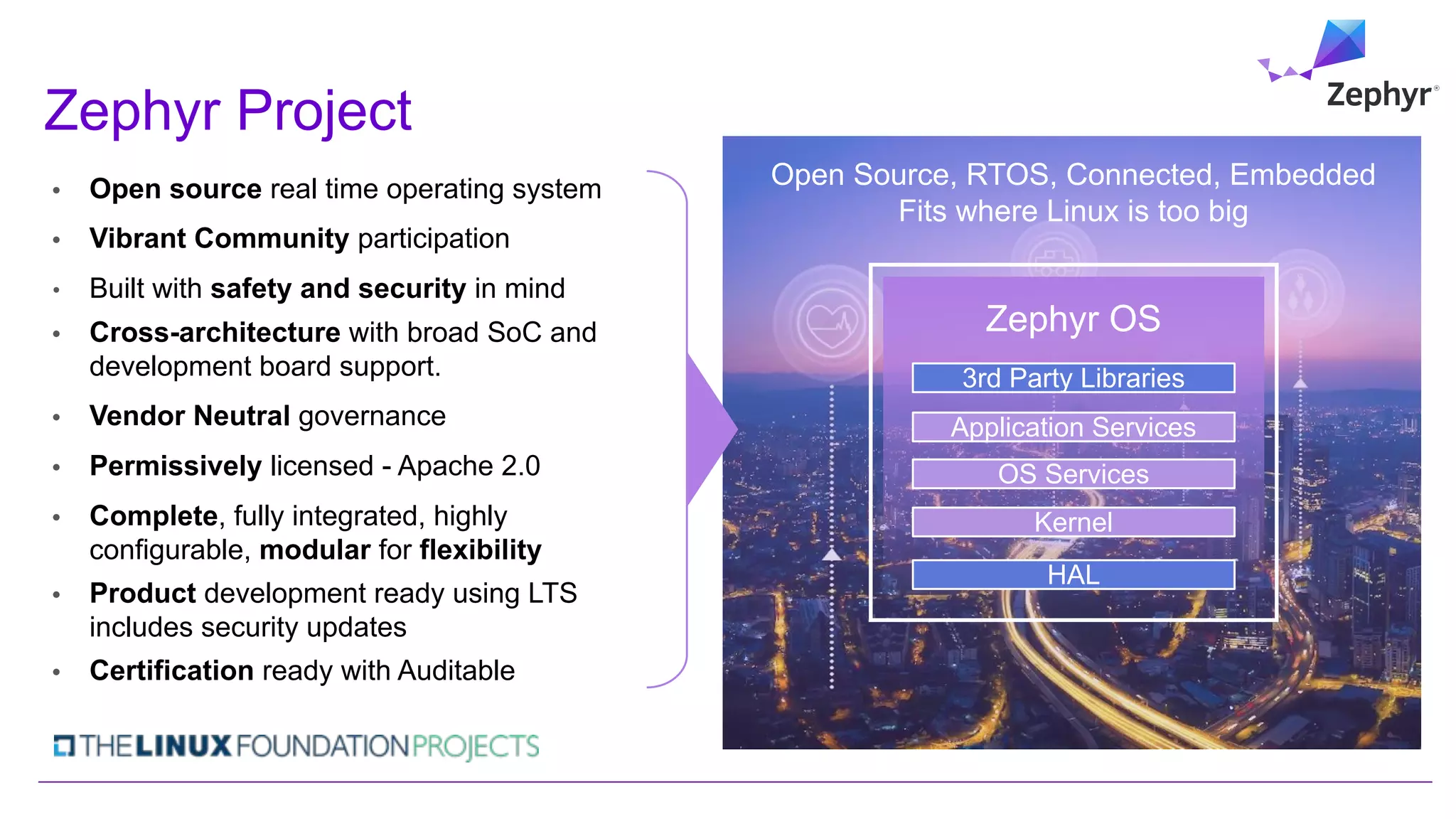
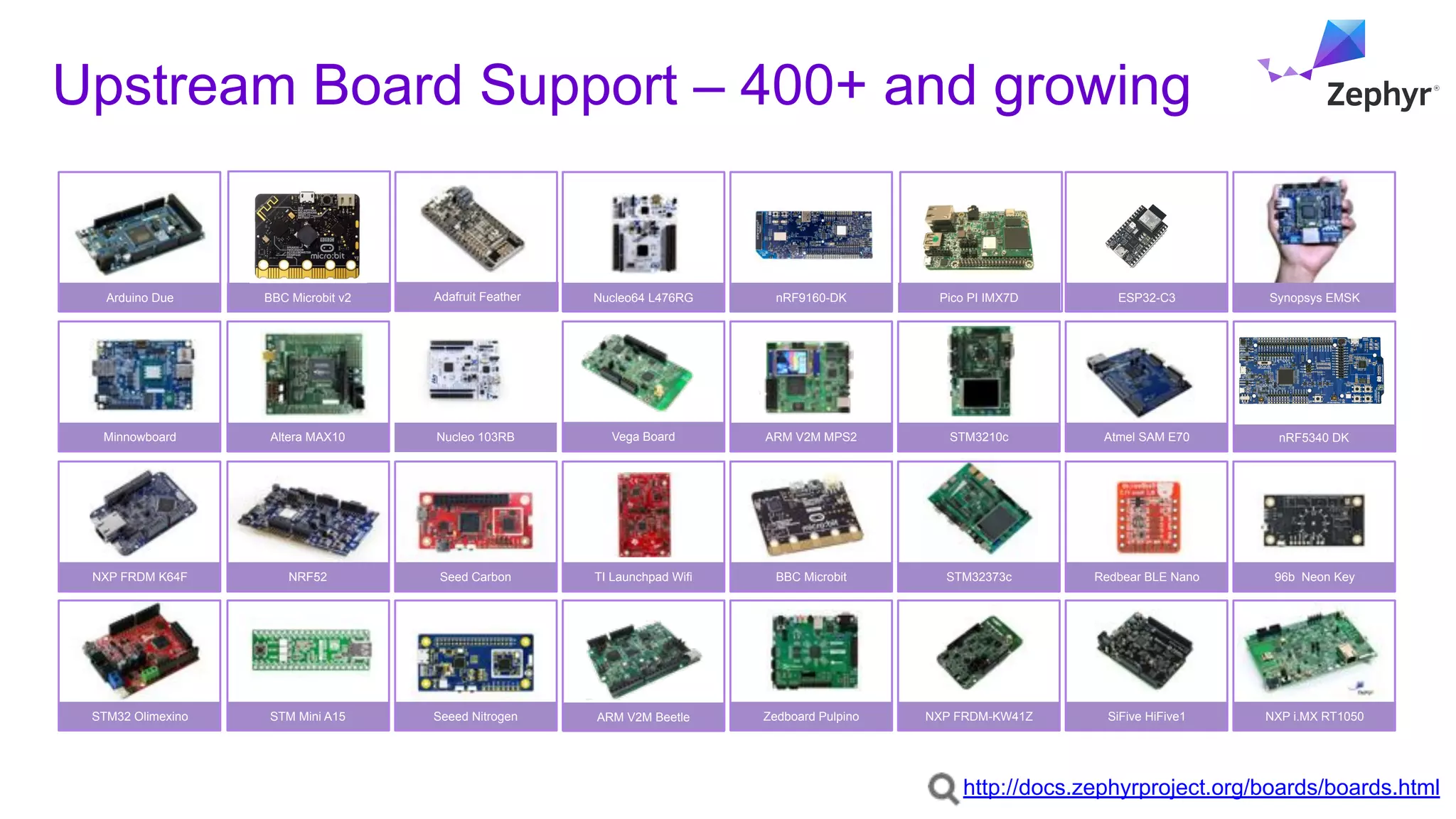
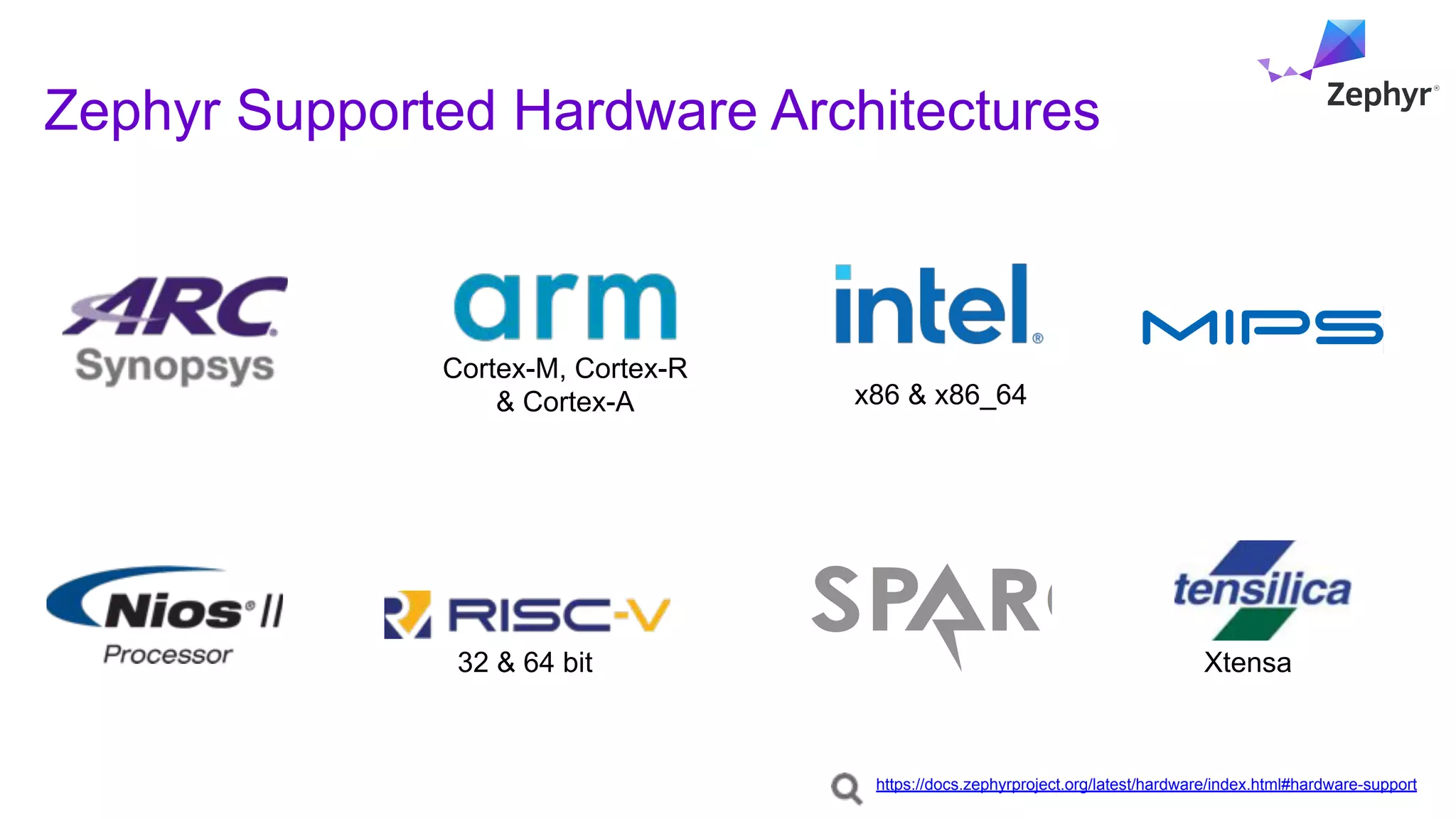
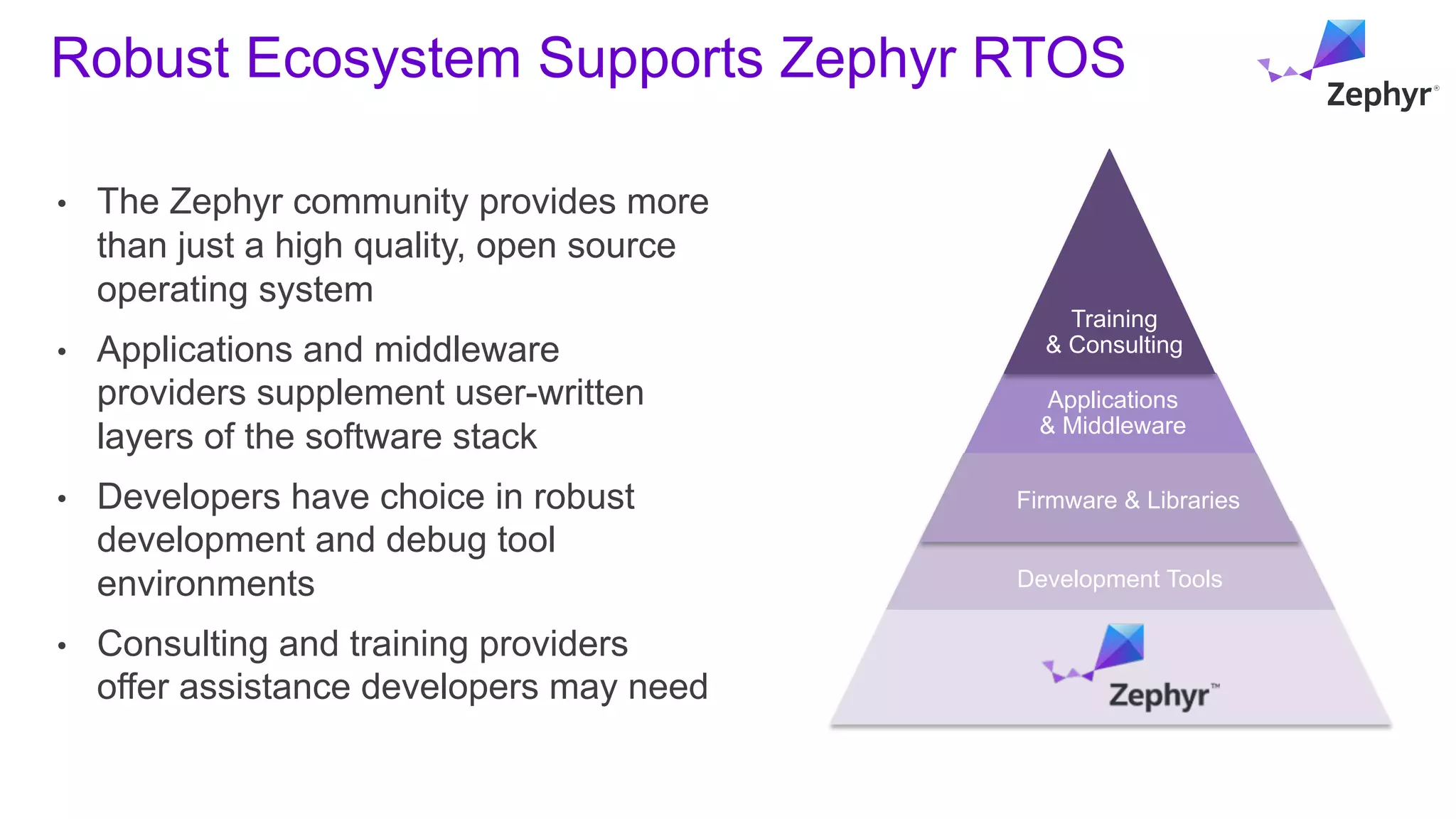
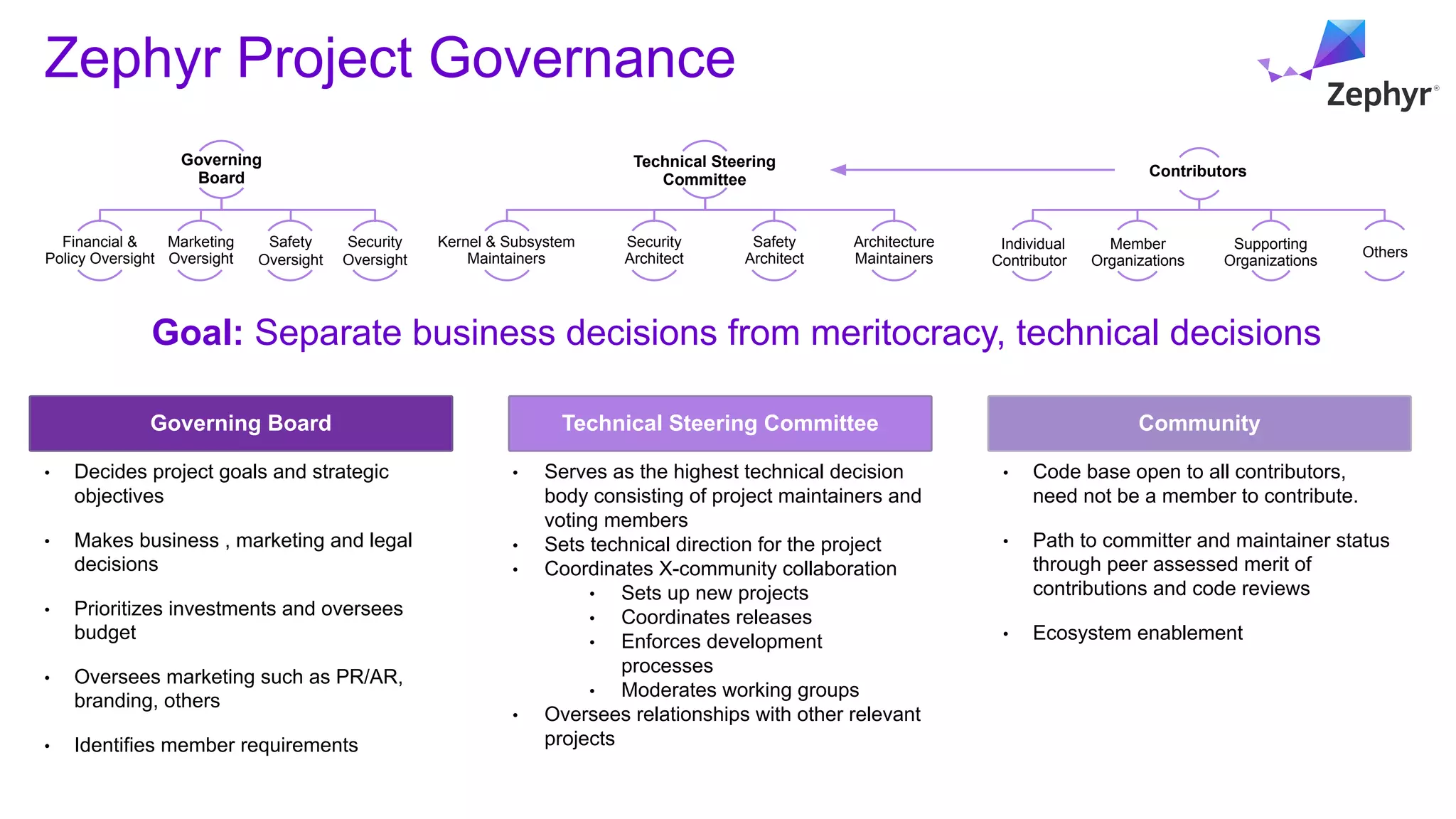
- The document describes the Zephyr real-time operating system which is open source, has a vibrant community, and is built with safety and security in mind. It supports multiple architectures and hardware boards and has vendor-neutral governance.
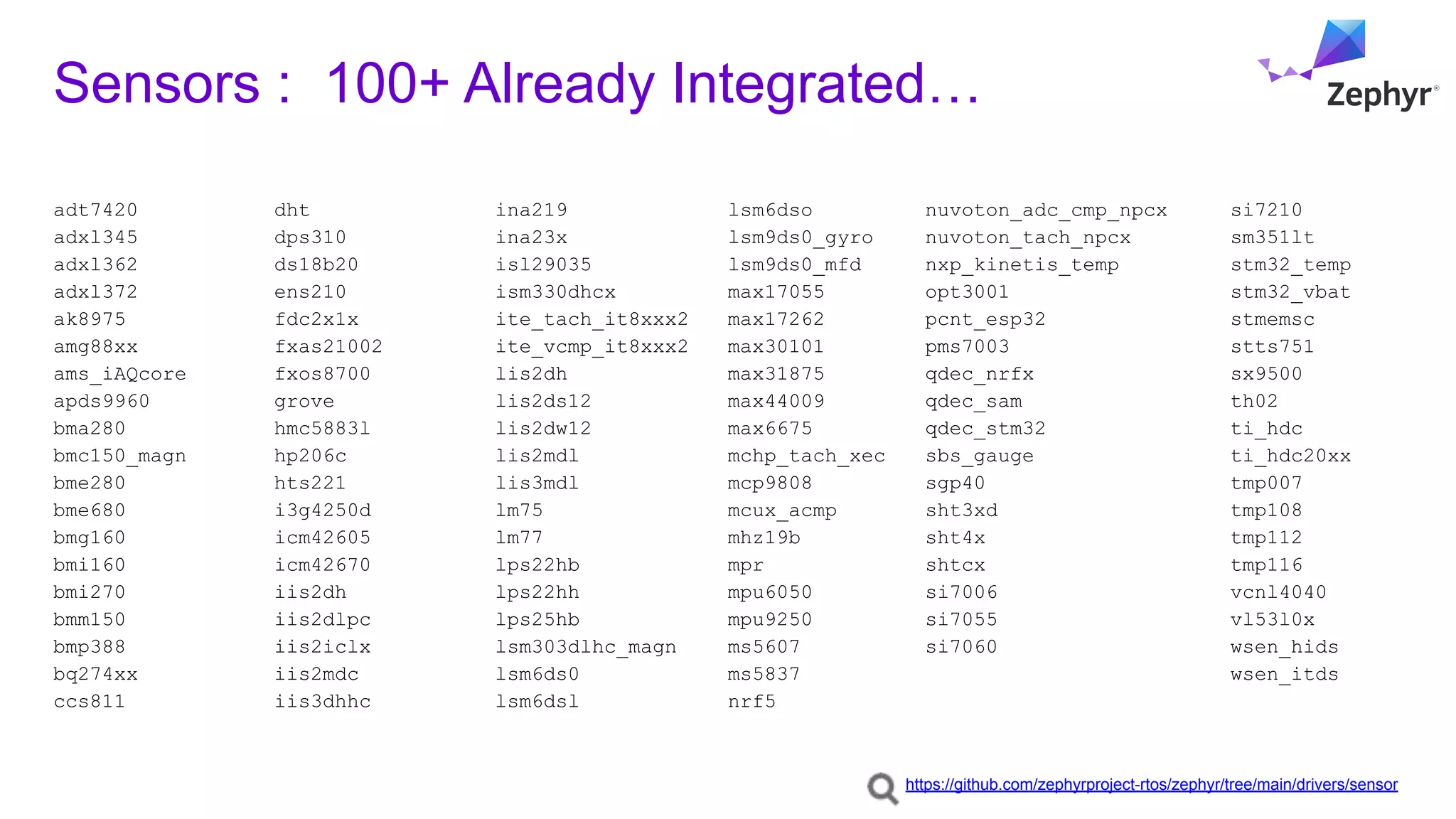
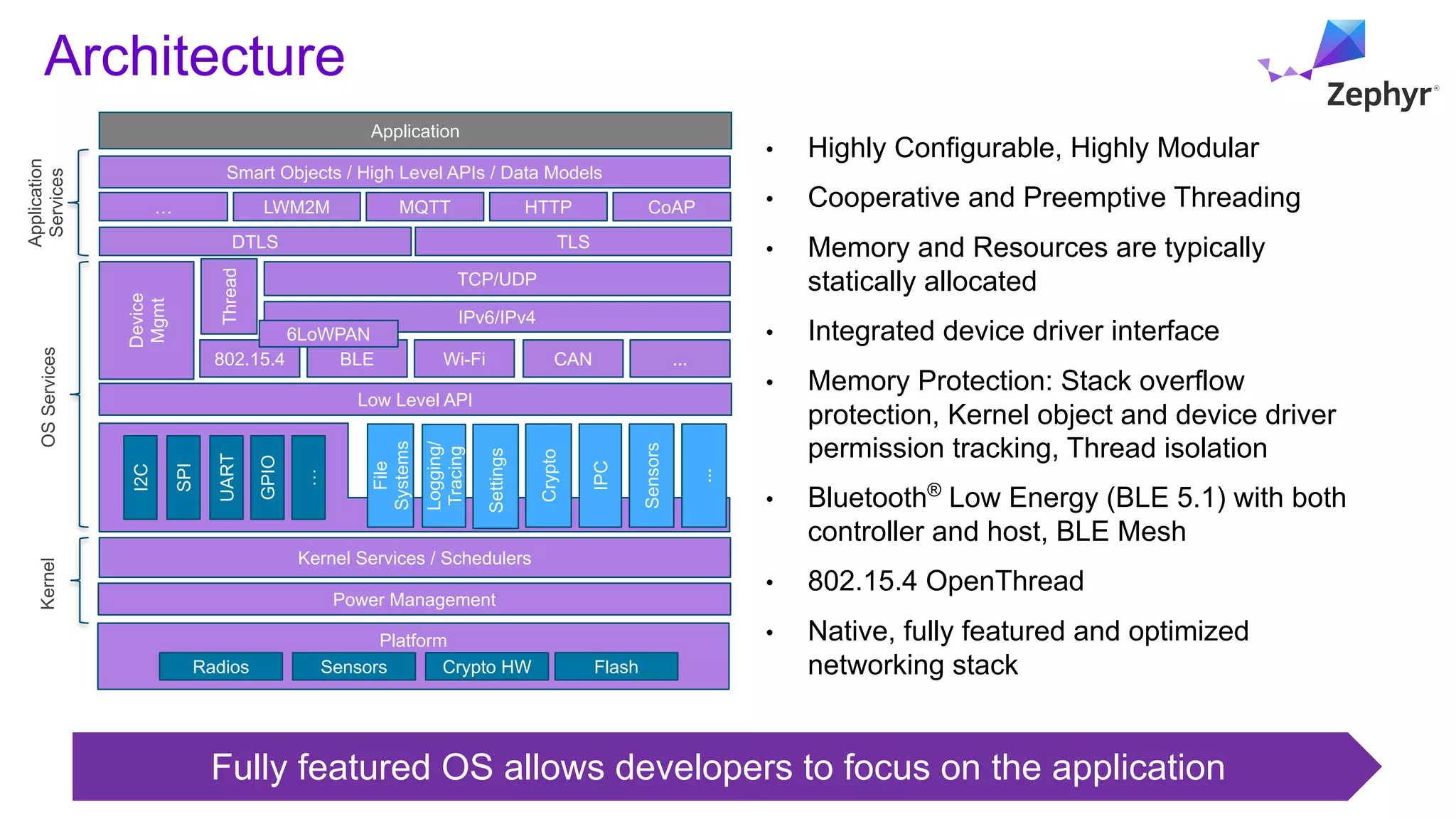
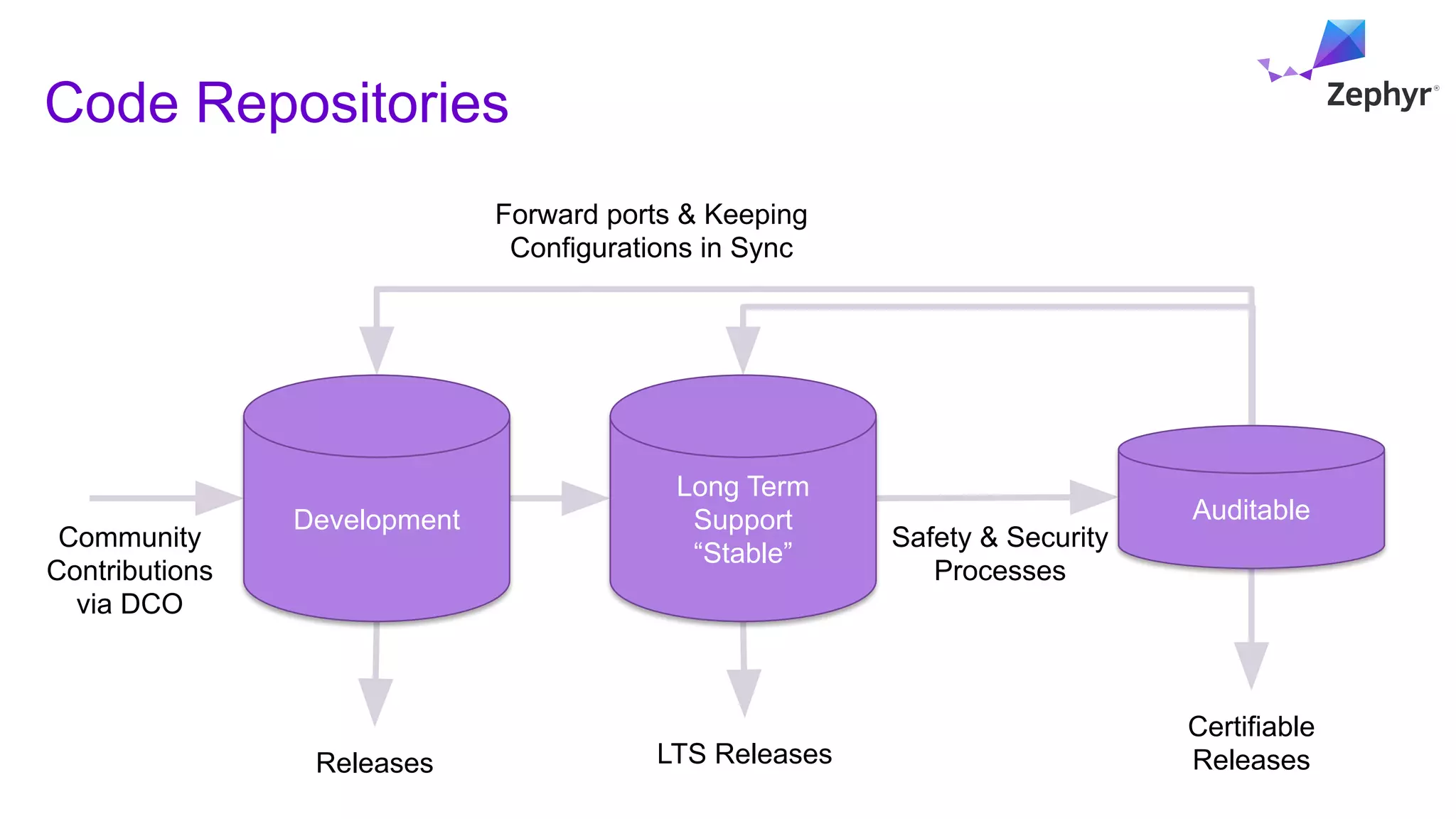
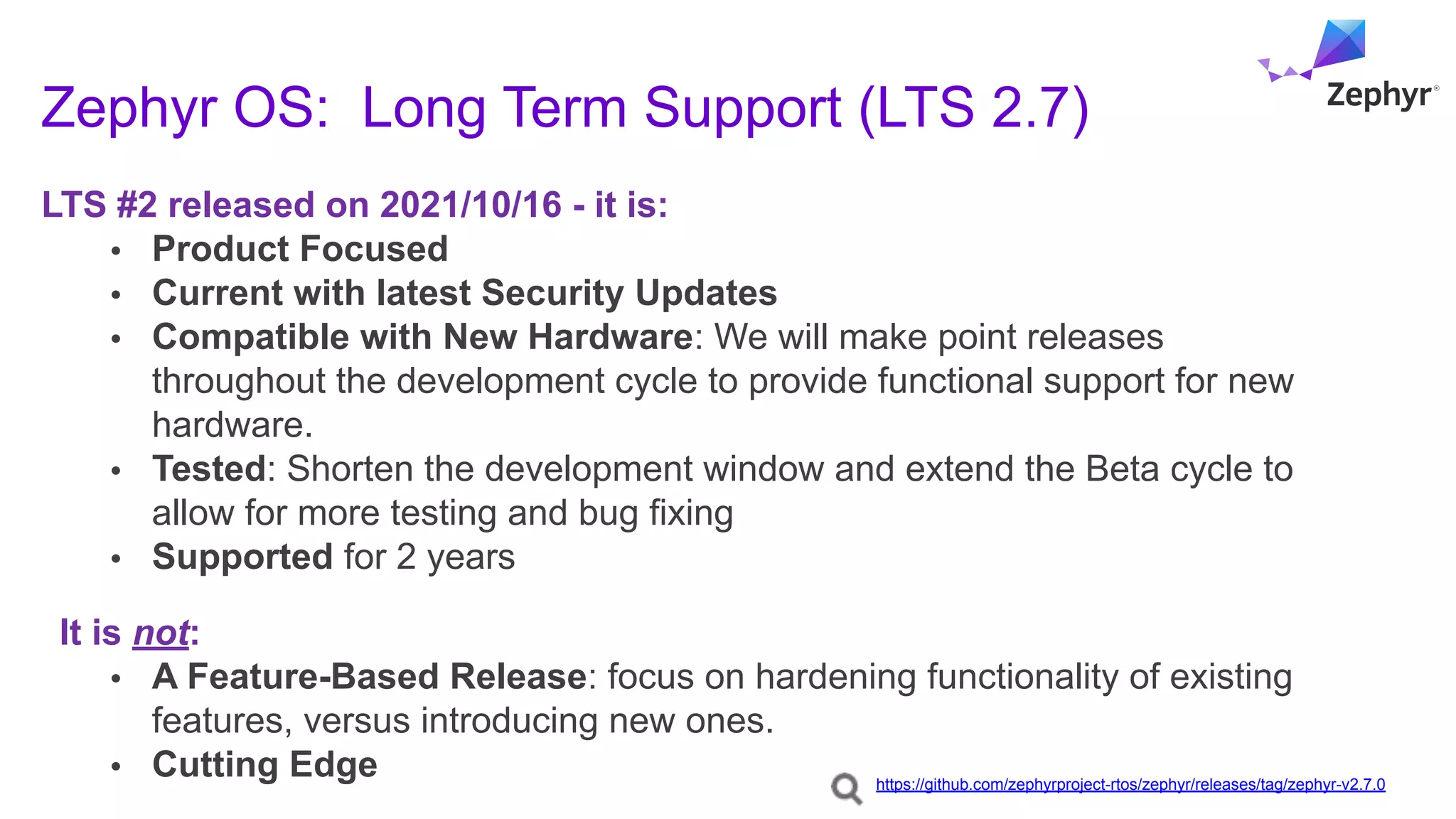
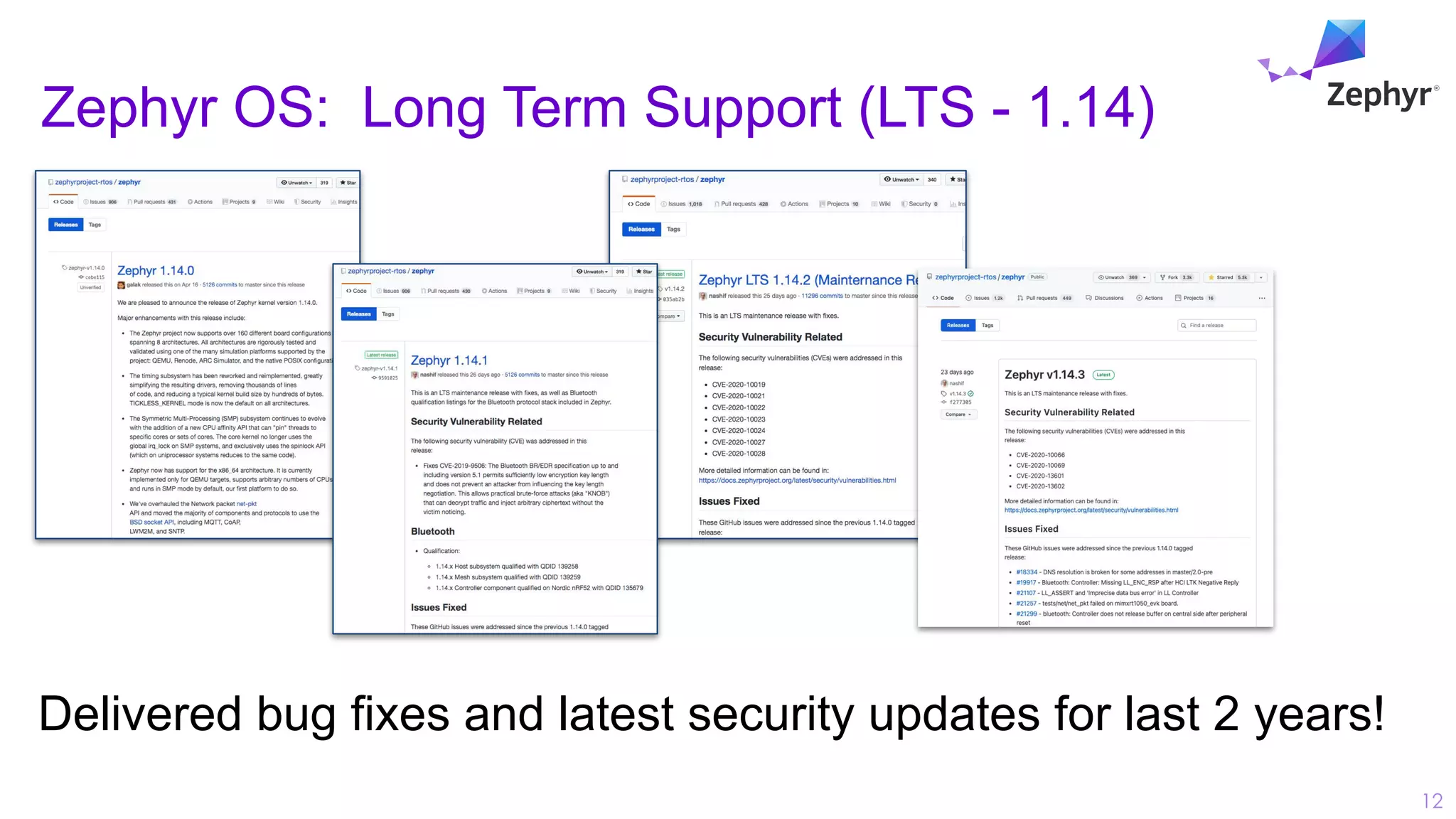
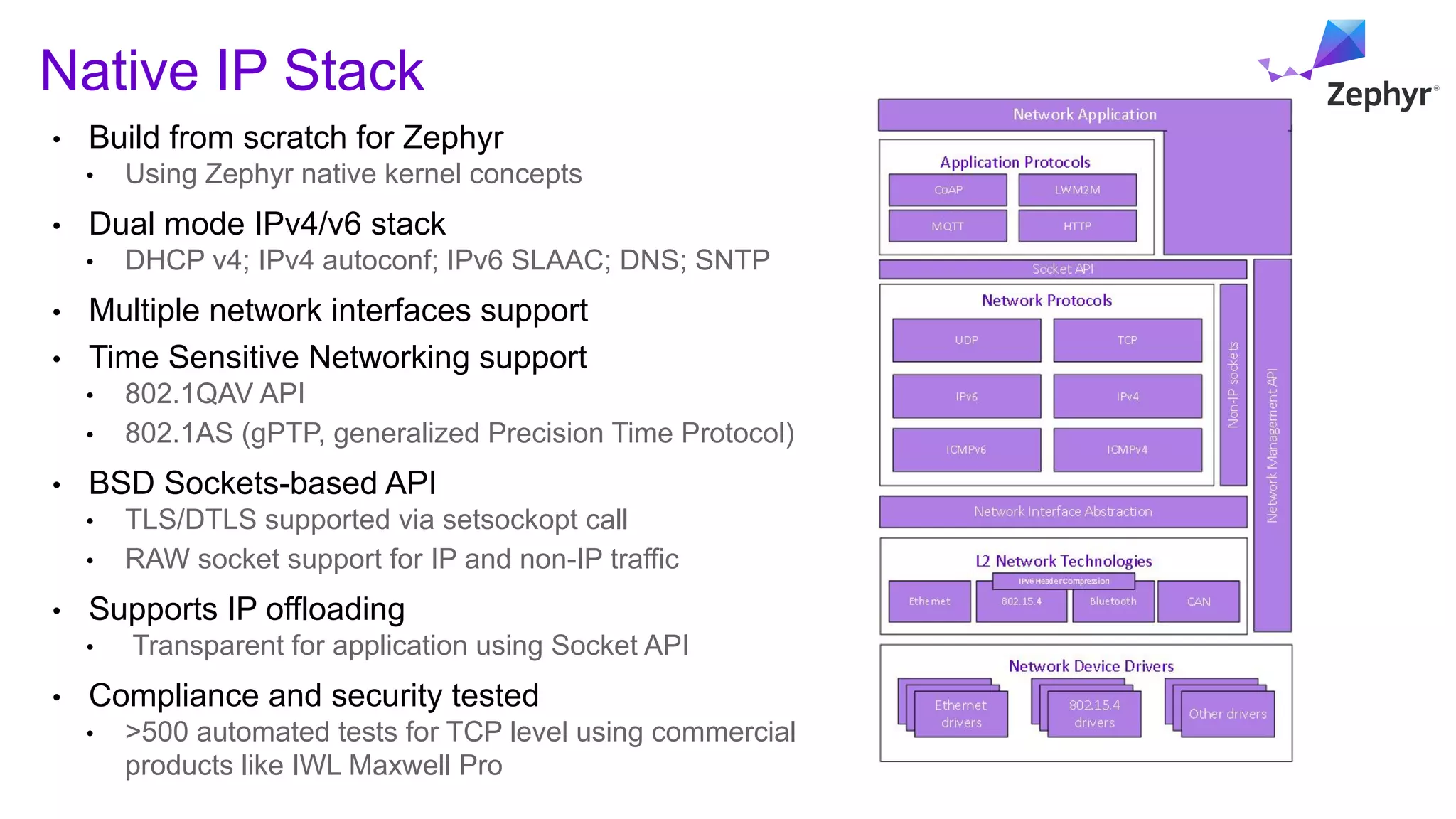
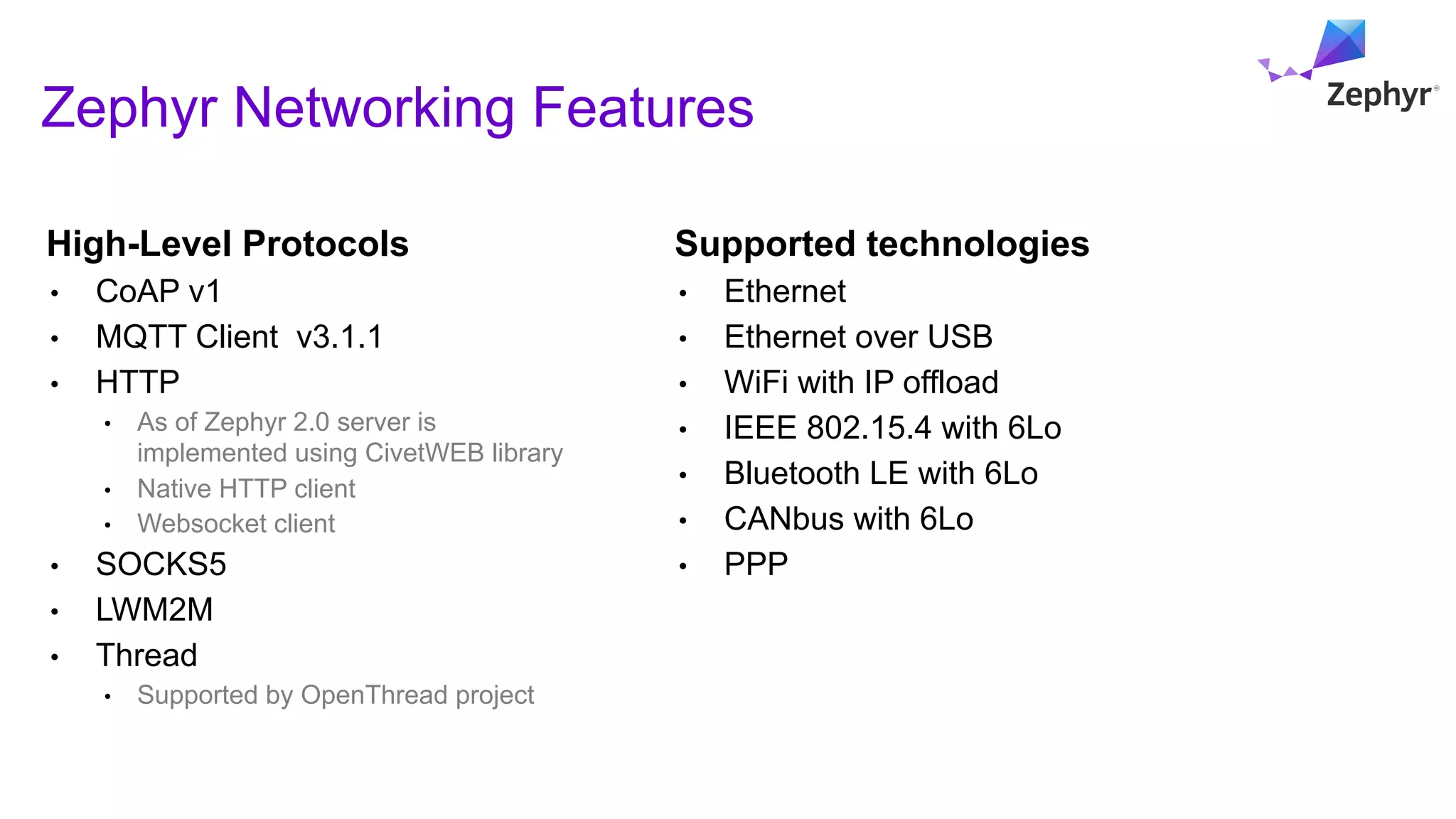
- Key features include being highly configurable, modular, and product development ready using long-term supported releases that include security updates. It provides a range of OS services and supports over 100 sensors out of the box.
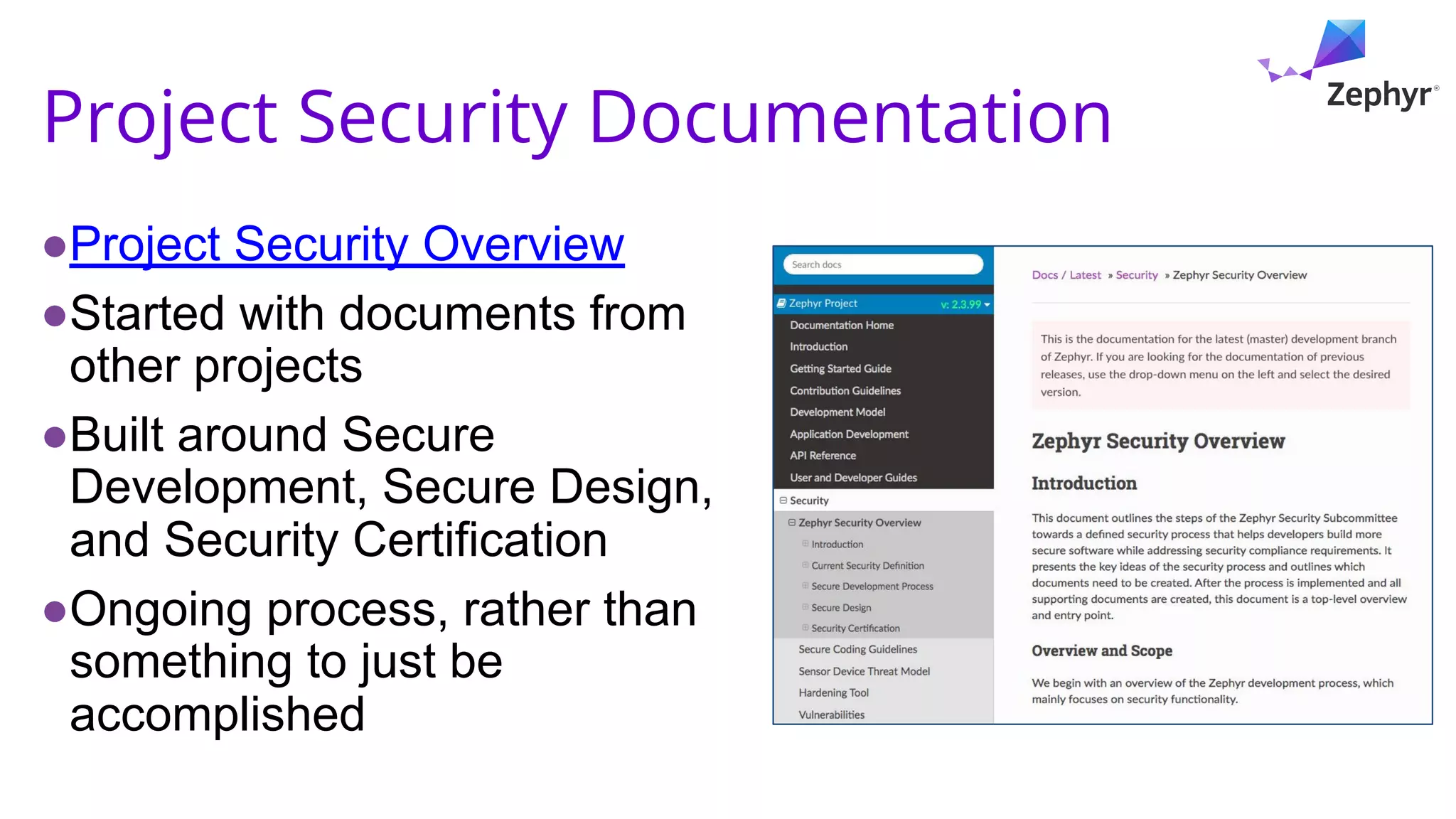
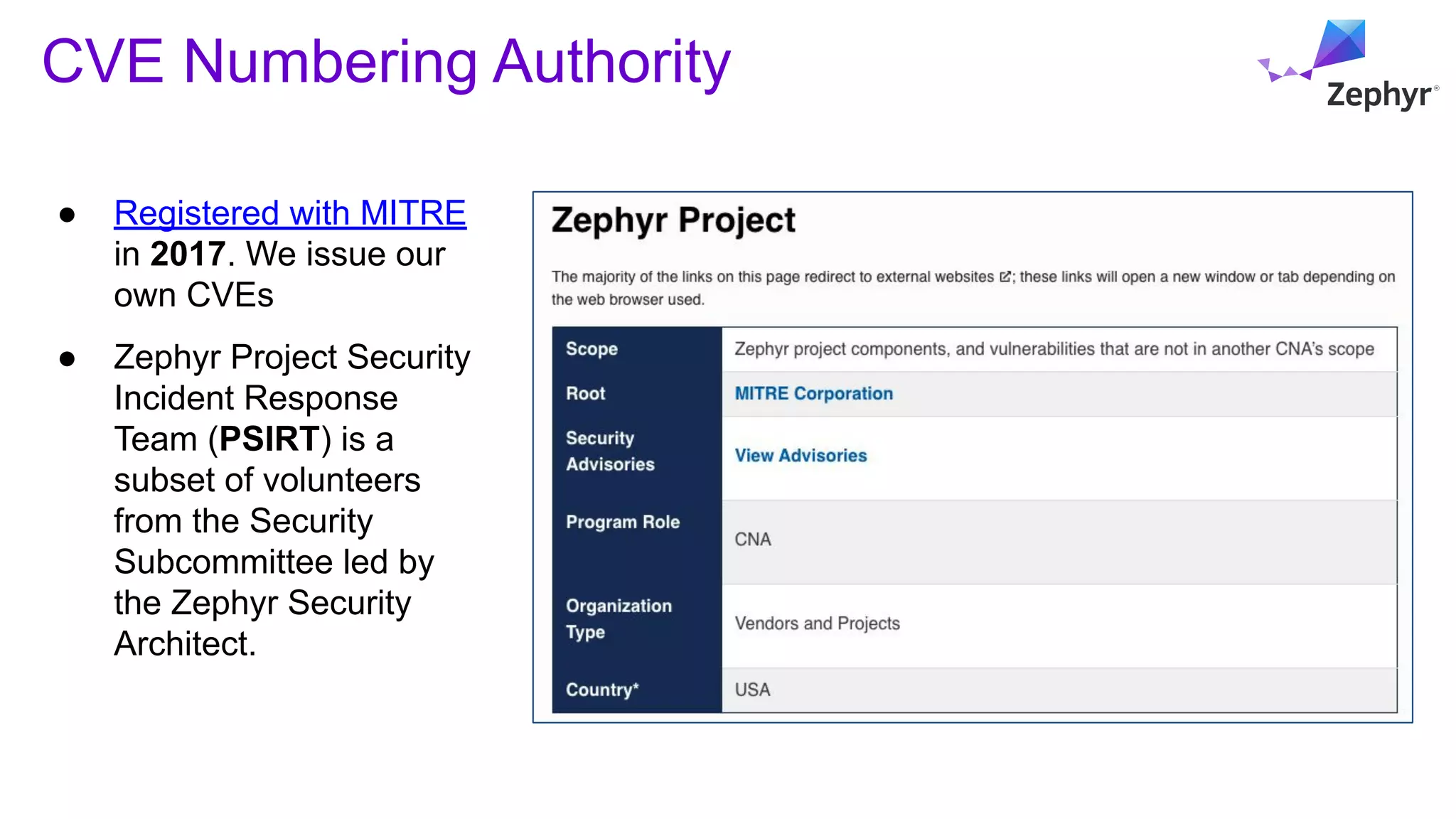
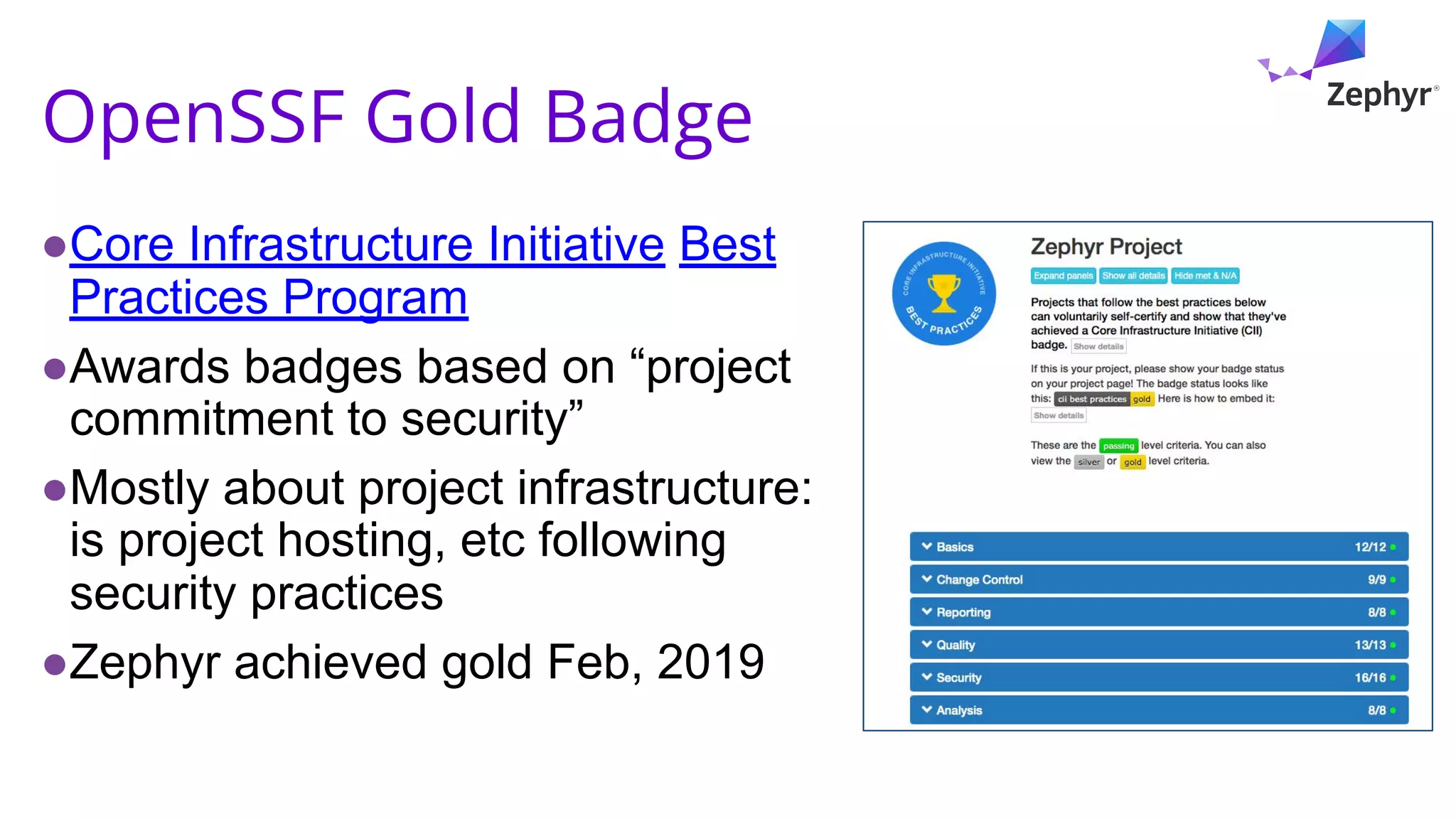
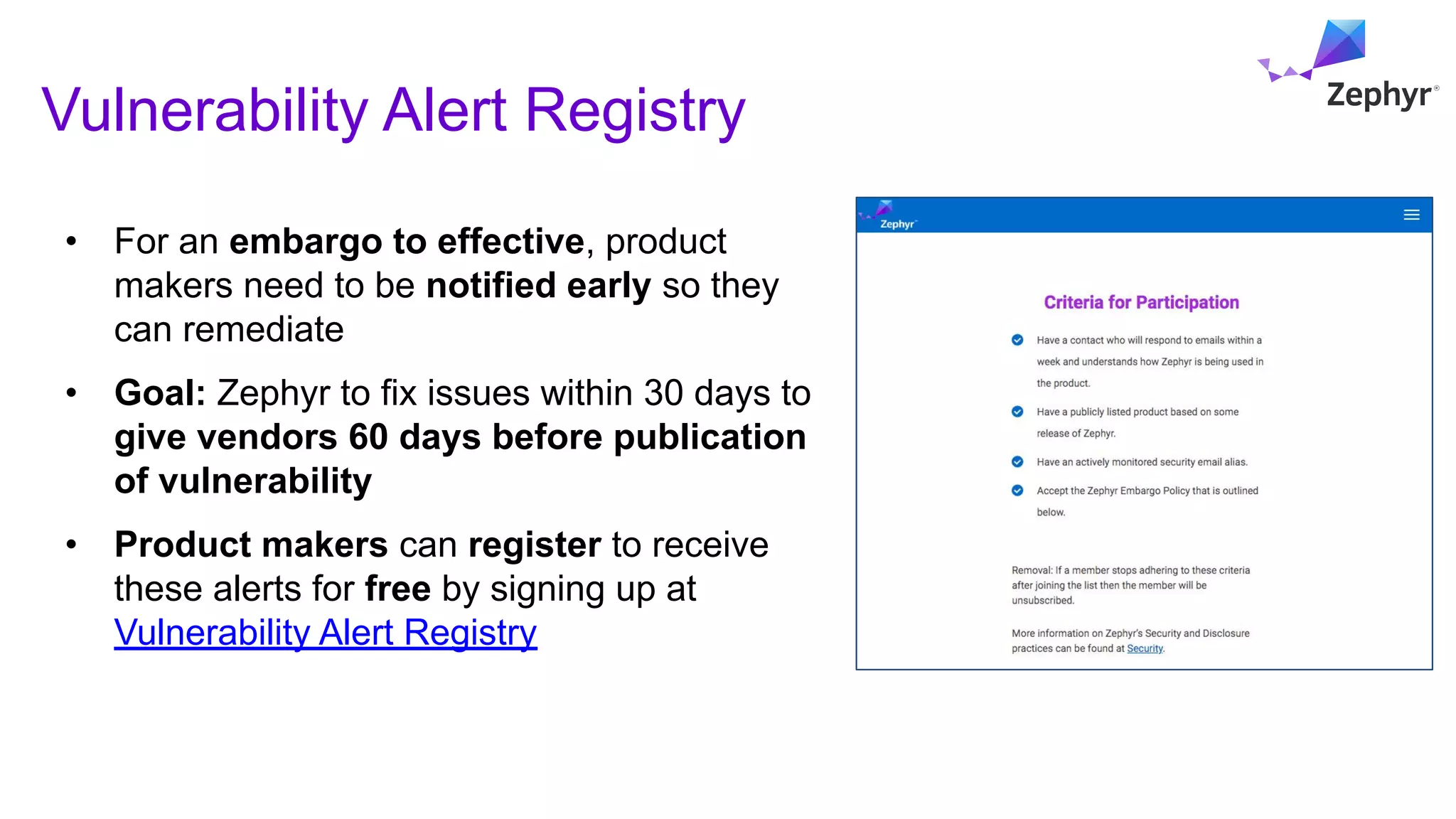
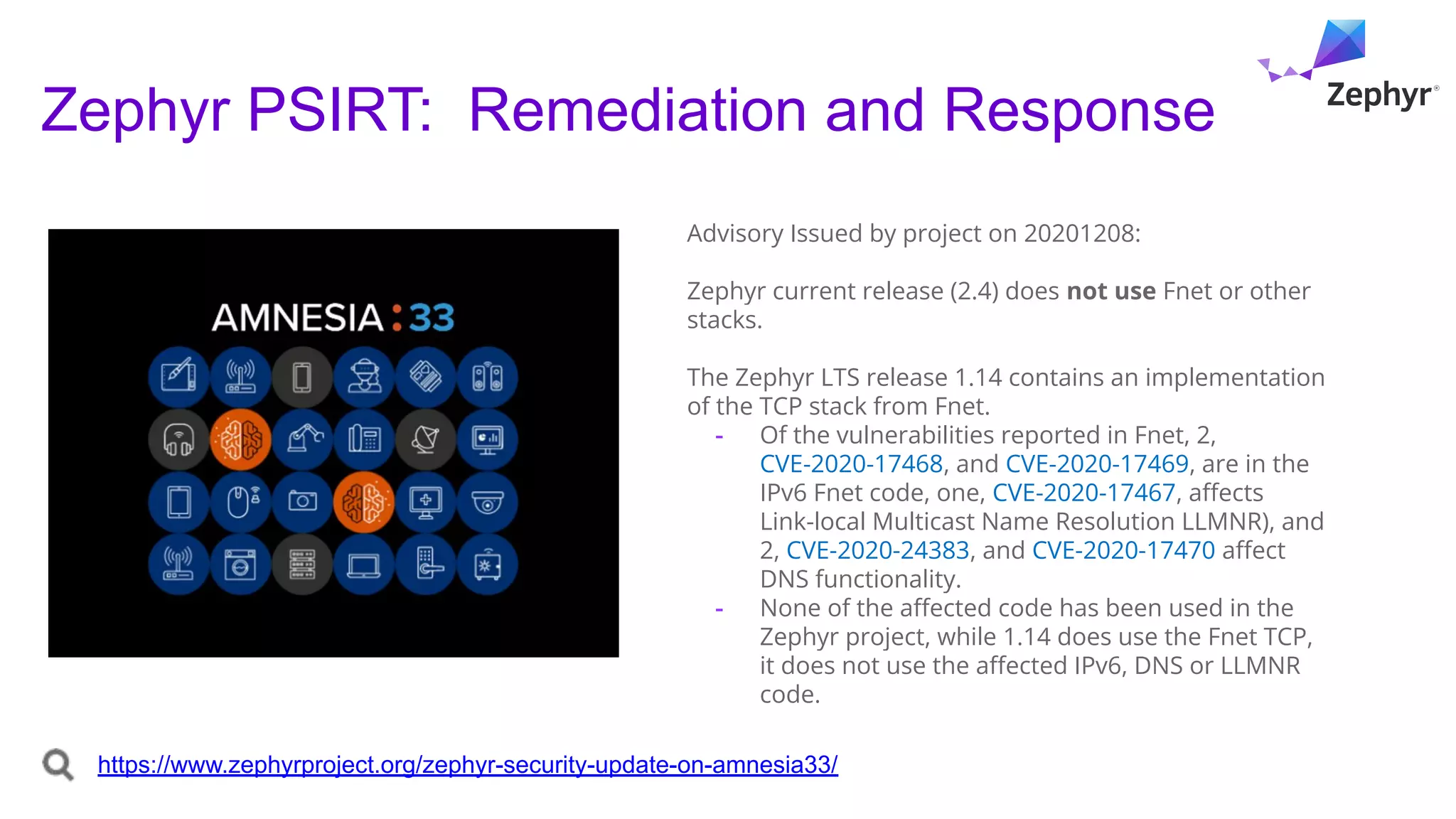
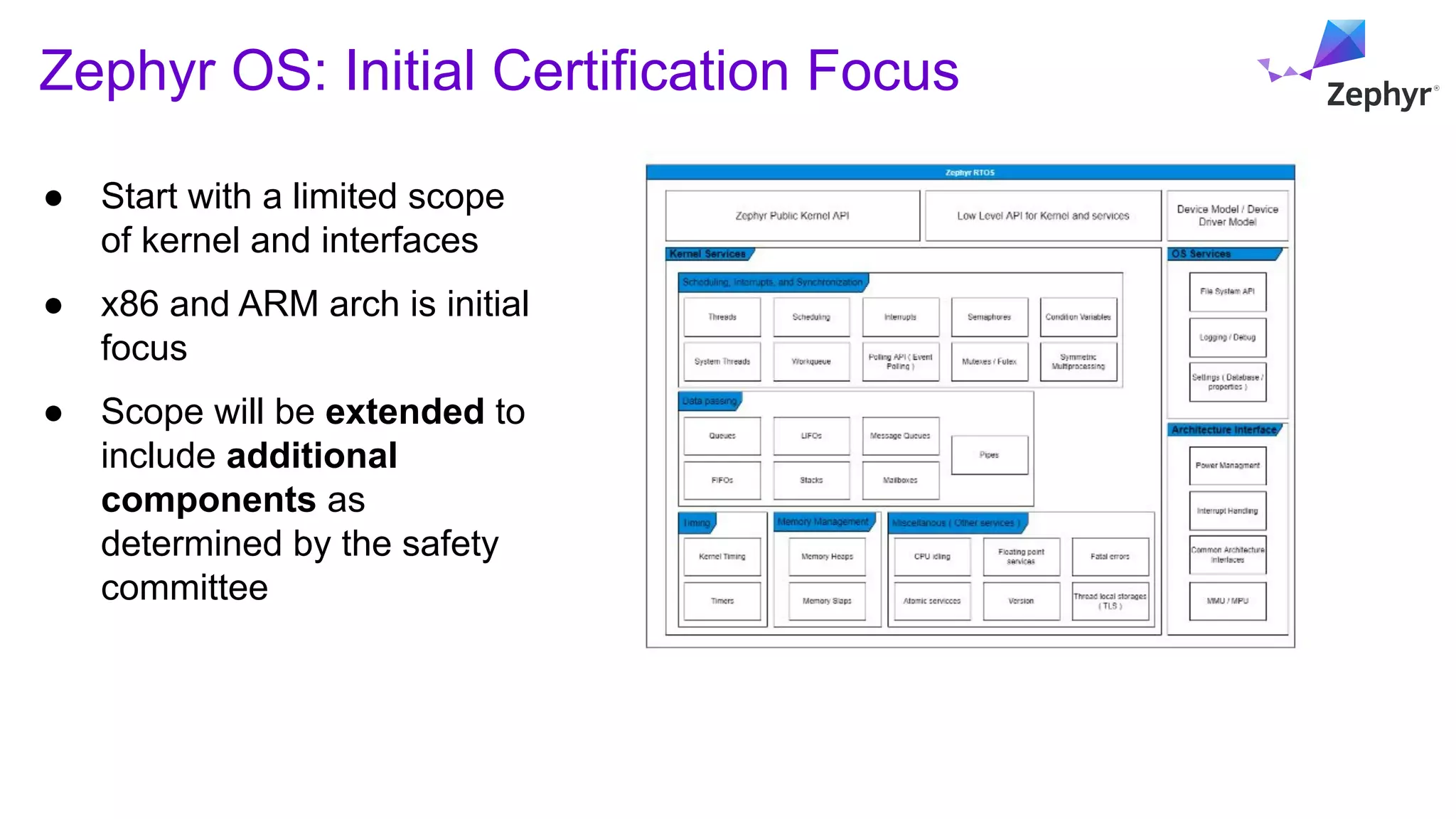
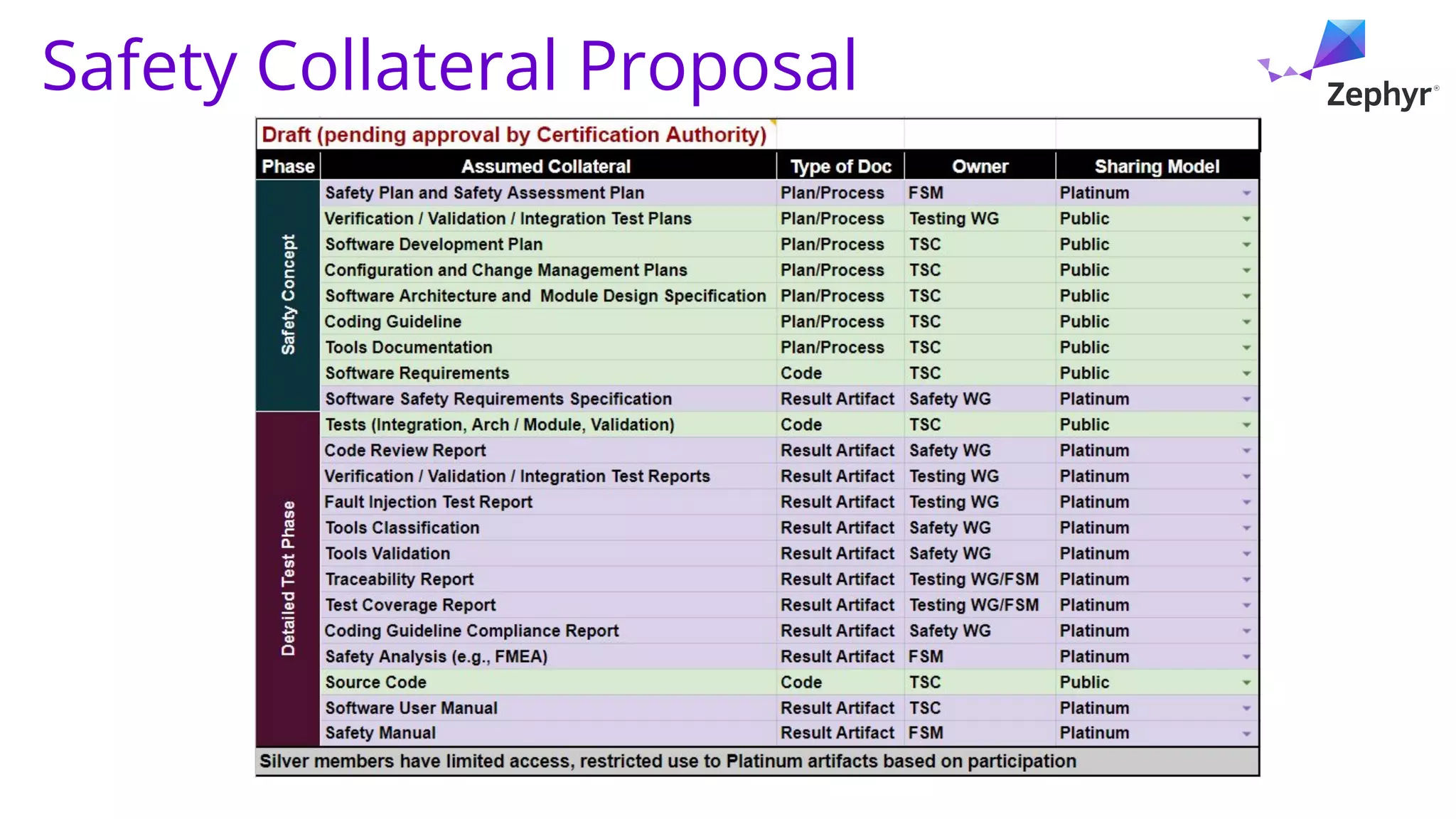
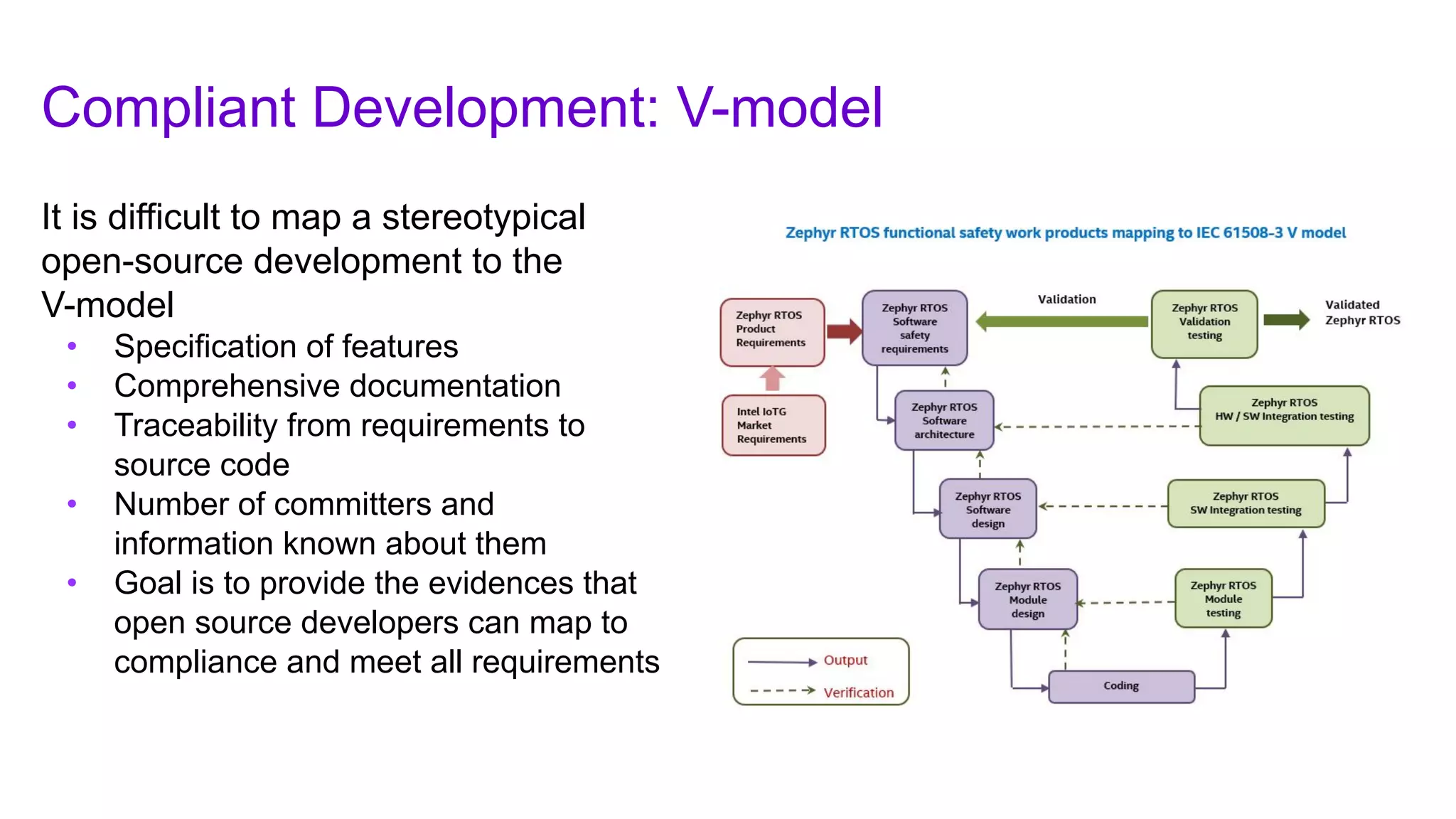
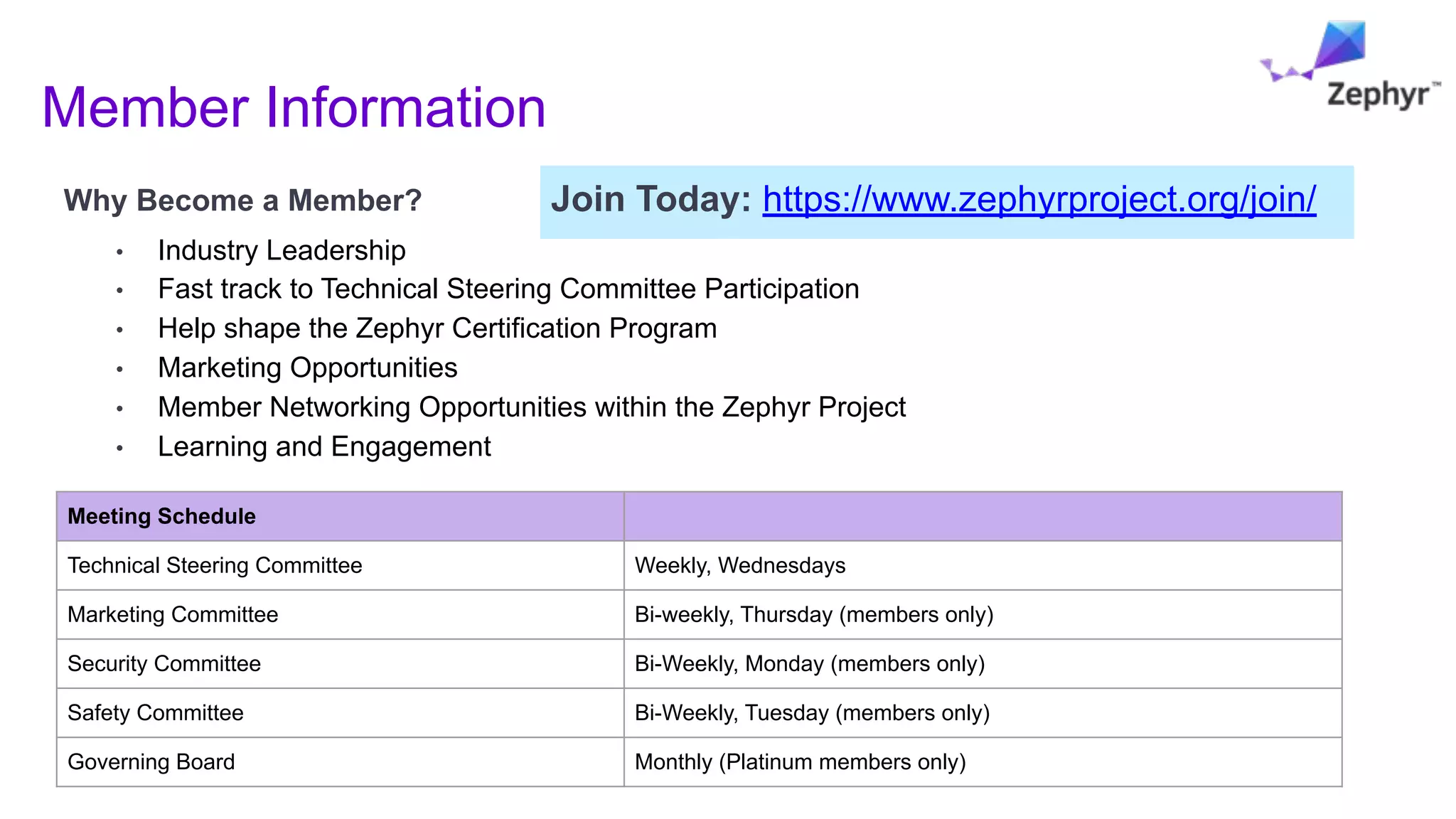
- The project focuses on safety and has established committees to improve security practices and work towards safety certification for applications requiring functional safety standards like IEC 61508.