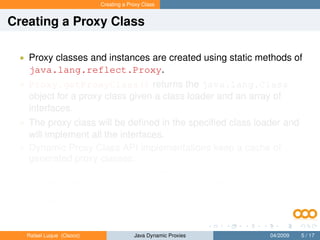
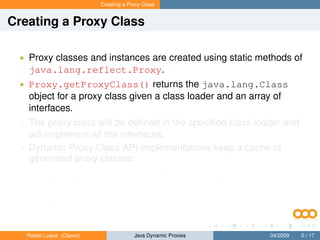
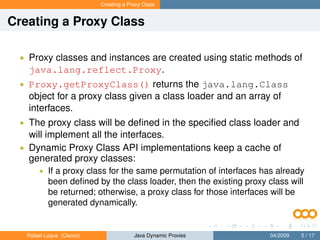
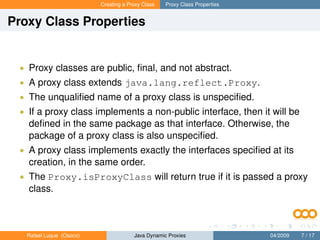
The document discusses creating proxy classes in Java at runtime. It explains that proxy classes are created using the Proxy class and implement interfaces specified at runtime. The Proxy class caches generated proxy classes and returns existing classes if they have been generated before for the same interfaces in a class loader. Properties of proxy classes are that they are public, final, extend Proxy and implement interfaces as specified when created.



![Creating a Proxy Class
Proxy.getProxyClass Method
Proxy.getProxyClass() method
public static Class getProxyClass(
ClassLoader loader,
Class[] interfaces)
throws IllegalArgumentException
Rafael Luque (Osoco) Java Dynamic Proxies 04/2009 6 / 17](https://image.slidesharecdn.com/javadynamicproxies-120914061916-phpapp02/85/Understanding-Java-Dynamic-Proxies-11-320.jpg)








![Creating a Proxy Instance
Proxy Instance I
• Each proxy class has one public constructor that takes as
argument an implementation of the interface
InvocationHandler.
• You can instantiate the proxy class using the reflection API:
Proxy for the Foo interface
Class proxyClass = Proxy.getProxyClass(
Foo.class.getClassLoader(), new Class[] { Foo.class });
InvocationHandler handler = new MyInvocationHandler(...);
Foo f = (Foo) proxyClass.
getConstructor(new Class[] { InvocationHandler.class }).
newInstance(new Object[] { handler });
Rafael Luque (Osoco) Java Dynamic Proxies 04/2009 10 / 17](https://image.slidesharecdn.com/javadynamicproxies-120914061916-phpapp02/85/Understanding-Java-Dynamic-Proxies-22-320.jpg)
![Creating a Proxy Instance
Proxy Instance II
• Better, you can use the Proxy.newProxyInstance method:
Proxy using Proxy.newProxyInstance
InvocationHandler handler = new MyInvocationHandler(...);
Foo f = (Foo) Proxy.newProxyInstance(
Foo.class.getClassLoader(),
new Class[] { Foo.class },
handler);
• This method combines the actions of calling
Proxy.getProxyClass with invoking the constructor with an
invocation handler.
Rafael Luque (Osoco) Java Dynamic Proxies 04/2009 11 / 17](https://image.slidesharecdn.com/javadynamicproxies-120914061916-phpapp02/85/Understanding-Java-Dynamic-Proxies-23-320.jpg)
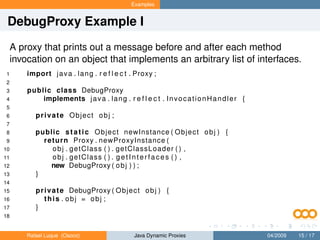
![Examples
DebugProxy Example II
19 public O b j e c t i n v o k e ( O b j e c t proxy , Method m, O b j e c t [ ] args )
20 throws Throwable {
21
22 Object r e s u l t ;
23 try {
24 System . o u t . p r i n t l n ( ‘ ‘ b e f o r e method ’ ’ ) ;
25 r e s u l t = m. i n v o k e ( obj , args ) ;
26 } catch ( I n v o c a t i o n T a r g e t E x c e p t i o n e ) {
27 throw e . g e t T a r g e t E x c e p t i o n ( ) ;
28 } catch ( E x c e p t i o n e ) {
29 throw new RuntimeException ( ) ;
30 } finally {
31 System . o u t . p r i n t l n ( ‘ ‘ a f t e r method ’ ’ ) ;
32 }
33 return r e s u l t ;
34
35 }
36
37 }
Rafael Luque (Osoco) Java Dynamic Proxies 04/2009 16 / 17](https://image.slidesharecdn.com/javadynamicproxies-120914061916-phpapp02/85/Understanding-Java-Dynamic-Proxies-28-320.jpg)
