Embed presentation
Download to read offline

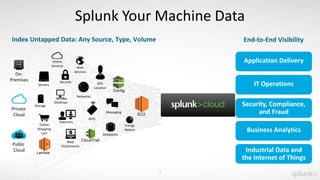
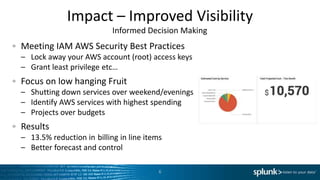
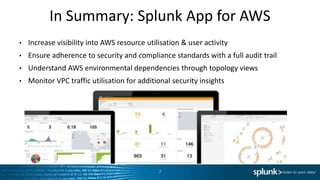

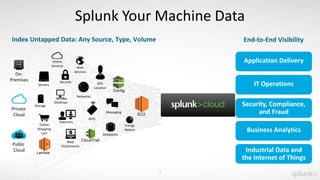
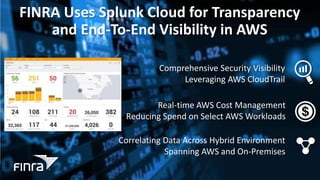
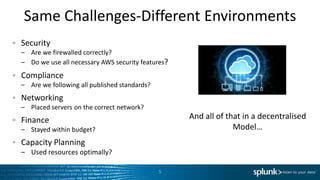
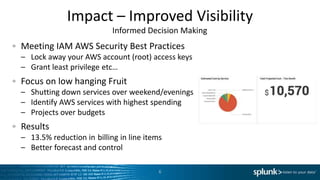
The document discusses the use of Splunk to manage AWS, emphasizing its ability to provide transparency and real-time visibility into cloud computing environments. It highlights features such as improved security, compliance adherence, and cost management, along with the ability to analyze machine data from various sources. Key outcomes include a 13.5% reduction in billing and enhanced informed decision-making capabilities.