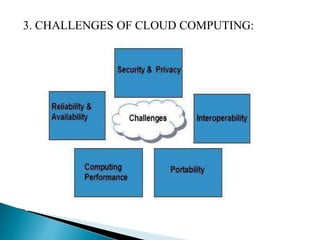
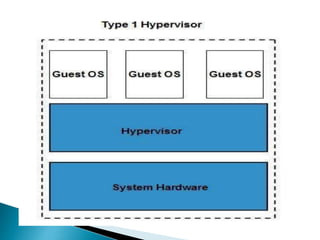
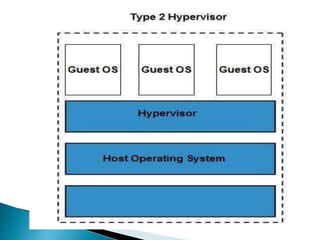
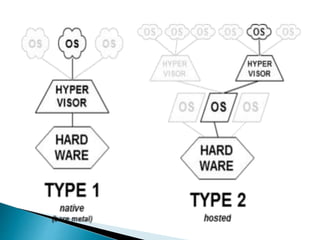
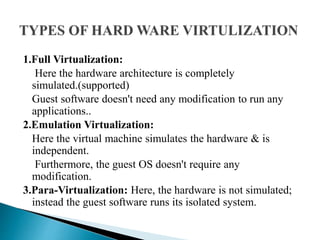
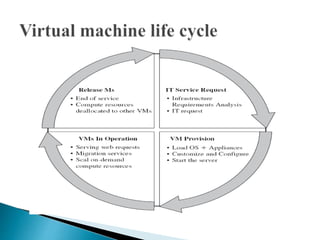
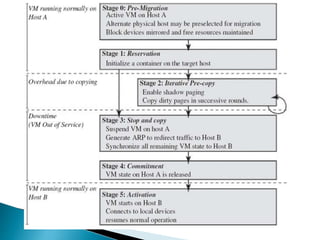
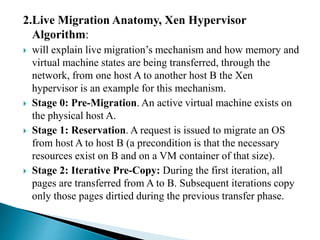
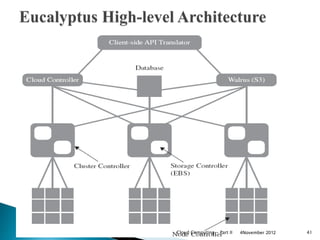
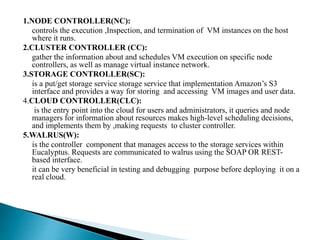
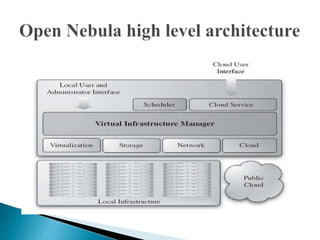
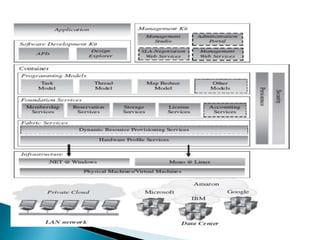
This document discusses cloud computing concepts including desired features of clouds, cloud computing features, challenges of cloud computing, hypervisor types, virtual machine migration techniques, and examples of cloud platforms and tools. The key points covered are the desired features of self-service, metering and billing, elasticity, and customization for clouds. Virtualization, virtual networking, and dynamic resource allocation are listed as important cloud computing features. Security, portability, interoperability, and performance are identified as challenges.