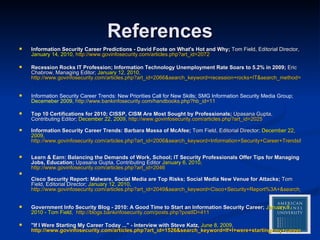
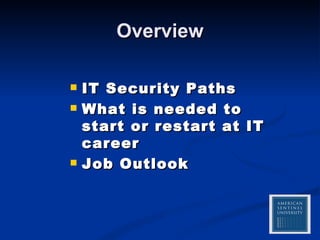
The document summarizes an IT security career webinar that covered the following key points:
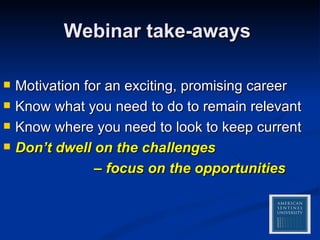
1) IT security is a promising career field with growing demand due to increasing cyber threats.
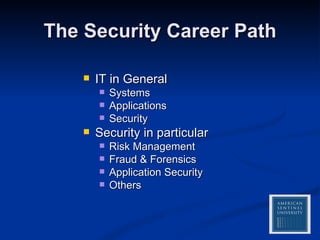
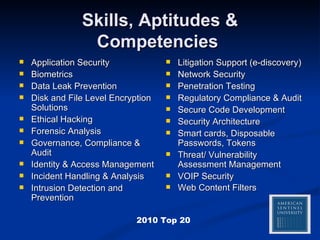
2) To start or restart an IT security career requires academic foundations, security certifications for focused training, hands-on experience, and continuous skills advancement.
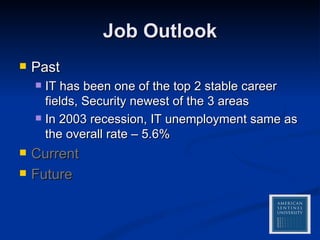
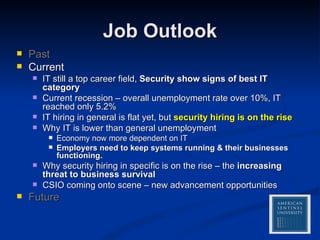
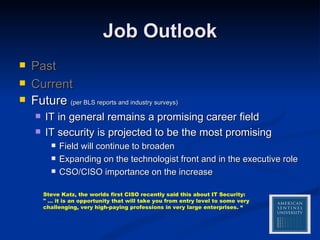
3) The job outlook for IT security is very positive and projected to be the most promising area within the stable IT field, with expanding roles and opportunities.
![American Sentinel University Career Webinar Series An IT Security Career Path “ This year and next year, bar none, security is the smart place to be in IT. – David Foote” Presented by Paul Capicik 866-470-3743 [email_address] 26 Jan 2010](https://image.slidesharecdn.com/webinar2security-12653841625972-phpapp01/75/Webinar-2-IT-Security-1-2048.jpg)


![American Sentinel University Career Webinar Series Q & A Americansentinel.edu/military [email_address] 866-470-3743](https://image.slidesharecdn.com/webinar2security-12653841625972-phpapp01/85/Webinar-2-IT-Security-15-320.jpg)