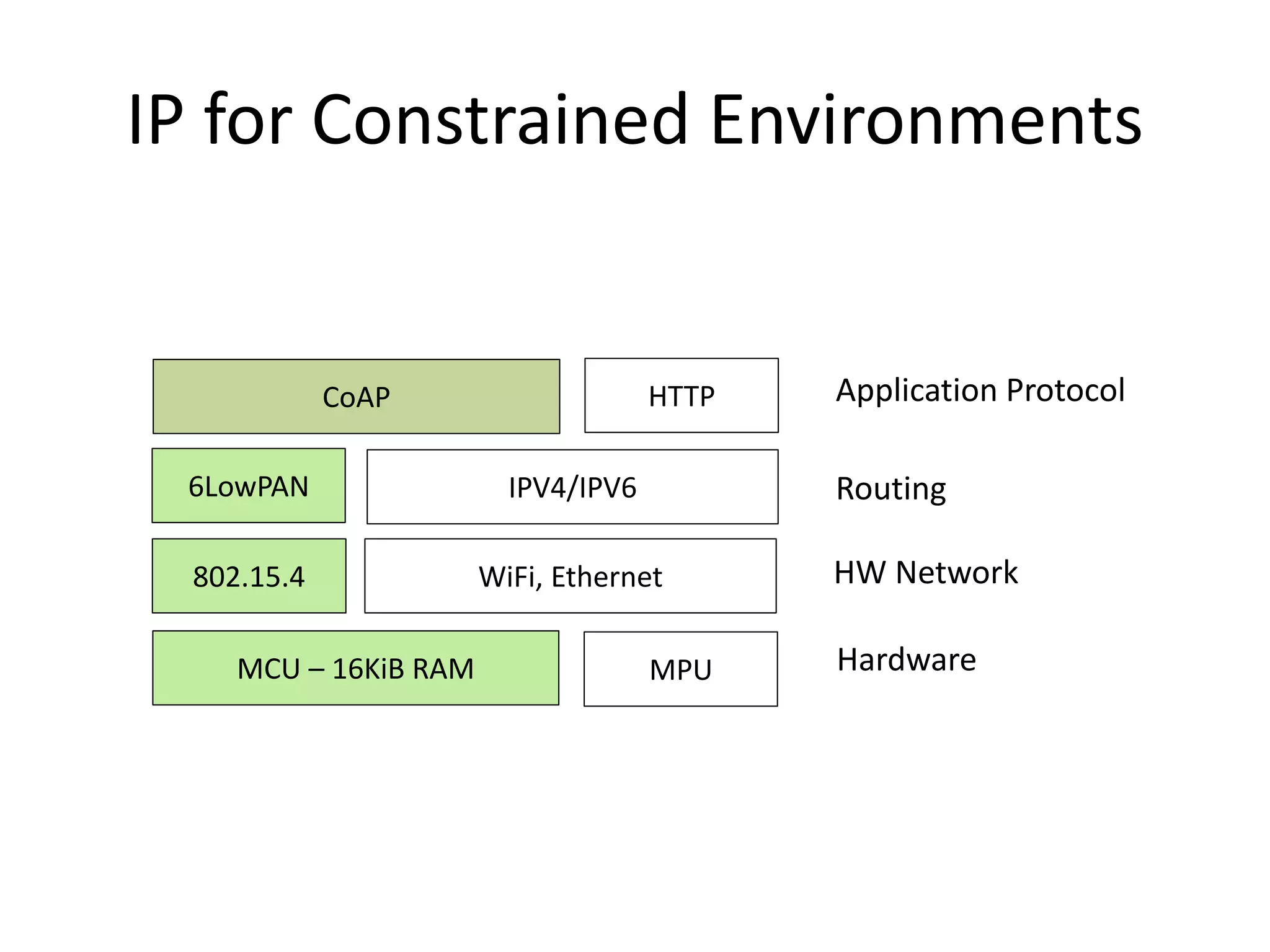
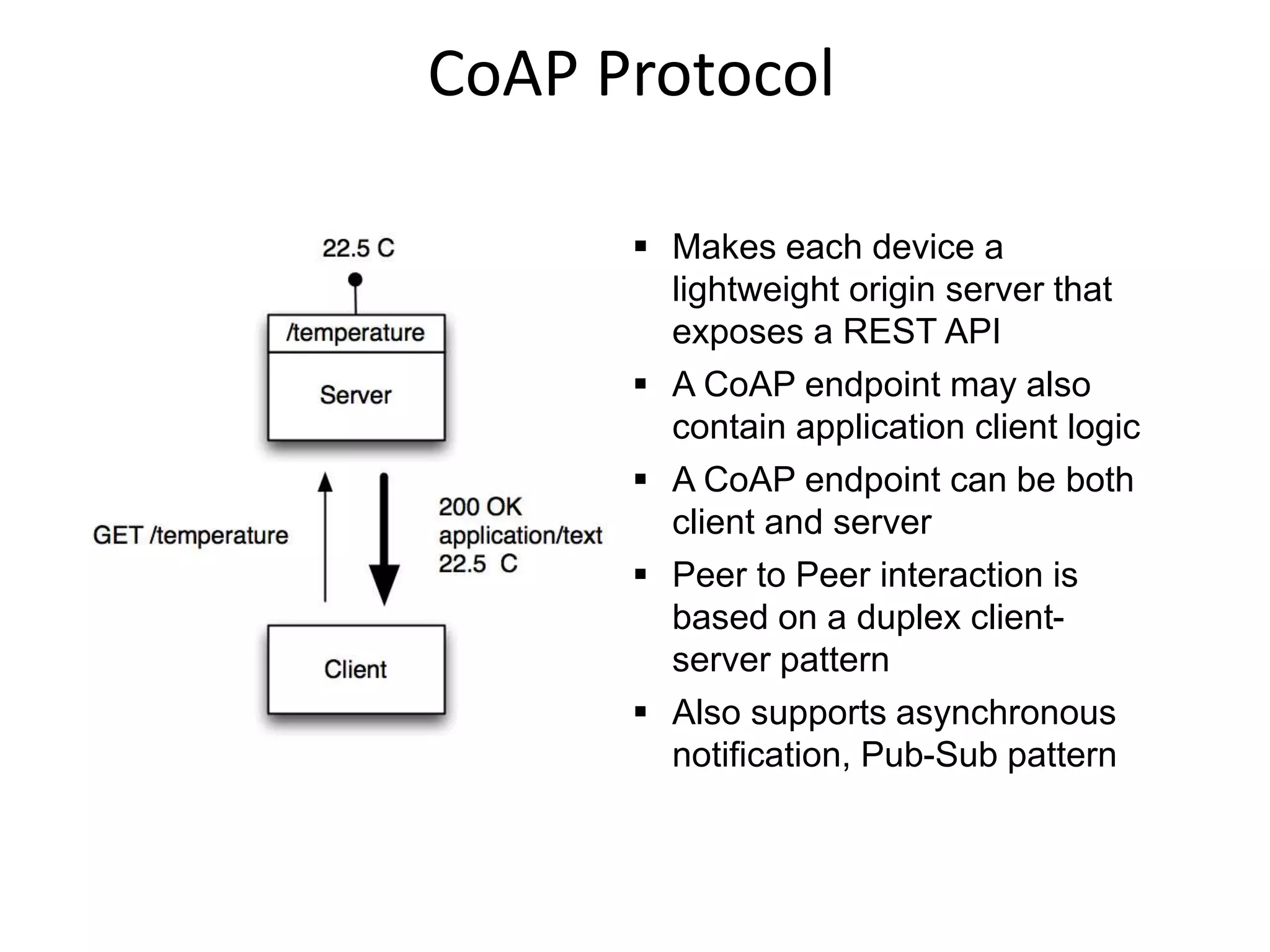
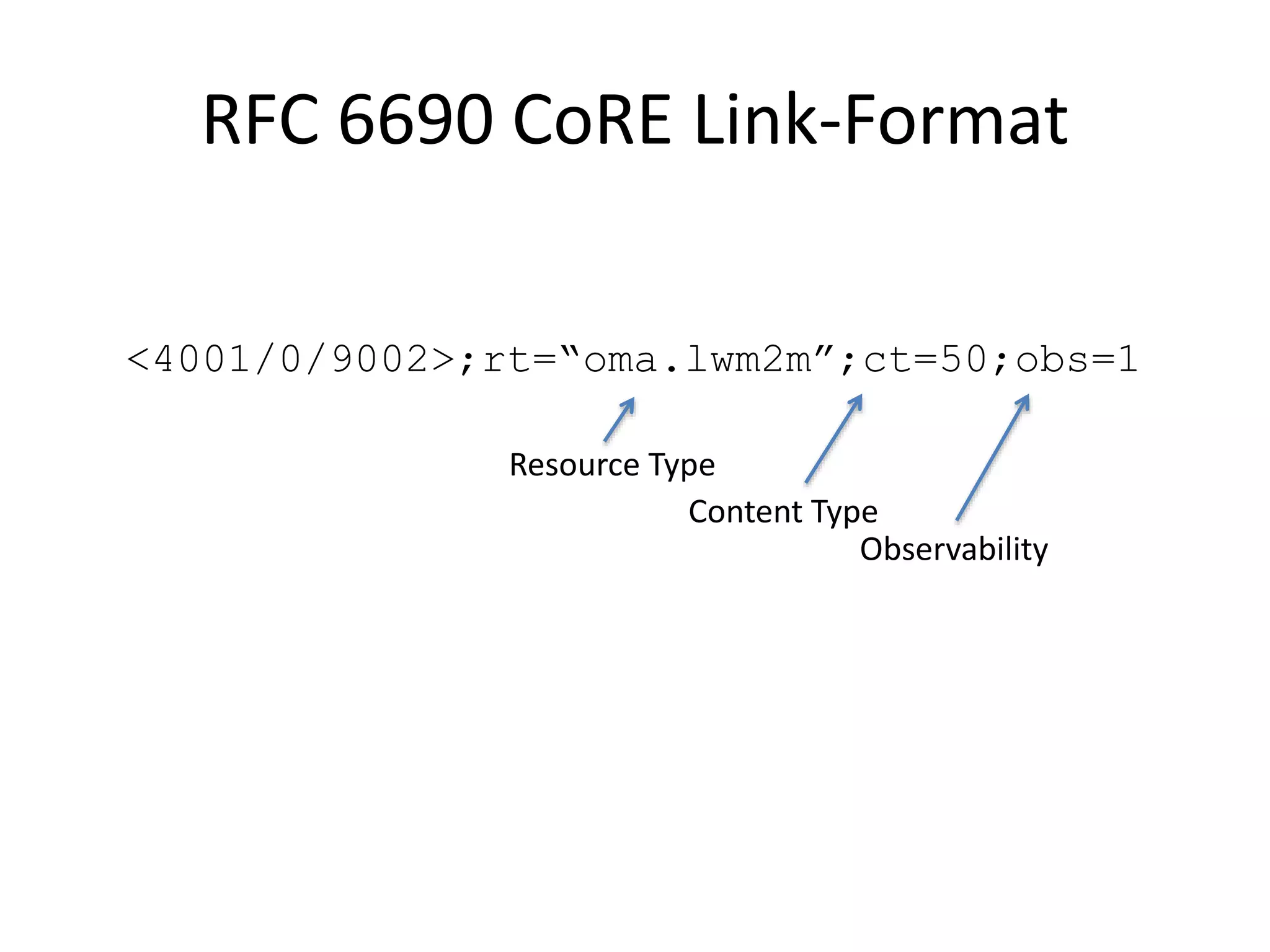
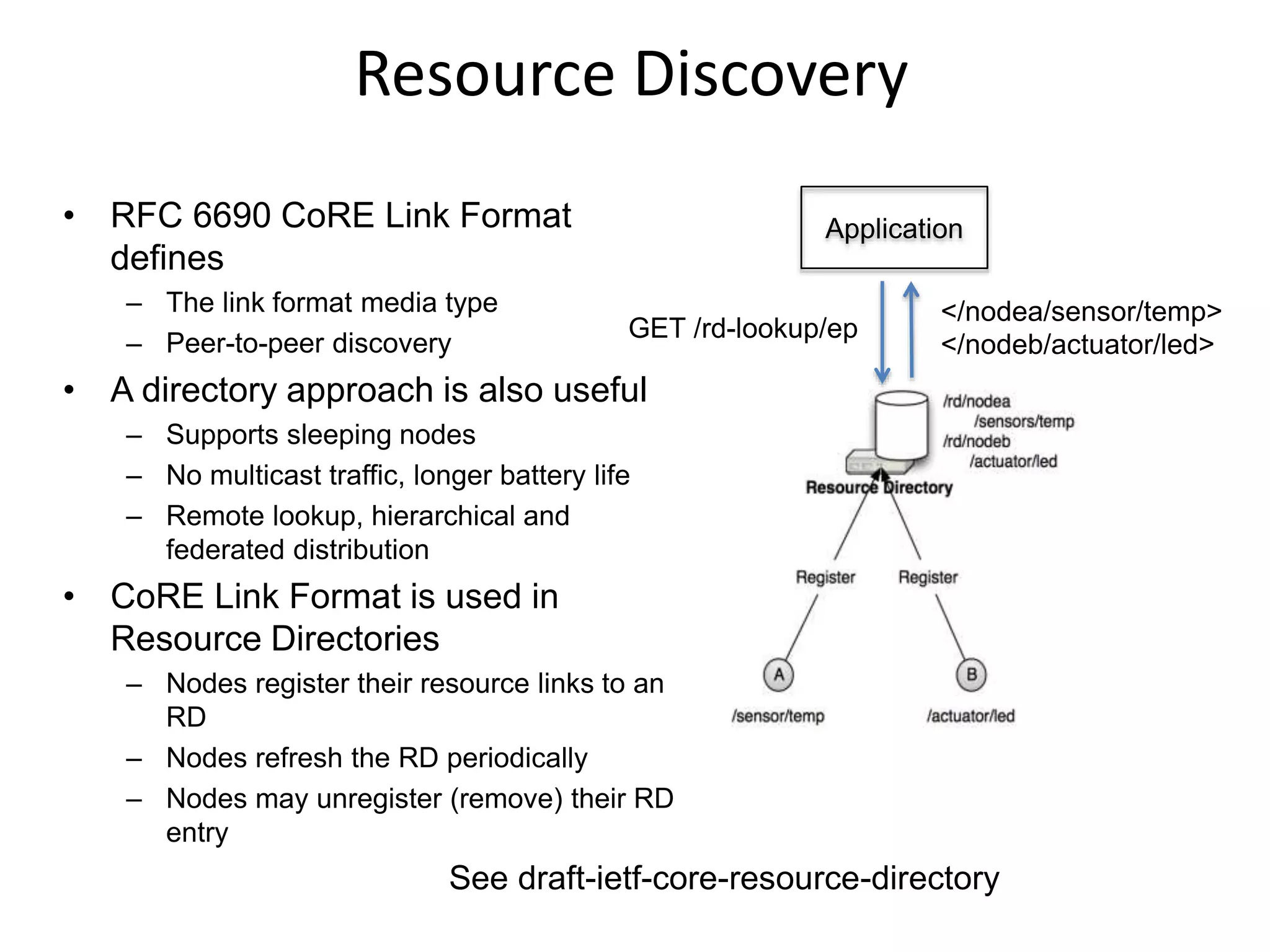
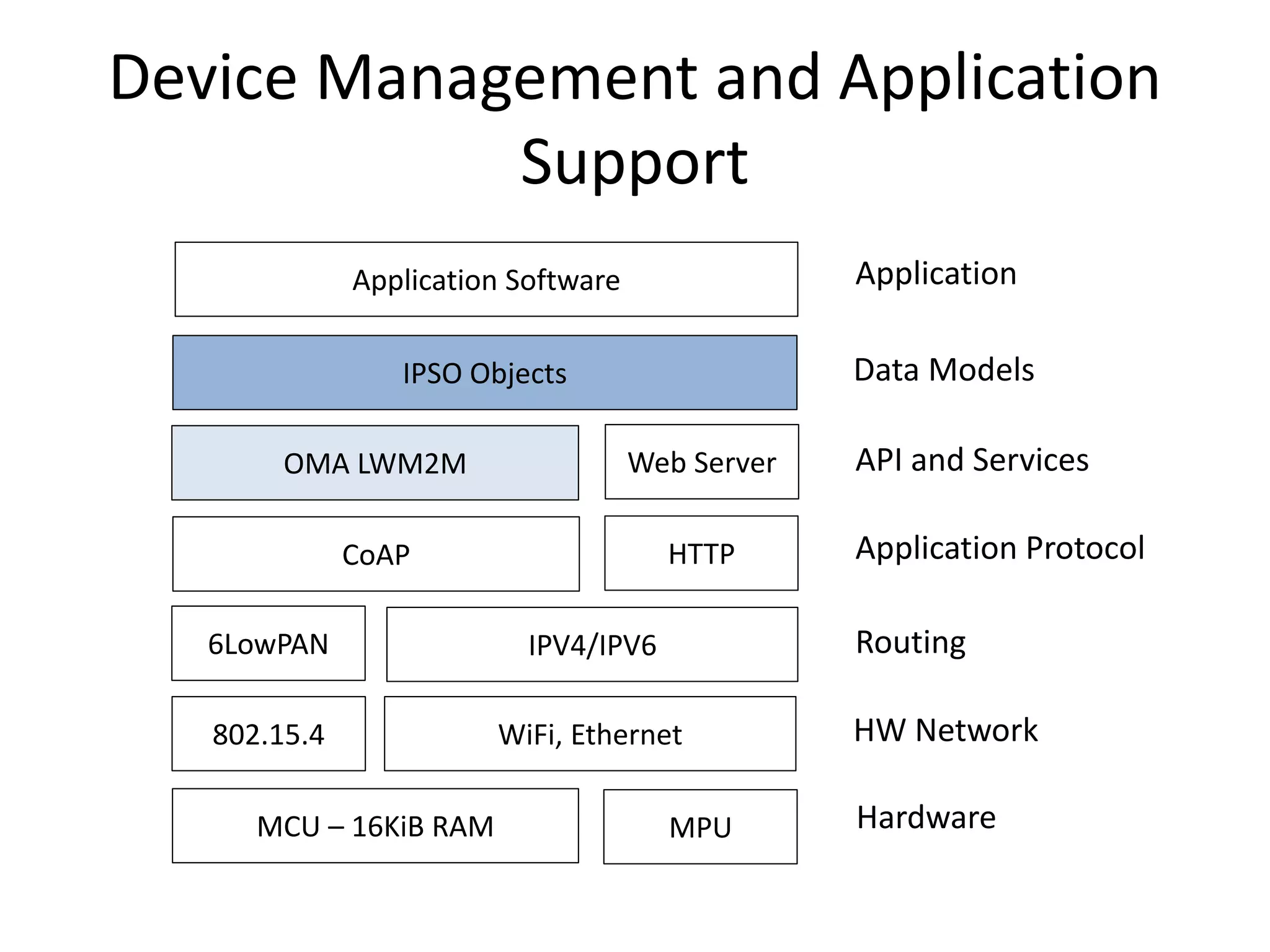
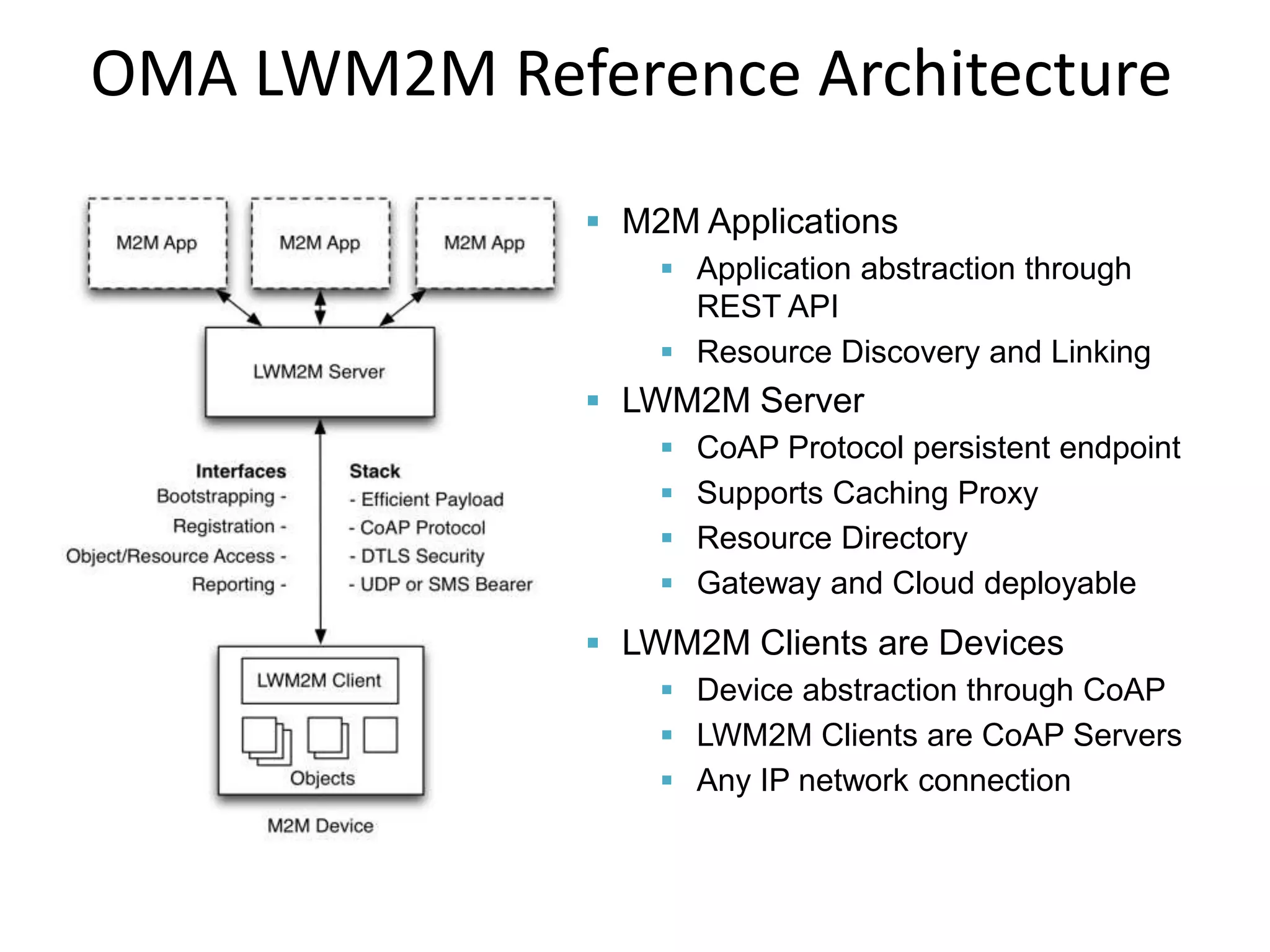
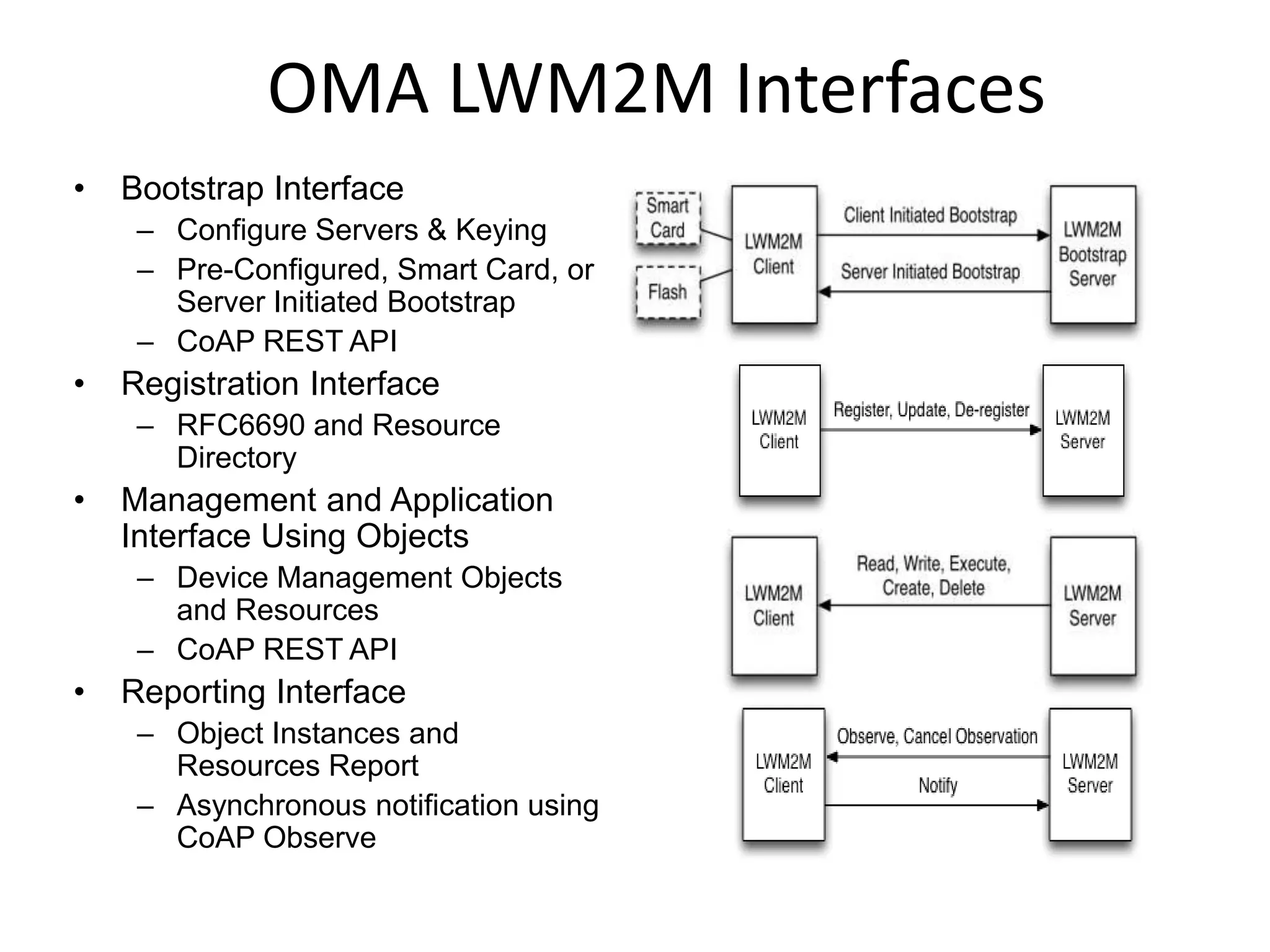
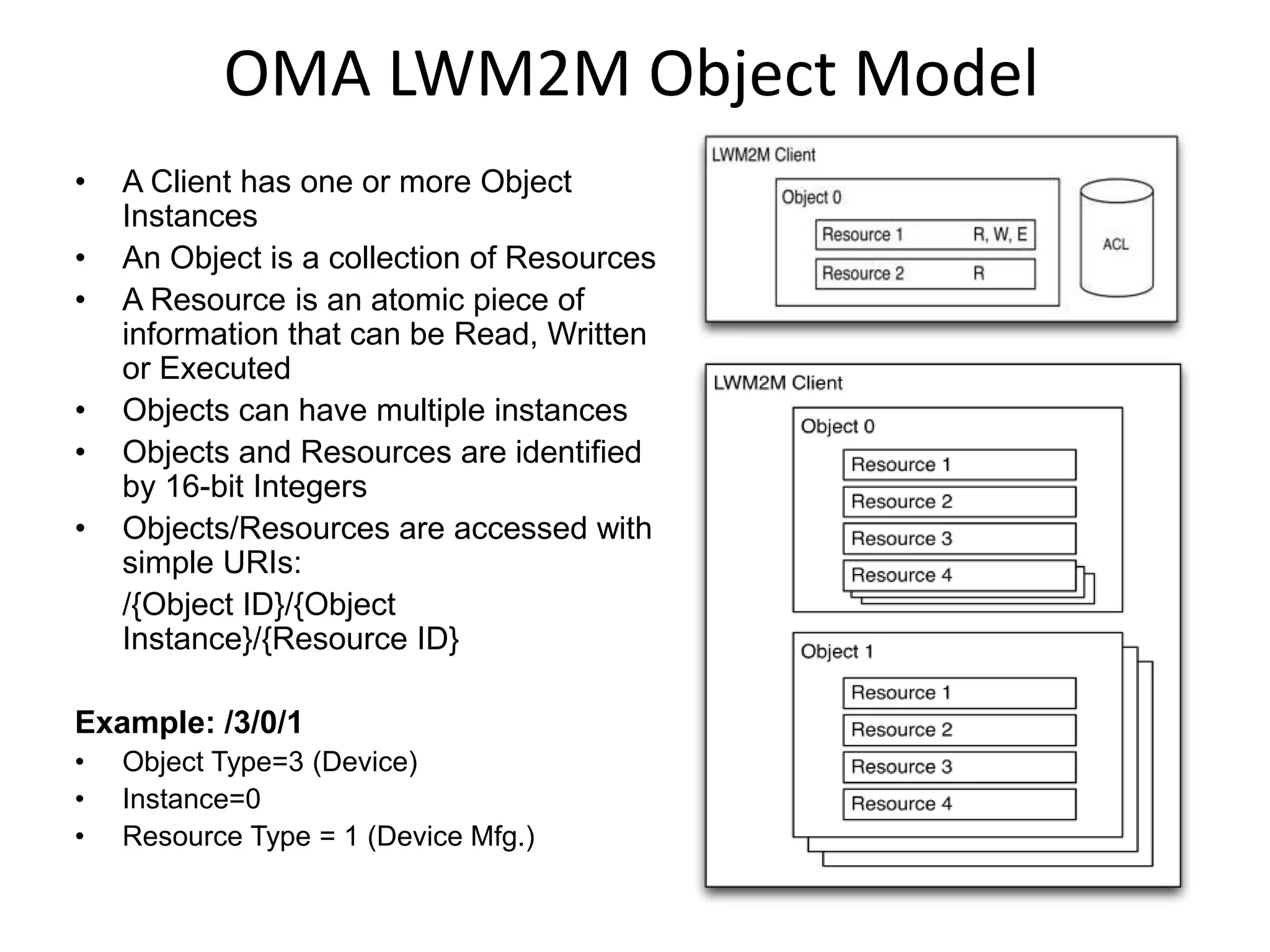
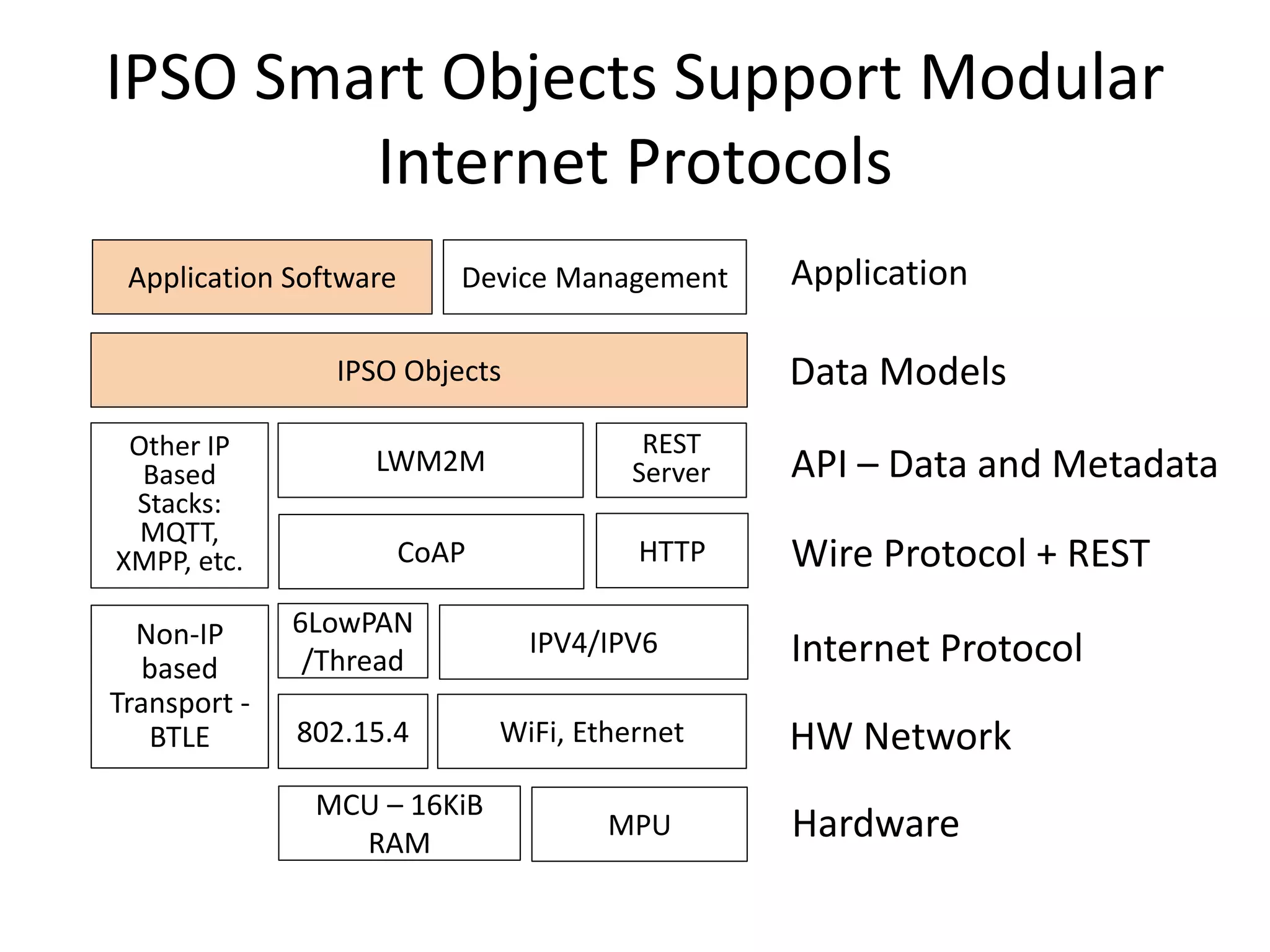
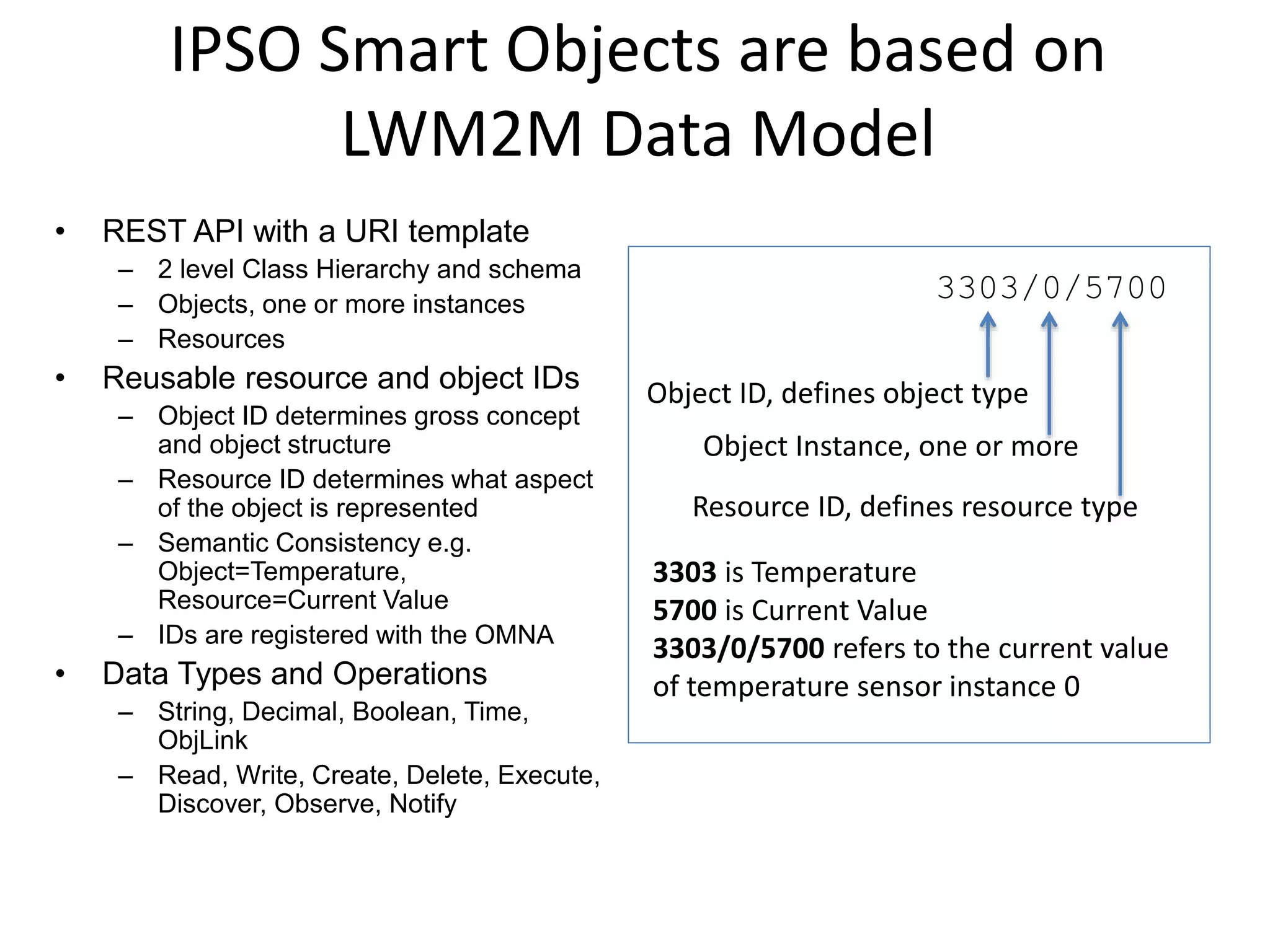
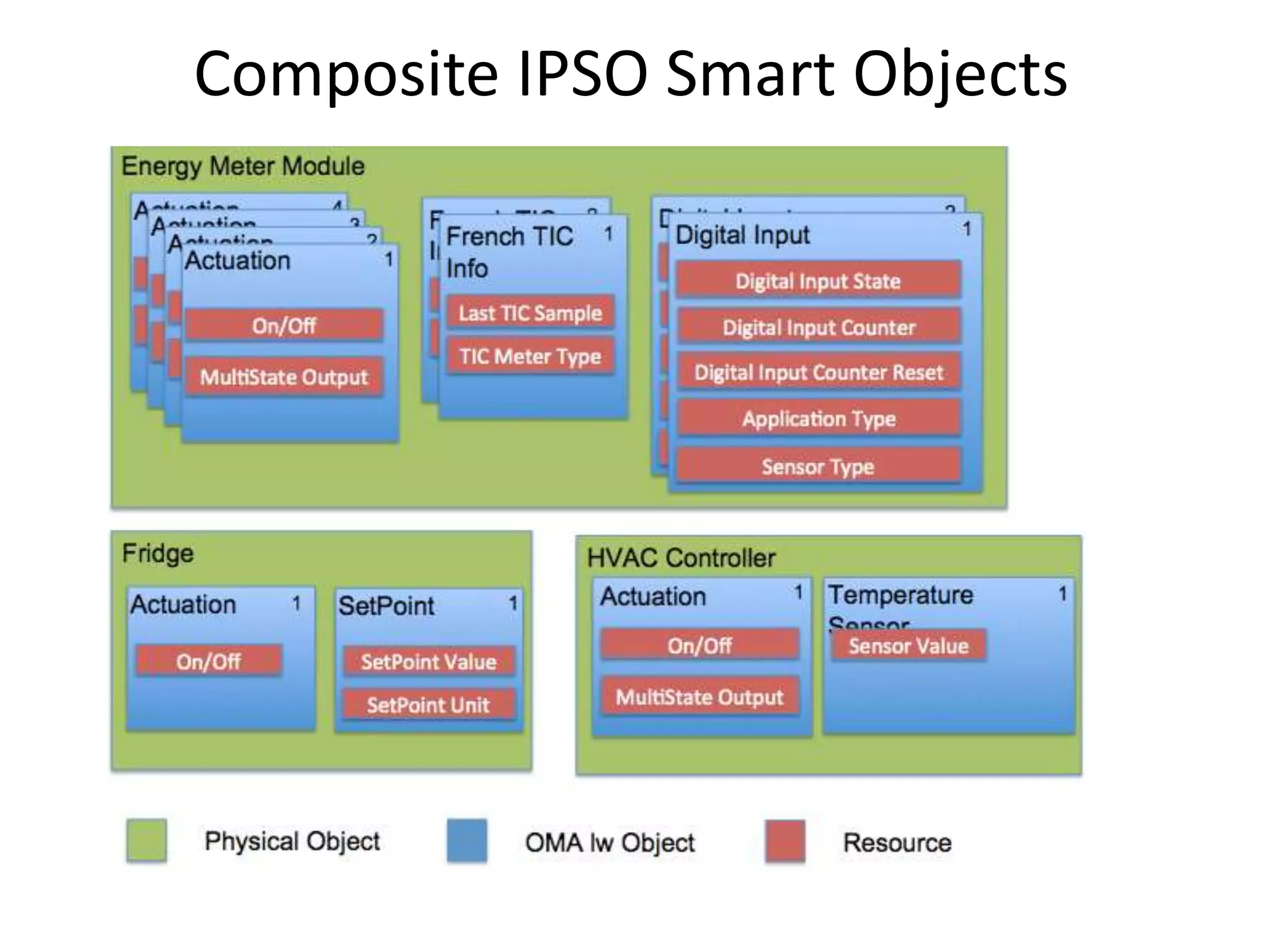
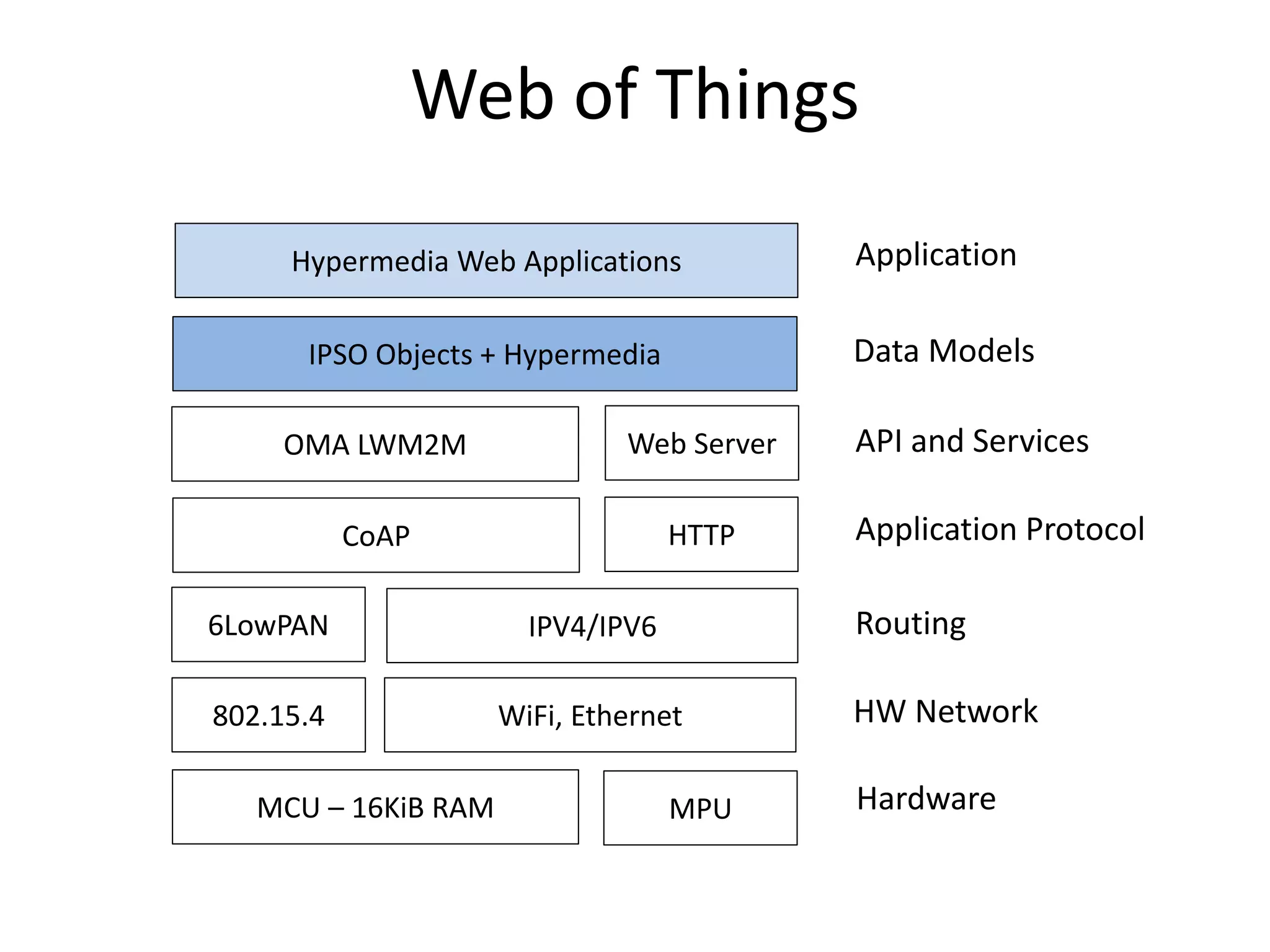
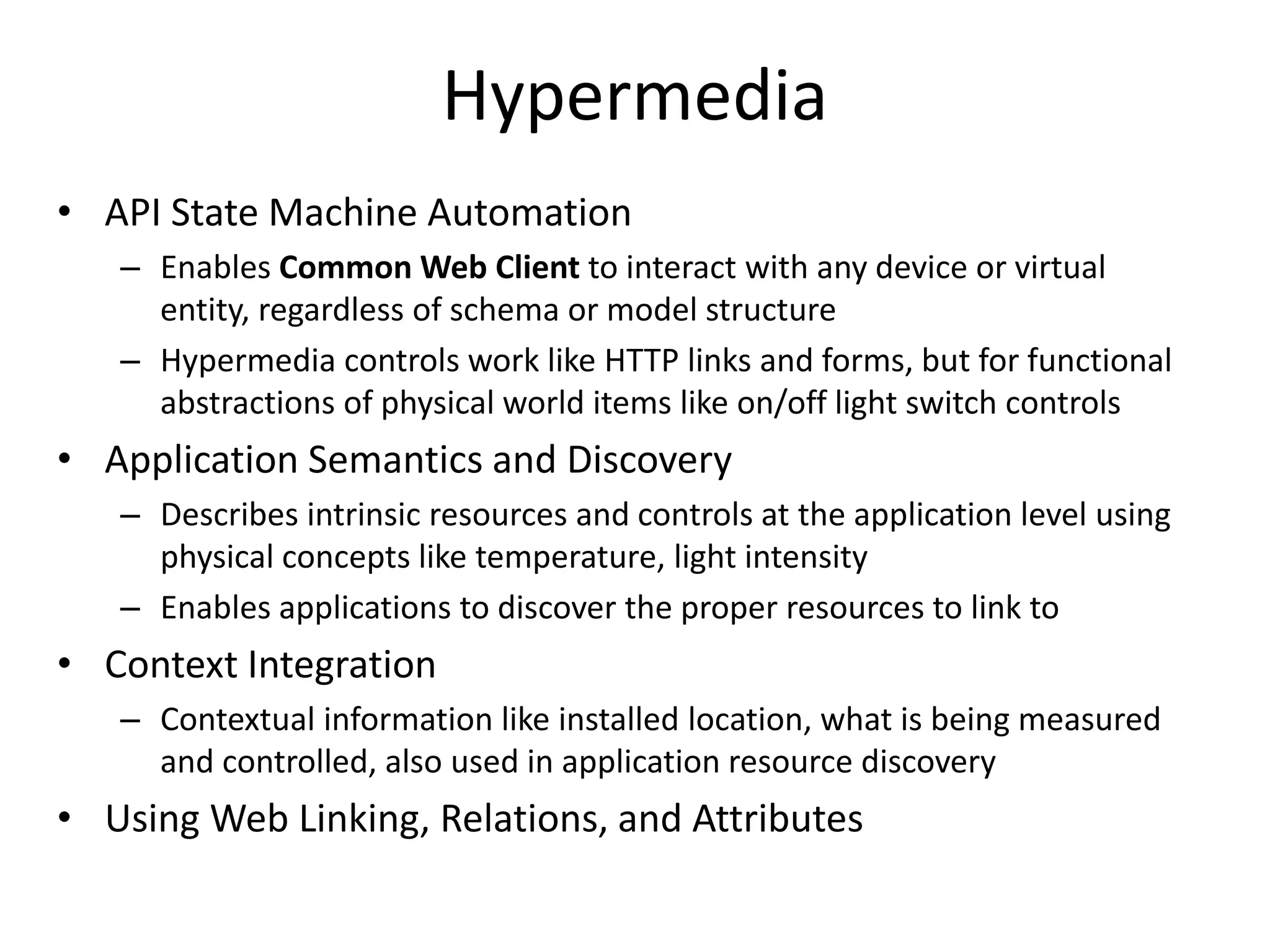
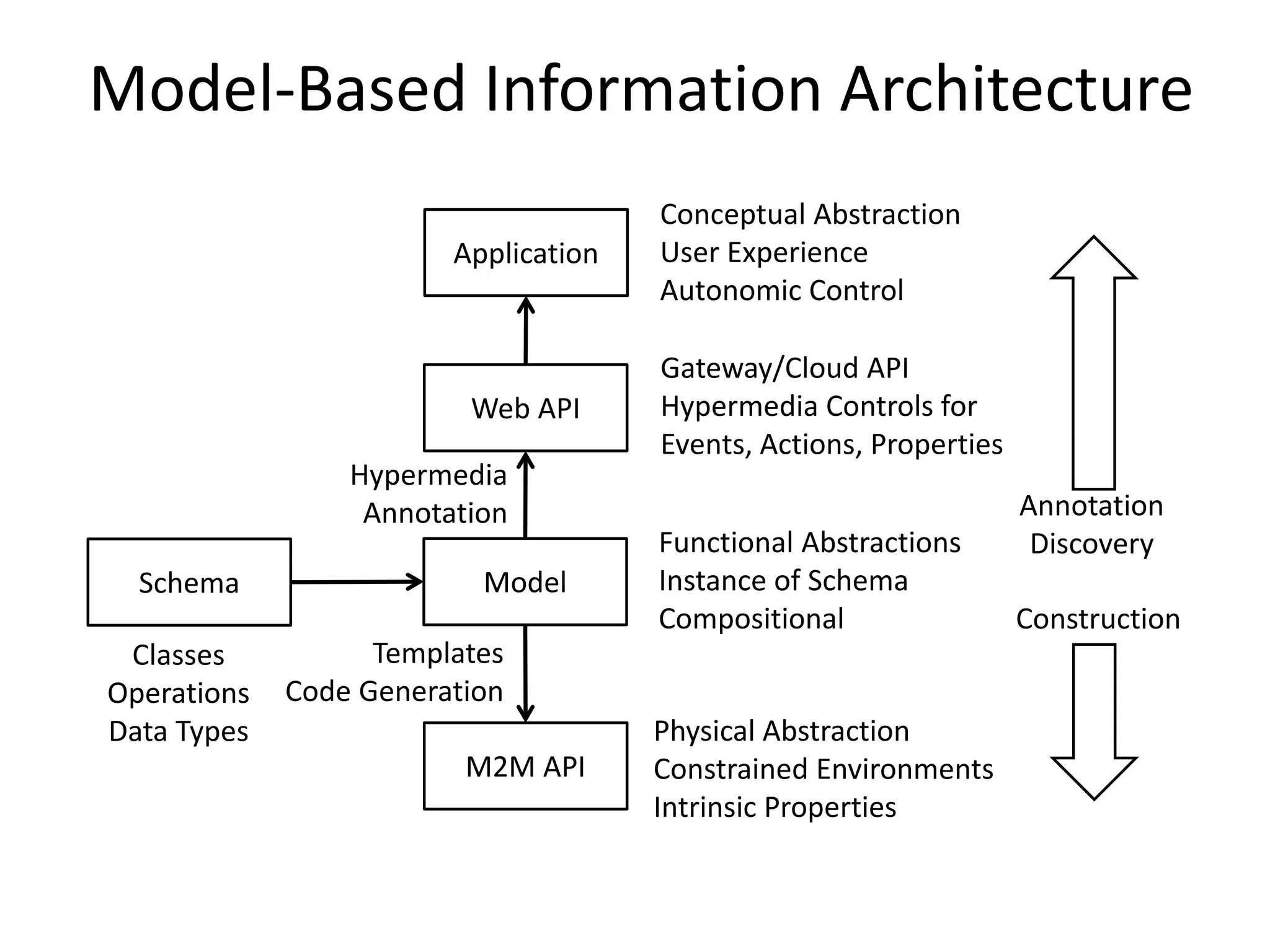
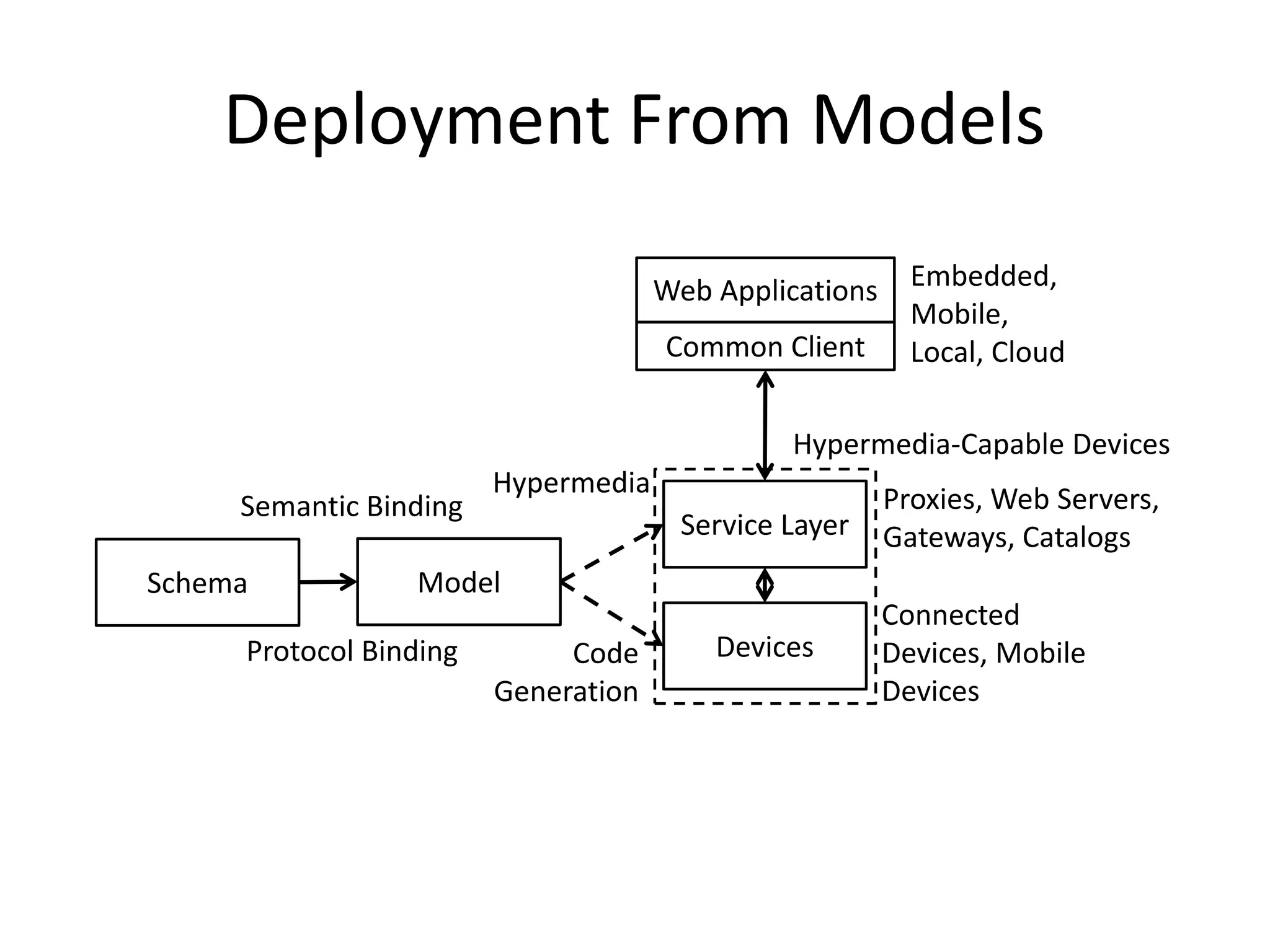
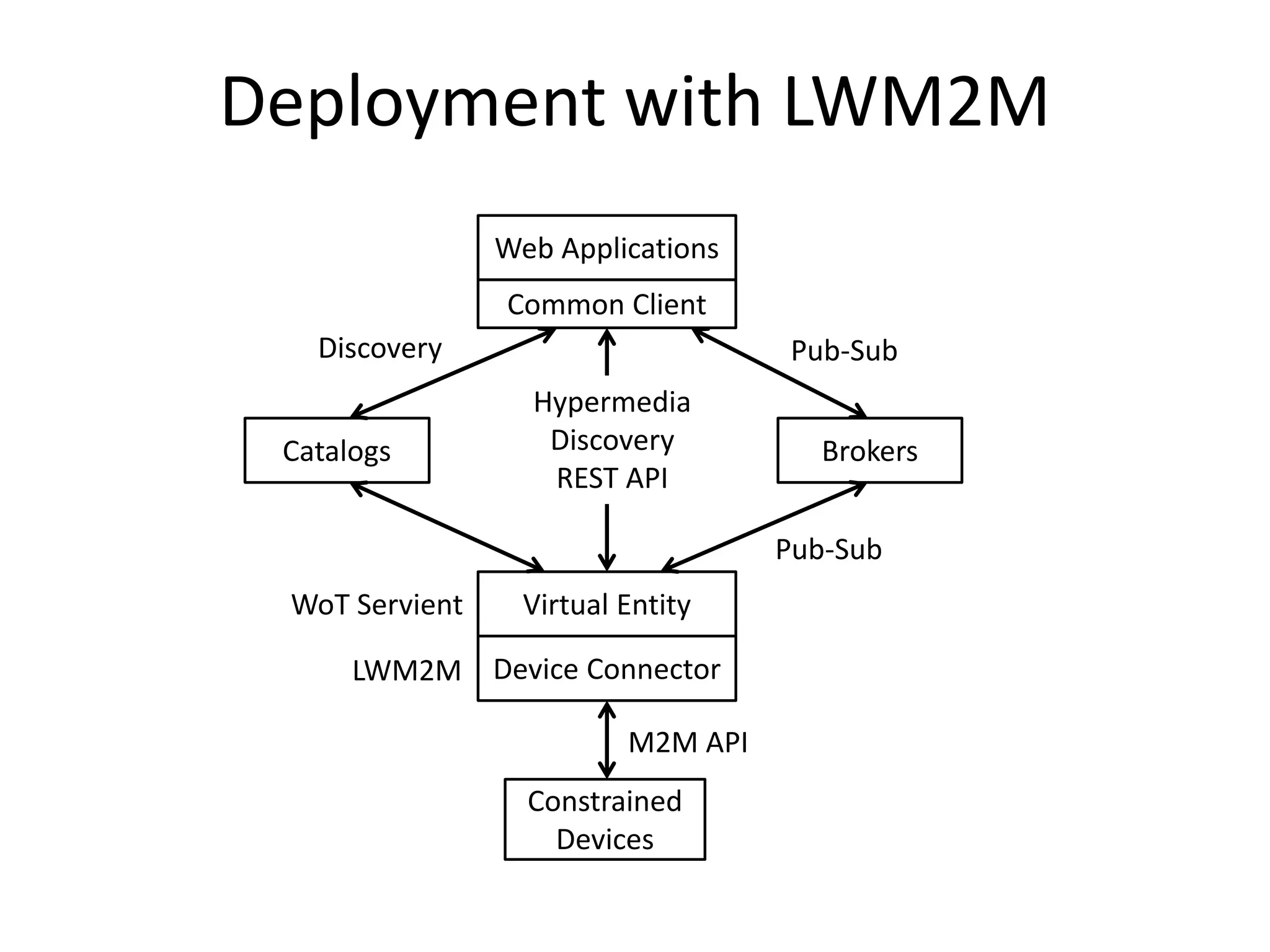
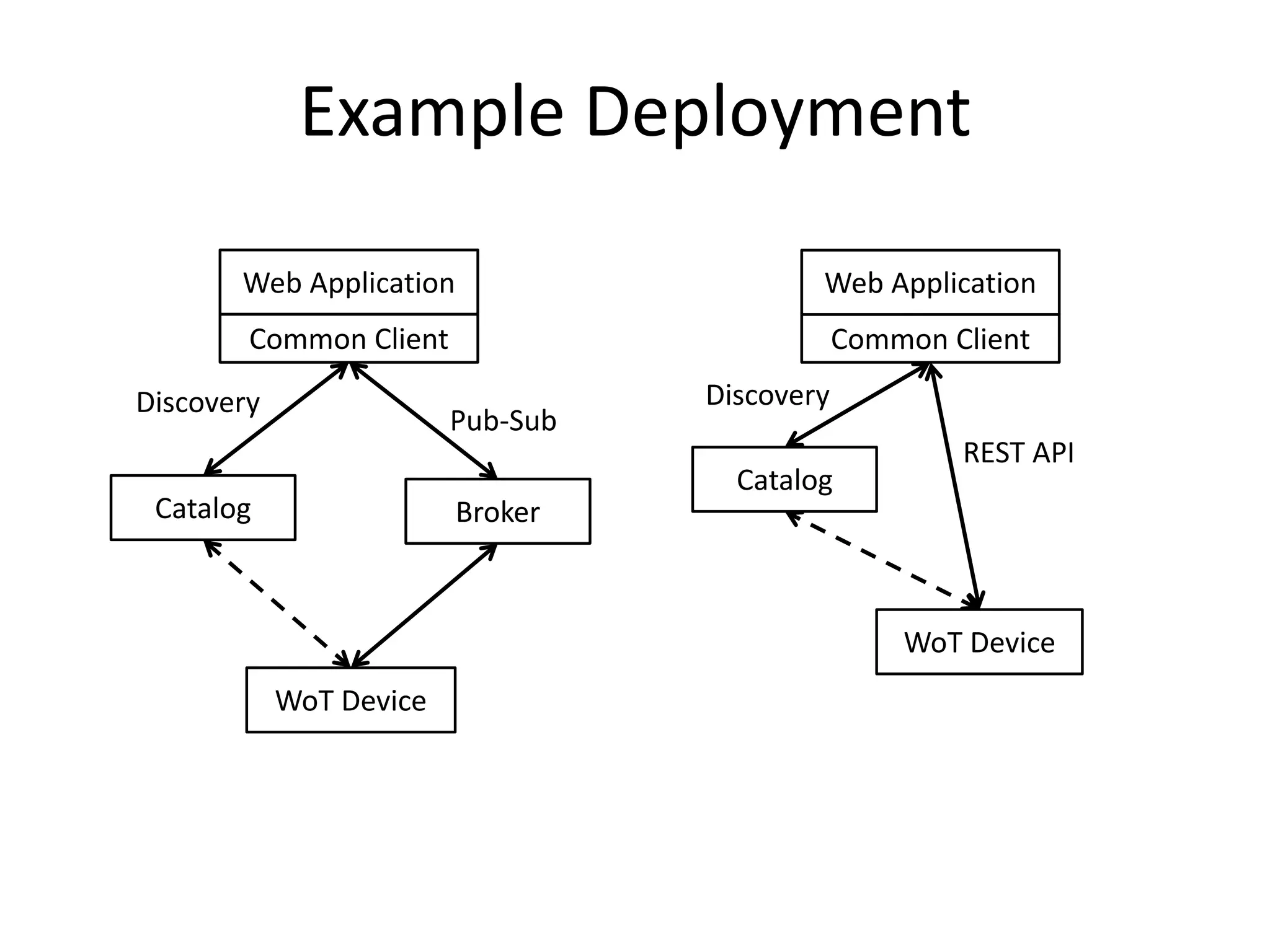
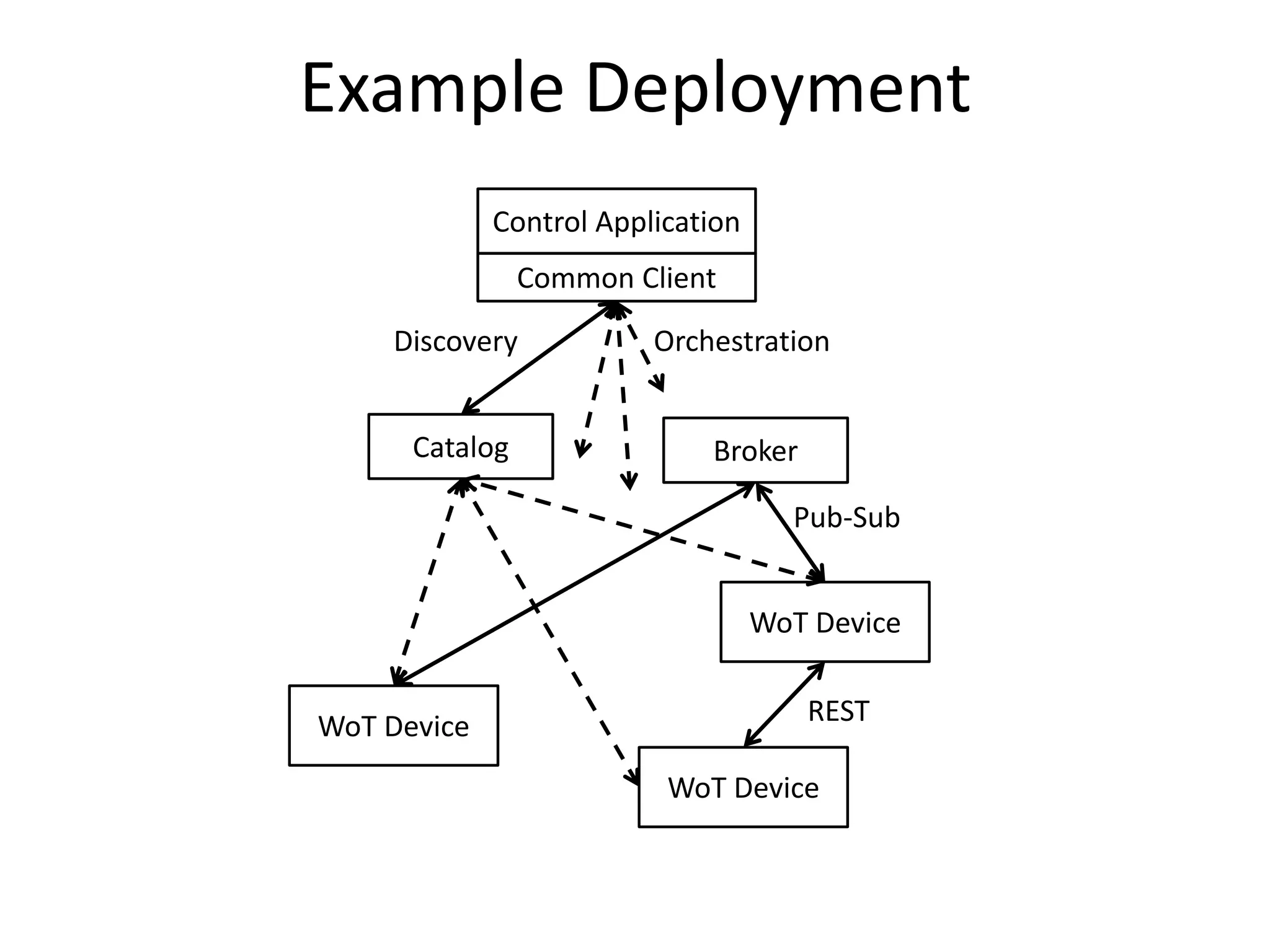
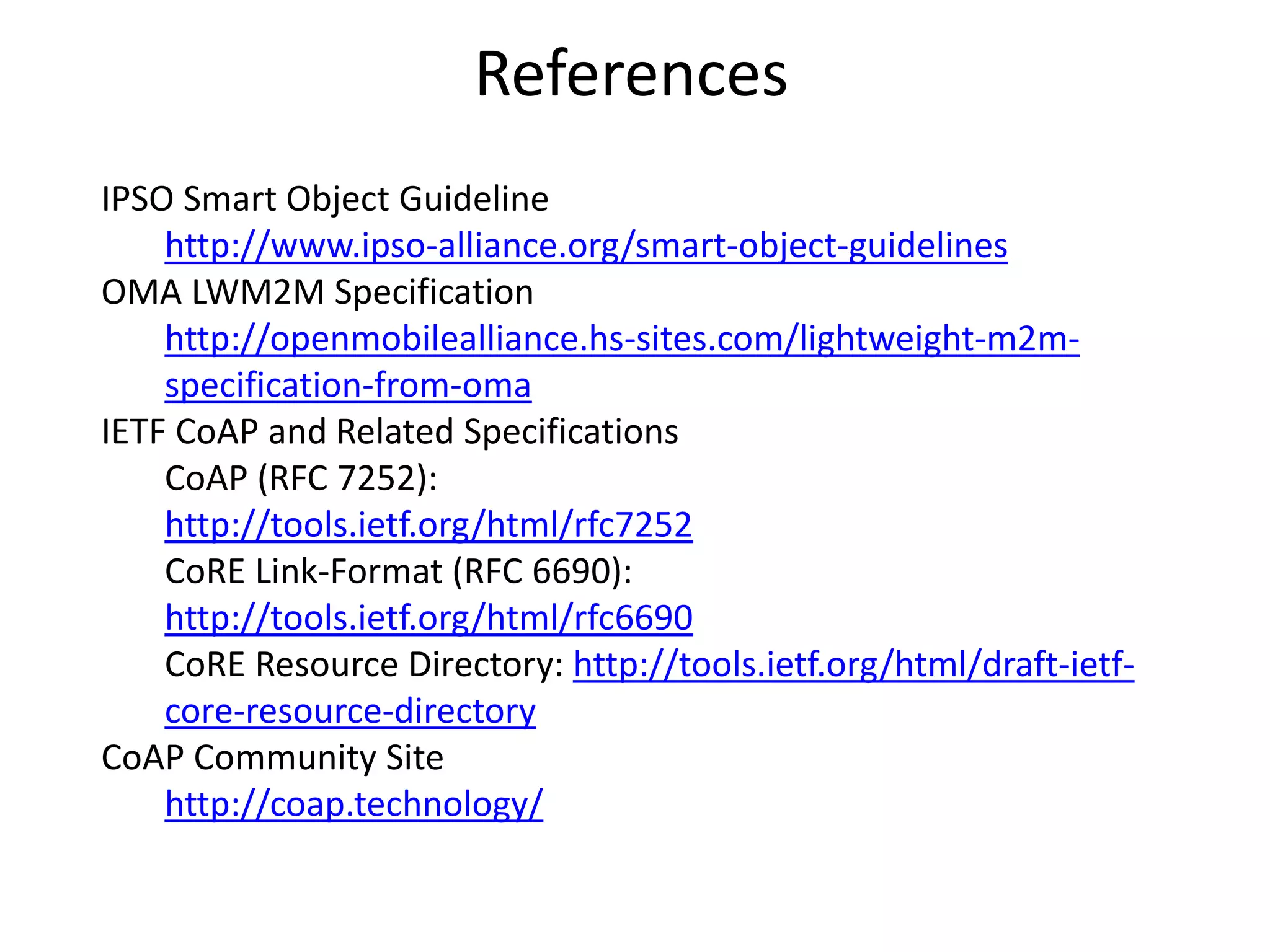
This document discusses using REST and hypermedia design patterns to build machine APIs for the Internet of Things (IoT). It proposes applying lessons from the Internet, such as using a "narrow waist" of common protocols, layered protocols, uniform addressing, and stateless interaction, to address challenges in IoT like interoperability, scalability, technology reuse, and lowering barriers to innovation. Specific protocols and standards discussed include CoAP, resource directories, IPSO smart objects, and OMA LWM2M. The document advocates using hypermedia to automate machine APIs and enable semantic discovery of IoT resources.