Www educationsmaterials-com-2020-12-uiet-csjm-university-microprocessor-ece-html
•
0 likes•10 views
UIET CSJM UNIVERSITY MICROPROCESSOR (ECE-S304) B.TECH PAPER 2020-https://www.educationsmaterials.com/2020/12/uiet-csjm-university-microprocessor-ece.html
Report
Share
Report
Share
Download to read offline
Recommended
Logarithm Problems

The document contains several math word problems and questions without showing the solutions:
1) An IBM manufacturer's profit function is given to find the spending needed for a $40 million profit.
2) Two questions ask to find the value of an expression given log or exponential equations.
3) Three questions involve finding unknown values like populations or expressions in terms of log base 2 of given numbers.
Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]![Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]
april - 2017, april - 2016, april - 2015, april - 2014, april - 2013, october - 2017, october - 2016, october - 2015, october - 2014, may - 2016, may - 2017, december - 2017, 75:25 pattern, 60:40 pattern, revised course, old course, mumbai bscit study, mumbai university, bscit semester vi, bscit question paper, old question paper, previous year question paper, semester vi question paper, question paper, CBSGS, IDOL, kamal t, internet technology, digital signals and systems, data warehousing, ipr and cyber laws, project management, geographic information system
Cs 68 (p)s1

The document is a past practical examination for a Bachelor of Computer Applications degree from June 2011. It consists of 4 short answer questions worth a total of 20 marks about computer networks topics like network topologies, switch specifications, checking the MAC address, and LAN cable specifications. Students have 2 hours to complete the examination which is worth 15% of the term grade.
Www educationsmaterials-com-2020-12-microprocessor-btech-paper-2020-kanpur-html

This document contains a microprocessor exam for a B.Tech IIIrd year Electronics and Communication Engineering course. The exam contains three sections with multiple choice and descriptive questions. Section A contains 5 short 2-mark questions about microprocessor instructions, bus demultiplexing, and generating square waves. Section B contains 6 longer 3-mark questions about memory interfacing, timing diagrams, registers, 7-segment displays, and arrays. Section C contains 3 even longer 4-mark questions about interrupts, addressing modes, analog to digital conversion, and interrupt controllers. Students are instructed to attempt all questions across the three sections in the allotted three hours.
Mcs 041 assignment solution (2020-21)

Mail us at : help.mbaassignments@gmail.com
Call us at : 08263069601
Dear students, get latest Solved assignments and case study help by professionals.
Coa 

The document discusses pipeline processing and memory organization. It provides definitions and explanations of key concepts related to pipelining such as stages in a pipeline, hazards, and caching. It also covers memory hierarchy concepts like registers, cache, main memory, and secondary storage. Multiple choice questions with answers are provided to test understanding of these topics.
Bca(rev syll ii-sem) assignment for july 2012 and jan 2013 sessionn

This document contains assignments for the second semester of the Bachelor of Computer Applications (BCA) program for the year 2012. It includes assignments for 6 courses - MCS-011 Problem Solving and Programming, MCS-012 Computer Organisation and Assembly Language Programming, MCS-013 Data Structure, MCS-015 Operating System, BCSL-021 Computer Oriented Statistical Techniques, and BCSL-022 Discrete Mathematics. The assignments provide questions to test students' understanding of the course content and must be submitted by October 15th for the July session or April 15th for the January session.
Penn State University School of.docx

This document describes a lab assignment for a computer organization and design course. The goal of the lab is for students to gain experience designing and testing the first four stages of a five-stage pipelined CPU using an FPGA design package. Specifically, students will implement circuits for the instruction fetch, instruction decode, execution, and memory stages. The document provides background on pipelining, describes the circuits for each stage, lists the MIPS registers and sample instructions, and provides instructions for students to design the stages in Verilog and write a report on their work.
Recommended
Logarithm Problems

The document contains several math word problems and questions without showing the solutions:
1) An IBM manufacturer's profit function is given to find the spending needed for a $40 million profit.
2) Two questions ask to find the value of an expression given log or exponential equations.
3) Three questions involve finding unknown values like populations or expressions in terms of log base 2 of given numbers.
Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]![Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Internet Technologies (October – 2016) [Question Paper | IDOL: Revised Course]
april - 2017, april - 2016, april - 2015, april - 2014, april - 2013, october - 2017, october - 2016, october - 2015, october - 2014, may - 2016, may - 2017, december - 2017, 75:25 pattern, 60:40 pattern, revised course, old course, mumbai bscit study, mumbai university, bscit semester vi, bscit question paper, old question paper, previous year question paper, semester vi question paper, question paper, CBSGS, IDOL, kamal t, internet technology, digital signals and systems, data warehousing, ipr and cyber laws, project management, geographic information system
Cs 68 (p)s1

The document is a past practical examination for a Bachelor of Computer Applications degree from June 2011. It consists of 4 short answer questions worth a total of 20 marks about computer networks topics like network topologies, switch specifications, checking the MAC address, and LAN cable specifications. Students have 2 hours to complete the examination which is worth 15% of the term grade.
Www educationsmaterials-com-2020-12-microprocessor-btech-paper-2020-kanpur-html

This document contains a microprocessor exam for a B.Tech IIIrd year Electronics and Communication Engineering course. The exam contains three sections with multiple choice and descriptive questions. Section A contains 5 short 2-mark questions about microprocessor instructions, bus demultiplexing, and generating square waves. Section B contains 6 longer 3-mark questions about memory interfacing, timing diagrams, registers, 7-segment displays, and arrays. Section C contains 3 even longer 4-mark questions about interrupts, addressing modes, analog to digital conversion, and interrupt controllers. Students are instructed to attempt all questions across the three sections in the allotted three hours.
Mcs 041 assignment solution (2020-21)

Mail us at : help.mbaassignments@gmail.com
Call us at : 08263069601
Dear students, get latest Solved assignments and case study help by professionals.
Coa 

The document discusses pipeline processing and memory organization. It provides definitions and explanations of key concepts related to pipelining such as stages in a pipeline, hazards, and caching. It also covers memory hierarchy concepts like registers, cache, main memory, and secondary storage. Multiple choice questions with answers are provided to test understanding of these topics.
Bca(rev syll ii-sem) assignment for july 2012 and jan 2013 sessionn

This document contains assignments for the second semester of the Bachelor of Computer Applications (BCA) program for the year 2012. It includes assignments for 6 courses - MCS-011 Problem Solving and Programming, MCS-012 Computer Organisation and Assembly Language Programming, MCS-013 Data Structure, MCS-015 Operating System, BCSL-021 Computer Oriented Statistical Techniques, and BCSL-022 Discrete Mathematics. The assignments provide questions to test students' understanding of the course content and must be submitted by October 15th for the July session or April 15th for the January session.
Penn State University School of.docx

This document describes a lab assignment for a computer organization and design course. The goal of the lab is for students to gain experience designing and testing the first four stages of a five-stage pipelined CPU using an FPGA design package. Specifically, students will implement circuits for the instruction fetch, instruction decode, execution, and memory stages. The document provides background on pipelining, describes the circuits for each stage, lists the MIPS registers and sample instructions, and provides instructions for students to design the stages in Verilog and write a report on their work.
Java Thread and Process Performance for Parallel Machine Learning on Multicor...

The growing use of Big Data frameworks on large machines highlights the importance of performance issues and the value of High Performance Computing (HPC) technology. This paper looks carefully at three major frameworks Spark, Flink and Message Passing Interface (MPI) both in scaling across nodes and internally over the many cores inside modern nodes.We focus on the special challenges of the Java Virtual Machine (JVM) using an Intel Haswell HPC cluster with 24 cores per node. Two parallel machine learning algorithms, K-Means clustering and Multidimensional Scaling (MDS) are used in our performance studies. We identify three major issues – thread models, affinity patterns, and communication mechanisms – as factors affecting performance by large factors and show how to optimize them so that Java can match the performance of traditional HPC languages like C. Further we suggest approaches that preserve the user interface and elegant dataflow approach of Flink and Spark but modify the runtime so that these Big Data frameworks can achieve excellent performance and realize the goals of HPCBig Data convergence.
Available HPC resources at CSUC

The document summarizes available HPC resources at CSUC, including hardware facilities, the working environment, development tools, and how to access services. The main systems are Canigó with 384 cores and 33 TFlops peak performance, and Pirineus II with 2,688 cores and 284 TFlops. Resources are managed by Slurm and available partitions include standard, GPU, and Intel KNL nodes. Users can access resources through RES projects or by purchasing compute units.
IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx

IFSM 310 Software and Hardware Infrastructure Concepts
Computer and Number Systems
1.
(10 pt)
You have been hired to develop a website-based sales system for a large international retail firm. List and describe at least four features that are specific to the Web design of your system and customer service important to consider if your system is to be successful at attracting and keeping customers living outside of the US. Include not only characteristics of the user interface, but those issues that must be uniquely addressed to successfully service your non-US customers.
2.
(2.5 pt each)
In order to receive credit for these problems, you must show all of the steps you took to arrive at your answers.
(c) Convert the following decimal number to binary:
21842
(d) Convert the following binary number to decimal:
11000111011.101
(c) Convert the following hexadecimal number to decimal:
CA97
(d) Convert the following binary number to hexadecimal:
1110011111011010100
CPU and Memory
3.
(10 pt)
ASCII, Unicode, and EBCDIC are, of course, not the only numeric / character codes. The Sophomites from the planet Collegium use the rather strange code shown in the Figure below. There are only thirteen characters in the Sophomite alphabet, and each character uses a 5-bit code. In addition, there are four numeric digits, since the Sophomites use base 4 for their arithmetic. Given the following Sophomite sequence, what is the corresponding binary message being sent by the Sophomites?
(HINT: Decode the sequence reading from left to right then write the corresponding binary sequence, leaving a space between each binary sequence.)
4.
(10 pt)
Define memory cache write-through and write-back techniques and describe the advantages and disadvantages of each.
Input / Output
5. Answer the follow questions about interrupts.
a.
(5 pt)
Describe in detail the steps that occur when a system receives an interrupt.
b.
(5 pt)
Describe how these steps differ in the case when a system receives multiple interrupts
Computer Systems
6. Answer the following questions about clusters.
a.
(5 pt)
Describe how you might use a cluster to provide fault-tolerant computing
b.
(5 pt)
Describe how you might use a cluster architecture to provide rapid scalability for a Web-based company experiencing rapid growth.
Networks
7. Answer the following questions about communication protocols.
a.
(5 pt)
Using the operations of UDP (User Datagram Protocol) and TCP (Transmission Control Protocol) as a basis, carefully explain the difference between connectionless and connection-oriented communication.
b.
(5 pt)
If you were ordering a number of items from an online seller, such as amazon.com, which Protocol (TCP or UDP) would you recommend and explain why
.
8. In the context of network security,
a.
(3 pt)
exp.
Ec6504 microprocessor and microcontroller

This document provides information about the 8086 microprocessor architecture. It describes how the 8086 CPU is divided into two units: the Bus Interface Unit (BIU) and the Execution Unit (EU). The BIU handles data and address transfers between memory and I/O, while the EU decodes instructions and performs operations. The 8086 uses a queue to prefetch and store up to 6 instruction bytes to improve performance. It can perform 16-bit word reads from memory in one operation if the data is stored at an even address, but requires two operations for odd addresses.
D I G I T A L I C A P P L I C A T I O N S J N T U M O D E L P A P E R{Www

This document contains eight questions related to digital integrated circuits and applications. The questions cover topics such as CMOS and TTL gates, VHDL programming, counters, decoders, arithmetic circuits, memories and programmable logic devices. Students are instructed to answer any five of the eight questions, which can include circuit design problems, writing VHDL code using different styles, and analyzing and explaining the operation of digital components.
Digital Ic Applications Jntu Model Paper{Www.Studentyogi.Com}

This document contains eight questions related to digital integrated circuits and applications. The questions cover topics such as CMOS and TTL gates, VHDL programming, counters, decoders, arithmetic circuits, memories and programmable logic devices. Students are instructed to answer any five of the eight questions, which can include circuit design problems, writing VHDL code, explaining concepts, and performing calculations. The exam is worth a total of 80 marks and is aimed at testing knowledge of digital logic design and implementation using integrated circuits.
Tute

This document contains 9 tutorials related to the subject of Advanced Computer Architecture for a BTech course at M.M.M. Engineering College in Gorakhpur, India during the 2007-2008 session. Each tutorial contains 2 questions related to topics such as instruction set architecture, performance analysis, parallelization, pipelining, multiprocessing, parallel algorithms and synchronization techniques.
7th Semester (June; July-2015) Computer Science and Information Science Engin...

7th Semester (June; July-2015) Computer Science and Information Science Engin...BGS Institute of Technology, Adichunchanagiri University (ACU)
This document contains 8 questions that are part of an examination for a 7th semester computer engineering course covering Java and JEE technologies. It provides instructions to answer 5 full questions out of the 8, with at least 2 questions from each part (A and B).
Part A covers core Java concepts like object-oriented programming, applets, events, AWT vs Swing, and GUI components. Part B focuses on more advanced Java EE topics such as JDBC, transactions, servlets, cookies, sessions, JSP, and RMI. Students are asked to explain, define, write examples, and compare/contrast various Java and Java EE programming concepts and technologies.Matrix transposition

1) The document presents various algorithms for efficiently transposing matrices while minimizing memory accesses and cache misses.
2) It analyzes the algorithms under different memory models: RAM, I/O, cache, and cache-oblivious. The block transpose, half/full copying, and Morton layout algorithms improve performance by reusing data blocks.
3) Experimental results on a 300MHz system show the Morton layout and half copying algorithms have the fastest runtimes due to minimizing data references, L1 misses, and TLB misses. The relative performance of algorithms depends on cache miss latency.
Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]![Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]
bscit question paper, bscit semester vi, c#, cbsgs, customer relations management, geographic information systems, idol, idol - revised course, internet technologies, it laws and patents, kamal t, may - 2018, mumbai bscit study, mumbai university, old question paper, previous year question paper, project management, question paper, semester vi question paper, strategic it management, Internet Technologies, Digital Signals and Systems, Data Warehousing, Project Management
MaPU-HPCA2016

The document describes the development and testing of a novel mathematical computing architecture called MaPU. Key highlights include a multi-granularity parallel storage system that enables simultaneous matrix row and column access, a high dimension data model, and a cascading pipeline with a state machine-based program model. The first MaPU chip was implemented on a 40nm process with 4 MaPU cores. Testing showed the MaPU core was up to 6.94 times faster than a similar TI C66x DSP core for various algorithms like FFT and matrix multiplication. Power analysis indicated tested power was within 8% of estimated power.
CS 6402 – DESIGN AND ANALYSIS OF ALGORITHMS questio

This document contains a past exam paper for the subject "Design and Analysis of Algorithms". It has 2 parts with a total of 15 questions. Part A covers basic algorithm concepts like recurrence relations, efficiency classes, minimum spanning trees, and more. Part B involves solving algorithm problems using techniques like dynamic programming, Huffman coding, shortest paths, and more. It also tests concepts like P vs NP, approximation algorithms, and analysis of algorithm efficiency.
Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]![Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
,mumbai bscit study ,kamal t ,mumbai university ,old question paper ,previous year question paper ,bscit question paper ,bscit semester ii ,semester ii question paper ,internet technology ,75:25 pattern ,revised syllabus ,question paper ,april – 2017 ,object oriented programming ,microprocessor architecture ,web programming ,numerical and statistical methods ,green computing
COMMONWEALTH OF AUSTRALIACopyright Regulations 1969

COMMONWEALTH OF AUSTRALIA
Copyright Regulations 1969
Warning
This material has been reproduced and communicated to you by or on behalf of The Charles Darwin University pursuant to Part VB of the Copyright Act 1968 (the Act). The material in this communication may be subject to copyright under the Act. Any further reproduction or communication of this material by you may be the subject of copyright protection under the Act.
Do not remove this notice
(
Semester 2, 2016
FINAL EXAMINATION
DURATION
HIT274 – Network Engineering Applications
Teaching Period
Student Number
Given Names
Family Name
Reading
Time:
10
minutes
Writing
Time:
180
minutes
)
INSTRUCTIONS TO CANDIDATES
The examination has 3 sections
Section A:
Suggested Time:
Multiple Choice Questions: Answer ALL questions
45 minutes (30 marks)
Section B:
Suggested Time:
Short Answer Questions: Answer ALL questions
95 minutes (50 marks)
Section B:
Suggested Time:
Case Study: Answer ALL questions
40 minutes (20 marks)
Questions in section A must be answered directly onto the Examination Paper. Section B and C are to be answered in the booklets provided.
Note that questions ARE NOT of equal value.
EXAM CONDITIONS
You may begin writing from the commencement of the examination session.The reading time indicated above is provided as a guide only.
This is a CLOSED BOOK examination No calculators are permitted
No handwritten notes are permitted No dictionaries are permitted
ADDITIONAL AUTHORISED MATERIALS
EXAMINATION MATERIALS TO BE SUPPLIED
No additional printed material is permitted
1 x 16 Page Book 1 x Scrap Paper
(
THIS EXAMINATION PAPER AND SUPPLIED MATERIALS ARE NOT PERMITTED TO BE REMOVED FROM ANY EXAMINATION VENUE IN ANY CIRCUMSTANCE. THIS EXAMINATION IS PRINTED DOUBLE-SIDED.
)
Semester 2, 2016 FINAL EXAMINATION
HIT274 – Network Engineering Applications
Page 1 of 10
THIS EXAMINATION IS PRINTED DOUBLE-SIDED.
THIS PAGE HAS BEEN INTENTIONALLY LEFT BLANK.
Semester 2, 2016 FINAL EXAMINATION
HIT274 – Network Engineering Applications
Page 2 of 10
Section A Multiple Choice QuestionsTotal No of Marks for this section: 30
This section should be answered directly into this booklet by placing an X next to your chosen answers. Please ensure that your name and student number have been written on this booklet.
Each question is worth 1 mark.
Suggested Time allocation for Section A: 45 mins
Semester 2, 2016 FINAL EXAMINATION
HIT274 – Network Engineering Applications
Page 3 of 10
Section B
Short Answer QuestionsTotal No of Marks for this section: 50
This section should be answered in the Answer Booklet provided.
Marks for each question are indicated.
Suggested Time allocation for Section B: 95 mins
Question 1
Complete the table below:
Full IPv6
Abbreviated IPv6
a
FE80:0000:0000:0400:0000:0000:0000:054A
fe80:0:0:400::54a
b
4:b200:80:f0a:5000:c:885:a000
4:B200:80:F0A:5000:C:885:A000
c
0C0 ...
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers concepts like cache hits, misses, block size, direct mapping, set associativity, compulsory misses, capacity misses, and conflict misses. Finally, it discusses using a second level cache to reduce memory access times by capturing misses from the first level cache.
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers concepts like cache hits, misses, block size, direct mapping, set associativity, compulsory misses, capacity misses, and conflict misses. Finally, it discusses using a second-level cache to reduce memory access times by capturing misses from the first-level cache.
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers concepts like cache hits, misses, block size, direct mapping, set associativity, compulsory misses, capacity misses, and conflict misses. It also discusses techniques for improving cache performance like multi-level caches, write buffers, increasing associativity, and interleaving memory banks.
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers topics like direct mapped caches, set associative caches, cache hits and misses, reducing miss penalties through multiple cache levels, and analyzing cache performance. Key goals in memory hierarchy design are reducing miss rates through techniques like larger blocks, higher associativity, and reducing miss penalties with lower level caches.
Cache recap

The document discusses memory hierarchy and cache performance. It introduces the concept of memory hierarchy to get the best of fast and large memories. It then discusses different memory technologies like SRAM, DRAM and disk and their access times. It explains the basic concepts of direct mapped cache, cache hits, misses and different ways to reduce miss penalties like using multiple cache levels. Finally, it classifies cache misses into compulsory, capacity and conflict misses and how these are affected based on cache parameters.
Cache recap

The document discusses memory hierarchy and cache performance. It introduces the concepts of memory hierarchy, cache hits, misses, and different types of cache organizations like direct mapped, set associative, and fully associative caches. It analyzes how cache performance is affected by miss rate, miss penalty, block size, cache size, and associativity. Adding a second level cache can help reduce the miss penalty and improve overall performance.
New techniques for characterising damage in rock slopes.pdf

rock mass characterization and New techniques for characterising damage in rock slopes
More Related Content
Similar to Www educationsmaterials-com-2020-12-uiet-csjm-university-microprocessor-ece-html
Java Thread and Process Performance for Parallel Machine Learning on Multicor...

The growing use of Big Data frameworks on large machines highlights the importance of performance issues and the value of High Performance Computing (HPC) technology. This paper looks carefully at three major frameworks Spark, Flink and Message Passing Interface (MPI) both in scaling across nodes and internally over the many cores inside modern nodes.We focus on the special challenges of the Java Virtual Machine (JVM) using an Intel Haswell HPC cluster with 24 cores per node. Two parallel machine learning algorithms, K-Means clustering and Multidimensional Scaling (MDS) are used in our performance studies. We identify three major issues – thread models, affinity patterns, and communication mechanisms – as factors affecting performance by large factors and show how to optimize them so that Java can match the performance of traditional HPC languages like C. Further we suggest approaches that preserve the user interface and elegant dataflow approach of Flink and Spark but modify the runtime so that these Big Data frameworks can achieve excellent performance and realize the goals of HPCBig Data convergence.
Available HPC resources at CSUC

The document summarizes available HPC resources at CSUC, including hardware facilities, the working environment, development tools, and how to access services. The main systems are Canigó with 384 cores and 33 TFlops peak performance, and Pirineus II with 2,688 cores and 284 TFlops. Resources are managed by Slurm and available partitions include standard, GPU, and Intel KNL nodes. Users can access resources through RES projects or by purchasing compute units.
IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx

IFSM 310 Software and Hardware Infrastructure Concepts
Computer and Number Systems
1.
(10 pt)
You have been hired to develop a website-based sales system for a large international retail firm. List and describe at least four features that are specific to the Web design of your system and customer service important to consider if your system is to be successful at attracting and keeping customers living outside of the US. Include not only characteristics of the user interface, but those issues that must be uniquely addressed to successfully service your non-US customers.
2.
(2.5 pt each)
In order to receive credit for these problems, you must show all of the steps you took to arrive at your answers.
(c) Convert the following decimal number to binary:
21842
(d) Convert the following binary number to decimal:
11000111011.101
(c) Convert the following hexadecimal number to decimal:
CA97
(d) Convert the following binary number to hexadecimal:
1110011111011010100
CPU and Memory
3.
(10 pt)
ASCII, Unicode, and EBCDIC are, of course, not the only numeric / character codes. The Sophomites from the planet Collegium use the rather strange code shown in the Figure below. There are only thirteen characters in the Sophomite alphabet, and each character uses a 5-bit code. In addition, there are four numeric digits, since the Sophomites use base 4 for their arithmetic. Given the following Sophomite sequence, what is the corresponding binary message being sent by the Sophomites?
(HINT: Decode the sequence reading from left to right then write the corresponding binary sequence, leaving a space between each binary sequence.)
4.
(10 pt)
Define memory cache write-through and write-back techniques and describe the advantages and disadvantages of each.
Input / Output
5. Answer the follow questions about interrupts.
a.
(5 pt)
Describe in detail the steps that occur when a system receives an interrupt.
b.
(5 pt)
Describe how these steps differ in the case when a system receives multiple interrupts
Computer Systems
6. Answer the following questions about clusters.
a.
(5 pt)
Describe how you might use a cluster to provide fault-tolerant computing
b.
(5 pt)
Describe how you might use a cluster architecture to provide rapid scalability for a Web-based company experiencing rapid growth.
Networks
7. Answer the following questions about communication protocols.
a.
(5 pt)
Using the operations of UDP (User Datagram Protocol) and TCP (Transmission Control Protocol) as a basis, carefully explain the difference between connectionless and connection-oriented communication.
b.
(5 pt)
If you were ordering a number of items from an online seller, such as amazon.com, which Protocol (TCP or UDP) would you recommend and explain why
.
8. In the context of network security,
a.
(3 pt)
exp.
Ec6504 microprocessor and microcontroller

This document provides information about the 8086 microprocessor architecture. It describes how the 8086 CPU is divided into two units: the Bus Interface Unit (BIU) and the Execution Unit (EU). The BIU handles data and address transfers between memory and I/O, while the EU decodes instructions and performs operations. The 8086 uses a queue to prefetch and store up to 6 instruction bytes to improve performance. It can perform 16-bit word reads from memory in one operation if the data is stored at an even address, but requires two operations for odd addresses.
D I G I T A L I C A P P L I C A T I O N S J N T U M O D E L P A P E R{Www

This document contains eight questions related to digital integrated circuits and applications. The questions cover topics such as CMOS and TTL gates, VHDL programming, counters, decoders, arithmetic circuits, memories and programmable logic devices. Students are instructed to answer any five of the eight questions, which can include circuit design problems, writing VHDL code using different styles, and analyzing and explaining the operation of digital components.
Digital Ic Applications Jntu Model Paper{Www.Studentyogi.Com}

This document contains eight questions related to digital integrated circuits and applications. The questions cover topics such as CMOS and TTL gates, VHDL programming, counters, decoders, arithmetic circuits, memories and programmable logic devices. Students are instructed to answer any five of the eight questions, which can include circuit design problems, writing VHDL code, explaining concepts, and performing calculations. The exam is worth a total of 80 marks and is aimed at testing knowledge of digital logic design and implementation using integrated circuits.
Tute

This document contains 9 tutorials related to the subject of Advanced Computer Architecture for a BTech course at M.M.M. Engineering College in Gorakhpur, India during the 2007-2008 session. Each tutorial contains 2 questions related to topics such as instruction set architecture, performance analysis, parallelization, pipelining, multiprocessing, parallel algorithms and synchronization techniques.
7th Semester (June; July-2015) Computer Science and Information Science Engin...

7th Semester (June; July-2015) Computer Science and Information Science Engin...BGS Institute of Technology, Adichunchanagiri University (ACU)
This document contains 8 questions that are part of an examination for a 7th semester computer engineering course covering Java and JEE technologies. It provides instructions to answer 5 full questions out of the 8, with at least 2 questions from each part (A and B).
Part A covers core Java concepts like object-oriented programming, applets, events, AWT vs Swing, and GUI components. Part B focuses on more advanced Java EE topics such as JDBC, transactions, servlets, cookies, sessions, JSP, and RMI. Students are asked to explain, define, write examples, and compare/contrast various Java and Java EE programming concepts and technologies.Matrix transposition

1) The document presents various algorithms for efficiently transposing matrices while minimizing memory accesses and cache misses.
2) It analyzes the algorithms under different memory models: RAM, I/O, cache, and cache-oblivious. The block transpose, half/full copying, and Morton layout algorithms improve performance by reusing data blocks.
3) Experimental results on a 300MHz system show the Morton layout and half copying algorithms have the fastest runtimes due to minimizing data references, L1 misses, and TLB misses. The relative performance of algorithms depends on cache miss latency.
Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]![Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]
bscit question paper, bscit semester vi, c#, cbsgs, customer relations management, geographic information systems, idol, idol - revised course, internet technologies, it laws and patents, kamal t, may - 2018, mumbai bscit study, mumbai university, old question paper, previous year question paper, project management, question paper, semester vi question paper, strategic it management, Internet Technologies, Digital Signals and Systems, Data Warehousing, Project Management
MaPU-HPCA2016

The document describes the development and testing of a novel mathematical computing architecture called MaPU. Key highlights include a multi-granularity parallel storage system that enables simultaneous matrix row and column access, a high dimension data model, and a cascading pipeline with a state machine-based program model. The first MaPU chip was implemented on a 40nm process with 4 MaPU cores. Testing showed the MaPU core was up to 6.94 times faster than a similar TI C66x DSP core for various algorithms like FFT and matrix multiplication. Power analysis indicated tested power was within 8% of estimated power.
CS 6402 – DESIGN AND ANALYSIS OF ALGORITHMS questio

This document contains a past exam paper for the subject "Design and Analysis of Algorithms". It has 2 parts with a total of 15 questions. Part A covers basic algorithm concepts like recurrence relations, efficiency classes, minimum spanning trees, and more. Part B involves solving algorithm problems using techniques like dynamic programming, Huffman coding, shortest paths, and more. It also tests concepts like P vs NP, approximation algorithms, and analysis of algorithm efficiency.
Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]![Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
,mumbai bscit study ,kamal t ,mumbai university ,old question paper ,previous year question paper ,bscit question paper ,bscit semester ii ,semester ii question paper ,internet technology ,75:25 pattern ,revised syllabus ,question paper ,april – 2017 ,object oriented programming ,microprocessor architecture ,web programming ,numerical and statistical methods ,green computing
COMMONWEALTH OF AUSTRALIACopyright Regulations 1969

COMMONWEALTH OF AUSTRALIA
Copyright Regulations 1969
Warning
This material has been reproduced and communicated to you by or on behalf of The Charles Darwin University pursuant to Part VB of the Copyright Act 1968 (the Act). The material in this communication may be subject to copyright under the Act. Any further reproduction or communication of this material by you may be the subject of copyright protection under the Act.
Do not remove this notice
(
Semester 2, 2016
FINAL EXAMINATION
DURATION
HIT274 – Network Engineering Applications
Teaching Period
Student Number
Given Names
Family Name
Reading
Time:
10
minutes
Writing
Time:
180
minutes
)
INSTRUCTIONS TO CANDIDATES
The examination has 3 sections
Section A:
Suggested Time:
Multiple Choice Questions: Answer ALL questions
45 minutes (30 marks)
Section B:
Suggested Time:
Short Answer Questions: Answer ALL questions
95 minutes (50 marks)
Section B:
Suggested Time:
Case Study: Answer ALL questions
40 minutes (20 marks)
Questions in section A must be answered directly onto the Examination Paper. Section B and C are to be answered in the booklets provided.
Note that questions ARE NOT of equal value.
EXAM CONDITIONS
You may begin writing from the commencement of the examination session.The reading time indicated above is provided as a guide only.
This is a CLOSED BOOK examination No calculators are permitted
No handwritten notes are permitted No dictionaries are permitted
ADDITIONAL AUTHORISED MATERIALS
EXAMINATION MATERIALS TO BE SUPPLIED
No additional printed material is permitted
1 x 16 Page Book 1 x Scrap Paper
(
THIS EXAMINATION PAPER AND SUPPLIED MATERIALS ARE NOT PERMITTED TO BE REMOVED FROM ANY EXAMINATION VENUE IN ANY CIRCUMSTANCE. THIS EXAMINATION IS PRINTED DOUBLE-SIDED.
)
Semester 2, 2016 FINAL EXAMINATION
HIT274 – Network Engineering Applications
Page 1 of 10
THIS EXAMINATION IS PRINTED DOUBLE-SIDED.
THIS PAGE HAS BEEN INTENTIONALLY LEFT BLANK.
Semester 2, 2016 FINAL EXAMINATION
HIT274 – Network Engineering Applications
Page 2 of 10
Section A Multiple Choice QuestionsTotal No of Marks for this section: 30
This section should be answered directly into this booklet by placing an X next to your chosen answers. Please ensure that your name and student number have been written on this booklet.
Each question is worth 1 mark.
Suggested Time allocation for Section A: 45 mins
Semester 2, 2016 FINAL EXAMINATION
HIT274 – Network Engineering Applications
Page 3 of 10
Section B
Short Answer QuestionsTotal No of Marks for this section: 50
This section should be answered in the Answer Booklet provided.
Marks for each question are indicated.
Suggested Time allocation for Section B: 95 mins
Question 1
Complete the table below:
Full IPv6
Abbreviated IPv6
a
FE80:0000:0000:0400:0000:0000:0000:054A
fe80:0:0:400::54a
b
4:b200:80:f0a:5000:c:885:a000
4:B200:80:F0A:5000:C:885:A000
c
0C0 ...
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers concepts like cache hits, misses, block size, direct mapping, set associativity, compulsory misses, capacity misses, and conflict misses. Finally, it discusses using a second level cache to reduce memory access times by capturing misses from the first level cache.
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers concepts like cache hits, misses, block size, direct mapping, set associativity, compulsory misses, capacity misses, and conflict misses. Finally, it discusses using a second-level cache to reduce memory access times by capturing misses from the first-level cache.
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers concepts like cache hits, misses, block size, direct mapping, set associativity, compulsory misses, capacity misses, and conflict misses. It also discusses techniques for improving cache performance like multi-level caches, write buffers, increasing associativity, and interleaving memory banks.
Cache recap

The document discusses memory hierarchy and caching techniques. It begins by explaining the need for a memory hierarchy due to differing access times of memory technologies like SRAM, DRAM, and disk. It then covers topics like direct mapped caches, set associative caches, cache hits and misses, reducing miss penalties through multiple cache levels, and analyzing cache performance. Key goals in memory hierarchy design are reducing miss rates through techniques like larger blocks, higher associativity, and reducing miss penalties with lower level caches.
Cache recap

The document discusses memory hierarchy and cache performance. It introduces the concept of memory hierarchy to get the best of fast and large memories. It then discusses different memory technologies like SRAM, DRAM and disk and their access times. It explains the basic concepts of direct mapped cache, cache hits, misses and different ways to reduce miss penalties like using multiple cache levels. Finally, it classifies cache misses into compulsory, capacity and conflict misses and how these are affected based on cache parameters.
Cache recap

The document discusses memory hierarchy and cache performance. It introduces the concepts of memory hierarchy, cache hits, misses, and different types of cache organizations like direct mapped, set associative, and fully associative caches. It analyzes how cache performance is affected by miss rate, miss penalty, block size, cache size, and associativity. Adding a second level cache can help reduce the miss penalty and improve overall performance.
Similar to Www educationsmaterials-com-2020-12-uiet-csjm-university-microprocessor-ece-html (20)
Java Thread and Process Performance for Parallel Machine Learning on Multicor...

Java Thread and Process Performance for Parallel Machine Learning on Multicor...
IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx

IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx
D I G I T A L I C A P P L I C A T I O N S J N T U M O D E L P A P E R{Www

D I G I T A L I C A P P L I C A T I O N S J N T U M O D E L P A P E R{Www
Digital Ic Applications Jntu Model Paper{Www.Studentyogi.Com}

Digital Ic Applications Jntu Model Paper{Www.Studentyogi.Com}
7th Semester (June; July-2015) Computer Science and Information Science Engin...

7th Semester (June; July-2015) Computer Science and Information Science Engin...
Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]![Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Internet Technologies (May - 2018) [IDOL - Revised Course | Question Paper]
CS 6402 – DESIGN AND ANALYSIS OF ALGORITHMS questio

CS 6402 – DESIGN AND ANALYSIS OF ALGORITHMS questio
Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]![Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Microprocessor Architecture (Question Paper) [April – 2017 | 75:25 Pattern]
COMMONWEALTH OF AUSTRALIACopyright Regulations 1969

COMMONWEALTH OF AUSTRALIACopyright Regulations 1969
Recently uploaded
New techniques for characterising damage in rock slopes.pdf

rock mass characterization and New techniques for characterising damage in rock slopes
Comparative analysis between traditional aquaponics and reconstructed aquapon...

The aquaponic system of planting is a method that does not require soil usage. It is a method that only needs water, fish, lava rocks (a substitute for soil), and plants. Aquaponic systems are sustainable and environmentally friendly. Its use not only helps to plant in small spaces but also helps reduce artificial chemical use and minimizes excess water use, as aquaponics consumes 90% less water than soil-based gardening. The study applied a descriptive and experimental design to assess and compare conventional and reconstructed aquaponic methods for reproducing tomatoes. The researchers created an observation checklist to determine the significant factors of the study. The study aims to determine the significant difference between traditional aquaponics and reconstructed aquaponics systems propagating tomatoes in terms of height, weight, girth, and number of fruits. The reconstructed aquaponics system’s higher growth yield results in a much more nourished crop than the traditional aquaponics system. It is superior in its number of fruits, height, weight, and girth measurement. Moreover, the reconstructed aquaponics system is proven to eliminate all the hindrances present in the traditional aquaponics system, which are overcrowding of fish, algae growth, pest problems, contaminated water, and dead fish.
International Conference on NLP, Artificial Intelligence, Machine Learning an...

International Conference on NLP, Artificial Intelligence, Machine Learning and Applications (NLAIM 2024) offers a premier global platform for exchanging insights and findings in the theory, methodology, and applications of NLP, Artificial Intelligence, Machine Learning, and their applications. The conference seeks substantial contributions across all key domains of NLP, Artificial Intelligence, Machine Learning, and their practical applications, aiming to foster both theoretical advancements and real-world implementations. With a focus on facilitating collaboration between researchers and practitioners from academia and industry, the conference serves as a nexus for sharing the latest developments in the field.
5214-1693458878915-Unit 6 2023 to 2024 academic year assignment (AutoRecovere...

Bigdata of technology
The Python for beginners. This is an advance computer language.

Python language is very important language at this time. we can easily understand this language by these notes.
Redefining brain tumor segmentation: a cutting-edge convolutional neural netw...

Medical image analysis has witnessed significant advancements with deep learning techniques. In the domain of brain tumor segmentation, the ability to
precisely delineate tumor boundaries from magnetic resonance imaging (MRI)
scans holds profound implications for diagnosis. This study presents an ensemble convolutional neural network (CNN) with transfer learning, integrating
the state-of-the-art Deeplabv3+ architecture with the ResNet18 backbone. The
model is rigorously trained and evaluated, exhibiting remarkable performance
metrics, including an impressive global accuracy of 99.286%, a high-class accuracy of 82.191%, a mean intersection over union (IoU) of 79.900%, a weighted
IoU of 98.620%, and a Boundary F1 (BF) score of 83.303%. Notably, a detailed comparative analysis with existing methods showcases the superiority of
our proposed model. These findings underscore the model’s competence in precise brain tumor localization, underscoring its potential to revolutionize medical
image analysis and enhance healthcare outcomes. This research paves the way
for future exploration and optimization of advanced CNN models in medical
imaging, emphasizing addressing false positives and resource efficiency.
A SYSTEMATIC RISK ASSESSMENT APPROACH FOR SECURING THE SMART IRRIGATION SYSTEMS

The smart irrigation system represents an innovative approach to optimize water usage in agricultural and landscaping practices. The integration of cutting-edge technologies, including sensors, actuators, and data analysis, empowers this system to provide accurate monitoring and control of irrigation processes by leveraging real-time environmental conditions. The main objective of a smart irrigation system is to optimize water efficiency, minimize expenses, and foster the adoption of sustainable water management methods. This paper conducts a systematic risk assessment by exploring the key components/assets and their functionalities in the smart irrigation system. The crucial role of sensors in gathering data on soil moisture, weather patterns, and plant well-being is emphasized in this system. These sensors enable intelligent decision-making in irrigation scheduling and water distribution, leading to enhanced water efficiency and sustainable water management practices. Actuators enable automated control of irrigation devices, ensuring precise and targeted water delivery to plants. Additionally, the paper addresses the potential threat and vulnerabilities associated with smart irrigation systems. It discusses limitations of the system, such as power constraints and computational capabilities, and calculates the potential security risks. The paper suggests possible risk treatment methods for effective secure system operation. In conclusion, the paper emphasizes the significant benefits of implementing smart irrigation systems, including improved water conservation, increased crop yield, and reduced environmental impact. Additionally, based on the security analysis conducted, the paper recommends the implementation of countermeasures and security approaches to address vulnerabilities and ensure the integrity and reliability of the system. By incorporating these measures, smart irrigation technology can revolutionize water management practices in agriculture, promoting sustainability, resource efficiency, and safeguarding against potential security threats.
TIME DIVISION MULTIPLEXING TECHNIQUE FOR COMMUNICATION SYSTEM

Time Division Multiplexing (TDM) is a method of transmitting multiple signals over a single communication channel by dividing the signal into many segments, each having a very short duration of time. These time slots are then allocated to different data streams, allowing multiple signals to share the same transmission medium efficiently. TDM is widely used in telecommunications and data communication systems.
### How TDM Works
1. **Time Slots Allocation**: The core principle of TDM is to assign distinct time slots to each signal. During each time slot, the respective signal is transmitted, and then the process repeats cyclically. For example, if there are four signals to be transmitted, the TDM cycle will divide time into four slots, each assigned to one signal.
2. **Synchronization**: Synchronization is crucial in TDM systems to ensure that the signals are correctly aligned with their respective time slots. Both the transmitter and receiver must be synchronized to avoid any overlap or loss of data. This synchronization is typically maintained by a clock signal that ensures time slots are accurately aligned.
3. **Frame Structure**: TDM data is organized into frames, where each frame consists of a set of time slots. Each frame is repeated at regular intervals, ensuring continuous transmission of data streams. The frame structure helps in managing the data streams and maintaining the synchronization between the transmitter and receiver.
4. **Multiplexer and Demultiplexer**: At the transmitting end, a multiplexer combines multiple input signals into a single composite signal by assigning each signal to a specific time slot. At the receiving end, a demultiplexer separates the composite signal back into individual signals based on their respective time slots.
### Types of TDM
1. **Synchronous TDM**: In synchronous TDM, time slots are pre-assigned to each signal, regardless of whether the signal has data to transmit or not. This can lead to inefficiencies if some time slots remain empty due to the absence of data.
2. **Asynchronous TDM (or Statistical TDM)**: Asynchronous TDM addresses the inefficiencies of synchronous TDM by allocating time slots dynamically based on the presence of data. Time slots are assigned only when there is data to transmit, which optimizes the use of the communication channel.
### Applications of TDM
- **Telecommunications**: TDM is extensively used in telecommunication systems, such as in T1 and E1 lines, where multiple telephone calls are transmitted over a single line by assigning each call to a specific time slot.
- **Digital Audio and Video Broadcasting**: TDM is used in broadcasting systems to transmit multiple audio or video streams over a single channel, ensuring efficient use of bandwidth.
- **Computer Networks**: TDM is used in network protocols and systems to manage the transmission of data from multiple sources over a single network medium.
### Advantages of TDM
- **Efficient Use of Bandwidth**: TDM all
Optimizing Gradle Builds - Gradle DPE Tour Berlin 2024

Sinan from the Delivery Hero mobile infrastructure engineering team shares a deep dive into performance acceleration with Gradle build cache optimizations. Sinan shares their journey into solving complex build-cache problems that affect Gradle builds. By understanding the challenges and solutions found in our journey, we aim to demonstrate the possibilities for faster builds. The case study reveals how overlapping outputs and cache misconfigurations led to significant increases in build times, especially as the project scaled up with numerous modules using Paparazzi tests. The journey from diagnosing to defeating cache issues offers invaluable lessons on maintaining cache integrity without sacrificing functionality.
ISPM 15 Heat Treated Wood Stamps and why your shipping must have one

For International shipping and maritime laws all wood must contain the ISPM 15 Stamp. Here is how and why.
Computational Engineering IITH Presentation

This Presentation will give you a brief idea about what Computational Engineering at IIT Hyderabad has to offer.
Presentation of IEEE Slovenia CIS (Computational Intelligence Society) Chapte...

Presentation of IEEE Slovenia CIS (Computational Intelligence Society) Chapte...University of Maribor
Slides from talk presenting:
Aleš Zamuda: Presentation of IEEE Slovenia CIS (Computational Intelligence Society) Chapter and Networking.
Presentation at IcETRAN 2024 session:
"Inter-Society Networking Panel GRSS/MTT-S/CIS
Panel Session: Promoting Connection and Cooperation"
IEEE Slovenia GRSS
IEEE Serbia and Montenegro MTT-S
IEEE Slovenia CIS
11TH INTERNATIONAL CONFERENCE ON ELECTRICAL, ELECTRONIC AND COMPUTING ENGINEERING
3-6 June 2024, Niš, Serbia官方认证美国密歇根州立大学毕业证学位证书原版一模一样

原版一模一样【微信:741003700 】【美国密歇根州立大学毕业证学位证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Modelagem de um CSTR com reação endotermica.pdf

Modelagem em função de transferencia. CSTR não-linear.
学校原版美国波士顿大学毕业证学历学位证书原版一模一样

原版一模一样【微信:741003700 】【美国波士顿大学毕业证学历学位证书】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Electric vehicle and photovoltaic advanced roles in enhancing the financial p...

Climate change's impact on the planet forced the United Nations and governments to promote green energies and electric transportation. The deployments of photovoltaic (PV) and electric vehicle (EV) systems gained stronger momentum due to their numerous advantages over fossil fuel types. The advantages go beyond sustainability to reach financial support and stability. The work in this paper introduces the hybrid system between PV and EV to support industrial and commercial plants. This paper covers the theoretical framework of the proposed hybrid system including the required equation to complete the cost analysis when PV and EV are present. In addition, the proposed design diagram which sets the priorities and requirements of the system is presented. The proposed approach allows setup to advance their power stability, especially during power outages. The presented information supports researchers and plant owners to complete the necessary analysis while promoting the deployment of clean energy. The result of a case study that represents a dairy milk farmer supports the theoretical works and highlights its advanced benefits to existing plants. The short return on investment of the proposed approach supports the paper's novelty approach for the sustainable electrical system. In addition, the proposed system allows for an isolated power setup without the need for a transmission line which enhances the safety of the electrical network
Recently uploaded (20)
New techniques for characterising damage in rock slopes.pdf

New techniques for characterising damage in rock slopes.pdf
Comparative analysis between traditional aquaponics and reconstructed aquapon...

Comparative analysis between traditional aquaponics and reconstructed aquapon...
ML Based Model for NIDS MSc Updated Presentation.v2.pptx

ML Based Model for NIDS MSc Updated Presentation.v2.pptx
International Conference on NLP, Artificial Intelligence, Machine Learning an...

International Conference on NLP, Artificial Intelligence, Machine Learning an...
5214-1693458878915-Unit 6 2023 to 2024 academic year assignment (AutoRecovere...

5214-1693458878915-Unit 6 2023 to 2024 academic year assignment (AutoRecovere...
The Python for beginners. This is an advance computer language.

The Python for beginners. This is an advance computer language.
Redefining brain tumor segmentation: a cutting-edge convolutional neural netw...

Redefining brain tumor segmentation: a cutting-edge convolutional neural netw...
A SYSTEMATIC RISK ASSESSMENT APPROACH FOR SECURING THE SMART IRRIGATION SYSTEMS

A SYSTEMATIC RISK ASSESSMENT APPROACH FOR SECURING THE SMART IRRIGATION SYSTEMS
TIME DIVISION MULTIPLEXING TECHNIQUE FOR COMMUNICATION SYSTEM

TIME DIVISION MULTIPLEXING TECHNIQUE FOR COMMUNICATION SYSTEM
Optimizing Gradle Builds - Gradle DPE Tour Berlin 2024

Optimizing Gradle Builds - Gradle DPE Tour Berlin 2024
ISPM 15 Heat Treated Wood Stamps and why your shipping must have one

ISPM 15 Heat Treated Wood Stamps and why your shipping must have one
Presentation of IEEE Slovenia CIS (Computational Intelligence Society) Chapte...

Presentation of IEEE Slovenia CIS (Computational Intelligence Society) Chapte...
Electric vehicle and photovoltaic advanced roles in enhancing the financial p...

Electric vehicle and photovoltaic advanced roles in enhancing the financial p...
Www educationsmaterials-com-2020-12-uiet-csjm-university-microprocessor-ece-html
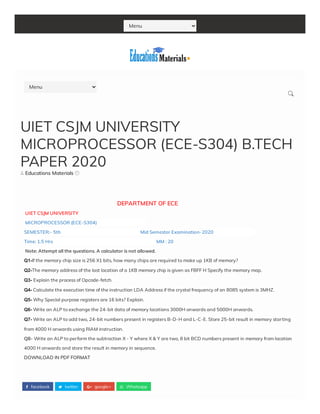
- 1. Menu facebook twitter google+ Whatsapp Educations Materials DEPARTMENT OF ECE UIET CSJM UNIVERSITY MICROPROCESSOR (ECE-S304) SEMESTER:- 5th Mid Semester Examination-2020 Time: 1.5 Hrs MM : 20 Note: Attempt all the questions. A calculator is not allowed. Q1-If the memory chip size is 256 X1 bits, how many chips are required to make up 1KB of memory? Q2-The memory address of the last location of a 1KB memory chip is given as FBFF H Specify the memory map. Q3- Explain the process of Opcode-fetch. Q4- Calculate the execution time of the instruction LDA Address if the crystal frequency of an 8085 system is 3MHZ. Q5- Why Special purpose registers are 16 bits? Explain. Q6- Write an ALP to exchange the 24-bit data of memory locations 3000H onwards and 5000H onwards. Q7- Write an ALP to add two, 24-bit numbers present in registers B-D-H and L-C-E. Store 25-bit result in memory starting from 4000 H onwards using RIAM instruction. Q8- Write an ALP to perform the subtraction X - Y where X & Y are two, 8 bit BCD numbers present in memory from location 4000 H onwards and store the result in memory in sequence. DOWNLOAD IN PDF FORMAT UIET CSJM UNIVERSITY MICROPROCESSOR (ECE-S304) B.TECH PAPER 2020 Menu
- 2. Newer Post Older Post Educations Materials In This Blog You will Find All Types of Study Materials Comment as: Google Accoun PublishPublish PreviewPreview Enter your comment... NO COMMENTS: POST A COMMENT
- 3. Educations Materials View my complete pro le Author Facebook Microprocessor B.tech Paper 2020 Kanpur University UNIVERSITY INSTITUTE OF ENGINEERING & TECHNOLOGY END-SEMESTER EXAMINATION 2020 B.TECH IIIrd YEAR ELECTRONICS & COMMUNICATION ENGINEE...
- 4. Educations Materials about a month ago 1 Comment Share Educations Materials 511 likes Like Page Sh Home Privacy Policy Terms and conditions Disclaimer Contact us
- 6. CREATED BY SORATEMPLATES | DISTRIBUTED BY SATISH VERMA Message * Send