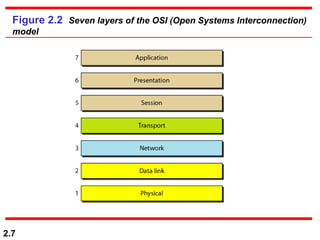
The document discusses the OSI model, which is a standard for network communication established by the International Organization for Standardization (ISO). The OSI model defines seven layers of network communication: physical, data link, network, transport, session, presentation, and application. Each layer has a specific role, with lower layers focusing on physical connectivity and higher layers focusing on end-user services. The physical layer is responsible for bit transmission between directly connected systems, while the transport layer handles process-to-process message delivery across networks.