Internet Standards and TCP/IP Protocol Suite
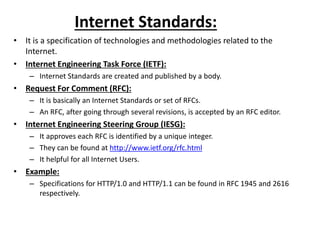
- 1. Internet Standards: • It is a specification of technologies and methodologies related to the Internet. • Internet Engineering Task Force (IETF): – Internet Standards are created and published by a body. • Request For Comment (RFC): – It is basically an Internet Standards or set of RFCs. – An RFC, after going through several revisions, is accepted by an RFC editor. • Internet Engineering Steering Group (IESG): – It approves each RFC is identified by a unique integer. – They can be found at http://www.ietf.org/rfc.html – It helpful for all Internet Users. • Example: – Specifications for HTTP/1.0 and HTTP/1.1 can be found in RFC 1945 and 2616 respectively.
- 2. TCP/IP Protocol Suite: • It is a set of protocols used in the Internet and other communication networks. • It creates the technical foundation of the Internet. • Two primary protocols: • Transmission Control Protocol (TCP) • Internet Protocol (IP) • But it consists of many other protocols.
- 4. • Each of which deals with a set of issues that arise while designing a communication network. • According to RFC 1122, only four layers. – Link layer – Internet layer – Transport layer – Application layer • Each layer provides a well-defined set of services to its upper layer and uses services provided by its lower layer.
- 5. Communication between two hosts using TCP/IP
- 7. Host-to-Host or Peer-to-Peer and N/W Interface or Link and Internet or Network
- 8. TCP/IP suite of protocols Layer Protocols Applicati on HTTP, SMTP, SSH, Telnet, SIP, Gopher, IMAP, SNIMP, Rlogin, POP3, DNS, SSL, FTP Transpor t TCP, UDP Internet IP, ICMP, IGMP, OSPF, BGP, RIP,ARP, RARP Link HDLC
- 9. Link Layer: • This is the lower most layer in TCP/IP protocol suite. • It deals with LAN (Local Area Network). • It is responsible for transferring data from one machine to another within the same local network. • Primary Function: – Framing – Error Detection – Error Correction – Flow Control – Error Control – Medium Access Control
- 10. Internet Layer: • It is to deliver packets from one network to another. • Routing: • It determines a suitable route from the source computer to the target and delivers packets through this route. • Purpose: • It introduces an addressing mechanism called IP addressing.
- 11. Transport Layer: • It is end-to-end message transfer. • Types of services to its upper layer: – Connection-oriented: • The segments of a message are delivered in order. • The TCP in a TCP/IP protocol suite provides connection- oriented service. – Connection-less: • No such guarantee is given. • User Datagram Protocol provides connection-less service.
- 12. • It also introduces port numbers to identify processes that run in a computer. • It should also implement the following optional tasks: – Segmentation – Flow Control – Error Control – Congestion Control
- 13. Application Layer: • This is the layer that users actually interact with. • It provides interfaces to users for network communication. • Example: • It provides an interface using which users can transfer files from one computer to another computer
- 15. IP Addresses: • What is an IP Address? – An IP address is a 32 bit sequence of 1’s and 0’s. – A way to identify a machines on a network. – TCP/IP protocol suite assigns a unique address. – IP version 4, an IP address is a 32 bit binary number. Purpose Identifying a host/network interface Location addressing
- 16. Dotted Decimal Notation: • IP addresses using 4 decimal numbers, each representing 8 bits. • The range 0 to 255. • It separate by three dots (.). • Example: • IP Address: 203.197.107.107 • Binary Form: 11001011.11000101.01101011.01101011 • Growth of internet, a new system IPv6 was introduced uses 128 bit address.
- 17. Part of an IP Address: – Network Part: • It identifies the network part is same for all hosts belonging to the same network – Host Part: • The number of bits in the host part determines the number of possible hosts within the network uniquely.
- 18. Classes for IP Address: Class es Starts with 1st Octet in Binary Range ID Reserved Network Host Class A 0XXXXXXX 0 to 127 or 1 to 126 W (8) x, y, z (24) Governments Class B 10XXXXXX 128 to 191 w, x (16) y, z (16) Medium Companies Class C 110XXXXX 192 to 223 w, x, y (24) Z (8) Small Companies Class D 1110XXXX 224 to 239 Reserved for Multicast - Multicasting Class E 1111XXXX 240 to 255 Reserved for Experiment - Future Use Class D and E are reserved for research purpose but aren’t used.
- 22. Classless Inter-Domain Routing: • It creating allocation for IP Address blocks and new rules of routing protocol using IPv4 addresses was implemented. • Introduced: Variable-length network ID • Result: Moderate utilization of IP addresses • A network consisting of consecutive IP addresses is very often represented as X/Y. • Subnet ID: where X is the first IP address in the series • Network ID: where Y is the number of bits in this field.
- 23. Example: • 203.197.107.96/28 having 28 bits in the network ID. • It means host ID field has 4 (32-28) bits. • So, possible IP addresses in this subnet is 16 (24). • They are 203.197.107.96-203.197.107.111. • Out of these 16 addresses, only 14 (16-2) can be assigned to hosts. • First - 203.197.107.96 and Second - 203.197.107.111. • It is used as subnet’s IP address and broadcast IP address. IP Address: The concept of classful IP address isn’t used in practice. It is only used in the technical jargon in network administrator’s.
- 24. IPv4 Private Addresses: • What is IPv4? • IPv4 (Internet Protocol Version 4) used to identify devices on a network through an addressing system. • It uses 32-bit address scheme allowing for a total of 2^32 addresses (just over 4 million addresses). • It including computers, smartphones and game consoles – connect to the internet requires an address.
- 25. • Early Network Design: • IP addresses assigned to particular computers or network devices were intended to be unique for global end-to-end communication. • It is exhausted quickly. • So, there was a tremendous demand to find a way out from this IPv4 address exhaustion. • It was released that IP addresses used by the computers in private networks need not be unique. • So, Computers are not connected to the Internet. • Example: • Factory machines that communicate only with each other via TCP/IP, need not have unique addresses.
- 28. Network Range Number of addresses 10.0.0.08/ (1 class A network) 10.0.0.0 - 10.255.255.255 16,777,216 172.16.0.0/12 (16 class B network) 172.16.0.0 - 172.313.255.255 1,048,576 192.168.0.0/16 (256 class C network) 192.168.0.0 - 192.168.255.255 65,536 • Three ranges of IPv4 addresses for private networks. • One range for each class (A, B, C) were reserved in RFC 1918. • Theses addresses are not routed on Internet and use need not be coordinated with an IP address registry. • Today, Private networks typically connect to the Internet through Network Address Translation (NAT).
- 31. MIME (Multipurpose Internet Mail Extension):• Simple Mail Transfer Protocol: – It is important and frequently used protocol in TCP/IP protocol suite. – It is used to deliver electronic mails (E mail). – SMTP was designed to transfer only text messages.
- 32. MIME MIME extends the format of following of email supports: • Text in character sets other that ASCII • Non text attachments. • Message bodies with multiple parts. • Header information in non ASCII character sets.
- 33. Sending Large Message: • When sending a large message, it splits them into small parts is called multi part message. • Peoples written emails can be transmitted through this SMTP in MIME format. • This format is specified as a part of HTTP/1.1. • MIME has grown beyond and describing the content of email to describing content type. – content type = multipart /related – content type = multipart/mixed Example: – In communication protocol like HTTP for WWW. – HTTP requires data transmitted in context of email like messages but data aren’t actually text. Important: – MIME use character encodings other than ASCII, and 8-bit binary content. – Mapping message into and out of MIME format is typically done automatically by e-mail or mail servers when sending or receiving e-mail to the internet.
- 34. Cyber Laws: • Cyber Laws is a system of law and regulation for the cyber space. • It refers to all the legal and regulatory aspects of the Internet and the applicable to WWW. Cyber Law-The Law of Internet & WWW: The number of users doubling using the Internet every 100 days New and sensitive issues related to various legal aspects of cyberspace began cropping up. A new and highly specialized branch of law came into existence Example: Cyber crimes involves traditional criminal activities such as theft, fraud, forgery, defamation and mischief. It can be categorized into two types:
- 35. Categories of Cyber Crime: Using computers as a tool Computers are used to attack other computers. It includes hacking, virus/worm attacks, DOS attacks, denial of service attacks, Trojan attacks, etc. Using computers as a weapon Computers are used as a weapon. It includes credit card frauds, email spoofing, email spamming, email bombing, cyber terrorism, EFT frauds, etc.