This document discusses common approaches for analyzing Windows crashes, including blue screen of deaths (BSODs), and provides examples of different types of kernel issues:
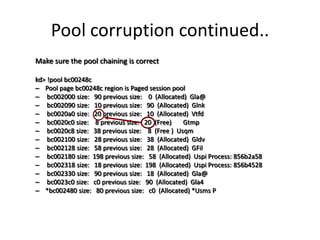
1. Memory corruption issues can be investigated using driver verifier and WinDBG commands like !analyze, kv, and !pool to check for pool corruption.
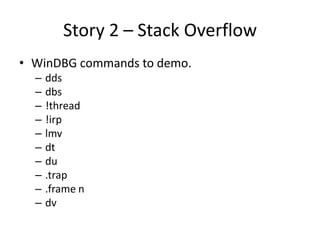
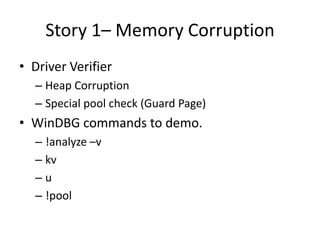
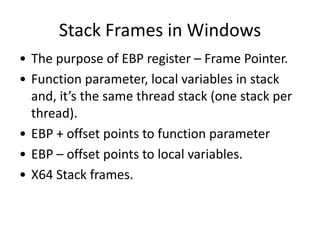
2. Stack overflows can be examined using WinDBG commands like dds, dbs, !thread, !irp, lmv, dt, du, .trap, and .frame to analyze stack frames and memory.
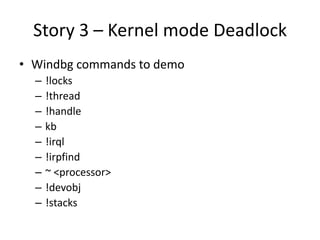
3. Kernel deadlocks can be debugged with commands like !locks, !thread, !handle, kb, !irql, !irpfind, ~
![Stack Frames continued..
• 0:000> u Simple_App_Crash3!CSimpleAppCrash3Dlg::OnBnClickedButton1
• Simple_App_Crash3!CSimpleAppCrash3Dlg::OnBnClickedButton1 [d:sisimonworking
areapresentationswindbgsimple app crash3simple app crash3simple app crash3dlg.cpp @
154]:
• 00401580 55 push ebp - First Push EBP to stack
• 00401581 8bec mov ebp,esp Set new ebp as current esp
• 00401583 83ec14 sub esp,14h make enough room for local variable
• 00401586 894dec mov dword ptr [ebp-14h],ecx <- Copy the this pointer to stack first
element for the current stack frame
• 00401589 c745f400000000 mov dword ptr [ebp-0Ch],0 one of the local var to 0
• 00401590 c745fc0a000000 mov dword ptr [ebp-4],0Ah Another local var to 10
• 00401597 c745f80f000000 mov dword ptr [ebp-8],0Fh Another local var to 15
• 0040159e cc int 3 Our hard coded break point](https://image.slidesharecdn.com/windowskerneldebugging-workshopinflorida-121205102842-phpapp02/85/Windows-kernel-debugging-workshop-in-florida-8-320.jpg)
![• 0:000> r
• eax=00000000 ebx=00000111 ecx=0013fe74 edx=00000000 esi=00403444 edi=00000001
• eip=0040159e esp=0013f860 ebp=0013f874 iopl=0 nv up ei pl nz na pe nc
• cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000206
• Simple_App_Crash3!CSimpleAppCrash3Dlg::OnBnClickedButton1+0x1e:
• 0040159e cc int 3
• 0:000> dds 0013f860
• 0013f860 0013fe74
• 0013f864 7e41b788 USER32!GetParent+0x59
• 0013f868 00000000
• 0013f86c 0000000f
• 0013f870 0000000a
• 0013f874 0013f884 push current ebp to stack, set new ebp as esp Stack Frame - 1
• 0013f878 7c1746cc MFC71!_AfxDispatchCmdMsg+0x3d [f:vs70builds3077vcmfcatlshipatlmfcsrcmfccmdtarg.cpp @ 89]
• 0013f87c 00403444 Simple_App_Crash3!CSimpleAppCrash3Dlg::messageMap
• 0013f880 0013fe74
• 0013f884 0013f8b4 push current ebp to stack, set new ebp as esp Stack Frame - 2
• 0013f888 7c171915 MFC71!CCmdTarget::OnCmdMsg+0x10a [f:vs70builds3077vcmfcatlshipatlmfcsrcmfccmdtarg.cpp @ 396]
• 0013f88c 0013fe74
• 0013f890 000003e8
• 0013f894 00000000
• 0013f898 00401580 Simple_App_Crash3!CSimpleAppCrash3Dlg::OnBnClickedButton1 [d:sisimonworking areapresentationswindbgsimple app
crash3simple app crash3simple app crash3dlg.cpp @ 154]
• 0013f89c 00000000
• 0013f8a0 00000035
• 0013f8a4 00000000
• 0013f8a8 0013fe74
• 0013f8ac 000003e8
• 0013f8b0 00000000
• 0013f8b4 0013f8d8 push current ebp to stack, set new ebp as esp, Stack Frame - 3
• 0013f8b8 7c14db36 MFC71!CDialog::OnCmdMsg+0x1b [f:vs70builds3077vcmfcatlshipatlmfcsrcmfcdlgcore.cpp @ 88]
• 0013f8bc 000003e8
• 0013f8c0 00000000
• 0013f8c4 00000000
• 0013f8c8 00000000
• 0013f8cc 000003e8
• 0013f8d0 0013fe74
• 0013f8d4 00000000
• 0013f8d8 0013f928
• 0013f8dc 7c175cd8 MFC71!CWnd::OnCommand+0x51 [f:vs70builds3077vcmfcatlshipatlmfcsrcmfcwincore.cpp @ 2549]](https://image.slidesharecdn.com/windowskerneldebugging-workshopinflorida-121205102842-phpapp02/85/Windows-kernel-debugging-workshop-in-florida-9-320.jpg)