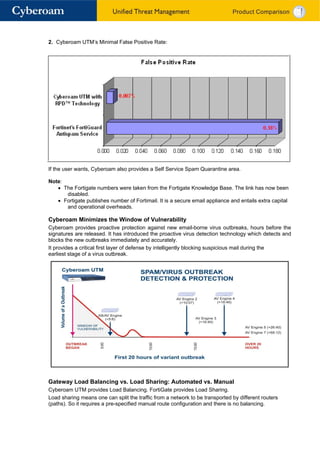
Cyberoam UTM provides a comprehensive security solution with certifications in enterprise firewall, VPN, anti-virus, anti-spam, IPS, and URL filtering capabilities. It takes an identity-based approach to security with user-centric policies and reporting. Cyberoam also offers superior anti-virus and anti-spam protection compared to FortiGate, including a proactive virus outbreak detection technology.