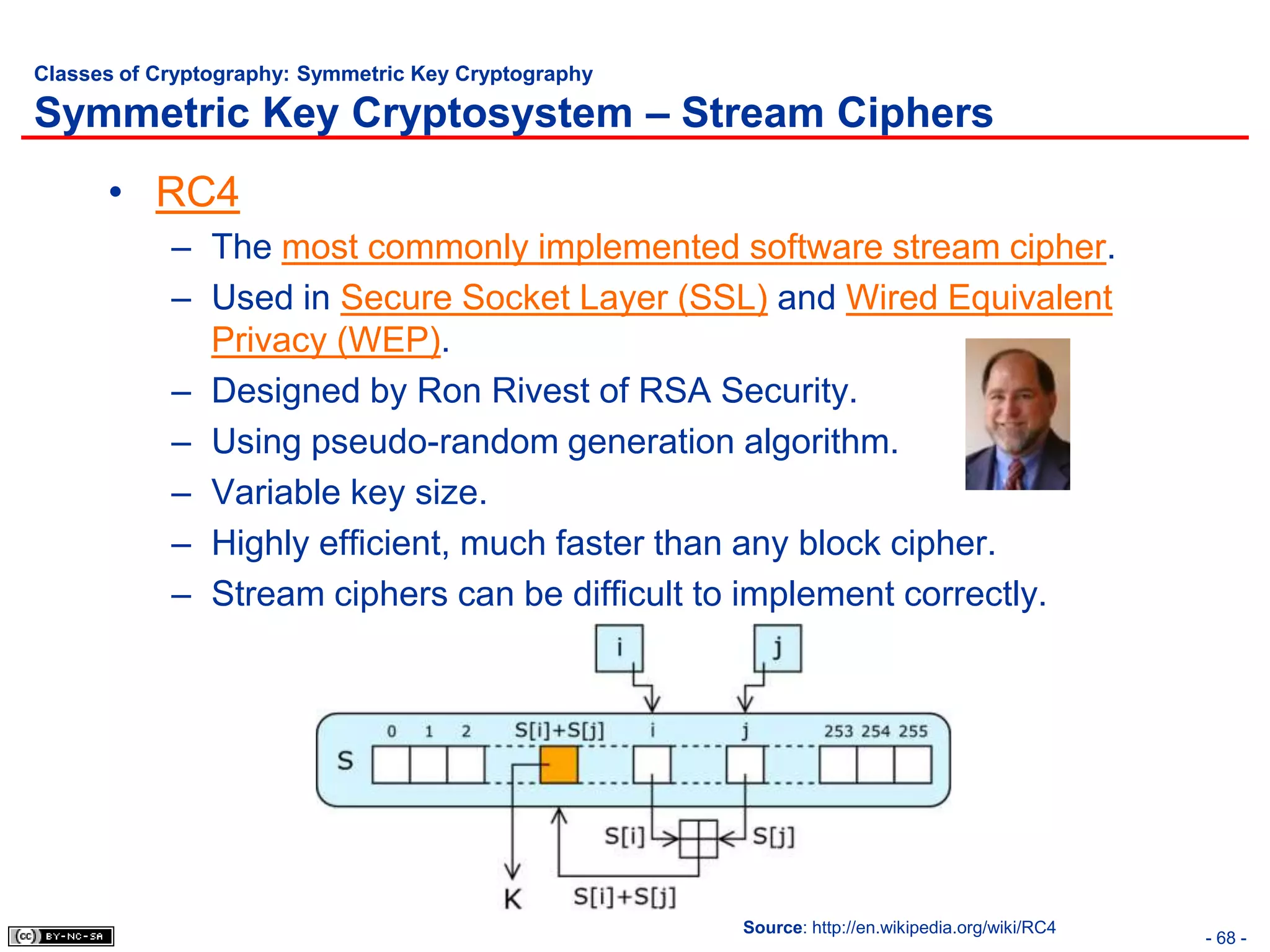
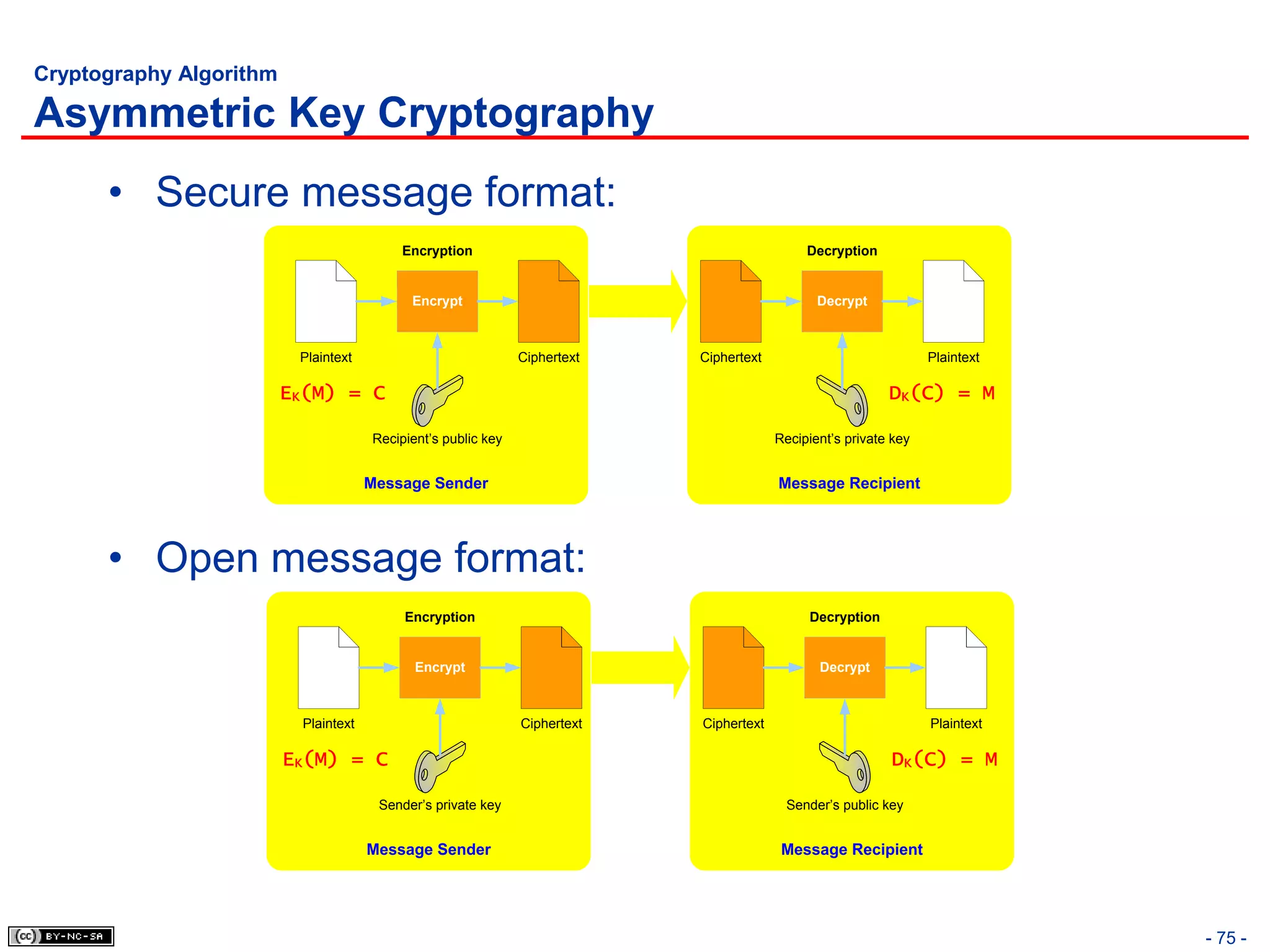
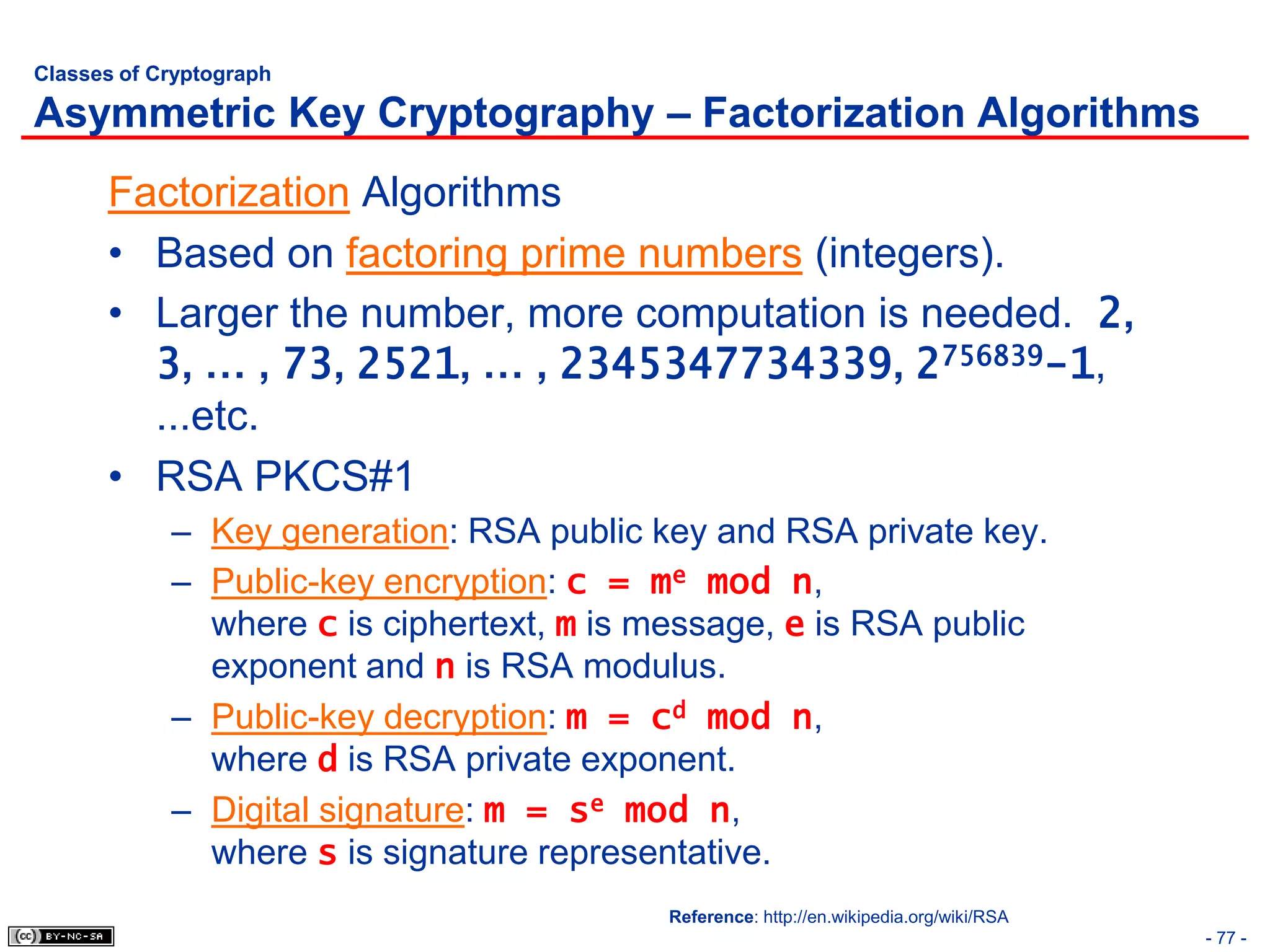
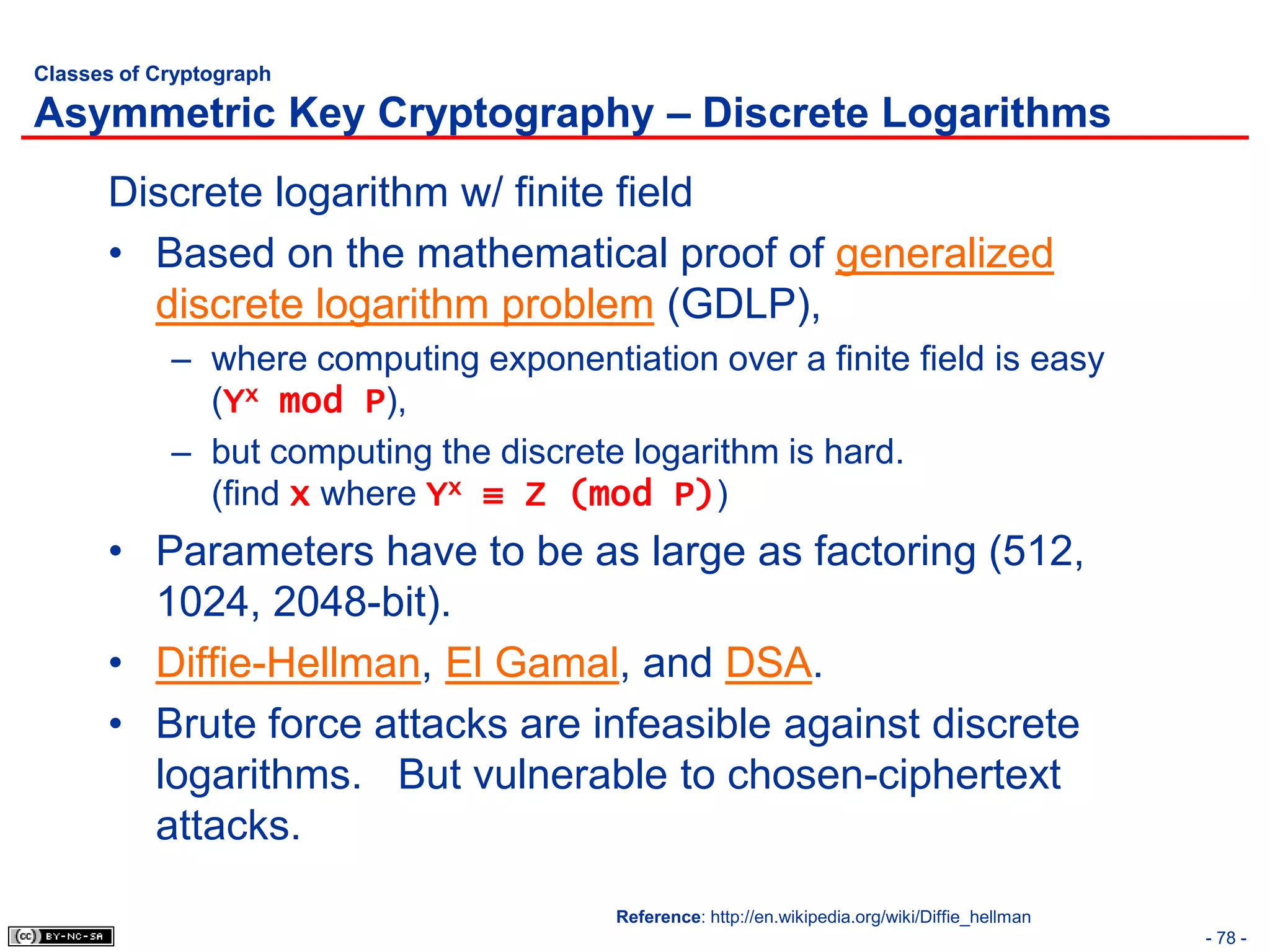
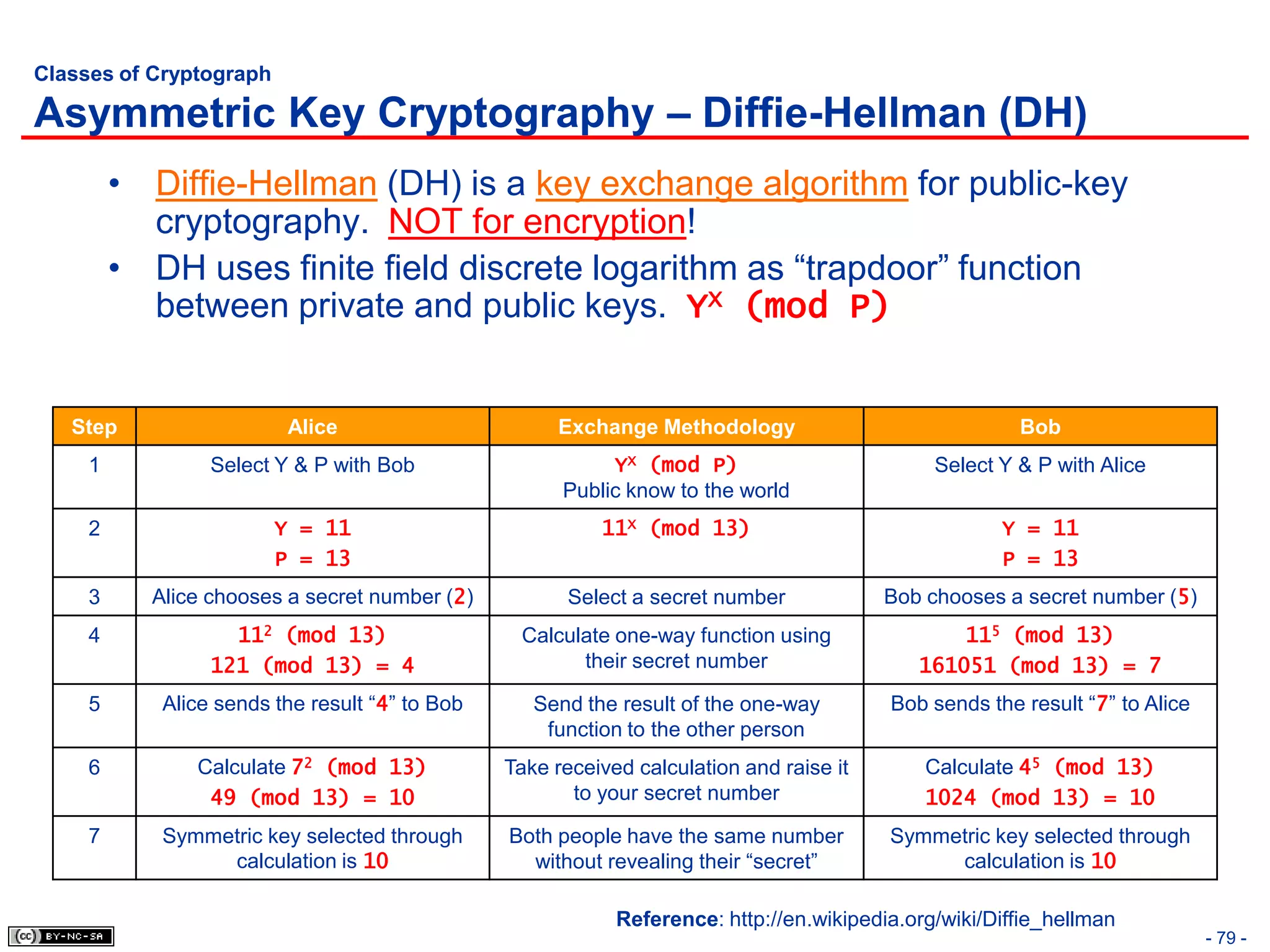
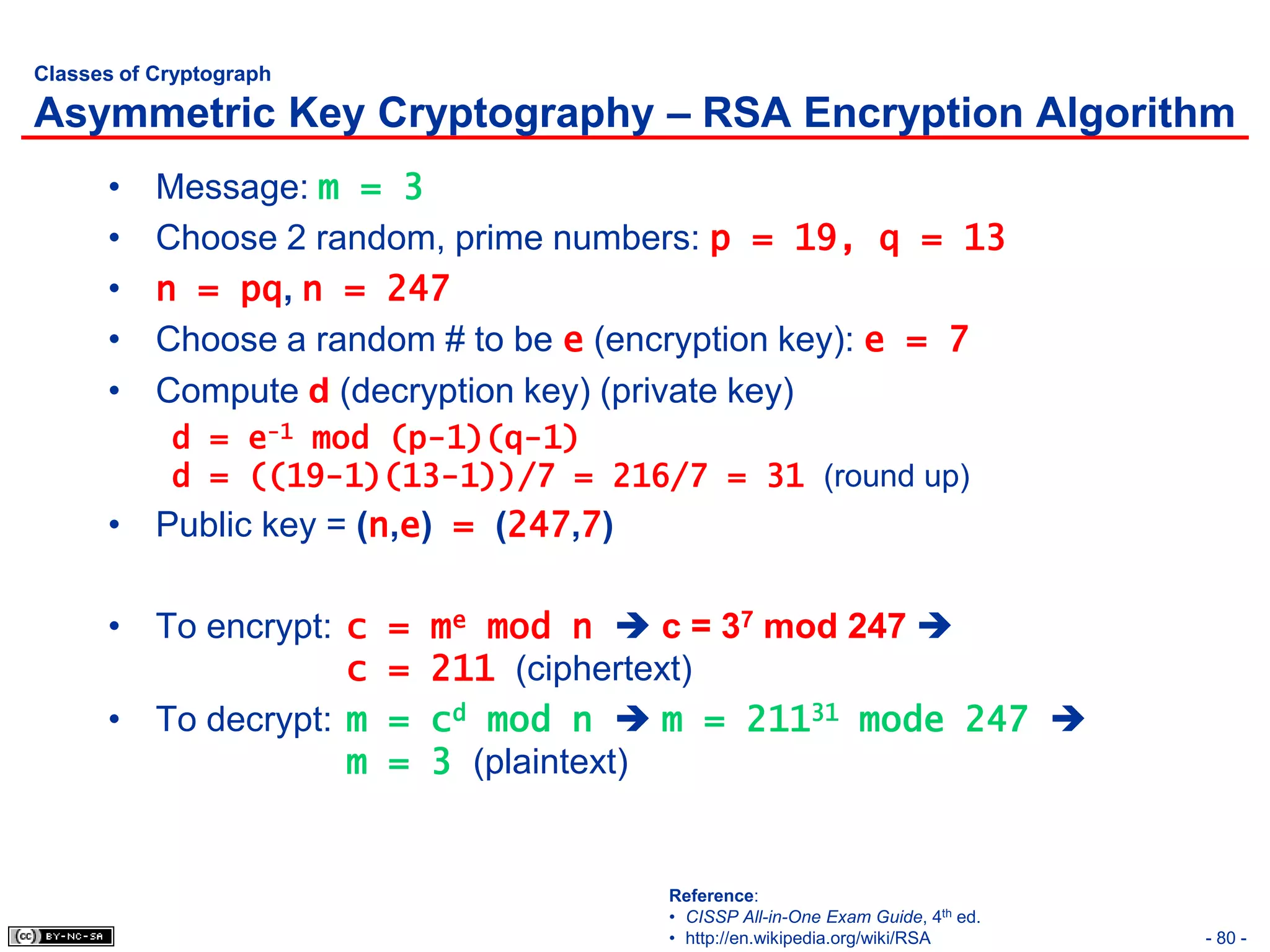
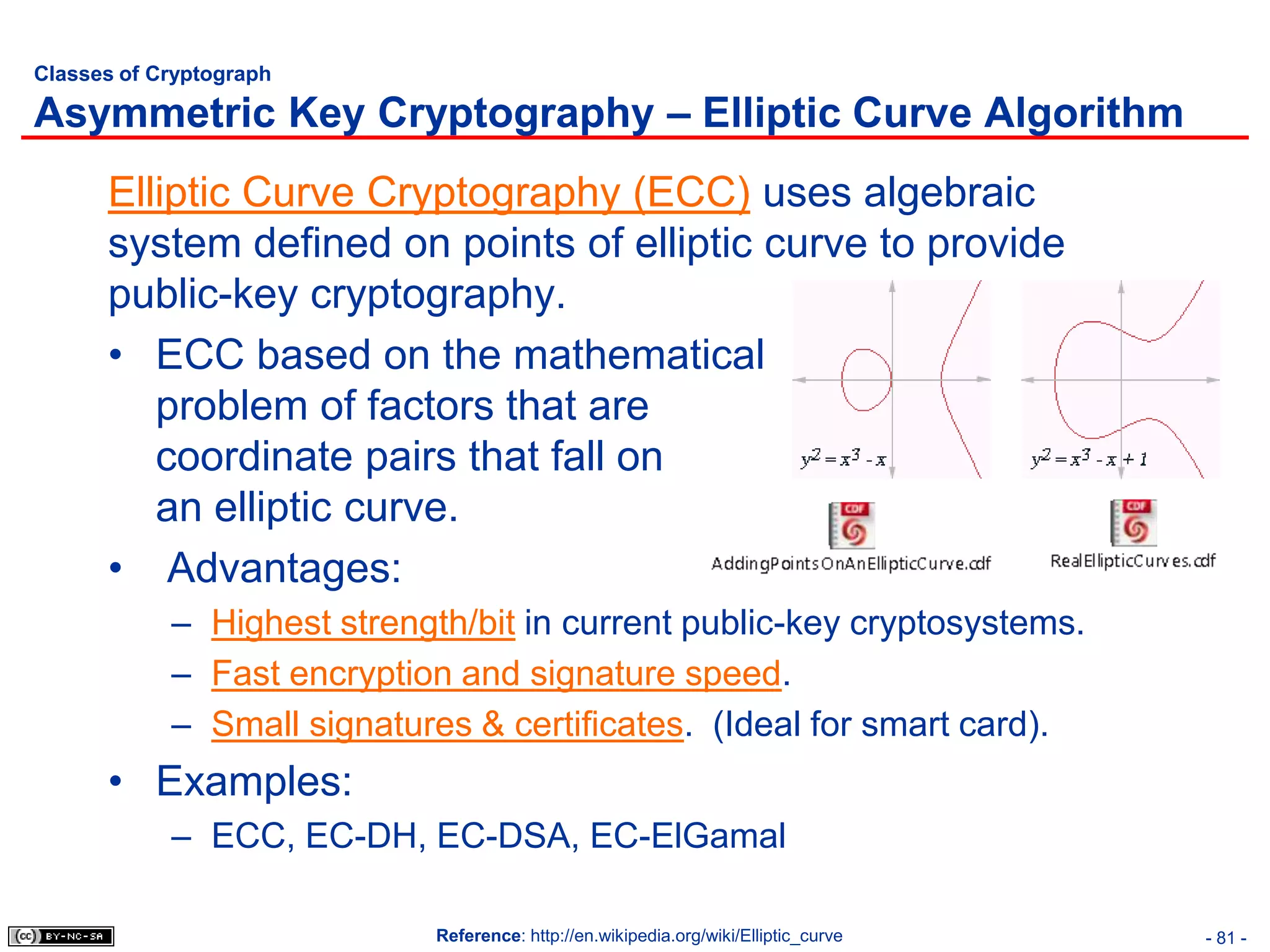
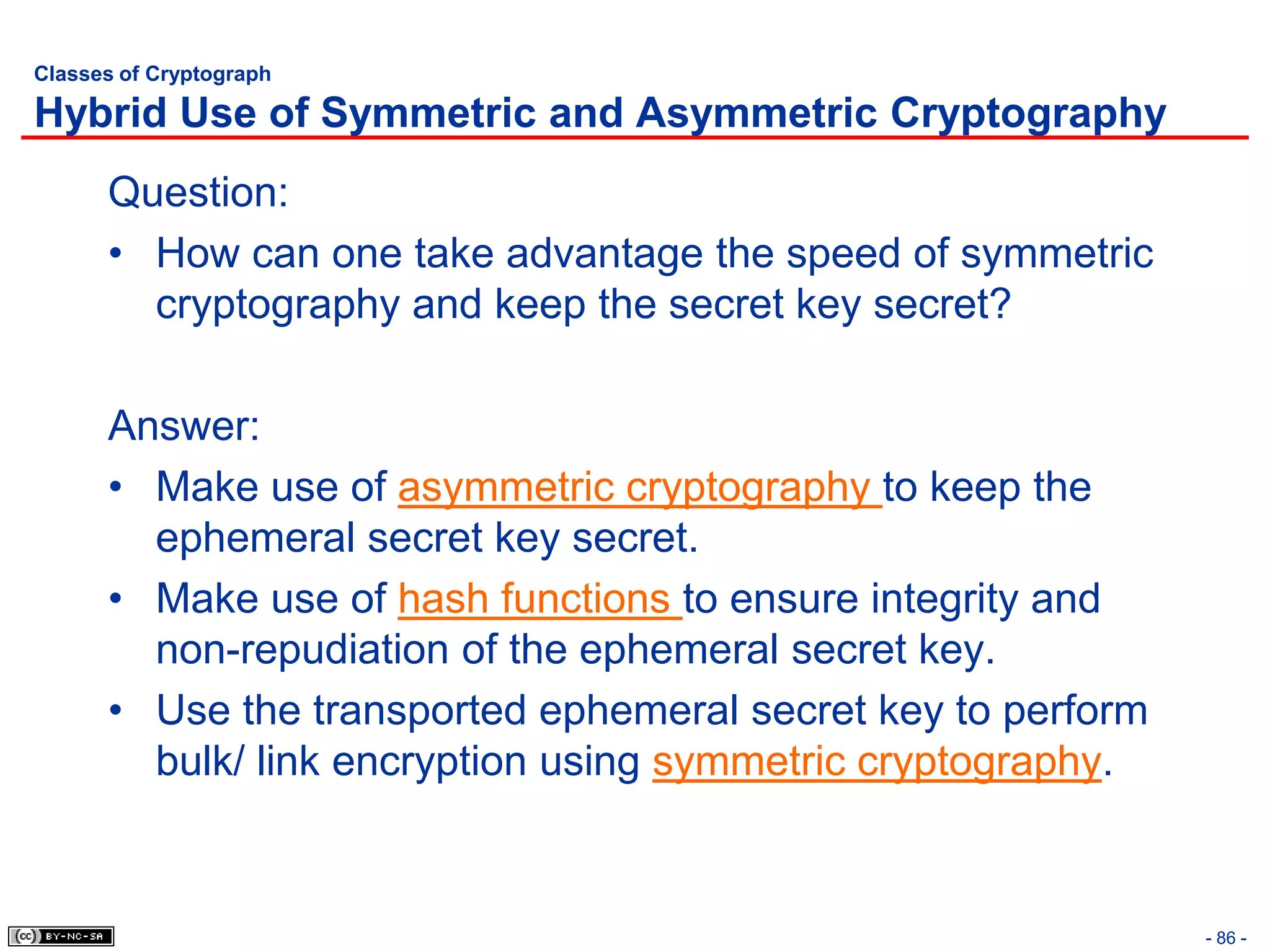
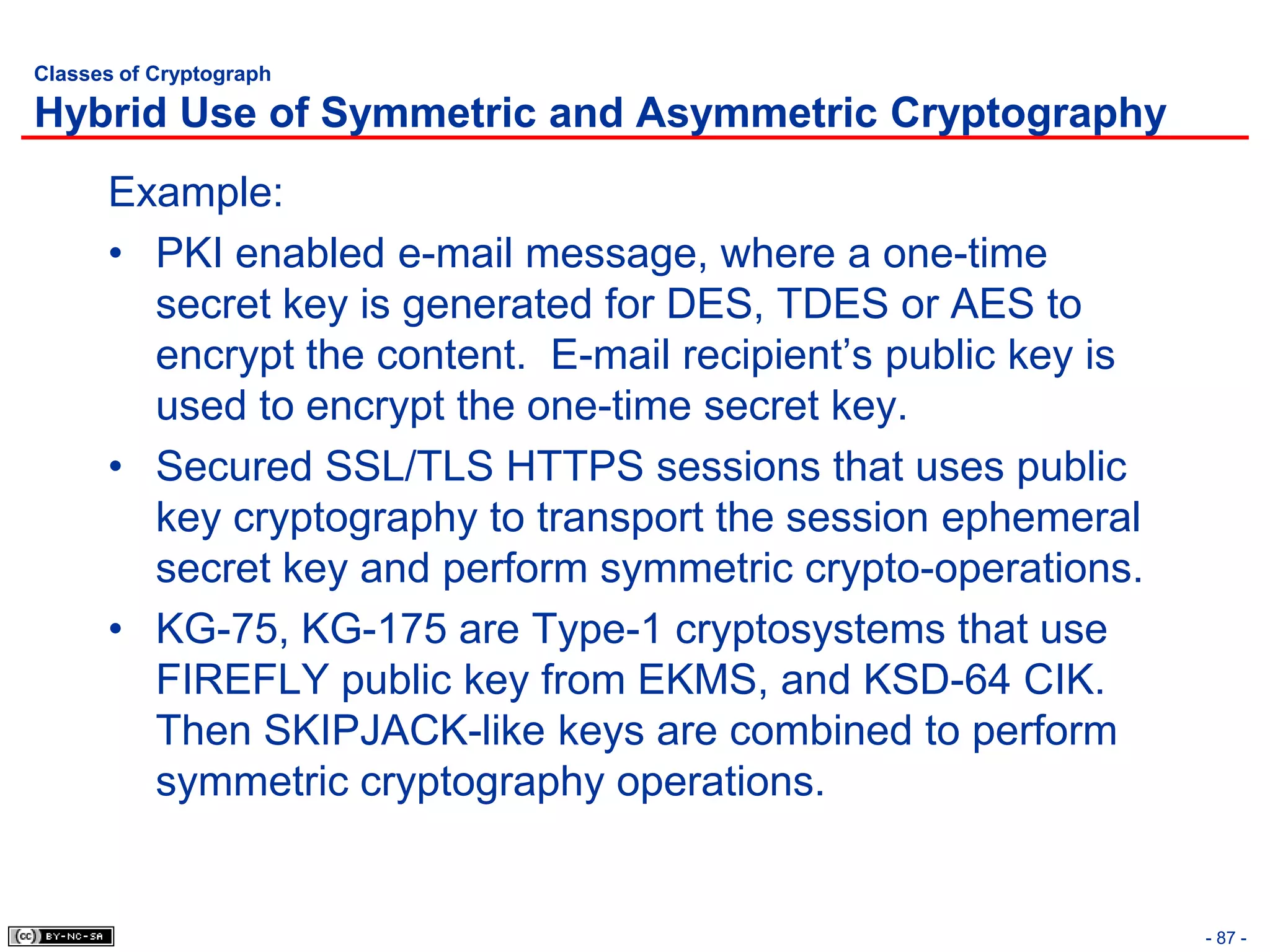
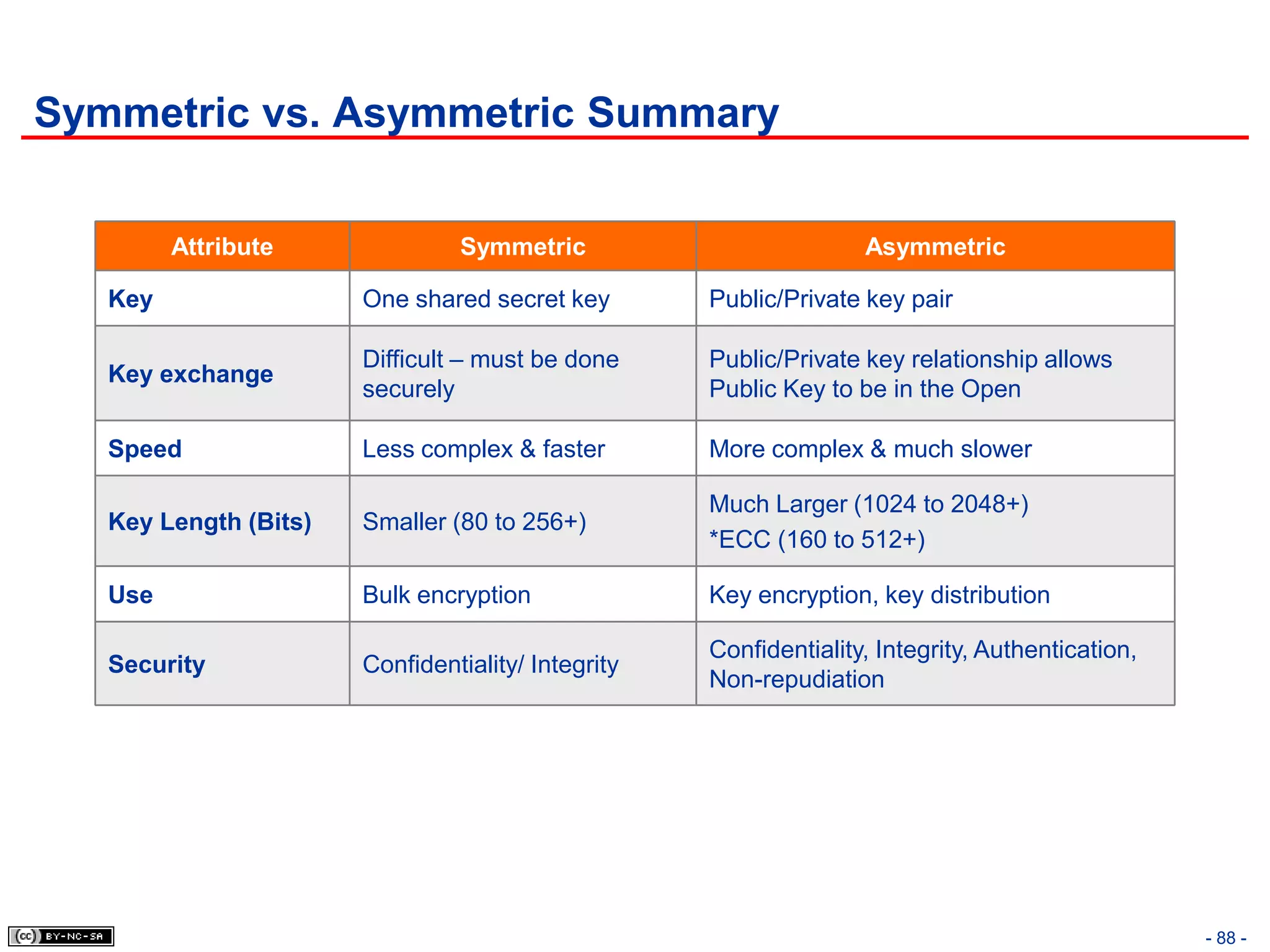
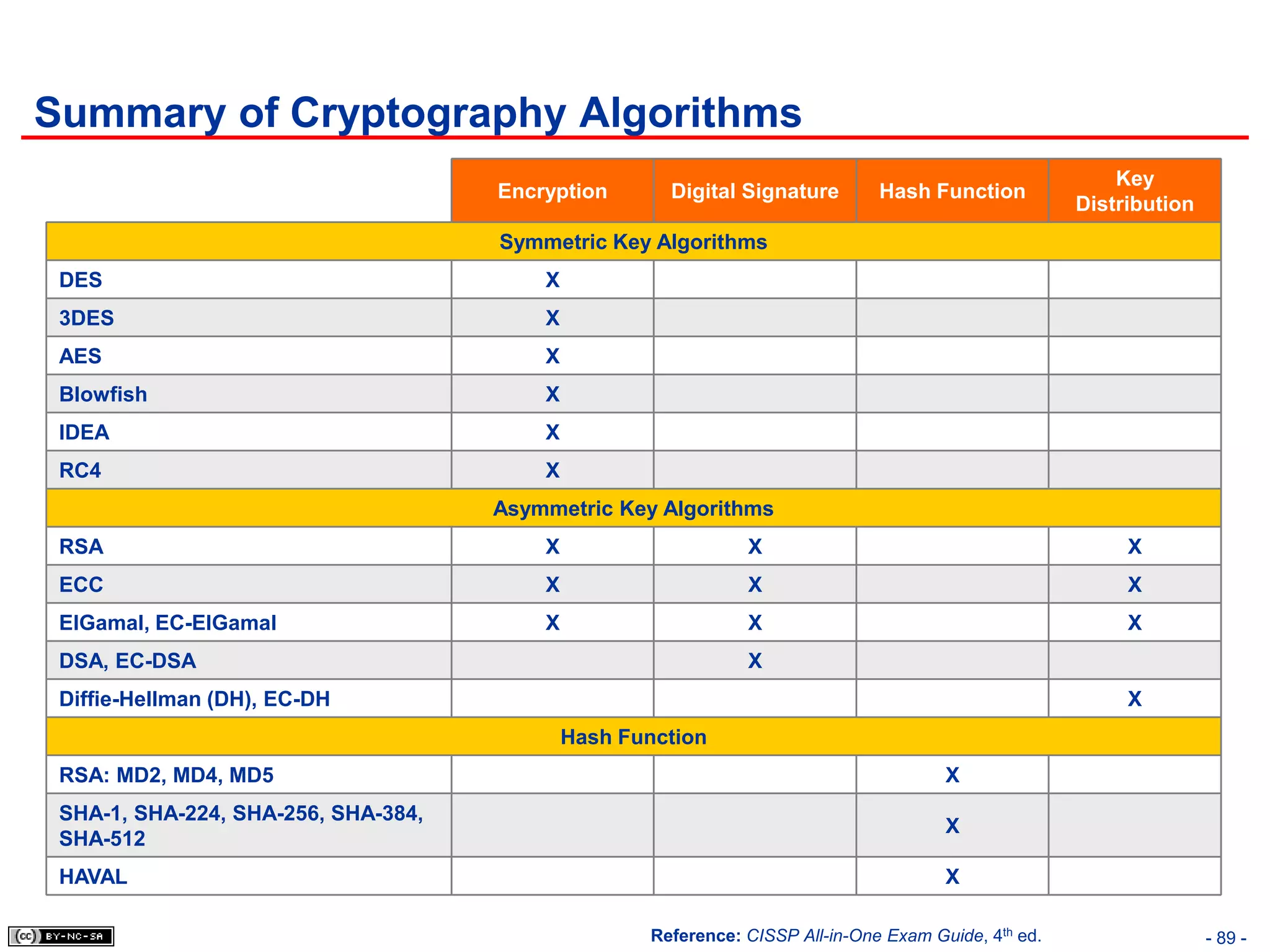
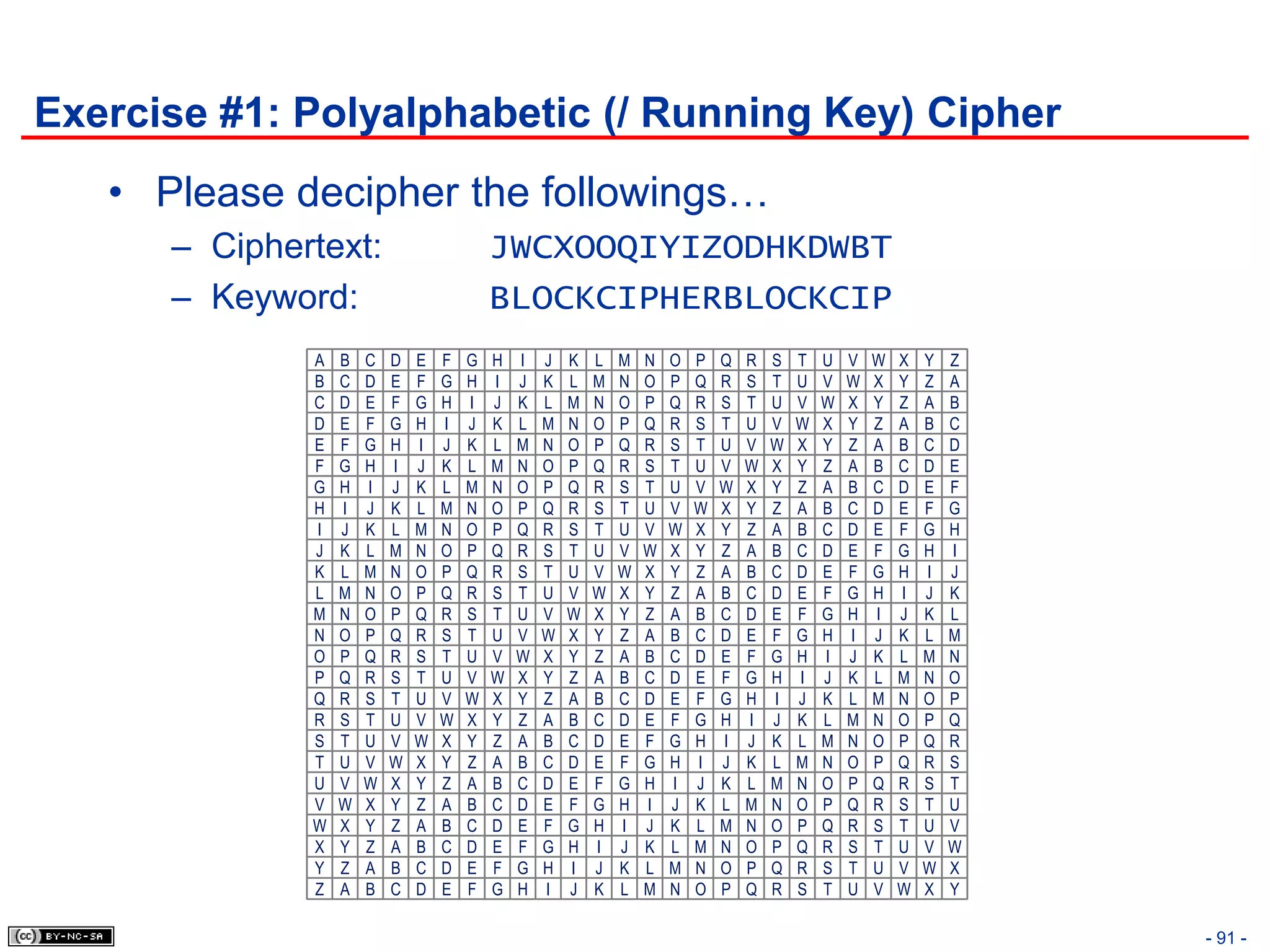
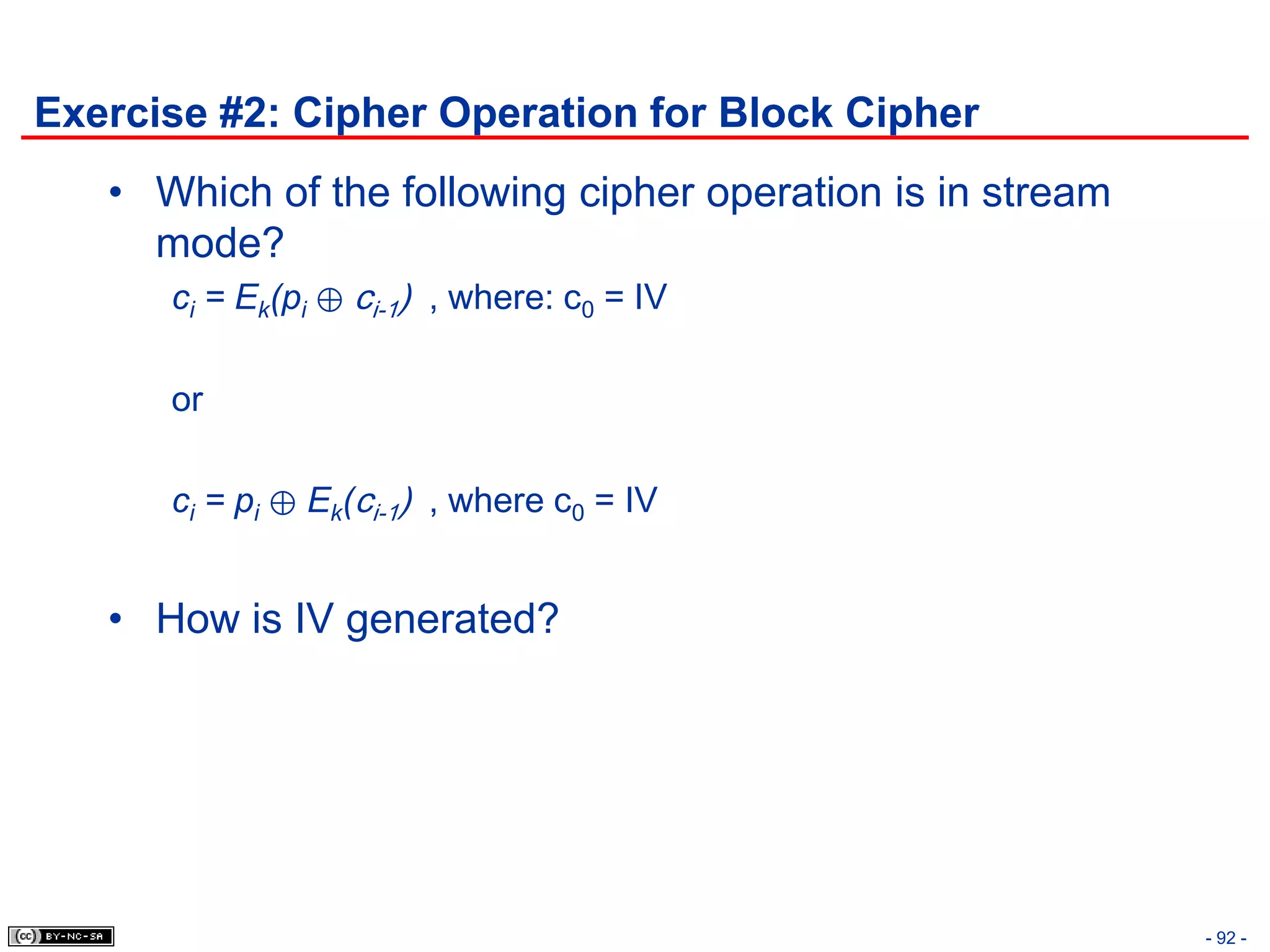
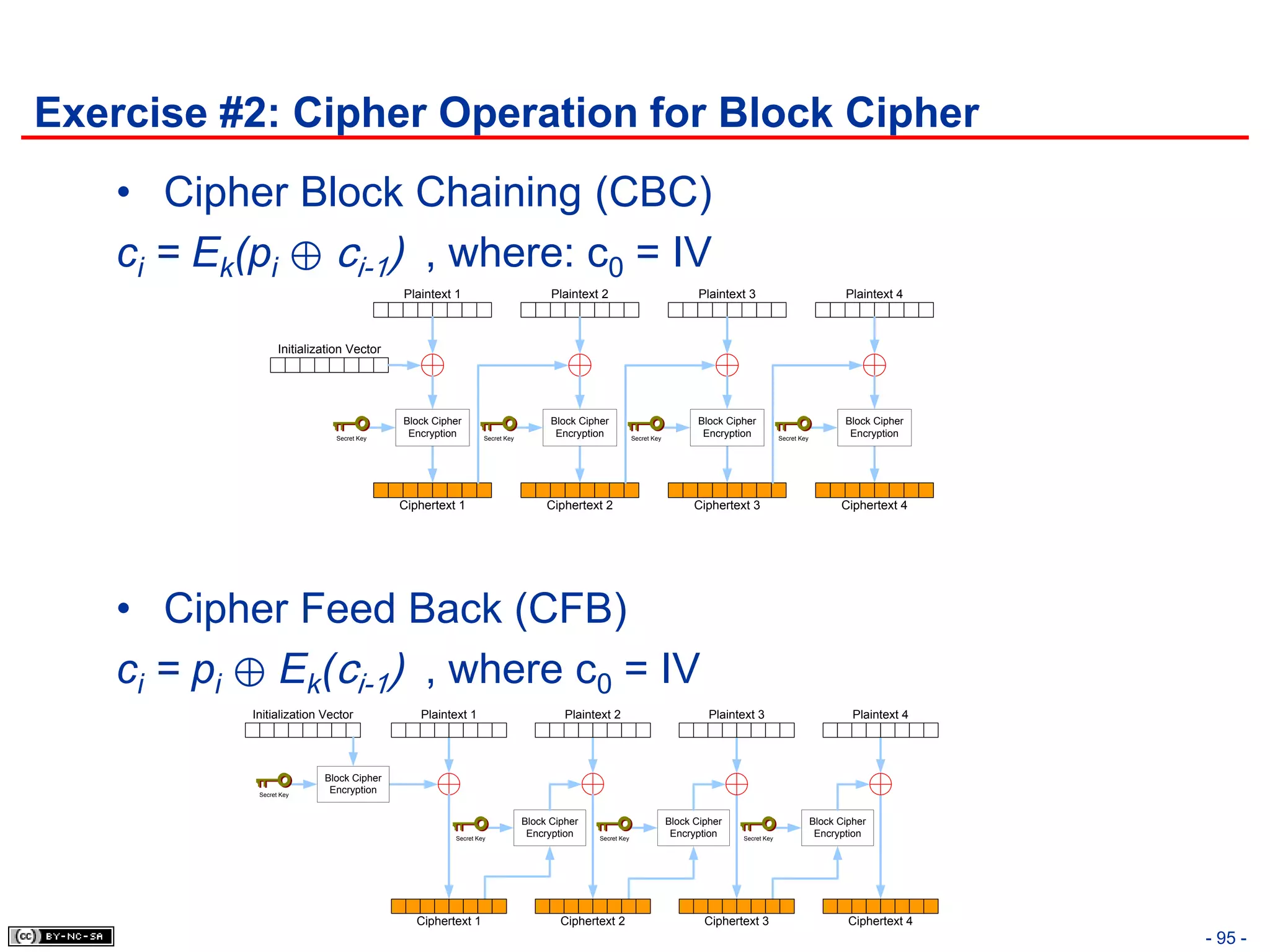
The document discusses the Cryptography domain of the CISSP exam, which addresses principles and methods for ensuring information security. It covers topics like cryptography terms and history, different types of ciphers and cryptographic algorithms, and utilization of cryptography in technologies like PKI and protocols. The document also provides sample questions to test understanding of cryptography concepts.