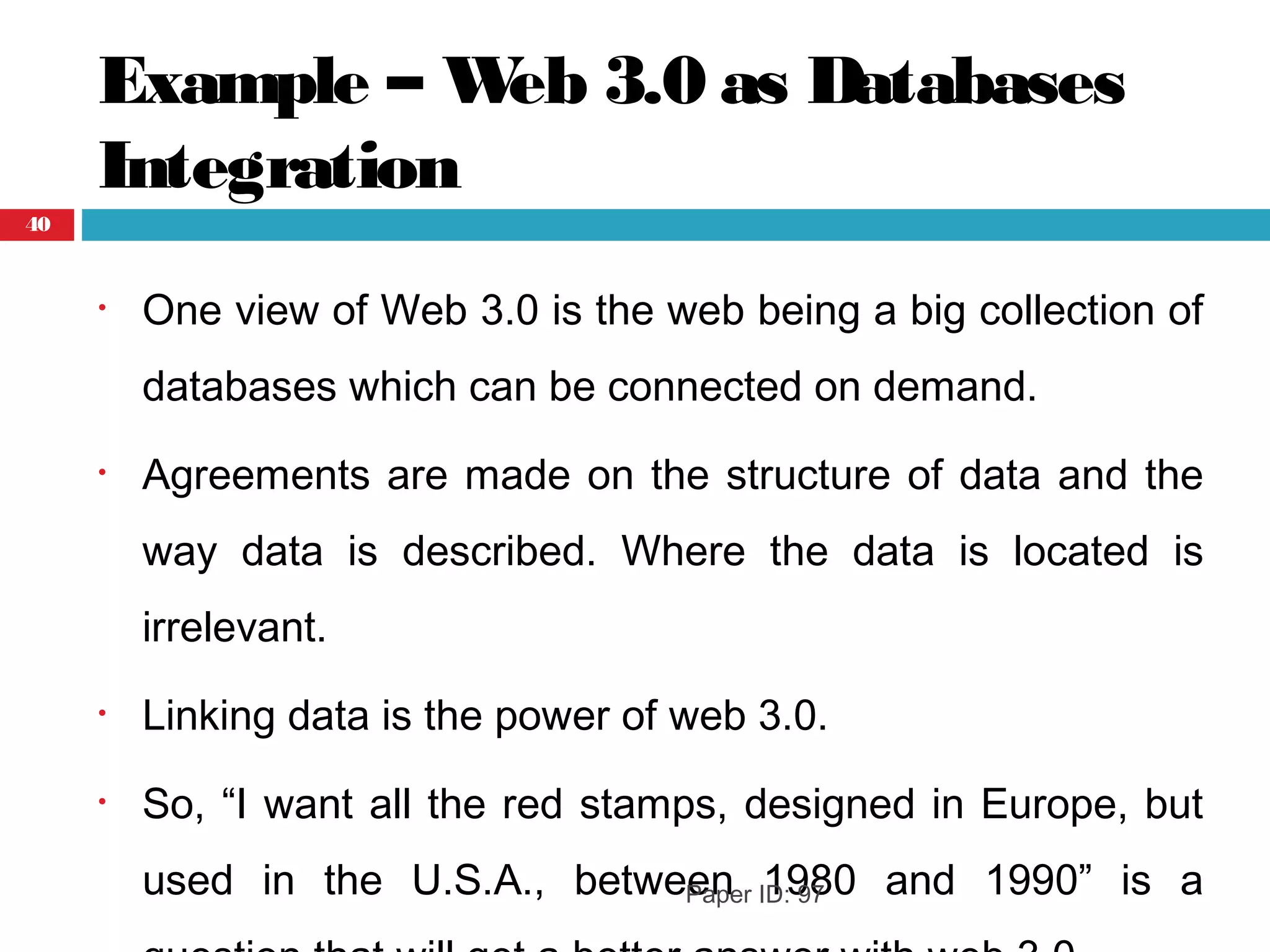
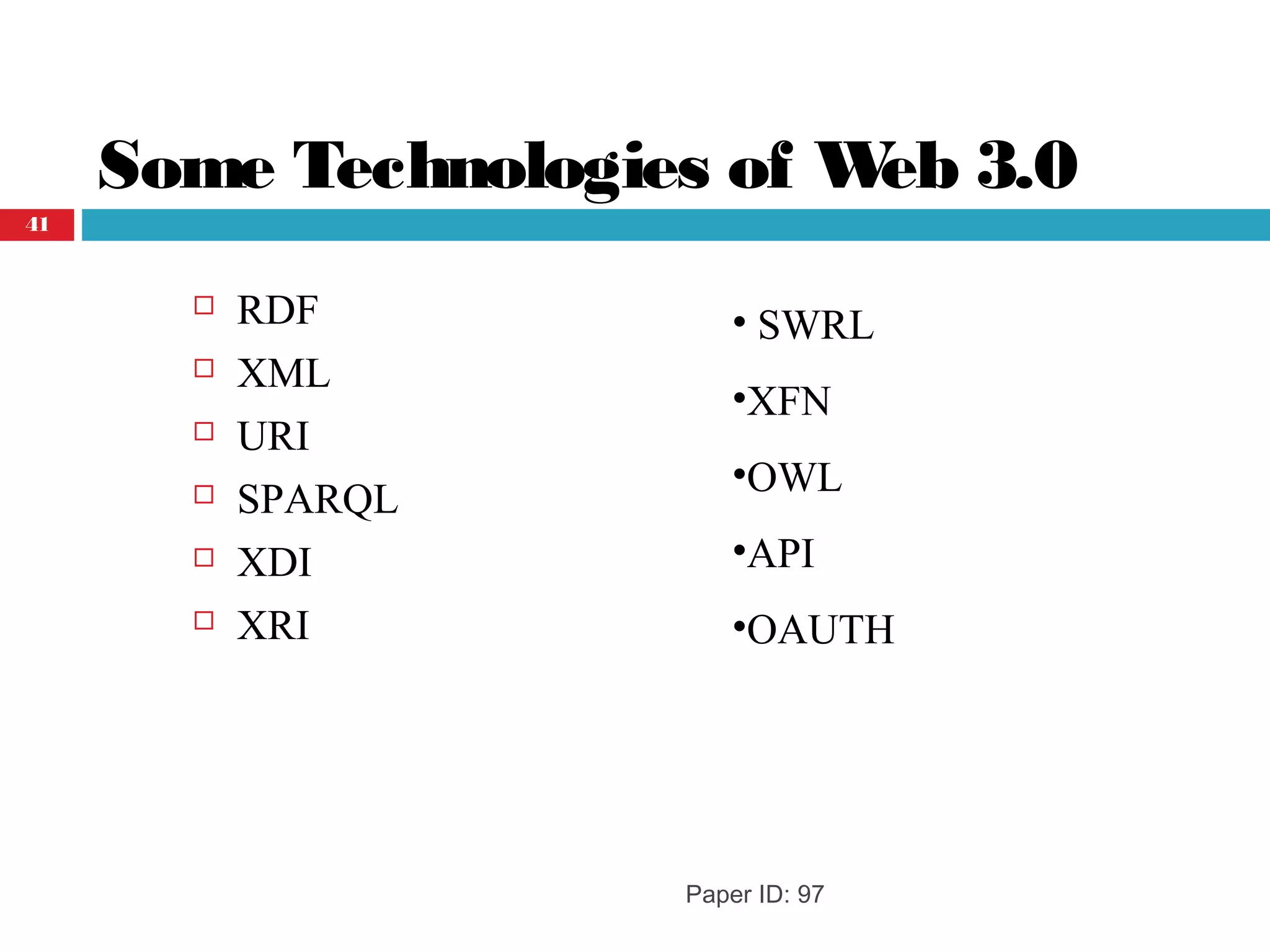
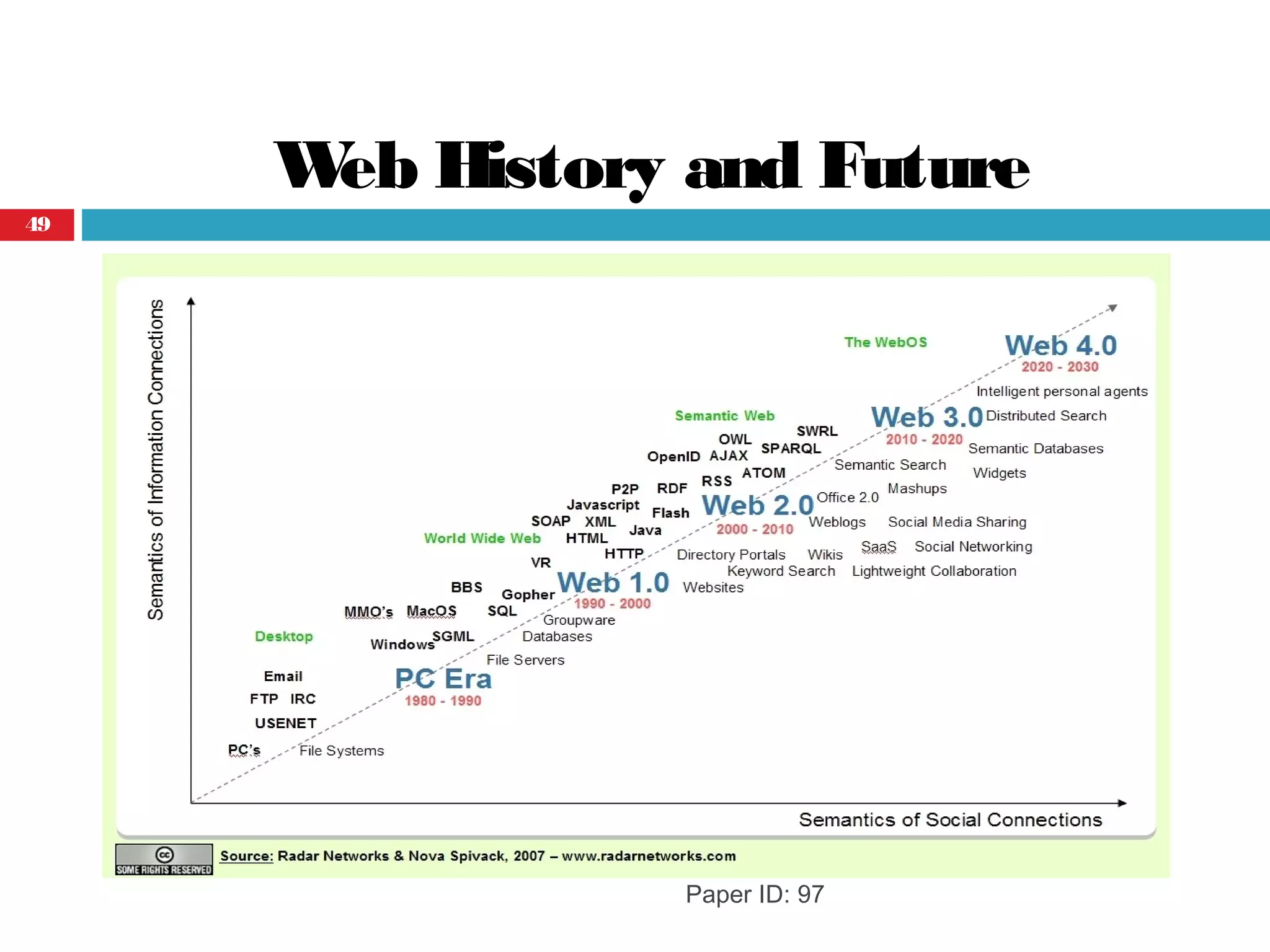
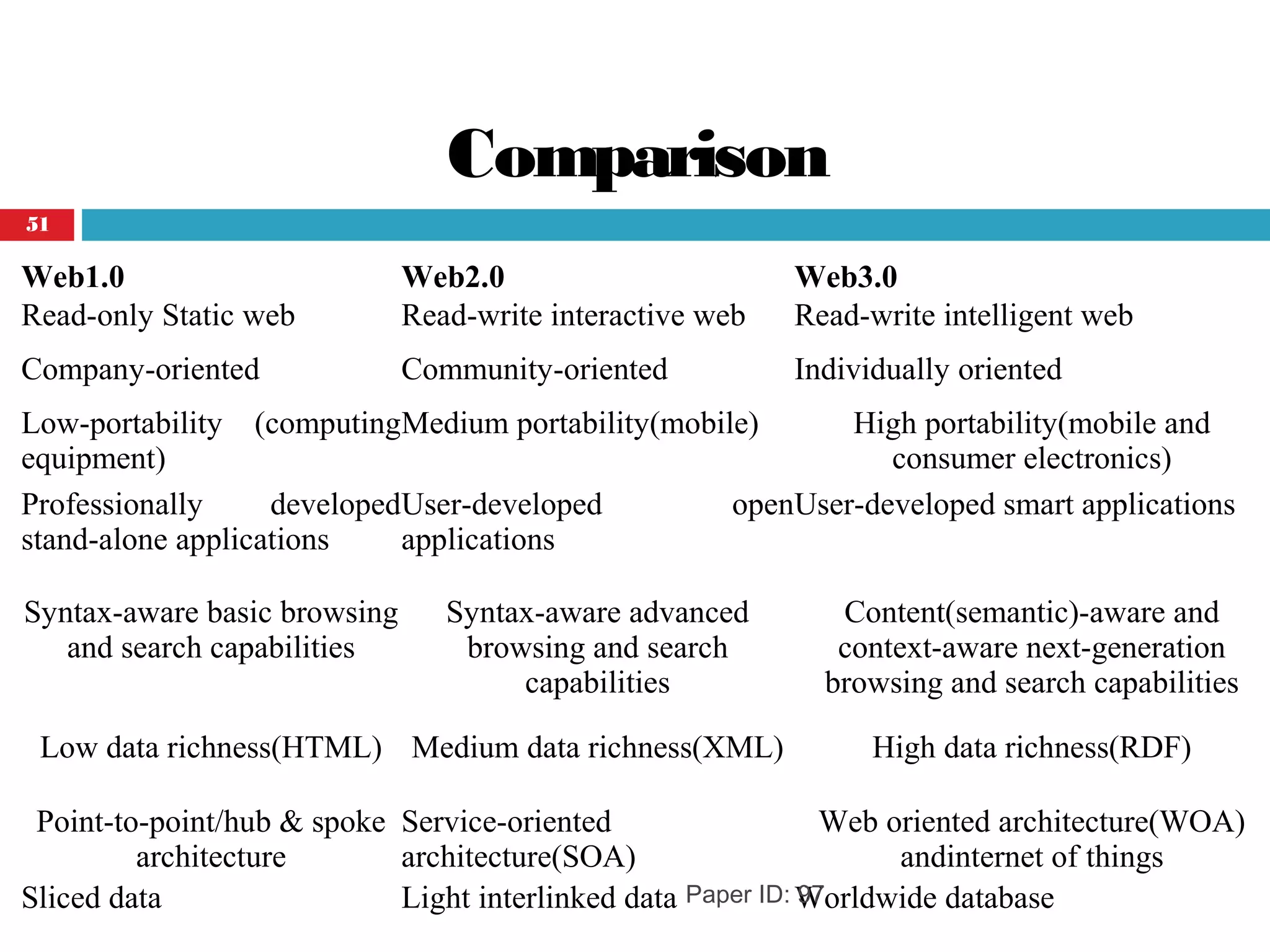
The document discusses the evolution of the World Wide Web from Web 1.0 to Web 3.0. Web 1.0 allowed only read-only access to static web pages. Web 2.0 enabled user-generated content and interaction through features like blogs and social media. Web 3.0, also called the Semantic Web, will feature an intelligent web that can understand the meaning of information through standards like XML, RDF, and OWL that structure and define relationships in data. This intelligent web of linked and integrated databases will enable more advanced searches and interactions that go beyond just keywords.

![Web 1.0
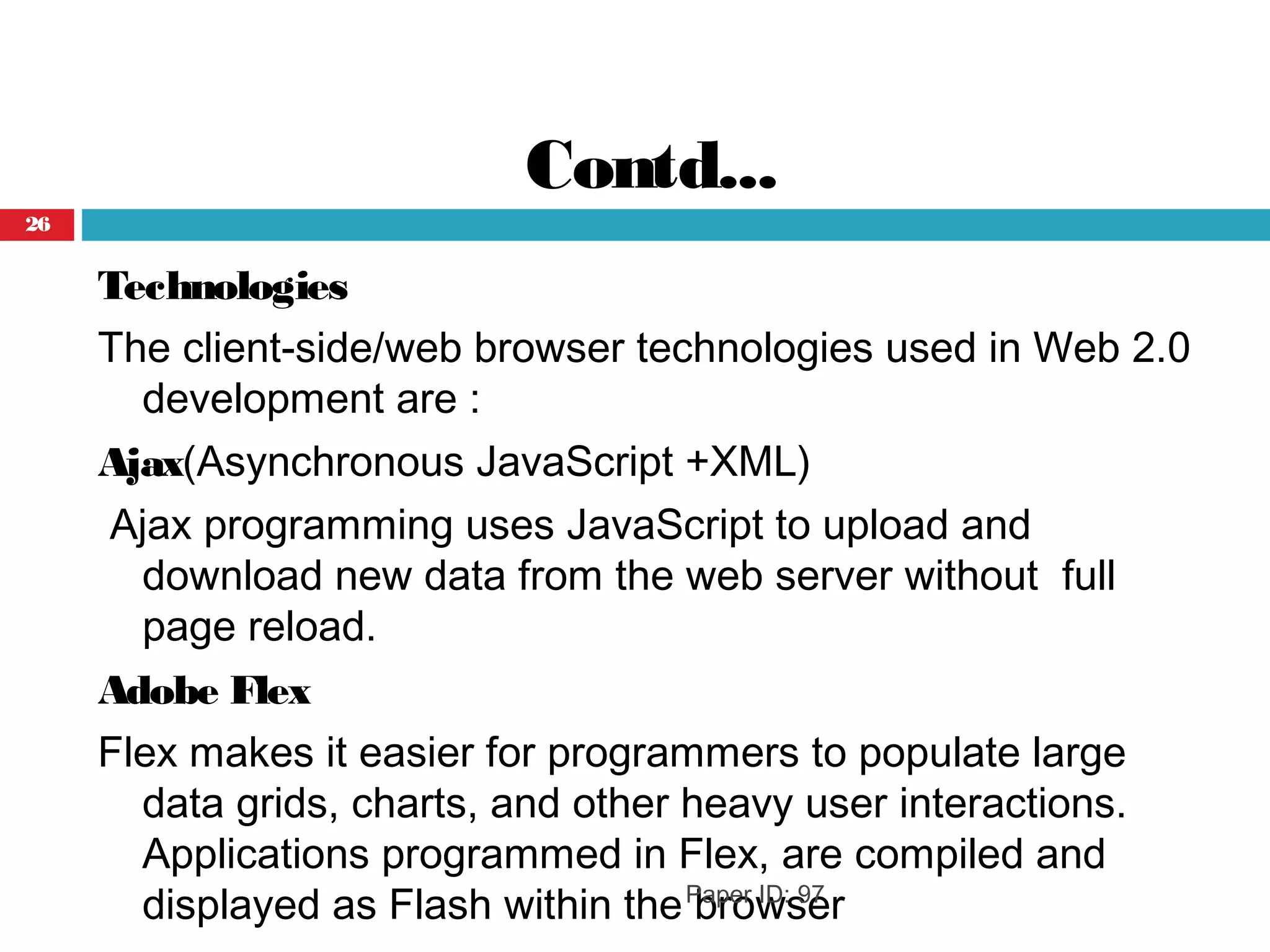
Web 1.0 [Push]
Web 1.0 is an old internet that only allows people
to read from the internet.
Paper ID: 97
Web1.0 is a one-way
platform
9](https://image.slidesharecdn.com/paperid-140528094849-phpapp01/75/Web-1-0-to-Web-3-0-Evolution-of-the-Web-and-its-Various-Challenges-9-2048.jpg)

![Paper ID: 97
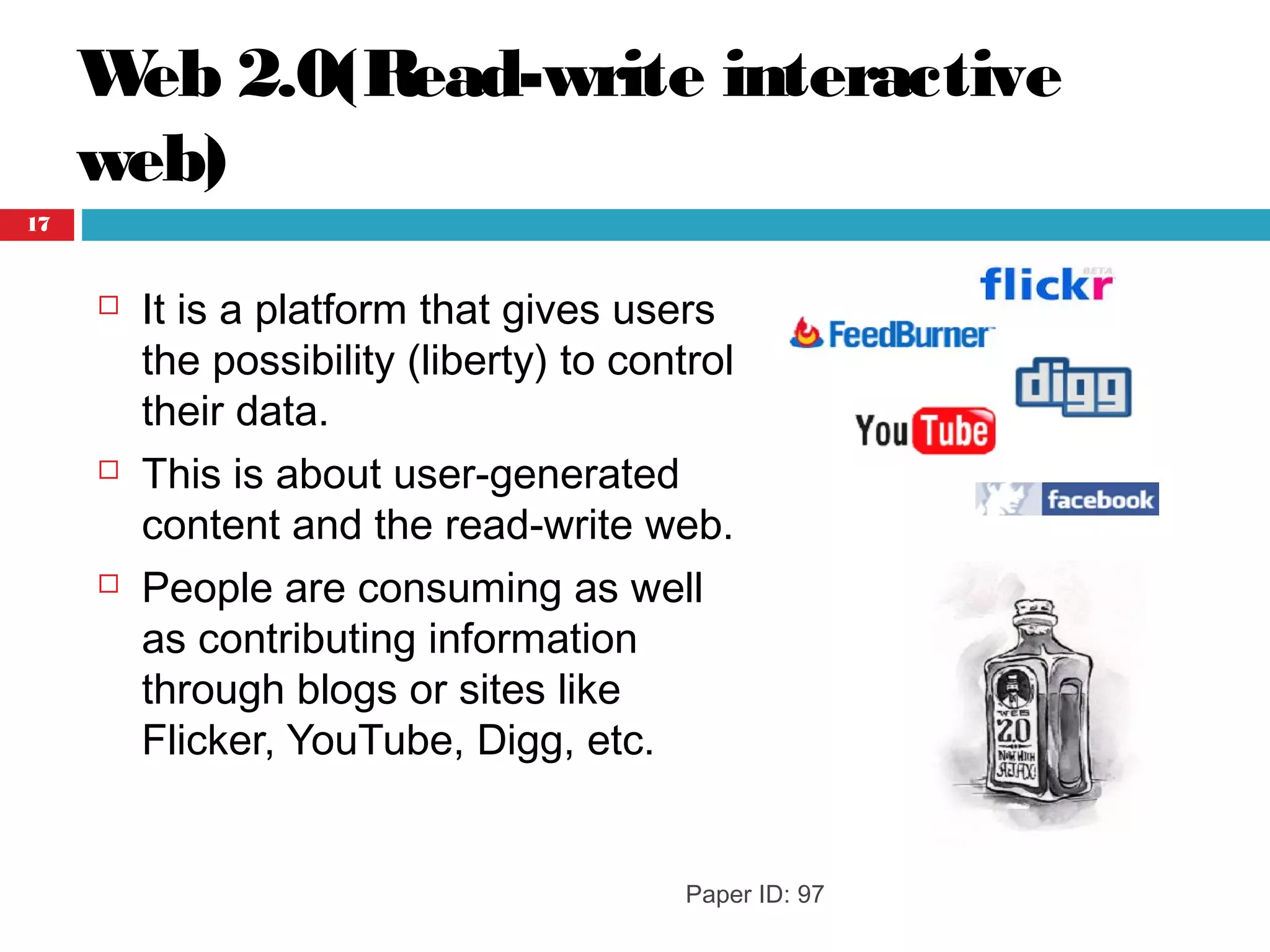
A term used to describe a new generation of
Web services and applications with an
increasing emphasis on human collaboration.
Web 2.0 [Share] Web2.0 is a two-way
Platform
16](https://image.slidesharecdn.com/paperid-140528094849-phpapp01/75/Web-1-0-to-Web-3-0-Evolution-of-the-Web-and-its-Various-Challenges-16-2048.jpg)


![Reference
[1] Dr Mike Evans.”The Evolution of the Web-From Web1.0toWeb4.0”.
[2] San, Murugesan (2007), “Understanding Web 2.0”, Journal IT
Professional.
[3]Akhilesh Dwivedi ,SureshKumar, Abhishek Dwivedi Dr. Manjeet
Sing “Current Security Considerations for Issues and Challenges of
Trustworthy Semantic Web” Int. J. Advanced Networking and
Applications Volume: 03, Issue: 01, Pages: 978-983 (2011).
[4]http://en.wikibooks.org/wiki/Web_2.0_and_Emerging_Learning_Tec
hnologies/Learning_Theory#Emerging_Web_2.0_Related_Learning
_Theory.
[5]David Rook “The Security Risks of Web 2.0”DefCon 17, Las Vegas.
[6]George Lawton ”Web 2.0 Creates Security Challenges” Published
by the IEEE Computer Society October 2007.
Paper ID: 97
52](https://image.slidesharecdn.com/paperid-140528094849-phpapp01/75/Web-1-0-to-Web-3-0-Evolution-of-the-Web-and-its-Various-Challenges-52-2048.jpg)
![[7]McAfee “White Paper The Security Implications of
Web2.0”http://www.ingrammicro.com/visitor/servicesdivision/McAfe
e-SaaS-Web-2-0-White-paper.pdf.
[8]Juan M. Silva , Abu Saleh Md. Mahfujur Rahman , Abdulmotaleb El
Saddik “Web 3.0: A Vision for Bridging the Gap between Real and
Virtual CommunicabilityMS '08 Proceedings of the 1st ACM
international workshop on Communicability design and evaluation
in cultural and ecological multimedia system.
[9]Second Life Official Website: http://secondlife.com
[10] Red-light Official Website: http://redlightcenter.com.
[11]Karim Sabbagh Olaf Acker Danny Karam Jad Rahban Designing
theTranscendent WebThe Power of Web 3.0 Booz & Company.
Paper ID: 97
53](https://image.slidesharecdn.com/paperid-140528094849-phpapp01/75/Web-1-0-to-Web-3-0-Evolution-of-the-Web-and-its-Various-Challenges-53-2048.jpg)