Embed presentation
Download as PDF, PPTX
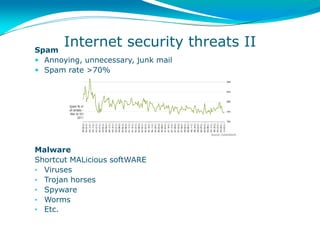

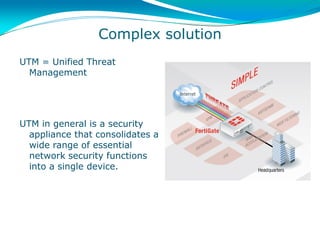


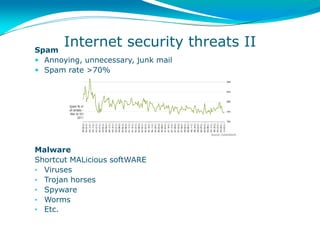
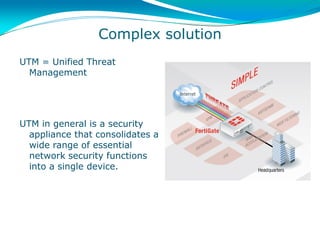
The document discusses internet security threats like malware, viruses, and spam. It describes how the traditional approach to these threats was to add standalone security technologies like antivirus, firewalls, and intrusion prevention systems. However, this led to complex solutions. The document then introduces unified threat management (UTM) as an integrated security appliance that consolidates these essential network security functions into a single device to provide an easier to manage solution to the new challenges posed by the internet.