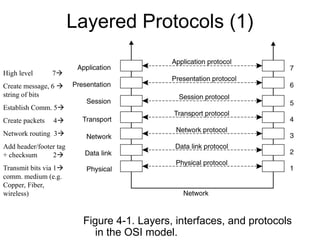
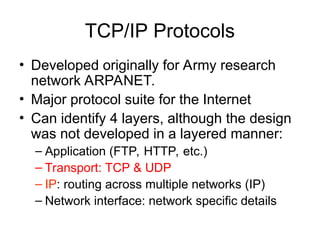
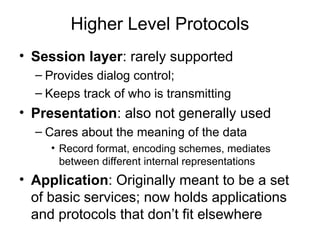
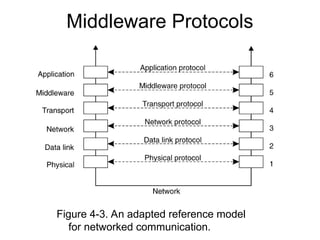
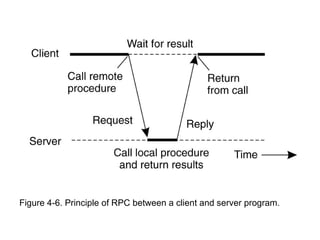
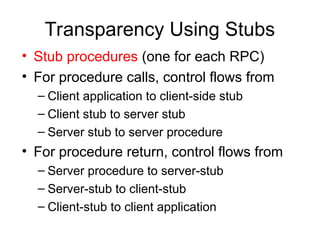
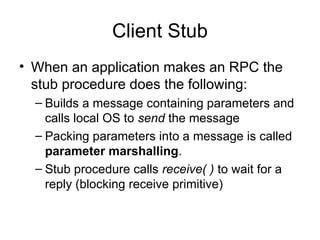
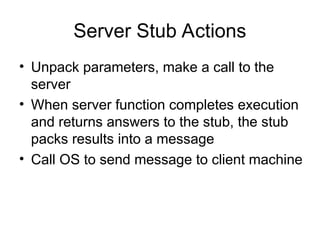
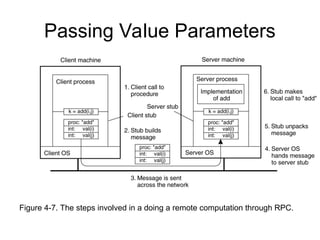
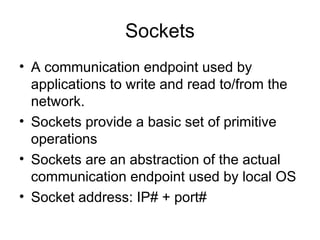
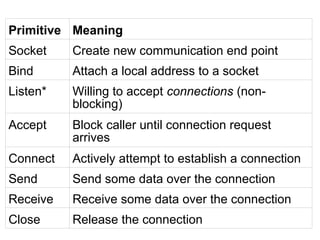
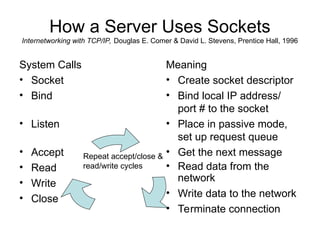
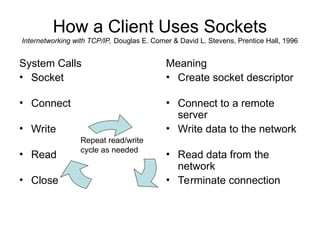
IPC: Introduction, Layered protocols, RMI, CORBA, API for internet
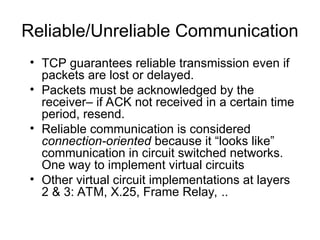
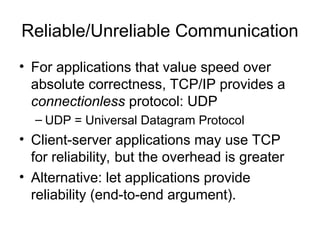
protocols, IPC through shared memory, external data representation
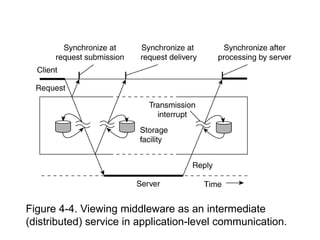
and marshaling, Types of communication, inter process
communication,
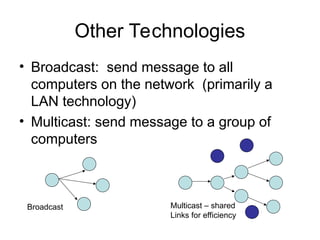
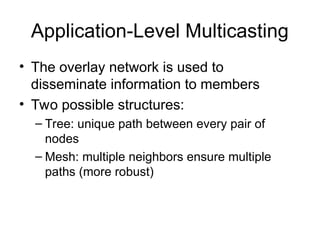
multicast
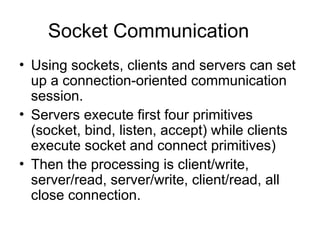
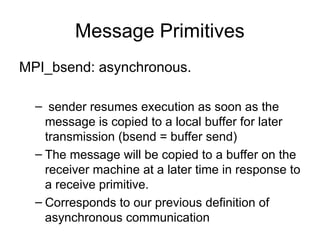
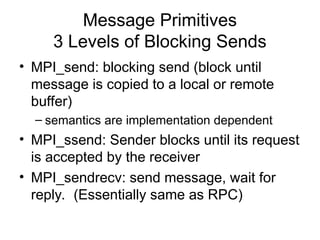
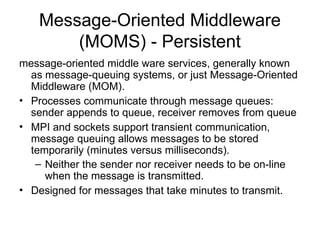
communication,message-oriented
communication, MPI, network virtualization, overlay networks