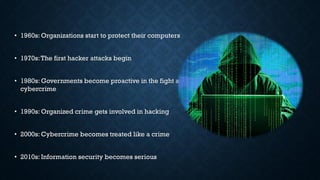
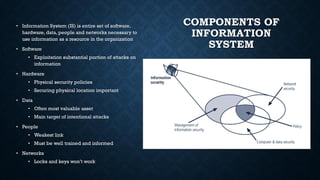
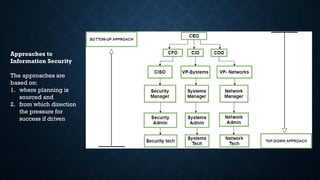
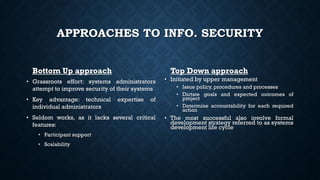
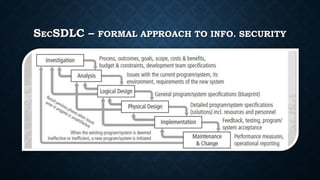
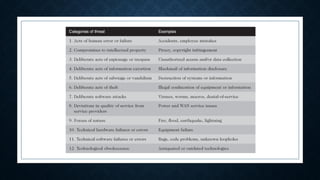
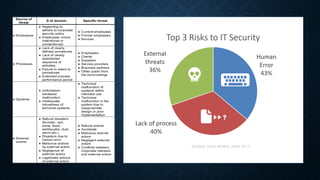
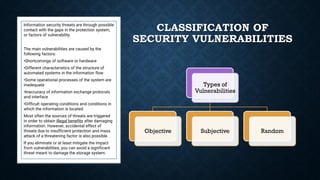
The document provides a comprehensive overview of information security, including its history, critical characteristics, and essential components designed to protect information assets. It discusses various security aspects, including physical, personal, and operational security, and highlights the importance of managing vulnerabilities and risks. Additionally, it outlines approaches to information security, emphasizing the need for both top-down and bottom-up strategies in developing effective protection measures.